
The Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent directive to U.S. federal civilian executive branch (FCEB) agencies, compelling immediate remediation of three actively exploited vulnerabilities within Apple’s iOS operating system. These security flaws, integral to the sophisticated DarkSword exploit kit, have been leveraged by advanced persistent threat (APT) actors in campaigns targeting sensitive data, including cryptocurrency assets, and engaging in cyberespionage activities. This mandate underscores the critical threat posed by mobile device compromises to governmental infrastructure and sensitive information, requiring a swift and comprehensive security response across the federal landscape.
The DarkSword exploit kit represents a significant escalation in mobile threat capabilities, employing a complex chain of six distinct vulnerabilities to achieve deep system compromise. Specifically, the flaws identified as CVE-2025-31277, CVE-2025-43529, CVE-2026-20700, CVE-2025-14174, CVE-2025-43510, and CVE-2025-43520 collectively enable adversaries to bypass critical security mechanisms. This multi-stage attack vector allows for sandbox escapes, elevation of privileges, and ultimately, remote code execution on vulnerable iPhones. While Apple has since addressed these vulnerabilities in more recent iOS releases, a substantial installed base of devices running iOS versions 18.4 through 18.7 remains susceptible, highlighting a window of opportunity for threat actors to exploit. The intricate nature of such an exploit chain suggests considerable resources and expertise invested by its developers, indicative of state-sponsored or highly sophisticated criminal organizations.
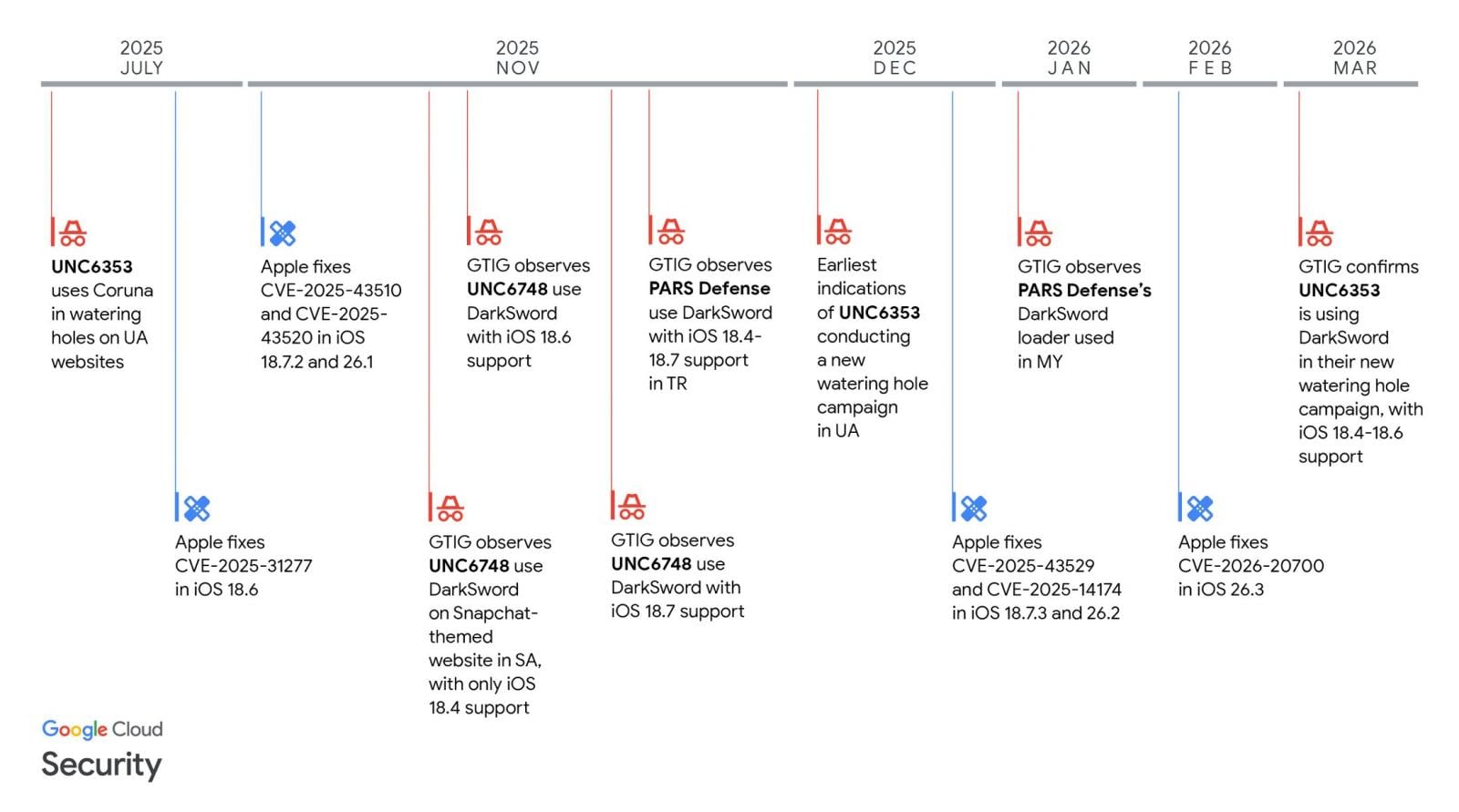
Investigations by leading security research entities, including Google Threat Intelligence Group (GTIG) and iVerify, have provided critical insights into the operational deployment of DarkSword. Their findings, brought to public attention recently, revealed the exploit kit’s role in information-stealing campaigns. Furthermore, the analysis has successfully linked DarkSword to multiple distinct threat groups, illuminating a complex ecosystem of actors leveraging these advanced tools. One such group, designated UNC6748, has been identified as a client of PARS Defense, a Turkish commercial surveillance vendor. This connection