
A sophisticated and expansive cyber campaign is currently exploiting the trusted communication channels of GitHub, specifically its Discussions feature, to disseminate malicious software. This operation strategically targets software developers by fabricating urgent security alerts for Visual Studio Code (VS Code) extensions, coercing unsuspecting users into downloading and executing malware. The intricate nature of this attack, combining social engineering with automated distribution, underscores a growing threat landscape where attackers meticulously mimic legitimate security practices to compromise development environments and, by extension, the broader software supply chain.
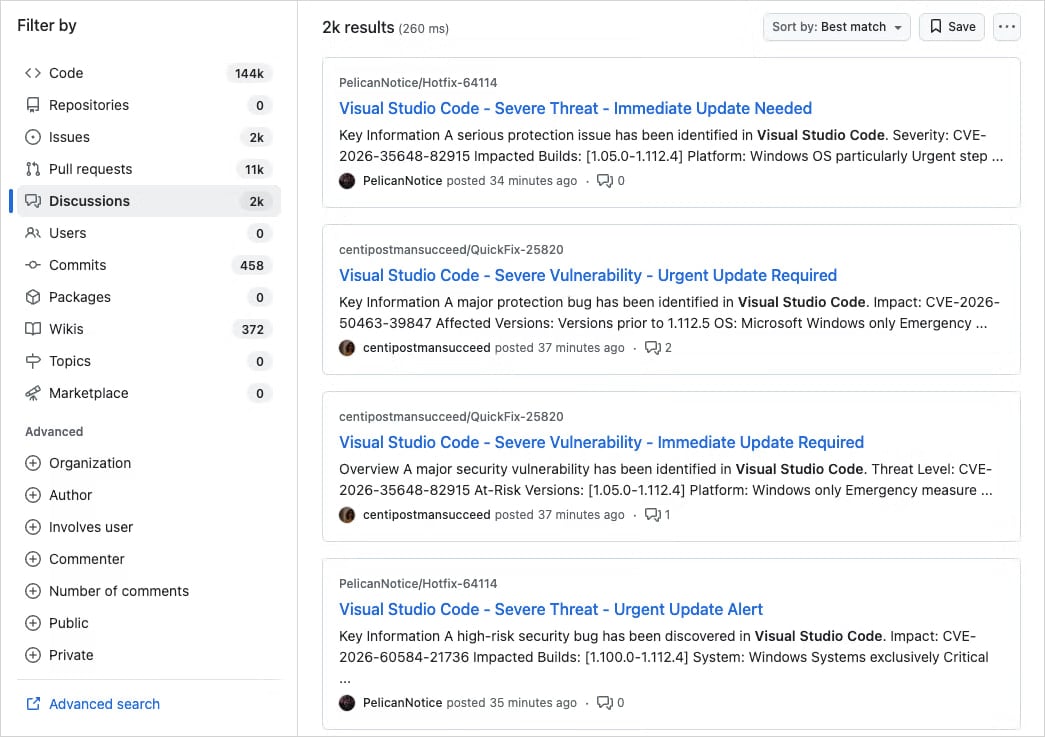
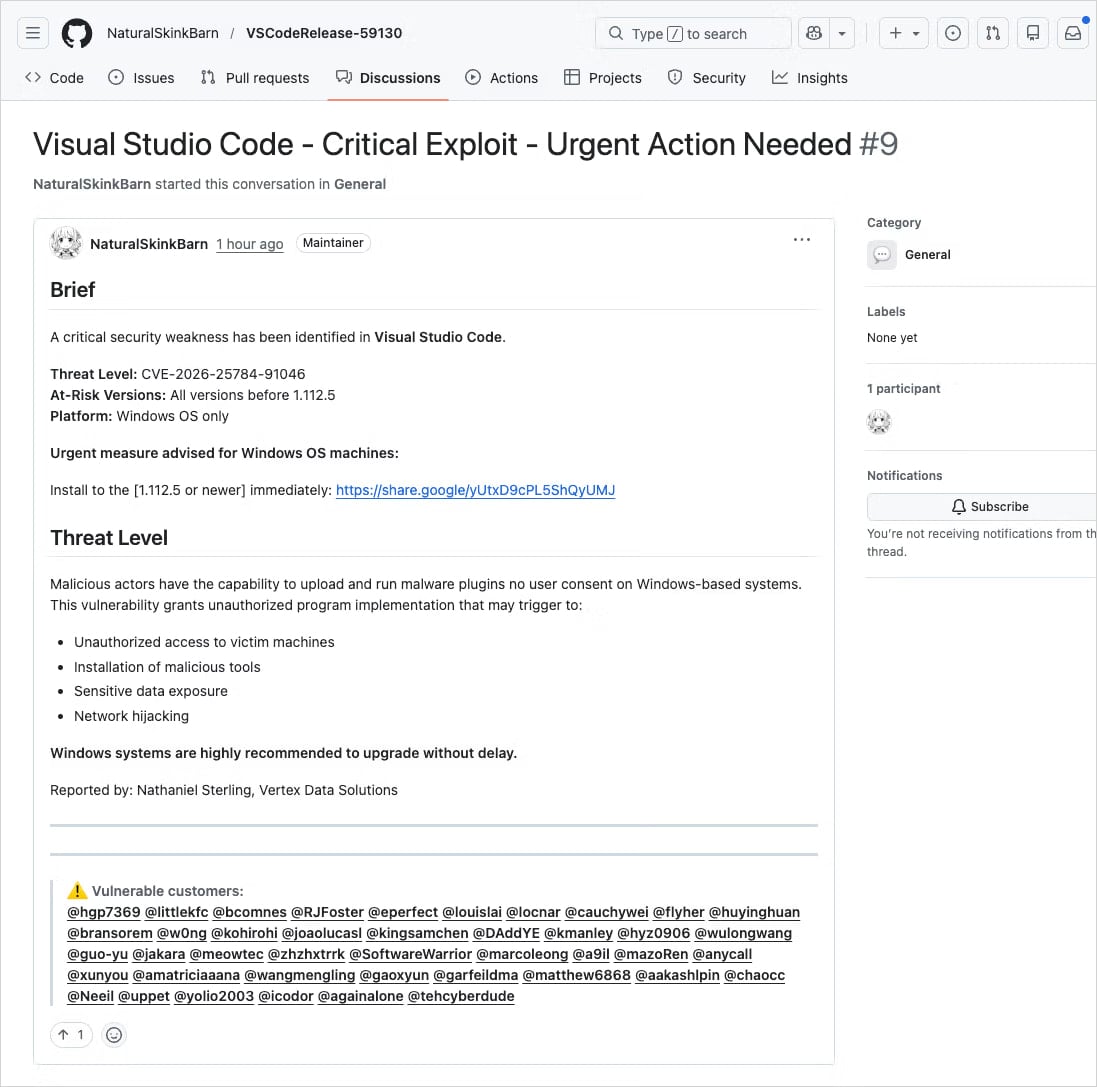
The core of this illicit operation involves the mass propagation of spurious vulnerability advisories within the Discussions sections of numerous GitHub projects. These fraudulent posts are meticulously crafted to appear authentic, often featuring compelling titles such as "Severe Vulnerability – Immediate Update Required" and incorporating fabricated Common Vulnerabilities and Exposures (CVE) identifiers. The language employed is designed to evoke a sense of crisis and urgency, pressuring developers to react swiftly without adequate scrutiny. Further enhancing their deceptive veneer, the threat actors frequently impersonate legitimate code maintainers or reputable security researchers, thereby leveraging established trust within the developer community to lend a false sense of credibility to their malicious communications.
