
In a pivotal move to fortify its extensive device ecosystem, Apple recently deployed crucial security patches aimed at its older iPhone and iPad models. These updates specifically target a sophisticated array of vulnerabilities that have been actively exploited by the Coruna exploit kit, a dangerous tool implicated in a range of malicious activities spanning cyberespionage and illicit cryptocurrency appropriation. This release underscores Apple’s sustained commitment to safeguarding its user base, extending critical protections to devices that no longer receive the latest operating system upgrades but remain susceptible to evolving digital threats.
The current wave of security updates is significant because it backports fixes for critical vulnerabilities that were previously addressed in newer iOS device models. The initial rollout of these crucial security enhancements commenced in September 2023 for more contemporary hardware. However, recognizing the persistent threat landscape and the extensive installed base of legacy devices, Apple has now extended these protections to older hardware running earlier iterations of its mobile operating system. This strategic decision ensures that a broader spectrum of its product line benefits from defenses against known, actively exploited vulnerabilities. Apple’s official security advisories confirm the direct link between these patches and the mitigation of threats posed by the Coruna exploit, explicitly stating that the update "brings that fix to devices that cannot update to the latest iOS version."
The vulnerabilities addressed by these backported security patches are not trivial; they are often components of multi-stage exploit chains. These chains are meticulously crafted to allow malicious actors to escalate privileges to the Kernel level or achieve remote code execution on compromised devices. Such capabilities represent the pinnacle of device compromise, granting attackers profound control over the affected hardware and its data. The implications of such breaches are severe, ranging from complete data exfiltration and persistent surveillance to the installation of further malware or the complete commandeering of the device for broader network attacks.
The threat landscape continuously evolves, and older devices, while no longer at the cutting edge of hardware and software, often represent a significant attack surface. Many users retain these devices for extended periods, and while they may not receive new feature updates, the expectation of ongoing security support is paramount. Apple’s approach reflects an understanding of this dynamic, ensuring that even devices deemed "legacy" are not left exposed to known, critical exploits. This strategy not only protects individual users but also contributes to the overall security posture of the broader Apple ecosystem, preventing older devices from becoming weak links in enterprise networks or personal digital lives.
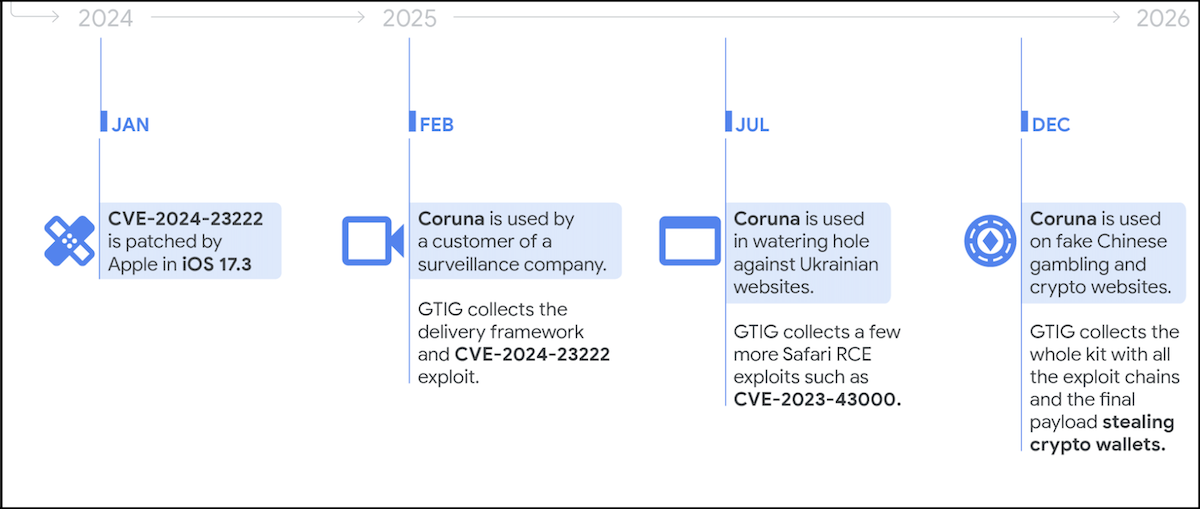
The Coruna exploit kit, central to these recent security concerns, represents a sophisticated and adaptable tool utilized by a diverse array of threat actors. Exploit kits are automated frameworks designed to identify and exploit vulnerabilities on target systems, often delivered via malicious websites or compromised online advertisements. Coruna, in particular, has demonstrated a high degree of sophistication since its emergence in early 2025, according to insights from Google Threat Intelligence Group (GTIG) researchers. Its deployment has been observed across multiple threat groups, highlighting its versatility and effectiveness in various malicious campaigns.
