
A sophisticated ransomware operation, identified as Payouts King, has adopted an innovative evasion tactic by deploying QEMU-based virtual machines (VMs) on compromised systems. This strategy establishes a stealthy reverse SSH backdoor, effectively creating an isolated environment for malicious activities that circumvents conventional endpoint security mechanisms and complicates detection. The technique represents a significant escalation in the cat-and-mouse game between threat actors and cybersecurity defenses, highlighting the evolving sophistication of ransomware attacks.
QEMU, an acronym for Quick Emulator, is a widely recognized open-source hardware virtualization tool capable of performing both hardware virtualization and full system emulation. It allows guest operating systems to run within a virtualized environment on a host system, isolated from the host’s native operations. While QEMU serves legitimate purposes in development, testing, and system administration, its inherent capability to create isolated execution environments makes it a potent tool for malicious actors seeking to obscure their presence and activities from security software designed to monitor the host operating system.
The fundamental advantage for threat actors in utilizing QEMU lies in its ability to establish a "blind spot" within the target network. Host-based security solutions, including Endpoint Detection and Response (EDR) platforms, typically lack the visibility to inspect the internal operations of a running virtual machine. This opacity enables attackers to execute payloads, store malicious tools, stage data for exfiltration, and establish persistent, covert command-and-control (C2) channels without triggering alerts from the host’s security stack. The reverse SSH backdoor mechanism further enhances this stealth, as it initiates an outbound connection from the compromised host to an attacker-controlled server. Outbound connections are often less scrutinized by network perimeter defenses than inbound attempts, allowing for more discreet communication and data transfer.
The abuse of virtualization technologies for malicious ends is not an entirely new phenomenon; previous campaigns have demonstrated similar tactics. For instance, the 3AM ransomware group, the LoudMiner cryptomining operation, and the ‘CRON#TRAP’ phishing attacks have all been documented leveraging QEMU or similar virtualization techniques to achieve their objectives. However, Payouts King’s integration of this method, particularly within the context of a ransomware lifecycle, underscores a growing trend towards more elaborate and harder-to-detect attack methodologies.
Recent analyses by cybersecurity researchers have illuminated two distinct campaigns where QEMU played a pivotal role in the threat actors’ arsenal, specifically in facilitating credential harvesting and broader network compromise. One campaign, tracked as STAC4713, has been directly linked to the Payouts King ransomware operation, with initial observations dating back to November 2025. Another campaign, identified as STAC3725, emerged in February of the current year and capitalizes on the CitrixBleed 2 vulnerability (CVE-2025-5777) affecting NetScaler ADC and Gateway instances. These parallel developments indicate a broader embrace of virtualization-based evasion across different threat groups or highly adaptive operational tactics within a single sophisticated entity.
The Modus Operandi of Payouts King (STAC4713): A Deep Dive

The STAC4713 campaign, attributed to the GOLD ENCOUNTER threat group, known for its expertise in targeting hypervisors and encrypting VMware and ESXi environments, demonstrates a meticulous approach to infiltration and persistence. Their proficiency in virtualized environments makes their adoption of QEMU a logical extension of their capabilities.
Initial access vectors for GOLD ENCOUNTER have been diverse, reflecting a willingness to exploit multiple entry points. Early attacks frequently leveraged exposed SonicWall VPNs. More recent incidents have seen exploitation of the SolarWinds Web Help Desk vulnerability (CVE-2025-26399). Beyond technical vulnerabilities, social engineering remains a potent tool; in a February attack, an exposed Cisco SSL VPN was compromised, while in March, the group impersonated IT staff on Microsoft Teams, tricking employees into downloading and installing QuickAssist. This multi-pronged approach to initial compromise highlights the importance of comprehensive security across an organization’s attack surface.
Upon gaining initial access, the threat actors establish persistence and deploy their stealthy VM environment. This is achieved by creating a scheduled task named "TPMProfiler," which is configured to launch a hidden QEMU VM with SYSTEM privileges. The virtual disk files necessary for the VM’s operation are ingeniously disguised as innocuous database or DLL files, further aiding in obfuscation. Crucially, port forwarding is configured to facilitate a reverse SSH tunnel, providing the attackers with covert remote access to the infected host without requiring direct inbound connections that might be blocked by firewalls.
