
The leading residential security services provider, ADT, has formally acknowledged a substantial data breach, confirming that an intrusion into its systems led to the exfiltration of sensitive customer and prospective customer information. This confirmation arrives in the wake of public claims by the notorious cyber extortion collective, ShinyHunters, which threatened to disseminate the stolen data unless a monetary payment was rendered. The incident underscores the persistent and evolving threat landscape facing even established security entities, highlighting the critical vulnerabilities within corporate digital infrastructures, particularly those involving third-party service providers and human elements.
ADT’s internal security teams first detected unauthorized activity within their digital environment on April 20. Prompt and decisive action was taken to contain the intrusion, effectively terminating the illicit access and initiating a comprehensive forensic investigation to ascertain the scope and nature of the compromise. The subsequent inquiry meticulously analyzed the affected systems and data repositories, ultimately confirming that personal information belonging to a segment of its vast customer base and individuals who had previously engaged with the company was indeed accessed and removed by the malicious actors.
According to statements issued by the company, the compromised data was primarily limited to foundational personal identifiers. This included names, residential addresses, and telephone numbers. In a smaller, yet still significant, subset of the affected records, more sensitive details such as dates of birth and the final four digits of Social Security numbers or Tax Identification numbers were also implicated. Critically, ADT has emphasized that no financial account information, including bank account details or credit card numbers, was compromised during the incident. Furthermore, the company assured that its core customer security systems remained unbreached and operational, mitigating immediate concerns regarding the physical security of its subscribers’ premises. In response to the confirmed breach, ADT has initiated direct communication with all individuals identified as being impacted by the data exfiltration, adhering to regulatory notification requirements and providing guidance on potential next steps.

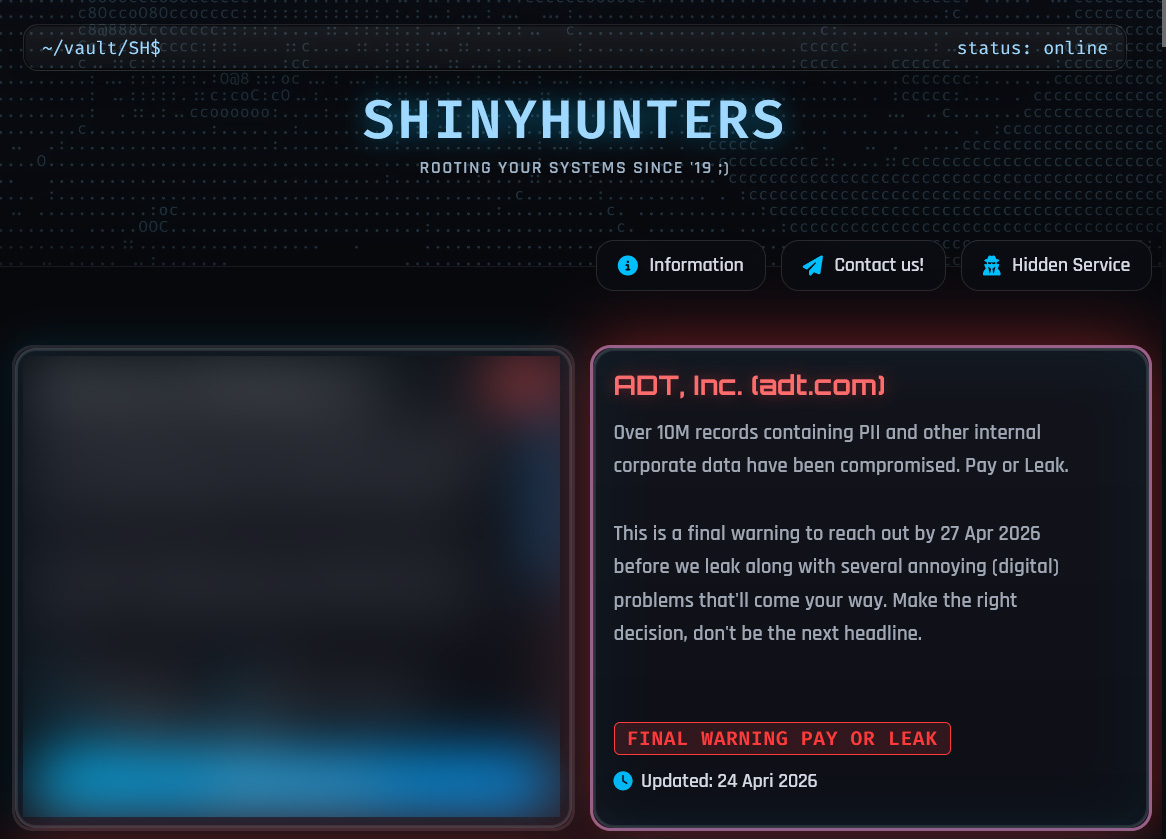
The corporate acknowledgment followed a public declaration by ShinyHunters on their dark web data leak portal. The extortion group asserted that they had successfully pilfered an extensive trove of information, claiming to possess over 10 million records containing personally identifiable information (PII) and various categories of internal corporate data. The group’s message on the leak site served as an ultimatum, stating, "Over 10M records containing PII and other internal corporate data have been compromised. Pay or Leak." A specific deadline of April 27, 2026, was stipulated for ADT to engage in ransom negotiations, accompanied by a veiled threat of "several annoying (digital) problems" should the company fail to comply. While ADT has confirmed the breach and the nature of the data involved, the company has refrained from corroborating the precise volume of stolen data as alleged by ShinyHunters.