Among the prominent actors leveraging Coruna is UNC6353, a group suspected of being backed by a state-sponsored entity, likely Russian. State-sponsored hacking groups are typically characterized by their advanced capabilities, extensive resources, and strategic objectives, which often include cyberespionage, intellectual property theft, or critical infrastructure disruption. The use of Coruna by such a group underscores the kit’s efficacy in achieving persistent access and covert operations, suggesting its ability to bypass advanced security measures and maintain a low profile post-exploitation. The geopolitical implications of such activity are significant, as state-sponsored cyberattacks can have far-reaching consequences on national security and international relations.
Another concerning facet of Coruna’s deployment involves its use by customers of surveillance vendors. The proliferation of commercial surveillance tools, often marketed as legitimate law enforcement or intelligence-gathering solutions, has created a shadowy market for offensive cyber capabilities. When such tools fall into the wrong hands or are used by regimes with questionable human rights records, they pose a severe threat to privacy, civil liberties, and democratic processes. The involvement of surveillance vendors’ customers suggests that Coruna’s capabilities are being leveraged for targeted monitoring and data exfiltration, potentially against dissidents, journalists, or political opponents. This blurs the lines between legitimate security operations and illicit surveillance, raising ethical and legal questions about the accountability of such vendors and the responsible use of powerful cyber tools.
Furthermore, Coruna has been adopted by financially motivated threat actors, specifically UNC6691, a Chinese group. This group has been observed deploying the exploit kit on fake gambling and cryptocurrency websites. Their modus operandi involves luring unsuspecting victims to these fraudulent platforms, where the Coruna exploit kit then facilitates the delivery of malware payloads. The primary objective of UNC6691’s campaigns is to steal cryptocurrency wallets from infected devices, capitalizing on the booming, yet often insecure, digital asset market. This highlights a growing trend in cybercrime where sophisticated exploitation techniques, traditionally associated with state-sponsored actors, are increasingly being adopted by criminal organizations for direct financial gain. The intersection of advanced exploitation and social engineering tactics employed by groups like UNC6691 poses a significant threat to individuals engaged in cryptocurrency transactions, emphasizing the need for heightened vigilance and robust security practices.
The specific vulnerabilities addressed in these backported patches include a series of critical flaws, some of which have already been cataloged by major cybersecurity agencies. While the provided content did not list all CVEs directly in the bulleted section, it later highlighted several key identifiers. These include CVE-2023-43010, a WebKit flaw, along with CVE-2023-41974, CVE-2021-30952, and CVE-2023-43000. WebKit vulnerabilities are particularly dangerous as WebKit is the browser engine used by Safari and all third-party browsers on iOS, making it a common entry point for exploits delivered through malicious websites. Flaws in this component can lead to remote code execution, allowing attackers to run arbitrary code simply by tricking a user into visiting a malicious webpage. Kernel vulnerabilities, on the other hand, are even more severe, as they allow attackers to gain the highest level of system privileges, effectively taking full control of the device. The inclusion of these specific CVEs in the Coruna exploit kit underscores its capability to target fundamental components of the iOS operating system, enabling comprehensive device compromise.
The range of devices impacted by these vulnerabilities is extensive, encompassing a wide array of older iPhone and iPad models that operate on iOS 15.8.7/16.7.15 and iPadOS 15.8.7/16.7.15. While Apple has not publicly listed all specific models in the provided context, it signifies that a substantial segment of its user base, relying on older hardware, was at risk. Users of these legacy devices often face a unique challenge: they may not be able to upgrade to the very latest iOS versions due to hardware limitations, making them dependent on these backported security patches for protection against contemporary threats. The demographic using these devices might also include individuals who are less tech-savvy or less diligent about checking for updates, further increasing their exposure if not for proactive measures by Apple.
