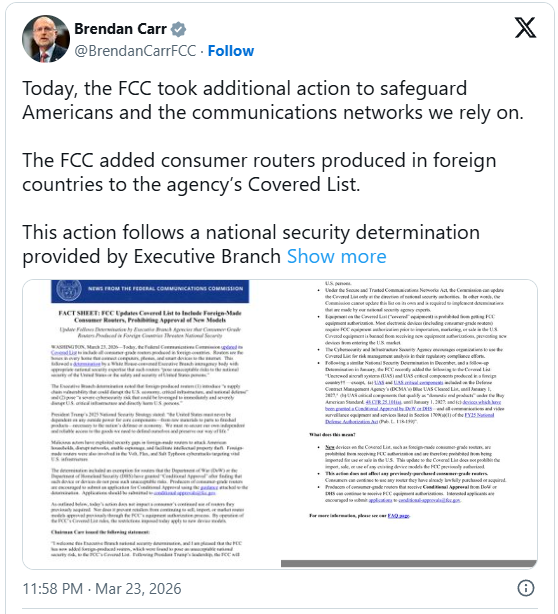
In a decisive move aimed at fortifying national cybersecurity infrastructure and safeguarding critical systems, the Federal Communications Commission (FCC) has significantly expanded its "Covered List," effectively prohibiting the sale of new consumer-grade routers produced outside the United States. This unprecedented regulatory action marks a pivotal escalation in the nation’s strategy to mitigate pervasive supply chain vulnerabilities within its communication networks, signaling a clear commitment to domestic security over globalized manufacturing paradigms for essential internet hardware.
The FCC’s determination to include all foreign-made consumer routers on its "Covered List" stems from a comprehensive National Security Determination issued on March 20 by an interagency body within the Executive Branch. This designation, enacted under the stringent provisions of the Secure and Trusted Communications Networks Act of 2019, identifies communication equipment and services deemed to pose an unacceptable risk to U.S. national security or the safety and security of American citizens. The act itself was a legislative response to growing concerns over foreign adversaries exploiting technological dependencies to compromise vital infrastructure and pilfer sensitive data.
Historically, the Covered List has targeted specific entities and products associated with documented security threats. Previous inclusions have featured companies such as Kaspersky, recognized for its software’s potential vulnerabilities and ties to foreign intelligence; telecommunications giants Huawei and ZTE, implicated in espionage and data exfiltration; and surveillance technology providers Hikvision and Dahua, whose equipment has been linked to human rights abuses and potential data harvesting for foreign governments. The latest amendment, however, represents a dramatic expansion, moving beyond individual company-specific prohibitions to a broad, country-of-origin criterion for an entire class of consumer devices. This shift underscores a recognition that the threat landscape has broadened, necessitating a more systemic approach to supply chain integrity.
The National Security Determination provided a stark assessment, articulating that routers produced abroad inherently carry a profound supply-chain risk. This risk profile, according to the interagency analysis, encompasses the potential for these devices to be exploited in ways that "could disrupt the U.S. economy, critical infrastructure, and national defense." Furthermore, the determination explicitly warned that compromised routers could be leveraged "to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons." The underlying concerns center on potential hardware backdoors, malicious firmware injections, or undisclosed vulnerabilities that could be exploited by state-sponsored actors or sophisticated criminal organizations. Such exploits could facilitate widespread surveillance, data exfiltration, or coordinated denial-of-service attacks, crippling essential services ranging from energy grids and financial systems to emergency services and telecommunications networks.
In support of its decision, the FCC cited specific instances where foreign-manufactured routers were instrumental in facilitating sophisticated cyberattacks against vital U.S. infrastructure. The agency highlighted the activities of threat groups identified as Volt, Flax, and Salt Typhoon. These advanced persistent threat (APT) actors have been linked to campaigns targeting various sectors of U.S. critical infrastructure, employing stealthy tactics to gain and maintain access to sensitive networks. The involvement of foreign-made routers in these attacks suggests that these devices may have served as initial compromise points, persistent backdoors, or command-and-control relays, demonstrating their utility as vectors for malicious activity by hostile state actors. The FCC’s emphasis on these concrete examples underscores the urgency and necessity of addressing the vulnerabilities inherent in a globalized router supply chain.
Strategic Exemptions and Rigorous Approval Pathways
While the FCC’s new directive establishes a broad prohibition, it also delineates specific exemptions and an alternative, highly stringent approval process for foreign manufacturers. Notably, conditional approval has been granted for certain router systems utilized by the Department of War (DoW) and the Department of Homeland Security (DHS), particularly those integrated into Unmanned Aircraft Systems (UAS). This specific carve-out suggests a recognition of specialized operational requirements and the implementation of bespoke security protocols within these critical defense and security sectors, which likely involve intensive vetting, bespoke hardening, and continuous monitoring, thereby mitigating the perceived security risks.