The operating system chosen for the attacker’s VM is Alpine Linux version 3.22.0. Alpine Linux is a lightweight, security-oriented distribution known for its minimal footprint and efficiency, making it an ideal choice for a stealthy, resource-efficient malicious VM. Inside this isolated environment, the attackers deploy a suite of specialized tools:
- AdaptixC2: A sophisticated command-and-control framework used for managing compromised systems.
- Chisel: A fast TCP/UDP tunnel over HTTP, enabling attackers to bypass firewalls and establish covert communication channels.
- BusyBox: A collection of essential Unix utilities in a single executable, offering a minimal yet comprehensive toolkit for system interaction within the VM.
- Rclone: A versatile command-line program for managing files on cloud storage, critical for data exfiltration to remote SFTP locations.
In the post-infection phase, the attackers demonstrate a clear understanding of Windows internals and data exfiltration techniques. They leverage the Volume Shadow Copy Service (VSS) via vssuirun.exe to create shadow copies, allowing them to access and copy sensitive system files like NTDS.dit (containing Active Directory database), SAM (Security Account Manager, storing local user hashes), and SYSTEM hives (containing system-wide configuration data, including encrypted credentials). These files are then copied to temporary directories, often using the print command over SMB, before being exfiltrated.
Further emphasizing their advanced tactics, GOLD ENCOUNTER employs binary sideloading. In observed instances, they used the legitimate ADNotificationManager.exe binary to load a Havoc C2 payload, disguised as vcruntime140_1.dll. This technique abuses trusted processes to execute malicious code, making detection more challenging. The exfiltrated data is then transferred to a remote SFTP location, typically facilitated by Rclone, ensuring efficient and encrypted data transfer.

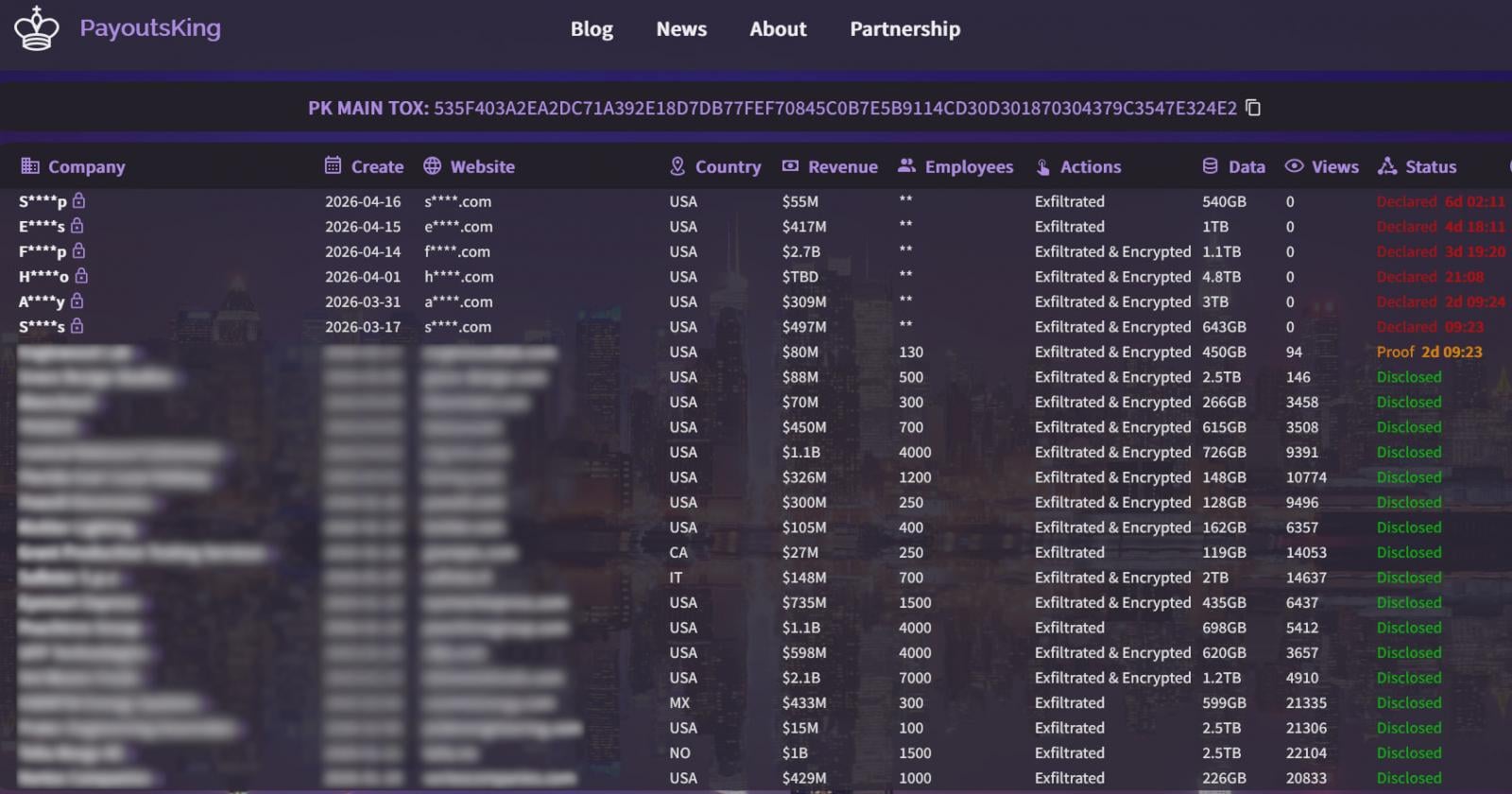
The Payouts King ransomware itself is characterized by heavy obfuscation and anti-analysis mechanisms, designed to hinder reverse engineering and evade security tools. It establishes persistence through scheduled tasks, a common but effective method, and notably terminates security tools using low-level system calls, demonstrating a deep understanding of operating system internals. The encryption scheme employed is AES-256 (CTR) with RSA-4096, often utilizing intermittent encryption for larger files. Intermittent encryption selectively encrypts portions of a file, speeding up the encryption process and making recovery more difficult without the key, while also potentially reducing the chances of detection by behavioral analysis tools looking for full file encryption patterns. The dropped ransom notes guide victims to leak sites hosted on the dark web, a standard double-extortion tactic.
The CitrixBleed 2 Campaign (STAC3725): Another Facet of VM Abuse