underscores the burgeoning market for offensive cyber capabilities, where sophisticated exploits are developed and sold to various state and non-state actors, significantly lowering the barrier to entry for highly impactful attacks. Another prominent actor associated with DarkSword is UNC6353, an entity suspected of operating under the auspices of Russian intelligence. The involvement of such diverse groups, with motivations ranging from commercial surveillance to state-sponsored espionage, signals the broad utility and effectiveness of the DarkSword capabilities.

The operational methodologies observed in these campaigns are varied yet consistently focused on data exfiltration and persistent access. GTIG’s intelligence indicates the deployment of at least three distinct information-theft malware families following successful DarkSword exploitation. GhostBlade, a highly aggressive JavaScript infostealer, demonstrates a robust capability for harvesting sensitive data from compromised devices. Concurrently, the GhostKnife backdoor provides adversaries with extensive data exfiltration capabilities, enabling the stealthy transfer of large volumes of victim information. The third identified payload, GhostSaber JavaScript, further extends the attackers’ reach by executing arbitrary code and facilitating additional data theft. The deployment of multiple malware families suggests a modular approach to exploitation, allowing threat actors to adapt their post-exploitation activities based on target profiles and strategic objectives.
A particularly concerning aspect of the DarkSword campaign involves watering-hole attacks orchestrated by UNC6353. This group has been observed deploying both the DarkSword and Coruna iOS exploit kits against iPhone users visiting compromised Ukrainian websites. The strategic targeting of e-commerce platforms, industrial equipment providers, and local services organizations in Ukraine points to a clear geopolitical motivation, likely aimed at intelligence gathering or disruptive activities. Watering-hole attacks are particularly insidious as they target users passively by compromising legitimate websites, making detection challenging for the average user. The dual deployment of DarkSword and Coruna suggests either an overlapping capability set or a preference for maximizing success rates by utilizing multiple proven exploit kits.