Moreover, the new regulatory framework does not entirely preclude foreign consumer-grade router manufacturers from entering the U.S. market. Instead, it establishes a demanding alternative certification pathway. To be considered for approval, manufacturers must provide unprecedented levels of transparency and commit to significant operational restructuring. Key requirements for this pathway include:
- Comprehensive Disclosure: Manufacturers are mandated to transparently disclose detailed information regarding their product’s design, internal components, software architecture, and firmware. This likely extends to providing access to source code for independent security audits, detailing the origin and supply chain of all sub-components, and outlining the entire manufacturing process from raw materials to final assembly.
- Onshoring Requirements: A critical, albeit implicitly detailed, condition for approval involves a significant onshoring or trusted-shoring component. This implies that critical aspects of the router’s production, assembly, or perhaps even core intellectual property development, must occur within the United States or within nations deemed trusted allies. This requirement aims to reduce the attack surface within the supply chain by bringing manufacturing processes under the purview of U.S. oversight and regulatory standards, thereby minimizing opportunities for malicious hardware or firmware injection at the point of origin.
- Rigorous Testing and Certification: Any router seeking approval via this alternative pathway will be subjected to an exhaustive battery of security tests, evaluations, and FCC certification processes. This will likely involve independent third-party penetration testing, vulnerability assessments, and compliance checks against established U.S. cybersecurity standards. This multi-layered scrutiny is designed to ensure that even if components or design elements originate abroad, the final product adheres to the highest security benchmarks before being introduced to the American market.
Profound Implications for Consumers and Industry Dynamics
For the vast majority of U.S. consumers, the immediate impact of these new regulations is expected to be minimal. All existing router models currently in circulation or inventory will remain legal for sale and use. Furthermore, the FCC has extended a grace period until at least January 1, 2027, for software and firmware updates for Unmanned Aircraft Systems (UAS) and their critical components, allowing for a phased transition.
However, the long-term implications for the consumer market and the broader technology industry are substantial and multifaceted:
- Reduced Product Availability: The most direct consequence for consumers will likely be a reduction in the diversity and number of new router models available in the U.S. market. Many foreign manufacturers, particularly smaller or mid-sized enterprises, may find the stringent new certification requirements, the extensive disclosure mandates, and especially the implicit or explicit onshoring requirement to be prohibitively complex and expensive. The decision to exit the U.S. market rather than undergo a costly and uncertain approval process could lead to fewer choices for consumers.
- Increased Costs: The additional layers of regulatory approval, extensive security testing, potential manufacturing relocation or diversification, and legal compliance will inevitably translate into higher production costs for manufacturers. These increased costs are highly likely to be passed on to consumers in the form of more expensive router models, impacting affordability and potentially widening the digital divide.
- Delayed Market Entry: The process of obtaining conditional approval, conducting rigorous testing, and securing FCC certification is inherently time-consuming. Even under ideal circumstances, meeting all the new conditions could extend product development and market entry timelines by several months, if not longer. This could mean that U.S. consumers will have delayed access to the latest router technologies and innovations compared to other global markets.
- Market Consolidation and Domestic Boost: The new rules are poised to reshape the competitive landscape. Larger, well-resourced multinational corporations or established domestic manufacturers may be better positioned to absorb the costs and complexities of compliance, potentially leading to market consolidation. Conversely, this regulatory shift could provide a significant impetus for domestic router manufacturing and innovation within the U.S., fostering the growth of American companies that can meet the "trusted supply chain" criteria.
- Supply Chain Reconfiguration: The onshoring requirement, in particular, will necessitate a fundamental reevaluation and reconfiguration of global supply chains. Manufacturers may need to invest heavily in establishing production facilities within the U.S. or allied nations, fostering new domestic component suppliers, and rethinking their entire logistical framework. This strategic pivot has significant geopolitical and economic ramifications, potentially leading to a more localized and resilient, albeit initially more expensive, technology supply ecosystem.
- Impact on Innovation: While the intent is to enhance security, there is a potential for this stringent regulation to inadvertently stifle innovation in the short term, as manufacturers prioritize compliance over rapid feature development. However, in the long term, it could also spur innovation in secure design principles, trusted manufacturing processes, and domestic technological capabilities.
This sweeping ban by the FCC represents a critical juncture in the U.S.’s ongoing efforts to secure its digital frontiers. By directly addressing the systemic vulnerabilities within the consumer router supply chain, the nation is taking a proactive stance against an evolving array of cyber threats. While the transition may present challenges for both industry and consumers, the long-term objective is a more resilient, secure, and trustworthy communication infrastructure, foundational to national security and economic stability in the digital age. The effectiveness of this policy will ultimately hinge on its implementation, the industry’s adaptability, and the continued vigilance against sophisticated cyber adversaries.






