
The clandestine marketplaces for compromised financial credentials have long been characterized by extreme volatility and pervasive deception, where even seasoned participants frequently encounter scams, exit frauds, and compromised service providers. This inherently unstable environment has intensified in recent years, driven by escalating pressure from international law enforcement agencies, endemic mistrust among criminal syndicates, and the transient nature of underground platforms. Consequently, threat actors are compelled to adopt increasingly rigorous methodologies to identify trustworthy data suppliers and mitigate operational risks within their illicit ventures.
A recently uncovered strategic document, circulating within a prominent underground forum and analyzed by cybersecurity experts, offers an unprecedented glimpse into the sophisticated due diligence processes employed by cybercriminals to navigate the treacherous landscape of stolen credit card (CC) marketplaces. This comprehensive guide, originally titled "The Underground Guide to Legit CC Shops: Cutting Through the Bullshit," transcends mere operational advice, detailing a structured framework for evaluating carding shops, implementing robust operational security (OpSec) protocols, and formulating effective data sourcing strategies. It effectively codifies the evolving paradigms of trust, reliability, and operational resilience that now define contemporary financial fraud actors. While certain sections appear to subtly endorse specific services, potentially indicating an author with vested interests, the document nonetheless provides invaluable intelligence into the intricate mechanics of the carding economy and the increasingly stringent standards demanded for sustained illicit operations.
From Opportunistic Exploitation to Strategic Procurement Discipline
Historically, the acquisition and use of stolen credit card data often stemmed from opportunistic exploits, relying on readily available compromised information. However, a striking revelation from the guide is its re-conceptualization of "carding" from a haphazard criminal act into a meticulously process-driven discipline. The document’s primary focus shifts decisively from the mechanics of exploiting stolen cards to the critical evaluation of data suppliers. This fundamental reorientation reflects a broader maturation within underground markets, where the paramount risk is no longer solely the failure of an individual fraudulent transaction, but rather the more profound threat of being defrauded by fellow criminals or inadvertently engaging with infrastructure already compromised by law enforcement.
The author repeatedly underscores that genuine legitimacy within these markets is not conferred by superficial branding, sophisticated web design, or high visibility, but by demonstrable longevity and survivability. A truly "reliable" shop, in this context, is one that consistently maintains operations over extended periods, effectively weathering sustained law enforcement interventions, internal scam attempts, and market instability. This criterion directly correlates with observed trends across various subterranean economies, where the operational lifespan of illicit marketplaces has become increasingly unpredictable, thereby necessitating continuous, rigorous verification practices from their users.
Furthermore, the guide explicitly states that the defining characteristic of a "legitimate" shop is not merely its consistent uptime, but the intrinsic quality and utility of the stolen data it provides. Direct references to "fresh bins" (Bank Identification Numbers) and consistently low transaction decline rates unequivocally point to the critical importance of the underlying data sources. These sources can range from widespread infostealer malware infections, sophisticated phishing campaigns, or targeted point-of-sale (PoS) system breaches. In this highly competitive ecosystem, a vendor’s reputation is not built on empty promises but on the verifiable track record of supplying credit card data that consistently facilitates successful fraudulent transactions. Shops that fail to maintain robust and fresh data streams are swiftly exposed and abandoned, while those with reliable, ongoing access to newly compromised credentials ascend to a position of dominance.
Cultivating Confidence in a Fundamentally Trustless Environment
Transparency emerges as another central tenet of the guide’s recommendations for establishing reliability. The document emphasizes the imperative of clear and unambiguous pricing structures, real-time inventory updates, and robust, functional support systems, including integrated ticketing and secure escrow services. These operational attributes bear a striking resemblance to the best practices observed in legitimate e-commerce platforms, highlighting how leading carding shops have strategically adopted mainstream business methodologies to foster user confidence and minimize transactional friction. The adaptation of such practices demonstrates a sophisticated understanding of consumer behavior, even within a criminal context, where perceived professionalism can significantly reduce apprehension and encourage repeat business.
Equally pivotal is the role of community validation. The guide explicitly dismisses on-site testimonials as inherently unreliable and easily fabricated, instead steering users towards detailed discussions within closed or invitation-only forums. This preference reflects a growing fragmentation of the underground landscape, where trust is increasingly forged and maintained within tightly controlled environments and through long-standing reputations verified by a trusted peer group. Actors are strongly encouraged to seek out sustained discussion threads, historical operational presence, and consistent positive feedback over time, rather than isolated or recently posted endorsements that could signal a "shill" campaign.