The STAC3725 campaign, active since February, represents another sophisticated use of virtualization, albeit with a different initial access vector. This campaign exploits the CitrixBleed 2 vulnerability (CVE-2025-5777) to breach NetScaler ADC and Gateway instances, critical components in many corporate networks.
Once NetScaler devices are compromised, the attackers deploy a ZIP archive containing a malicious executable. This executable installs a service named "AppMgmt," creates a new local administrator user (CtxAppVCOMService), and installs a ScreenConnect client. ScreenConnect is a legitimate remote access tool, and its abuse provides the attackers with persistent access to the compromised system with system privileges. The client connects to a remote relay server, establishing a session that bypasses many network restrictions.
Following the establishment of persistent access, the attackers deploy and extract a QEMU package. A hidden Alpine Linux VM is then launched using a custom .qcow2 disk image. Unlike the Payouts King campaign that relies on a pre-built toolkit, the attackers in STAC3725 manually install and compile their tools within the VM. This approach allows for greater customization, potentially tailoring tools to specific target environments and making them harder to detect by signature-based security solutions. The toolkit includes:
- Impacket: A collection of Python classes for working with network protocols, often used for Active Directory enumeration and exploitation.
- KrbRelayx: A tool for Kerberos relay attacks.
- Coercer: Likely a tool used for credential dumping or privilege escalation.
- BloodHound.py: A Python-based ingestor for BloodHound, used for visualizing and exploiting Active Directory attack paths.
- NetExec: A network exploitation tool.
- Kerbrute: A tool for Kerberos username enumeration.
- Metasploit: A widely used penetration testing framework.
The observed activities within this VM environment include extensive credential harvesting, Kerberos username enumeration, and Active Directory reconnaissance—all precursors to lateral movement and privilege escalation. Data is then staged for exfiltration via FTP servers, indicating a focus on data theft alongside potential ransomware deployment.

Attribution and Linkages
Intelligence reports from Zscaler further strengthen the understanding of Payouts King, suggesting a strong likelihood of its ties to former BlackBasta affiliates. This connection is based on shared initial access methods, including spam bombing, Microsoft Teams phishing, and the abuse of Quick Assist, all tactics previously associated with BlackBasta operations. This highlights the dynamic nature of the ransomware ecosystem, where experienced individuals or subgroups often transition between different operations, bringing their refined tactics, techniques, and procedures (TTPs) with them. Such evolution underscores the importance of tracking TTPs rather than solely focusing on specific malware families.