A key operational characteristic of DarkSword, noted by security researchers, is its design for short-term surveillance operations and evasion of detection. Following the successful exfiltration of target data, DarkSword is programmed to wipe temporary files and terminate its processes, effectively covering its tracks. This self-cleaning mechanism is a hallmark of sophisticated cyber espionage tools, indicating a deliberate effort to minimize forensic artifacts and impede incident response efforts. Such an operational philosophy is consistent with intelligence gathering objectives, where rapid data acquisition followed by stealthy withdrawal is paramount. Mobile security firm Lookout, which initially discovered DarkSword during an investigation into infrastructure linked to Coruna attacks, further corroborates this assessment. Lookout’s analysis suggests that DarkSword is actively employed in cyber-espionage campaigns aligned with Russian intelligence requirements, with some activity also attributed to a Russian threat actor pursuing financial objectives. This dual motivation – state-sponsored espionage and financial gain – is not uncommon, as intelligence agencies may contract out services or utilize financially motivated groups for deniability or complementary operations.
In response to these pervasive and sophisticated threats, CISA moved to formally add three of the six DarkSword vulnerabilities – CVE-2025-31277, CVE-2025-43510, and CVE-2025-43520 – to its authoritative catalog of actively exploited security flaws. This inclusion triggers a mandatory patching timeline for all Federal Civilian Executive Branch (FCEB) agencies under the provisions of Binding Operational Directive (BOD) 22-01. The directive mandates that FCEB agencies apply vendor-provided mitigations or discontinue the use of affected products within a two-week timeframe, specifically by April 3. CISA’s official warning emphasized the gravity of these vulnerabilities, stating, "These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise." The KEV catalog serves as a crucial mechanism for prioritizing remediation efforts across federal networks, ensuring that agencies address the most critical and actively exploited threats first. BOD 22-01 itself represents a proactive approach by the U.S. government to enhance cybersecurity posture by establishing clear, enforceable deadlines for addressing known vulnerabilities.
While the binding operational directive primarily applies to federal agencies, CISA concurrently issued a strong advisory to all organizations, including those within the private sector, to prioritize the immediate remediation of these critical iOS flaws. The agency’s broader call to action underscores the universal applicability of these threats and the potential for spillover effects beyond governmental entities. Commercial organizations, particularly those handling sensitive customer data, intellectual property, or critical infrastructure, are equally vulnerable to sophisticated mobile exploitation campaigns. The interconnected nature of modern digital ecosystems means that a compromise in one sector can have ripple effects across others, making a collective defense strategy essential.
The emergence of sophisticated mobile exploit kits like DarkSword signals a continuing evolution in the threat landscape. Mobile devices, once considered less critical than traditional endpoints, are now primary targets due to their pervasive use, rich data environment, and often less stringent security postures compared to enterprise servers or workstations. The integration of personal and professional activities on these devices makes them attractive vectors for both espionage and financially motivated attacks. Looking ahead, the cat-and-mouse game between device manufacturers, security researchers, and threat actors will undoubtedly intensify. Apple and other mobile OS developers will continue to invest heavily in security enhancements, but the lucrative nature of zero-day exploits ensures that adversaries will persist in their efforts to uncover new vulnerabilities.
For organizations, a robust and proactive security posture is no longer merely advantageous but imperative. This includes not only timely patching but also implementing comprehensive mobile device management (MDM) solutions, employing advanced endpoint detection and response (EDR) for mobile devices, and fostering a culture of cybersecurity awareness among employees. Regular security audits, penetration testing of mobile applications, and rigorous vulnerability management programs are essential components of a resilient defense strategy. Furthermore, active participation in threat intelligence sharing initiatives can provide early warnings and crucial insights into emerging threats, allowing organizations to pre-emptively strengthen their defenses. The DarkSword campaign serves as a stark reminder that mobile devices are critical enterprise assets requiring the same, if not greater, level of security scrutiny and investment as traditional IT infrastructure. Failure to address these vulnerabilities promptly and comprehensively could result in severe operational disruptions, significant financial losses, and irreparable damage to an organization’s reputation and security integrity.






