
The United Kingdom’s Companies House, the official registrar of companies in the nation, has confirmed the remediation of a significant security vulnerability within its WebFiling service, which for an approximate five-month period allowed unauthorized access to sensitive corporate and individual data. This flaw, introduced during system updates in October 2025, permitted logged-in users to potentially view confidential information pertaining to other registered entities and even initiate fraudulent filings. The incident underscores critical challenges in governmental digital infrastructure security and has prompted investigations by national cybersecurity and data protection authorities.
Companies House serves as a cornerstone of the UK’s business landscape, maintaining the official register of over five million companies. Its remit includes the incorporation of new businesses, the recording of statutory information such as director details, registered office addresses, annual accounts, and confirmation statements. The WebFiling service is a primary digital portal for businesses to submit these mandatory updates and filings. The integrity and security of this system are paramount, not only for regulatory compliance but also for safeguarding the personal and financial information of millions of individuals and the operational stability of countless enterprises.
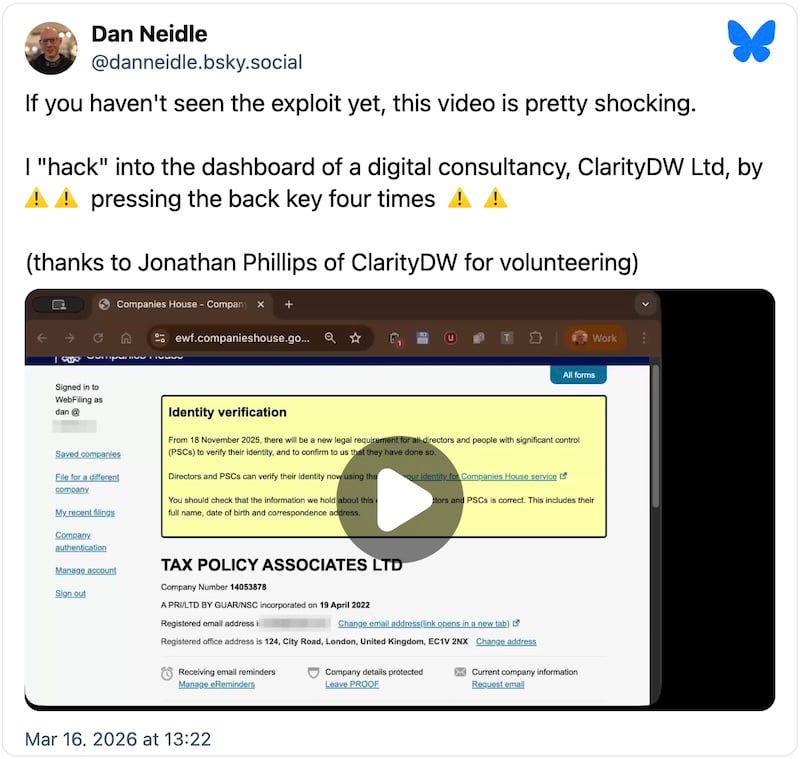
The vulnerability came to light through the diligent efforts of independent researchers. John Hewitt of Ghost Mail initially identified the flaw, subsequently engaging Dan Neidle, founder of the non-profit Tax Policy Associates, after encountering difficulties in receiving a timely response from Companies House. Neidle publicly reported the issue, detailing a relatively straightforward method of exploitation that leveraged a navigation flaw within the WebFiling interface. According to Neidle’s account, a logged-in user, after accessing their own company dashboard, could initiate a filing for a different company by entering its registration number. While an authentication code would typically be required, navigating back through the browser’s history a few times would inexplicably redirect the user to the other company’s dashboard, bypassing the necessary authorization. This critical bypass granted unauthorized access to a range of information and functionalities intended solely for the legitimate representatives of that company.
The scope of the exposed data was substantial. Companies House’s subsequent confirmation revealed that specific data elements not typically made public on the main register could have been rendered visible to unauthorized logged-in WebFiling users. This included highly sensitive personal identifiers such as dates of birth, residential addresses of company directors and secretaries, and private company email addresses. The potential ramifications extend beyond mere data visibility; the agency also acknowledged that the flaw could have facilitated "unauthorised filings," encompassing critical documents such as annual accounts or changes to a company’s director roster, without the consent of the legitimate entity. This capability poses a severe risk of corporate identity theft, financial fraud, and significant disruption to business operations.
