
The landscape of cloud security threats is undergoing a profound transformation, with sophisticated actors increasingly circumventing traditional perimeter defenses to leverage system vulnerabilities rather than relying on compromised or weak credentials. A recent comprehensive analysis highlights a significant pivot in attacker methodologies, indicating that the window for organizations to identify and patch newly disclosed software flaws has dramatically narrowed, shifting from weeks to a mere matter of days. This accelerated exploitation cycle underscores a critical challenge for defenders in an era of rapid digital evolution.
Historically, the weakest link in many security chains resided in human factors – readily guessable passwords, reused credentials, or easily exploitable misconfigurations. While these vectors remain relevant, their prevalence as primary initial access points has demonstrably decreased in recent periods. Incident response investigations now reveal that the exploitation of software bugs constitutes the leading entry method for malicious actors into cloud environments, signaling a heightened level of attacker sophistication and the effectiveness of enhanced identity and access management controls. This strategic evolution by threat actors necessitates a fundamental re-evaluation of defensive priorities, moving beyond basic hygiene to embrace proactive vulnerability management and rapid incident response capabilities.
According to a detailed examination of cloud intrusion incidents, the exploitation of vulnerabilities served as the predominant access vector in nearly 45% of all investigated breaches. In stark contrast, compromised credentials accounted for a notably smaller proportion, responsible for just over a quarter of documented intrusions. This data signifies a critical inflection point, where the battle for cloud security is increasingly fought at the application and infrastructure layer rather than solely at the authentication gateway. The shift is attributed, in part, to widespread industry efforts to strengthen credential protections, implement multi-factor authentication, and adopt secure-by-default postures, effectively raising the barrier for entry via conventional means.
The Rise of Remote Code Execution and Supply Chain Vulnerabilities
Among the myriad vulnerability types, Remote Code Execution (RCE) flaws emerge as the most frequently exploited, presenting attackers with the highest degree of control over compromised systems. RCE vulnerabilities allow an attacker to execute arbitrary code on a target machine, effectively taking full control of the affected system. Recent examples of such high-impact flaws include specific weaknesses identified in popular frameworks like React2Shell (CVE-2025-55182) and critical vulnerabilities within collaborative platforms such as XWiki (CVE-2025-24893). These vulnerabilities have not merely been theoretical threats; they have been actively weaponized in large-scale malicious campaigns, including those associated with botnets like RondoDox, demonstrating the immediate and tangible risk they pose to cloud infrastructure.
The rapid weaponization of these flaws is a testament to the agility of threat actors. Observations indicate that cryptominers, a common payload for financially motivated attackers, have been deployed within 48 hours of a vulnerability’s public disclosure. This shrinking window of opportunity for defenders – from disclosure to active exploitation – emphasizes the urgent need for organizations to implement robust patch management programs, continuous vulnerability scanning, and automated threat intelligence feeds that can rapidly contextualize new risks. The implications extend beyond direct system compromise; exploitation of flaws in third-party software or open-source components introduces significant supply chain risks, where a single vulnerability can ripple through an organization’s entire software ecosystem.

Evolving Attack Objectives: Stealth, Persistence, and Data Exfiltration
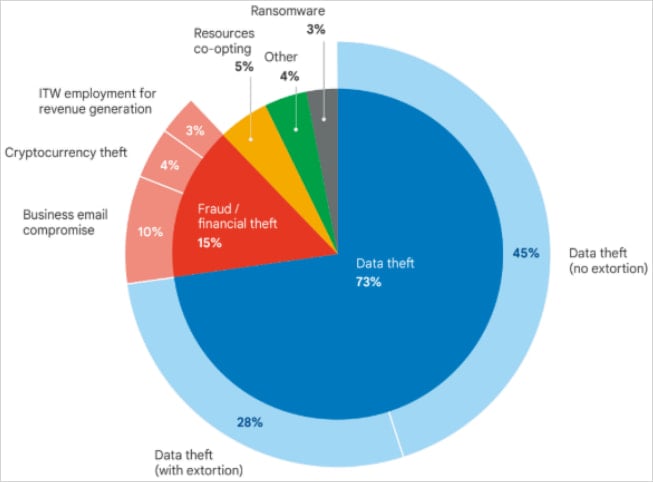
The motivations behind these advanced cloud intrusions are also evolving. While immediate financial extortion through ransomware has historically dominated headlines, the recent analysis reveals a predominant focus on silent data exfiltration and maintaining long-term persistence within victim environments. Attackers are increasingly prioritizing the surreptitious theft of high volumes of proprietary data without immediate demands, opting for a low-profile approach that can extend the dwell time within a network for prolonged periods. This strategy minimizes the immediate detection risk and maximizes the potential for sustained intelligence gathering or strategic advantage.