The document also reveals a profound awareness of adversarial pressures. The pronounced emphasis on security-first infrastructure, such as the deployment of multiple mirror domains, robust Distributed Denial of Service (DDoS) protection, and the deliberate absence of tracking mechanisms, strongly suggests that operators are actively engaged in defending their services not only against monitoring efforts by law enforcement but also against disruption attempts from rival criminal groups. In essence, these illicit marketplaces function not merely as distribution channels for compromised data, but as fortified operational environments meticulously engineered to ensure continuous service delivery and evade detection. This level of defensive sophistication underscores the increasing stakes and professionalism within the cybercrime underworld.
The Technical Due Diligence Framework
Beyond these overarching principles, the guide introduces a detailed, step-by-step vetting protocol that provides invaluable insight into the granular due diligence conducted by threat actors. Technical checks, including domain age analysis, scrutiny of WHOIS privacy registrations, and evaluation of SSL certificate configurations, are presented as non-negotiable baseline requirements. While these individual checks are relatively straightforward, their collective application signifies a concerted effort to introduce structured, analytical rigor into what was historically a far more informal, trust-based decision-making process. It moves away from anecdotal evidence towards verifiable technical indicators.
The guide further highlights the strategic importance of identifying and verifying mirror infrastructure and redundant access points. It explicitly notes that well-established, resilient illicit operations rarely depend on a single domain, acknowledging the inherent instability of underground services where takedowns and disruptions are commonplace. The demonstrable presence of multiple, geographically diverse access points is framed as a crucial indicator of operational maturity, resilience, and a proactive approach to business continuity in the face of inevitable adversarial action.
Social intelligence gathering plays an equally significant, albeit indirect, role. Rather than relying on direct, potentially compromised interactions with vendors, users are advised to meticulously analyze historical forum discussions, track vendor operational histories, and identify subtle patterns of behavior over extended periods. Particular emphasis is placed on detecting coordinated endorsement campaigns, such as a sudden influx of positive reviews originating from newly created or previously inactive accounts—a classic tactic frequently associated with fraudulent schemes or "exit scams."
Paramount Importance of Operational Security
A cornerstone of the guide’s instructional content is its unwavering focus on operational security (OpSec). The recommendations, while specifically contextualized within the realm of credit card fraud, closely mirror the advanced practices observed across a broad spectrum of sophisticated cybercriminal activities. Users are rigorously advised to avoid direct network connections to illicit services, to consistently utilize anonymizing proxy services strategically aligned with target geographies, and to rigorously compartmentalize their operational environments through the use of dedicated physical systems or isolated virtual machines. This multi-layered approach to network and system isolation minimizes potential forensic linkages back to the perpetrator.
The discussion surrounding cryptocurrency usage is particularly illuminating. The guide strongly cautions against direct transactions originating from regulated or identifiable cryptocurrency exchanges, instead advocating for the exclusive use of intermediary "mixing" services, multiple hop wallets, and privacy-focused digital assets such as Monero. This reflects a heightened and growing awareness among threat actors regarding the advanced capabilities of blockchain analysis firms and the inherent traceability risks associated with transactions involving more transparent cryptocurrencies like Bitcoin.
Collectively, these comprehensive OpSec recommendations underscore a critical evolutionary shift: contemporary threat actors are no longer relying solely on individual anonymization tools to evade detection. Instead, they are systematically adopting layered, holistic strategies meticulously designed to reduce their exposure across every conceivable point of the entire operational chain. This elevated level of discipline suggests that even mid-tier financial fraud actors are increasingly integrating advanced security practices once exclusively associated with highly sophisticated and state-sponsored threat groups.
Market Segmentation: Scale Versus Exclusivity
The guide further categorizes carding shops into distinct operational models, reflecting the increasing diversification and specialization within the underground economy. These models include large, highly automated platforms and smaller, more exclusive, curated vendor groups. This segmentation illustrates how different threat actors prioritize various attributes—such as sheer scale, ease of accessibility, or the perceived quality of data—depending on their specific objectives and risk tolerance.
Automated platforms are characterized as exceptionally efficient environments, frequently featuring integrated tools, real-time inventory, and instant purchasing capabilities. These operations mirror legitimate online marketplaces in both their structural organization and functional design, enabling users to rapidly acquire and test large volumes of compromised data. They cater to a broad base of users seeking speed and volume.
In stark contrast, boutique vendor groups prioritize exclusivity, consistently higher data quality, and tightly controlled access. These operations frequently rely on invitation-based membership systems and cultivate long-term, trusted relationships with a select clientele. They often specialize in more sensitive or harder-to-acquire data, appealing to more discerning or high-value fraudsters.