Analysis by application security firm Socket indicates that this activity transcends the scope of opportunistic, narrowly targeted incidents. Instead, it manifests as a highly organized and large-scale endeavor, characterized by its systematic and automated deployment. The malicious discussions are disseminated with remarkable speed and breadth, originating from newly established or low-activity GitHub accounts that flood thousands of repositories within a condensed timeframe. This rapid, widespread posting strategy is particularly effective because GitHub Discussions are configured to trigger email notifications to project participants and followers, ensuring direct delivery of these deceptive alerts into a vast number of developers’ inboxes. This mechanism effectively bypasses many conventional email security filters that might otherwise flag suspicious external communications, positioning the malicious content within a context of presumed legitimacy.

The reported findings highlight the coordinated nature of the campaign, with researchers noting "thousands of nearly identical posts across repositories," confirming its status as a deliberate and expansive spam operation rather than an isolated occurrence. The direct delivery of these notifications to developers’ inboxes significantly amplifies the campaign’s reach, exploiting a fundamental feature of collaborative development platforms to achieve maximum exposure for the malicious content.
The deceptive posts invariably contain links purporting to lead to patched versions of the supposedly vulnerable VS Code extensions. However, these links redirect users to external hosting services, prominently Google Drive. While Google Drive is a widely recognized and generally trusted cloud service, its use as a primary distribution channel for official software updates, particularly for development tools like VS Code extensions, constitutes a significant red flag. Nevertheless, the urgency instilled by the fake security alerts, coupled with the inherent trust in the hosting service, can lead developers to overlook this critical anomaly and proceed with the download.
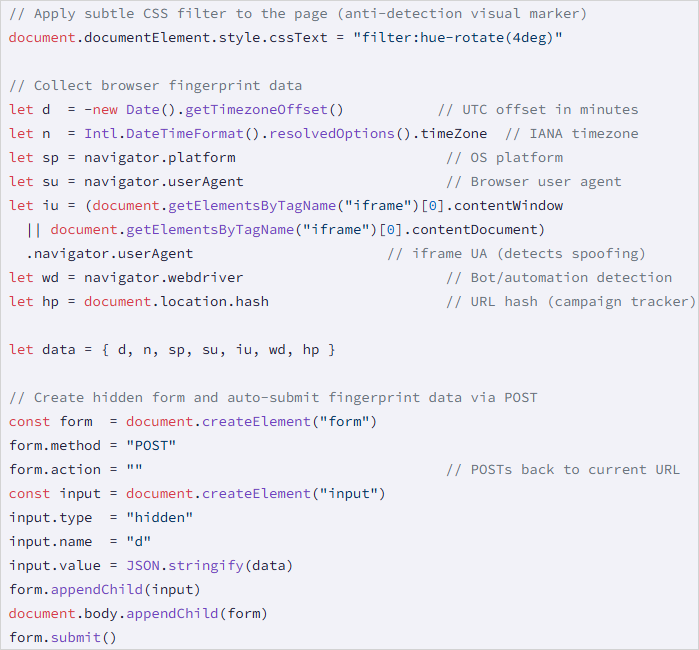
Upon clicking these external links, victims are subjected to a multi-stage redirection chain, often initiated by cookie-driven mechanisms, culminating in their navigation to a specific malicious domain, identified as drnatashachinn[.]com. This domain hosts a sophisticated JavaScript reconnaissance script, the primary objective of which is to meticulously profile the victim’s environment. The script collects a comprehensive array of data, including the victim’s timezone, locale settings, user agent string, operating system details, and various indicators of automation. This collected intelligence is then packaged and exfiltrated to a command-and-control (C2) server via a POST request.
This initial profiling stage serves as a critical traffic distribution system (TDS) filtering layer. Its purpose is to differentiate genuine developer targets from automated analysis tools, security researchers, or bots. By meticulously analyzing the collected data, the attackers can effectively filter out undesirable traffic, ensuring that the subsequent, more potent stages of the attack are only delivered to validated, high-value victims. While the specific second-stage payload was not fully captured during the analysis, it was noted that the JavaScript reconnaissance script does not directly deliver it, nor does it attempt to harvest credentials at this initial stage, suggesting a more complex, multi-layered infection process designed for stealth and persistence.