The duration of the exposure, spanning from October 2025 until the service was temporarily taken offline for remediation in March 2026, raises serious concerns about the efficacy of ongoing security monitoring and internal audit processes. Five months is an extensive period for such a critical vulnerability to persist in a core governmental service, particularly one handling sensitive corporate and personal data. While Companies House has stated that no user passwords were compromised and data used in identity verification processes, such as passport information, remained secure, the potential for exploitation of other exposed data points remains high. Furthermore, the agency confirmed that existing filed documents, like previously submitted accounts or confirmation statements, could not have been retrospectively altered, mitigating one specific vector of potential historical data manipulation.

The incident has immediately triggered regulatory involvement. Companies House has formally reported the security breach to the Information Commissioner’s Office (ICO), the UK’s independent authority established to uphold information rights in the public interest, promoting openness by public bodies and data privacy for individuals. The ICO’s investigation will undoubtedly scrutinize the nature of the breach, the extent of data compromised, Companies House’s compliance with data protection regulations, specifically the General Data Protection Regulation (GDPR) and the Data Protection Act 2018, and the appropriateness of the agency’s response. Potential penalties for non-compliance with data protection laws can be substantial, reflecting the seriousness of safeguarding personal data.
Concurrently, the National Cyber Security Centre (NCSC), the UK’s authority on cyber security, has also been engaged. The NCSC’s involvement typically focuses on assessing the technical aspects of the vulnerability, understanding the threat landscape, and advising on robust mitigation strategies to prevent future occurrences. Their expertise will be crucial in a comprehensive forensic investigation to ascertain whether the vulnerability was actively exploited and to what extent, if any, data was accessed or altered without authorization. At the current stage, Companies House has stated it has no reports of malicious exploitation, but the investigation is ongoing, and a definitive conclusion remains pending.
From an expert analysis perspective, this incident highlights several critical areas of cybersecurity governance and practice. Firstly, the nature of the vulnerability points to a fundamental failure in authorization and session management within the WebFiling application. The ability to bypass authentication by manipulating browser navigation history indicates a lack of robust server-side validation for user requests, a common flaw often categorized under "Insecure Direct Object References (IDOR)" or broken access control. When a system allows a user to request data or actions without properly verifying that the user is authorized to access that specific resource or perform that specific action, such vulnerabilities arise.
Secondly, the timeline underscores deficiencies in the Secure Software Development Lifecycle (SSDLC). Updates to systems, particularly those handling sensitive data, should undergo rigorous security testing, including penetration testing, vulnerability assessments, and comprehensive code reviews, before deployment to a live environment. The introduction of such a significant flaw during a system update suggests that these critical security gates either failed or were insufficiently applied.
Thirdly, the initial difficulty in reporting the vulnerability by external researchers points to potential weaknesses in Companies House’s vulnerability disclosure program or its channels for receiving and acting upon external security intelligence. Establishing clear, accessible, and responsive mechanisms for ethical hackers and security researchers to report findings is a best practice that can significantly enhance an organization’s defensive posture by identifying flaws before malicious actors exploit them.
The implications of such a breach extend far beyond regulatory fines. The exposure of residential addresses for company directors poses significant personal security risks, potentially exposing individuals to identity theft, targeted fraud, or even physical threats. For businesses, the ability for unauthorized parties to alter company filings could lead to severe financial and reputational damage, legal disputes, and operational paralysis. It undermines trust in the accuracy and integrity of the official company register, which is a foundational element of the UK’s business environment.
Looking ahead, Companies House faces a multifaceted challenge. Beyond the immediate technical remediation, a comprehensive review of its entire digital infrastructure’s security posture will be necessary. This should include re-auditing all applications, implementing continuous security monitoring, and potentially establishing a public bug bounty program to incentivize ongoing external security research. Furthermore, clear communication with affected companies and individuals will be paramount, detailing the specific data that may have been exposed and providing guidance on protective measures they can take.
This incident serves as a stark reminder for all public and private sector organizations about the persistent and evolving nature of cyber threats. It emphasizes the critical importance of embedding security at every stage of system development and operation, fostering a culture of proactive vigilance, and maintaining robust incident response capabilities. The integrity of national digital services hinges on these foundational principles, and the UK’s Companies House incident provides valuable, albeit challenging, lessons for strengthening cyber resilience across the board. The ongoing investigations will provide crucial insights into the precise impact and ultimately guide the necessary systemic improvements to safeguard the UK’s corporate data infrastructure.