Commercial Imperatives and Operational Realities
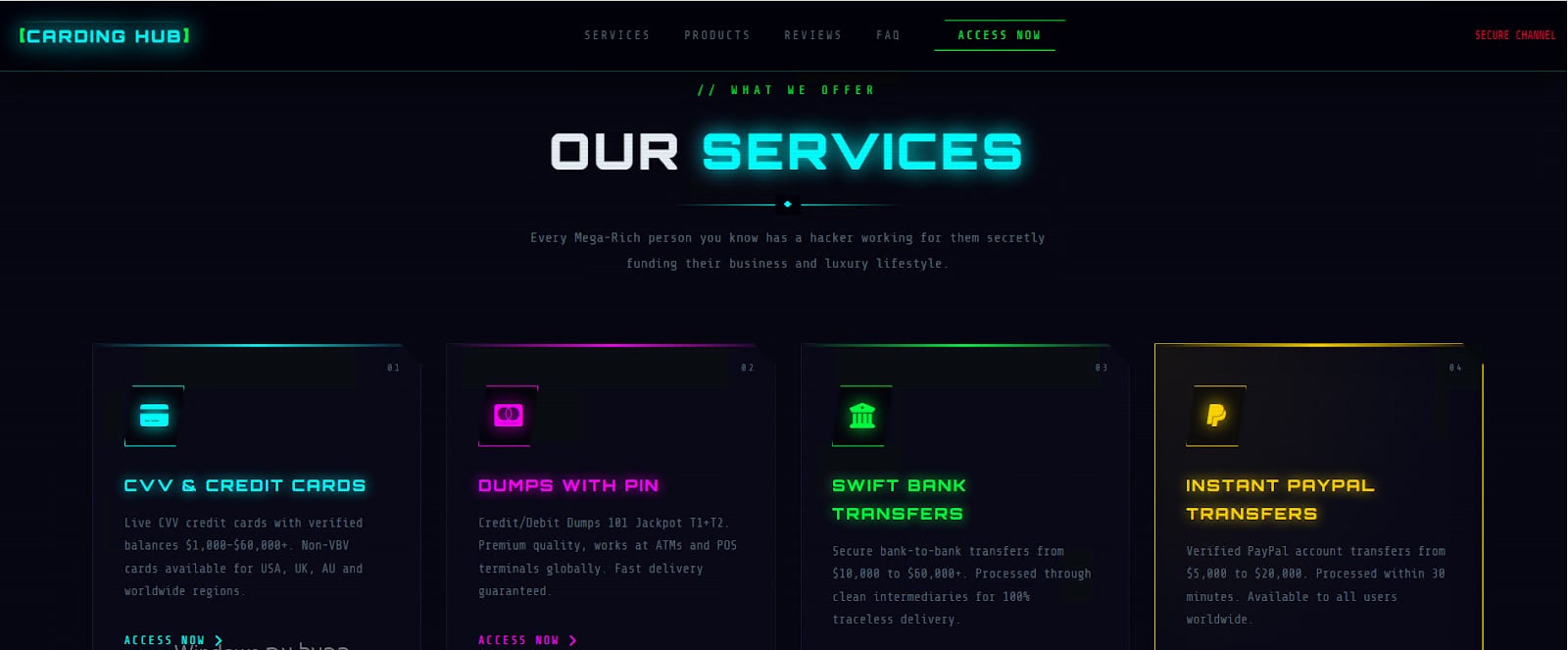
Despite its ostensibly structured and objective approach, the guide is not devoid of inherent biases. The explicit inclusion of a direct endorsement for a particular platform strongly suggests that the author may indeed possess a vested financial or reputational interest in promoting specific services. This phenomenon is a pervasive pattern within underground communities, where seemingly neutral informational content is frequently leveraged as a subtle vehicle for advertising, affiliate marketing, or reputation laundering.
Such endorsements, while providing a degree of insight into market preferences, should be interpreted with considerable caution. However, their presence does not necessarily invalidate the broader analytical insights provided by the guide itself. Instead, they serve to highlight the complex and often contradictory interplay between genuine information sharing and the commercial imperatives that drive cybercriminal ecosystems.
From a defensive standpoint, this detailed guide offers invaluable strategic intelligence regarding how threat actors assess risk, make critical operational decisions, and adapt to evolving threats. The pronounced emphasis on meticulous verification, community-driven validation, and layered security architecture reflects a level of operational maturity that significantly complicates traditional disruption efforts. Rather than exhibiting single points of failure, contemporary cybercriminal operations are increasingly characterized by redundancy, adaptability, and a proactive approach to mitigating vulnerabilities within their workflows.
Ultimately, this document functions as both a tactical playbook for aspiring fraudsters and a crucial signal for cybersecurity defenders. It unequivocally demonstrates that the carding ecosystem has evolved into a more structured, more cautious, and significantly more resilient illicit industry. For organizations tasked with protecting financial assets and preventing fraud, comprehending these intricate dynamics is absolutely critical for anticipating how these markets will continue to evolve, and for identifying where strategic opportunities for effective disruption may still exist. Understanding the adversary’s playbook is the first step towards dismantling their operations.






