
In a decisive move reflecting a heightened commitment to digital security, the European Union has implemented stringent new sanctions against three companies—two based in China and one in Iran—alongside two key individuals, holding them accountable for their direct involvement in sophisticated cyber operations and malign influence campaigns that have compromised European infrastructure and democratic processes. This action underscores a growing international resolve to counter state-sponsored digital aggression, aiming to disrupt the capabilities of actors engaged in espionage, sabotage, and disinformation.
The measures, unanimously adopted by the Council of the European Union, are a direct response to a series of malicious cyber activities that have plagued member states, ranging from widespread device exploitation to targeted attacks on critical national services. These sanctions signify a clear message from Brussels that such digital incursions will not be tolerated, and perpetrators, regardless of their origin, will face severe economic and travel restrictions. The targeted entities and individuals are now subject to asset freezes across all EU territories, while EU citizens and businesses are prohibited from providing them with any financial or economic resources. Furthermore, the two individuals face a comprehensive travel ban, preventing their entry into or transit through any EU member state.
One of the Chinese entities singled out for its egregious activities is Integrity Technology Group. Between 2022 and 2023, this company allegedly provided crucial technical and material support enabling the compromise of over 65,000 devices across six EU member states. Such widespread access to digital systems, often involving routers, IoT devices, and other network infrastructure, can facilitate espionage, data exfiltration, or the establishment of persistent access for future disruptive operations. The scale of this compromise highlights the pervasive nature of modern cyber threats and the often-underestimated vulnerability of widely deployed consumer and enterprise hardware. This incident, impacting tens of thousands of endpoints, represents a significant breach of digital sovereignty and a direct threat to the privacy and security of European citizens and organizations.
The second Chinese firm facing EU penalties is Anxun Information Technology, also widely known by its alternative designation, i-Soon. This company has been identified as a provider of sophisticated hacking services, explicitly targeting critical infrastructure and essential functions within EU member states and third countries. Attacks on critical infrastructure—such as energy grids, transportation networks, or communication systems—carry the potential for severe disruption, economic damage, and even risks to public safety. The inclusion of Anxun’s co-founders on the sanctions list, signifying their pivotal roles in orchestrating these attacks, underscores the EU’s intent to hold individual architects of cyber campaigns personally accountable. Their involvement highlights the hierarchical and organized nature of such state-affiliated cyber operations.

The Iranian entity, Emennet Pasargad, has been implicated in a diverse range of malign activities, extending beyond traditional cyber espionage into the realm of information warfare and influence operations. This company has been linked to multiple campaigns designed to manipulate public opinion and sow discord, including the compromise of an SMS service in Sweden. Such an attack could enable the distribution of false information or the disruption of vital communications, with potentially significant societal impacts. Furthermore, Emennet Pasargad was involved in the audacious hijacking of advertising billboards to disseminate misinformation during the lead-up to the 2024 Paris Olympics. This tactic, leveraging public display infrastructure for propaganda, demonstrates a clear intent to exploit high-profile events for political messaging and destabilization.
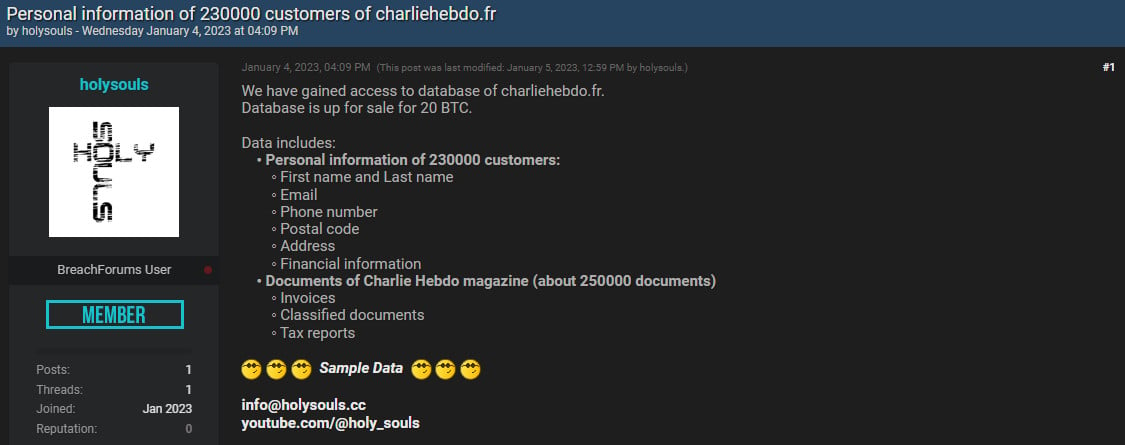
Adding to its extensive portfolio of malicious activities, Emennet Pasargad, operating under the moniker "Holy Souls" on hacker forums, was identified by Microsoft as having offered to sell the personal information of 230,000 subscribers to the French satirical magazine Charlie Hebdo in early January 2023. The asking price for this sensitive data, which included subscriber names and addresses, was 20 bitcoins, equivalent to approximately $340,000 at the time. This incident not only constitutes a significant data breach but also carries a strong symbolic weight, given Charlie Hebdo‘s history and its role in freedom of expression debates. The act of monetizing stolen personal data while simultaneously engaging in influence operations underscores the multi-faceted nature of modern state-sponsored cyber threats, often blurring the lines between intelligence gathering, financial gain, and political coercion.