Government cybersecurity agencies play a crucial role in disseminating information about critical vulnerabilities and mandating protective actions. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has been particularly proactive in this regard. CISA notably added three of the vulnerabilities targeted by the Coruna exploit kit to its authoritative catalog of Known Exploited Vulnerabilities (KEV). This catalog serves as a critical resource for federal agencies, highlighting vulnerabilities that are actively being exploited in the wild and requiring immediate remediation. The inclusion of CVE-2023-43010, CVE-2023-41974, CVE-2021-30952, and CVE-2023-43000 in the KEV catalog underscores their severe nature and the urgency for patching.
In a direct response to these pervasive threats, CISA issued a directive to all Federal Civilian Executive Branch (FCEB) agencies, mandating that they apply the necessary patches to their iOS devices by March 26. This directive, issued under the authority of Binding Operational Directive (BOD) 22-01, highlights the critical importance of these updates for national security. CISA’s warning accompanying the directive emphasized that "these types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise." The implication is clear: failure to patch these vulnerabilities could lead to widespread compromise of government systems, with potential consequences for sensitive data, critical infrastructure, and national security operations. This underscores the ripple effect of individual device security on broader institutional resilience.
Beyond the Coruna-related vulnerabilities, Apple has been actively addressing other critical zero-day exploits. Earlier this year, the company fixed a separate zero-day vulnerability, identified as CVE-2026-20700 (though the year seems to be a typo and likely refers to a recent event). This particular flaw was described as having been exploited in an "extremely sophisticated attack" targeting specific individuals, allowing threat actors to execute arbitrary code on compromised devices. The discovery and reporting of this zero-day were credited to Google’s Threat Analysis Group (TAG), a team renowned for its expertise in tracking state-sponsored and highly sophisticated threat actors. While Apple did not disclose specific details about the nature or perpetrators of these "extremely sophisticated attacks," the involvement of Google TAG often indicates targeting by well-resourced groups with advanced capabilities, further emphasizing the constant arms race in cybersecurity.
The continuous discovery and exploitation of zero-day vulnerabilities, coupled with the sophisticated nature of exploit kits like Coruna, paint a stark picture of the contemporary threat landscape. The commoditization of offensive cyber capabilities, where exploit kits can be purchased or rented, democratizes access to powerful hacking tools, making them available to a wider range of malicious actors, from state-sponsored entities to financially motivated cybercriminals. This trend necessitates a multi-layered defense strategy, combining robust vendor-supplied security updates with vigilant user practices and proactive threat intelligence sharing among cybersecurity agencies and private firms.
For users, the primary implication of these developments is the absolute necessity of maintaining updated software, even on older devices. While the allure of new features might fade for legacy hardware, the continuous stream of security patches remains vital for digital safety. Ignoring these updates leaves devices exposed to known, actively exploited vulnerabilities, turning them into easy targets for cybercriminals and state-sponsored adversaries alike. The digital security of personal data, financial assets, and online identities hinges on prompt application of vendor-provided security fixes.
In conclusion, Apple’s release of these backported security updates for older iPhones and iPads is a critical intervention against the pervasive threat posed by the Coruna exploit kit and other sophisticated attack vectors. It reflects a comprehensive strategy to secure its entire ecosystem, acknowledging that even legacy devices require robust protection against advanced threats. The involvement of state-sponsored groups, surveillance vendors, and financially motivated cybercriminals in deploying Coruna highlights the diverse and complex nature of modern cyber warfare and cybercrime. As the digital landscape continues to evolve, the collaborative efforts between technology vendors, cybersecurity agencies, and threat intelligence groups, coupled with proactive user engagement, will remain indispensable in safeguarding against these persistent and increasingly sophisticated digital threats. Users of affected devices are strongly advised to install these critical updates without delay to ensure their continued protection.






