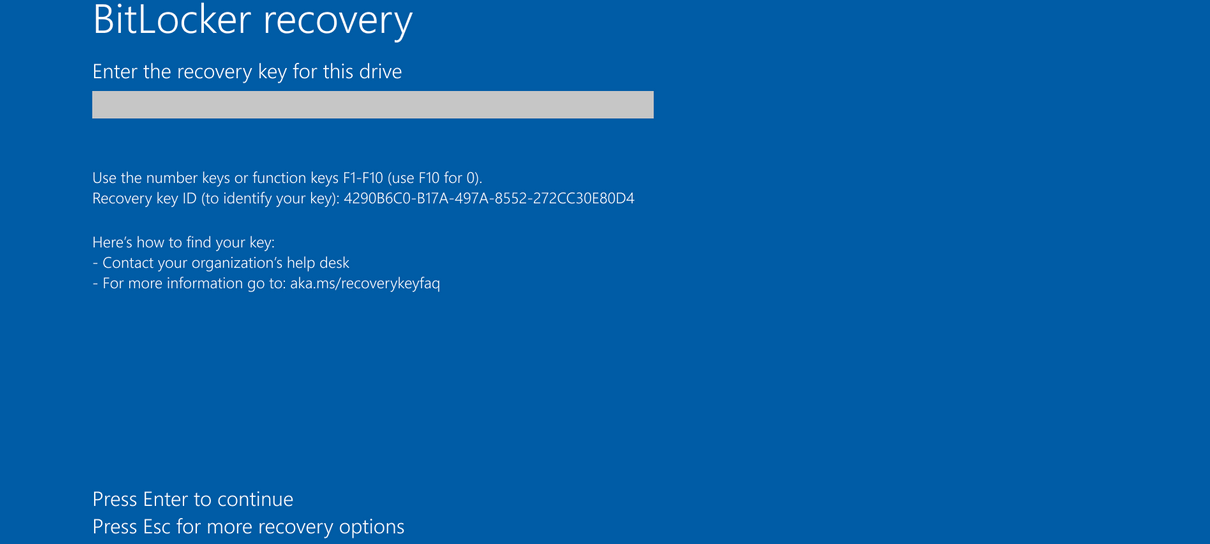
Microsoft has confirmed that the recent April 2026 security update, identified as KB5082063, is causing certain Windows Server 2025 systems to enter BitLocker recovery mode upon their initial restart post-installation. This development underscores the inherent complexities of maintaining security and operational continuity within sophisticated enterprise IT environments, particularly when integrating critical system updates with existing, highly specific configurations.
The Role of BitLocker in Enterprise Security
BitLocker Drive Encryption is a foundational security feature integrated into Microsoft Windows, designed to safeguard data by providing full volume encryption for operating system drives, fixed data drives, and removable data drives. Its primary purpose is to protect against unauthorized data access in scenarios involving physical theft, loss, or unauthorized disposal of devices. BitLocker leverages a Trusted Platform Module (TPM) – a specialized microcontroller that stores cryptographic keys – to ensure the integrity of the boot process. When a system boots, BitLocker verifies the system’s state against a known good configuration. If any unauthorized changes are detected in critical boot components, such as the boot loader, firmware, or hardware, BitLocker will intentionally lock the drive and prompt for a recovery key. This mechanism, while designed to enhance security, can become an operational impediment when triggered unexpectedly by legitimate system updates.
Understanding the Trigger: KB5082063 and Specific Configurations
The current issue specifically impacts Windows Server 2025 devices that possess an "unrecommended BitLocker Group Policy configuration." Microsoft elaborates that the recovery prompt occurs only when a confluence of precise conditions is met. While the full list of these conditions was not provided in the initial alert, the core mechanism revolves around how BitLocker is bound to the system’s security hardware and software components, particularly concerning the Platform Configuration Register (PCR) values.
PCRs are registers within the TPM that record measurements of components loaded during the boot process. BitLocker can be configured to bind to specific PCRs, most notably PCR7, which is tied to the Secure Boot process. Secure Boot is a security standard developed by members of the PC industry to help ensure that a device boots using only software that is trusted by the Original Equipment Manufacturer (OEM). When BitLocker is configured to use PCR7, it means that changes to the Secure Boot configuration, or any components measured by PCR7, will trigger a BitLocker recovery event.
The "unrecommended Group Policy configuration" likely refers to a setting that either explicitly disables or incorrectly configures the use of PCR7 for BitLocker binding, or otherwise creates a conflict with the expected boot state after the KB5082063 update. This specific update, intended to bolster Windows security, inadvertently modifies a component in a way that, under these particular configurations, appears as an unauthorized change to BitLocker, hence triggering the recovery prompt. Microsoft clarifies that this recovery key input is a one-time requirement, provided the problematic Group Policy configuration remains unchanged, implying that the update establishes a new baseline state for BitLocker. Subsequent restarts will not prompt for the key once the new state is accepted.
Operational Impact and Enterprise Challenges
The implications of unexpected BitLocker recovery prompts, particularly on server environments, are substantial. Servers are the backbone of enterprise operations, hosting critical applications, databases, and services. Any disruption, even a temporary one, can lead to significant downtime, loss of productivity, and potential financial repercussions.