This incident is not an isolated phenomenon but rather indicative of a persistent and evolving trend where threat actors actively abuse legitimate GitHub notification systems to facilitate phishing and malware distribution. The open-source ecosystem, particularly platforms like GitHub, has become an increasingly attractive target for cybercriminals due given its central role in modern software development. Compromising a developer’s environment can grant attackers access to sensitive intellectual property, proprietary code, build pipelines, and even critical production infrastructure, making developers a high-value target in the broader supply chain attack landscape.
Historical precedents underscore the recurring nature of these threats. In March 2024 (or potentially 2025 as per original text, but 2024 is more likely given the current date), a widespread phishing campaign specifically targeted approximately 12,000 GitHub repositories. This campaign similarly leveraged fake security alerts, but its objective was to trick developers into authorizing a malicious OAuth application. Successful authorization would grant attackers unauthorized access to the victim’s GitHub account, potentially leading to code tampering, data exfiltration, or further supply chain compromise. More recently, in June 2024, threat actors manipulated GitHub’s email notification system by submitting spam comments and pull requests on various repositories. These actions were designed to direct targets to phishing pages, demonstrating the versatility and persistence of attackers in exploiting platform features for malicious ends.
The increasing sophistication of these attacks necessitates a robust and multi-faceted approach to security, both for individual developers and the organizations they serve. For developers, a fundamental shift towards a more critical and skeptical mindset when encountering security alerts is paramount. Verifying vulnerability identifiers in authoritative sources such as the National Vulnerability Database (NVD), CISA’s catalog of Known Exploited Vulnerabilities, or MITRE’s Common Vulnerabilities and Exposures (CVE) program should be a standard operating procedure. This proactive verification process can swiftly expose fraudulent claims lacking official corroboration.
Furthermore, developers must rigorously adhere to the principle of downloading software and updates exclusively from official, verified distribution channels. For VS Code extensions, this means the official VS Code Marketplace, and for other software, the project’s official GitHub releases page or dedicated vendor websites. Any deviation to external cloud storage services, regardless of their perceived trustworthiness, should immediately trigger alarm bells. Key indicators of fraud include the presence of external download links, unverifiable CVEs, and the mass tagging of unrelated users within the discussion threads. Developers should also be vigilant for subtle red flags such as unusual sender addresses in email notifications, grammatical inconsistencies in the alert text, or unexpected communication channels for security advisories. Implementing multi-factor authentication (MFA) on all GitHub accounts and adhering to the principle of least privilege in development environments further enhance security posture.
For organizations, the implications are significant, demanding comprehensive strategies to mitigate these evolving supply chain risks. Regular and targeted security awareness training for developers, specifically focused on social engineering tactics and the nuances of supply chain attacks, is crucial. Establishing and enforcing stringent security policies for software sourcing, installation, and dependency management can create a protective framework. The deployment of advanced Endpoint Detection and Response (EDR) solutions on developer workstations is essential for proactively monitoring and identifying suspicious activities that might bypass initial social engineering defenses. Additionally, integrating code signing and integrity checks into the software development lifecycle can help ensure the authenticity and integrity of development tools and dependencies.
Looking ahead, the arms race between cybercriminals and security defenders within the open-source ecosystem is poised to intensify. Platform providers like GitHub will need to continually enhance their automated detection capabilities, leveraging advanced AI and machine learning algorithms to identify and thwart spam, impersonation attempts, and malicious links within their extensive discussion and collaboration features. Implementing stricter rate limiting for new or low-activity accounts posting across numerous repositories could deter automated campaign deployment. Improving user-friendly and effective reporting mechanisms for suspicious activity is also vital, empowering the community to act as an early warning system. Furthermore, exploring features such as automated warning labels for external links within discussions could provide an additional layer of defense for unsuspecting users. The developer environment remains a high-value target, and the ongoing vigilance, education, and implementation of robust security measures will be paramount in safeguarding the integrity and trustworthiness of the global software supply chain.