Emennet Pasargad is widely believed to operate as a cybersecurity services provider for the Iranian government, indicating a direct link between its illicit activities and state objectives. Its long history of involvement in influence campaigns dates back several years, drawing international scrutiny. Notably, in November 2021, the U.S. Department of Justice offered a $10 million reward for information leading to the location of two Iranian nationals who were working as contractors for the company, further illustrating the international dimension of efforts to disrupt its operations. This consistent pattern of behavior highlights a sophisticated and persistent threat actor operating with state backing, employing both technical exploits and psychological manipulation to achieve strategic goals.
The EU’s decision to impose these sanctions is not an isolated event but rather a continuation of a broader strategy initiated in 2019 to establish a robust framework for deterring and responding to malicious cyber activities. This sanctions regime has progressively expanded, and with the latest additions, it now targets a total of 19 individuals and seven entities deemed responsible for significant cyber threats against the Union and its member states. The legal basis for these measures allows the EU to act decisively against actors, whether state-sponsored or otherwise, whose cyber operations pose a severe risk to national security, critical infrastructure, democratic processes, and fundamental rights.
The European Union’s actions align with and build upon previous measures taken by international partners, particularly the United States, demonstrating a coordinated global effort to address these persistent threats. Integrity Technology Group, for instance, was connected by the U.S. Federal Bureau of Investigation (FBI) in 2024 to the "Raptor Train" botnet. This massive network of compromised devices, believed to be operated by the Chinese state-sponsored threat actor "Flax Typhoon," had infected an estimated 260,000 routers and IP cameras, creating a formidable platform for various malicious activities, from distributed denial-of-service (DDoS) attacks to espionage. In January 2025, the U.S. Treasury Department had already sanctioned Integrity Technology Group for its pivotal role in enabling the Raptor Train botnet, signaling an early international consensus on its harmful activities.
Similarly, Anxun Information Technology (i-Soon) has been under intense international scrutiny. In March 2025, the U.S. Justice Department had previously sanctioned the company, citing its extensive history of offering "hacker-for-hire" services and carrying out cyberattacks since at least 2011. A significant blow to the company’s operations and reputation occurred in mid-February 2024, when a major data leak exposed i-Soon’s internal workings as a China-affiliated hacking contractor, revealing a trove of information about its offensive toolkit, targets, and operational methodologies. This unprecedented leak provided invaluable intelligence into the mechanics of a state-aligned cyber espionage firm. Following these revelations, U.S. authorities announced substantial rewards of up to $10 million for valid information leading to the location of ten key Anxun Information Technology executives and technical staff members, further intensifying pressure on the organization and its leadership.
The cumulative effect of these international sanctions and law enforcement actions aims to significantly degrade the capabilities of these entities. Asset freezes disrupt their financial lifelines, making it harder to procure advanced tools, recruit talent, and sustain complex operations. Travel bans directly impede the movement of key personnel, complicating their ability to collaborate internationally or evade justice. More broadly, these measures impose substantial reputational damage, making it difficult for the sanctioned entities to operate legitimately in the global digital economy and deterring potential partners or clients.
From an analytical perspective, these sanctions represent a hardening of the EU’s stance on cyber sovereignty and a recognition of the growing threat landscape. State-sponsored cyber warfare has evolved far beyond traditional espionage, now encompassing critical infrastructure sabotage, widespread data theft, and sophisticated disinformation campaigns designed to influence elections and undermine public trust. The EU’s actions demonstrate a clear shift towards a more proactive and punitive approach, moving beyond mere attribution to direct economic and legal consequences for malicious actors. This strategy aims not only to punish past transgressions but also to establish a credible deterrent against future cyberattacks.
The implications for international relations are significant. These sanctions signal a coordinated effort by Western powers to push back against cyber aggression from states like China and Iran, potentially leading to increased tensions in the digital domain. However, they also underscore the necessity of international cooperation in combating a borderless threat. The shared intelligence and synchronized actions between the EU and the U.S. illustrate a model for effective global cybersecurity governance.
Looking ahead, the effectiveness of these sanctions will depend on several factors, including the continued vigilance of intelligence agencies, the ability to enforce the measures rigorously, and the willingness of other nations to join this concerted effort. While sanctions can disrupt operations and inflict economic pain, they may also provoke retaliatory actions in the cyber realm. Therefore, alongside punitive measures, there remains an urgent need for enhanced cyber resilience within critical infrastructure, robust threat intelligence sharing, and continuous diplomatic engagement to de-escalate tensions and establish clearer norms for responsible state behavior in cyberspace. The EU’s latest move marks a pivotal moment in the ongoing global struggle to secure the digital commons and uphold international law in an increasingly interconnected and contested digital landscape.