ShinyHunters, in direct communication with media outlets, detailed their methodology for infiltrating ADT’s systems. The group claimed to have leveraged a sophisticated voice phishing, or "vishing," attack. This social engineering technique targeted an ADT employee, manipulating them into compromising their Okta single sign-on (SSO) account credentials. Once the Okta SSO account was illicitly accessed, the threat actors reportedly exploited this gateway to penetrate and exfiltrate data from ADT’s Salesforce instance, a critical customer relationship management (CRM) platform. This account of the attack vector aligns with ShinyHunters’ established operational tactics.
The group has, over the past year, been implicated in a series of widespread vishing campaigns specifically designed to compromise SSO accounts across various platforms, including Microsoft Entra (formerly Azure AD), Okta, and Google Workspace. Their targets often include employees of large corporations and business process outsourcing (BPO) agents, recognizing that these individuals frequently possess access to sensitive corporate resources. The efficacy of vishing lies in its ability to bypass technical security controls by exploiting human trust and vulnerability, often leading employees to inadvertently disclose credentials or grant access under false pretenses. This method represents a significant evolution from traditional email-based phishing, leveraging real-time voice interaction to build rapport and urgency, making detection and defense more challenging.

Once unauthorized access to a corporate SSO account is established, the threat actors gain an invaluable foothold, essentially acquiring "keys to the kingdom" for a wide array of connected Software-as-a-Service (SaaS) applications. These applications, central to modern business operations, can include platforms like Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, and Dropbox. The stolen data typically spans customer records, internal communications, intellectual property, and operational intelligence. The subsequent extortion model employed by ShinyHunters is straightforward: demand a ransom payment from the victim organization, with the explicit threat of publicly leaking the exfiltrated data if their demands are not met. This strategy not only pressures the victim financially but also leverages reputational damage and regulatory penalties as additional motivators for payment.
For ADT, a company whose very brand is synonymous with security and trust, this incident carries substantial implications beyond the immediate financial and operational burdens. A data breach, particularly one facilitated by social engineering and targeting customer data, can severely erode customer confidence. Customers entrust ADT not only with their physical security but also with their personal information, and any compromise of that data can lead to a significant breach of that trust. The reputational damage for a security provider can be particularly acute, potentially impacting customer retention and future sales. Moreover, the incident will undoubtedly trigger intense scrutiny from regulatory bodies, given the involvement of PII and potentially stricter data protection laws such as GDPR, CCPA, and various state-level data breach notification statutes. Non-compliance or inadequate protection of data can result in substantial fines and legal challenges, including potential class-action lawsuits from affected individuals seeking damages.
This is not an isolated incident for ADT, which has previously disclosed other data breaches in recent history. The company confirmed a breach in August and another in October 2024, both of which exposed customer and employee information. The recurrence of such incidents underscores a potential systemic vulnerability within the organization’s security posture or a persistent targeting by sophisticated threat actors. It raises critical questions about the effectiveness of existing security protocols, employee training, and third-party vendor risk management. Each subsequent breach amplifies the reputational damage and increases the pressure on the company to demonstrate a robust and resilient cybersecurity strategy.
The ADT breach serves as a stark reminder of the broader cybersecurity challenges confronting enterprises globally. The increasing reliance on cloud-based SaaS applications, while offering flexibility and scalability, also expands the attack surface. Many organizations struggle with securing these environments, especially when access is predicated on SSO solutions that, if compromised, can lead to widespread data exfiltration. The "human element" continues to be identified as the weakest link in the security chain, with social engineering attacks like vishing proving highly effective against even well-trained employees. This trend necessitates a multi-layered defense strategy that not only focuses on technical safeguards but also heavily invests in continuous security awareness training, simulating real-world attack scenarios to harden employee resilience against manipulation.
To mitigate such risks, organizations must adopt comprehensive cybersecurity frameworks that include robust multi-factor authentication (MFA) across all critical systems, particularly for SSO accounts. Implementing stringent access controls, regular security audits of both internal systems and third-party SaaS vendors, and advanced threat detection capabilities like Endpoint Detection and Response (EDR) and Security Information and Event Management (SIEM) are paramount. Furthermore, cultivating a strong security culture within the organization, where every employee understands their role in protecting corporate assets, is indispensable. Incident response plans must be meticulously developed, regularly tested, and refined to ensure rapid detection, containment, and recovery from breaches, thereby minimizing their impact.
Looking ahead, the landscape of cyber extortion is likely to grow in complexity and audacity. Threat actors like ShinyHunters will continue to innovate their attack vectors, targeting the most vulnerable points in an organization’s defenses. The monetization of stolen data, whether through direct ransom or sale on underground markets, remains a powerful incentive for these groups. Enterprises, particularly those managing vast quantities of sensitive customer data, must prioritize proactive and adaptive security measures. This includes investing in threat intelligence to anticipate emerging attack methodologies, implementing zero-trust architectures, and fostering strong partnerships with cybersecurity experts. The imperative for continuous vigilance, technological advancement, and human education in cybersecurity has never been more critical, as organizations navigate an increasingly hostile digital environment where data integrity and customer trust are perpetually under assault.