Implications and Challenges for Cybersecurity Defenders
The sophisticated use of QEMU VMs by groups like Payouts King presents significant challenges for modern cybersecurity defenses:
- Evasion of Host-Based Security: The primary implication is the creation of an execution environment largely invisible to traditional EDR and antivirus solutions operating on the host. This renders a crucial layer of defense ineffective against activities within the VM.
- Detection Difficulties: The combination of legitimate tool abuse (QEMU, ScreenConnect, Rclone, VSS), sophisticated obfuscation, low-level system calls to terminate security software, and disguised virtual disk files makes detection exceptionally difficult. Behavioral analysis, while more robust, must contend with activities occurring in an isolated, opaque environment.
- Resource Consumption as a Double-Edged Sword: While running a VM consumes host resources (CPU, RAM, disk I/O), which could theoretically serve as a detection indicator, these anomalies are often overlooked or dismissed as normal system fluctuations, especially in busy server environments.
- Sophistication and Skill Requirement: Deploying and managing QEMU VMs, configuring reverse SSH tunnels, and assembling a custom toolkit requires a higher degree of technical skill and operational maturity from the attackers, signaling a more dangerous adversary.
- Undermining Zero Trust: This technique directly challenges the principles of Zero Trust architectures, which assume no inherent trust inside or outside the network. By creating an unmonitored enclave, attackers can bypass micro-segmentation and access controls from within a trusted host.
Defensive Strategies and Recommendations
To counter such advanced evasion techniques, organizations must adopt a multi-layered, proactive defense strategy:
-
Enhanced Visibility and Monitoring:
- QEMU Installation Detection: Implement robust monitoring for unauthorized installations of QEMU or similar virtualization software on endpoints and servers. This includes file system monitoring for QEMU executables and libraries.
- Scheduled Task Analysis: Scrutinize scheduled tasks, particularly those running with SYSTEM privileges, for unusual names (e.g., "TPMProfiler") or commands.
- Network Anomaly Detection: Monitor network traffic for unusual SSH port forwarding, especially outbound SSH tunnels on non-standard ports. Behavioral analysis of network connections can identify deviations from baselines.
- Resource Usage Baselines: Establish baselines for CPU, memory, and disk I/O. Alert on significant, sustained deviations that could indicate a hidden VM.
- Process Monitoring: Monitor for suspicious process creations, especially those that launch virtualization components or legitimate tools in unusual contexts.
- User and Account Monitoring: Alert on the creation of new local administrator accounts (e.g., CtxAppVCOMService) or services, which often indicate compromise.
-
Proactive Security Measures:
- Vulnerability Management and Patching: Aggressively patch all internet-facing devices, VPNs (SonicWall, Cisco SSL VPN), remote access solutions (Citrix NetScaler), and critical software (SolarWinds Web Help Desk) to eliminate common initial access vectors.
- Application Whitelisting: Implement strict application whitelisting to prevent the execution of unauthorized programs, including virtualization software like QEMU, unless explicitly approved.
- Least Privilege Principle: Enforce the principle of least privilege for all users and services, limiting the potential impact of a compromise.
- Network Segmentation: Implement strong network segmentation to limit lateral movement, even if an endpoint is compromised.
- Advanced EDR/XDR: Deploy EDR or XDR solutions capable of deep behavioral analysis, process-level introspection, and cross-platform correlation to detect anomalous activities that might indicate a VM operating under the radar.
- Security Awareness Training: Conduct regular and effective security awareness training to educate employees about social engineering tactics, such as Microsoft Teams phishing and Quick Assist abuse, to prevent initial compromise.
- Active Directory Security: Implement robust Active Directory security practices, including strong password policies, multi-factor authentication, and continuous monitoring for suspicious activity like Kerberos enumeration and credential harvesting.
- Data Exfiltration Monitoring: Monitor for unusual data access patterns, especially attempts to copy sensitive system files like NTDS.dit, SAM, and SYSTEM hives, and track large outbound data transfers.
Future Outlook
The Payouts King ransomware’s adoption of QEMU VMs signals a critical evolution in the ransomware landscape. As traditional endpoint security becomes more sophisticated, threat actors will continue to seek novel methods to operate stealthily within compromised environments. The abuse of legitimate tools and the creation of isolated execution spaces are likely to become more prevalent. This trend necessitates a shift in defensive paradigms, moving beyond signature-based detection to comprehensive behavioral analytics, deep system introspection, and an unwavering focus on visibility across the entire IT estate. The arms race will continue, demanding constant adaptation and innovation from cybersecurity professionals to stay ahead of increasingly clever adversaries.