- Downtime and Service Interruption: Each server requiring a recovery key means manual intervention, delaying the return to service. In large organizations with hundreds or thousands of servers, this can quickly escalate into a massive operational bottleneck.
- Administrative Burden: IT teams must identify affected servers, locate the correct recovery keys, and manually enter them. This process is time-consuming and resource-intensive, diverting personnel from other critical tasks.
- Security Concerns: While BitLocker is a security feature, the need to retrieve and input recovery keys frequently can, ironically, introduce security risks if keys are not stored securely or if the process is rushed. Moreover, users might be tempted to disable BitLocker or modify configurations without proper understanding to avoid future prompts, inadvertently weakening their security posture.
- Complexity of Enterprise Environments: The issue highlights the inherent challenges in managing diverse and complex enterprise IT landscapes. Group Policies, designed for centralized management, can also be a source of unforeseen interactions when updates are deployed across heterogeneous systems with varying configurations and legacy settings. The specific impact on Windows Server 2025 further indicates the sensitivity of newer operating system iterations to certain policy interactions.
Microsoft’s Response and Mitigation Strategies
Microsoft has acknowledged the issue and is actively working on a permanent resolution. In the interim, they have provided immediate workarounds to help administrators deploy the April security updates without encountering the BitLocker recovery prompt. These workarounds focus on modifying the system’s configuration to align with BitLocker’s expectations before the update is applied:
- Group Policy Configuration Removal: Administrators are advised to remove the specific Group Policy configuration that causes the conflict prior to deploying KB5082063. This involves ensuring that BitLocker bindings correctly utilize the PCR7 profile. By aligning the policy with recommended practices, the system’s boot state after the update is less likely to be perceived as a security threat by BitLocker.
- Known Issue Rollback (KIR): For environments where removing the PCR7 Group Policy before installation is not feasible, Microsoft offers a Known Issue Rollback (KIR). KIRs are designed to revert specific, problematic changes introduced by an update without requiring a full uninstall of the update itself. In this scenario, applying a KIR prevents the automatic switch to the 2023 Boot Manager, thereby avoiding the BitLocker recovery trigger. This provides a crucial lifeline for organizations that cannot easily modify their Group Policies on a large scale before a mandatory security update.
These temporary solutions underscore the delicate balance between rapid security patching and ensuring operational stability in a production environment.
A Recurring Pattern: Historical Context of BitLocker Incidents
This is not an isolated incident, but rather the latest in a series of similar BitLocker recovery issues following Windows updates. This recurring pattern raises questions about the robustness of Microsoft’s update testing protocols, especially concerning the intricate interactions between security features, system components, and diverse enterprise configurations.
- May 2025 Windows 10 Emergency Updates: Microsoft previously issued emergency updates to address an issue causing Windows 10 systems to enter BitLocker recovery after installing the May 2025 security updates. This incident also involved unexpected boot integrity checks.
- August 2024 BitLocker Recovery Fix: One year prior, in August 2024, Microsoft resolved another widespread issue that triggered BitLocker recovery prompts across all supported Windows versions following the July 2024 Windows security updates. This problem highlighted the broad impact such issues can have.
- August 2022 KB5012170 Security Update: In August 2022, Windows devices experienced similar BitLocker recovery prompts after installing the KB5012170 security update, which focused on Secure Boot DBX (Denied Boot Execution) updates. This particular update aimed to patch a critical vulnerability in the Secure Boot process, but its deployment led to unexpected BitLocker triggers for many users and organizations.
The consistent recurrence of these issues suggests that the interaction between BitLocker’s highly sensitive boot integrity checks and routine system updates remains a complex challenge. Each incident, while distinct in its root cause, points to the potential for critical security updates to inadvertently disrupt system functionality, particularly in configurations that deviate from Microsoft’s ideal baseline.
Future Outlook and Best Practices
For organizations, these incidents serve as a critical reminder of the importance of a robust update management strategy:
- Staged Deployment and Testing: Implement a staged deployment approach for all critical updates, beginning with a pilot group of non-production systems or a dedicated testing environment. This allows for early detection of issues before they impact the entire production infrastructure.
- Comprehensive Documentation of Configurations: Maintain meticulous documentation of all Group Policies, BitLocker configurations, and security baselines. Understanding existing configurations is crucial for diagnosing and mitigating update-related issues.
- Secure Recovery Key Management: Ensure that BitLocker recovery keys are securely stored, easily accessible to authorized personnel, and regularly backed up. Centralized key management solutions are essential for enterprise environments.
- Adherence to Recommended Policies: Regularly review and align BitLocker Group Policy configurations with Microsoft’s recommended best practices. Deviating from these can introduce unforeseen vulnerabilities or operational challenges during updates.
- Stay Informed: Monitor Microsoft’s official channels and security advisories closely for known issues and recommended mitigations following update releases.
As enterprise IT environments become increasingly complex and intertwined with critical security features like BitLocker, the delicate balance between enhancing security and ensuring operational stability becomes paramount. Microsoft’s ongoing efforts to refine its update process and provide timely solutions are crucial, but organizations must also bolster their internal strategies to navigate these inevitable challenges effectively. The latest BitLocker incident on Windows Server 2025 is another testament to the intricate dance between cutting-edge security and the practical realities of large-scale system administration.