This shift underscores the strategic value of intellectual property, trade secrets, and sensitive customer data. Rather than causing disruptive outages, sophisticated actors aim to become an enduring presence, continuously siphoning off valuable information. The absence of immediate extortion attempts suggests that the stolen data serves varied purposes, ranging from competitive intelligence and market manipulation to state-sponsored espionage and the development of future attack capabilities. The goal is not just a quick hit, but a sustained, clandestine operation to exploit valuable digital assets over time.
Nation-State Espionage and Long-Term Compromise
The report highlights several instances of sophisticated espionage campaigns orchestrated by state-sponsored actors. These groups, often linked to geopolitical rivals, demonstrate an unparalleled level of patience and resourcefulness. For example, threat actors associated with Iran, identified as UNC1549, maintained access to a target environment for over eighteen months. Their initial compromise involved stolen VPN credentials, followed by the deployment of custom malware like MiniBike, enabling them to exfiltrate nearly one terabyte of proprietary data. This prolonged access allowed for a deep understanding of the victim’s operations and a systematic siphoning of valuable information.
Similarly, a China-sponsored actor, UNC5221, utilized the BrickStorm malware to sustain access to a victim’s VMware vCenter servers for at least eighteen months, resulting in the theft of critical source code. These examples underscore the strategic imperative of nation-states to acquire sensitive technological, economic, and military intelligence. Their tactics involve not only initial penetration but also meticulous lateral movement, privilege escalation, and the establishment of resilient persistence mechanisms designed to withstand detection and disruption over extended periods. For organizations operating in sectors of strategic interest, such as aerospace, defense, and advanced technology, the threat of such long-term, clandestine compromise remains acutely elevated.
Financially Motivated Cybercrime: North Korea’s Sophisticated Schemes
While nation-states pursue strategic objectives, financially motivated groups, particularly those linked to North Korea, exhibit a high degree of sophistication in their pursuit of monetary gain. A portion of the analyzed intrusions were attributed to North Korean IT workers, identified as UNC5267, who leveraged fraudulent identities to secure employment and generate illicit revenue for the government. This novel approach to cybercrime highlights the blurring lines between traditional espionage and financially driven operations, as state-sponsored entities increasingly use cyber means to circumvent sanctions and fund national programs.

Another North Korean threat actor, UNC4899, demonstrated a multi-stage attack specifically engineered for digital asset theft, culminating in the exfiltration of millions of U.S. dollars in cryptocurrency. This operation began with a highly targeted social engineering scheme, tricking a developer into downloading a malicious archive disguised as an open-source project collaboration. The developer’s subsequent transfer of the file from a personal device to a corporate workstation and its execution within an AI-assisted integrated development environment (IDE) created the initial foothold.
The malicious Python code embedded within the archive deployed a binary masquerading as a Kubernetes command-line tool. This binary then established a covert communication channel with UNC4899-controlled domains, serving as a sophisticated backdoor into the victim’s workstation and, by extension, the corporate network. From this initial beachhead, UNC4899 executed meticulous reconnaissance within the cloud environment, exploring specific pods in the Kubernetes cluster, establishing further persistence, and ultimately obtaining a highly privileged token for a CI/CD service account. This critical access allowed for lateral movement to more sensitive systems, including a pod responsible for network policy enforcement, which they then exploited to break out of the containerized environment and plant additional backdoors. The final stage involved compromising a system handling customer information, including identities, account security, and cryptocurrency wallet data, where insecurely stored database credentials facilitated the theft of substantial cryptocurrency holdings. This intricate attack chain illustrates a deep understanding of cloud infrastructure, development workflows, and cryptocurrency operations.
The Peril of OpenID Connect Abuse and Supply Chain Attacks
Modern cloud environments heavily rely on federated identity management protocols such as OpenID Connect (OIDC) to streamline authentication and authorization. However, this reliance introduces new attack vectors when trust relationships are exploited. A notable incident involved the abuse of a GitHub-to-AWS OIDC trust relationship following the compromise of an npm package named QuietVault. The attacker initially stole a developer’s GitHub token, which was then leveraged to create a new administrative account within the cloud environment by exploiting the OIDC trust.
This attack, part of the broader "s1ngularity" supply-chain campaign in August 2025, demonstrated an alarming speed of compromise and destruction. Within just three days of initial access, the QuietVault attacker obtained the developer’s GitHub and npm API keys, reportedly through the use of AI prompts with local AI command-line interface tools. They then abused the CI/CD pipeline to acquire the organization’s AWS API keys, subsequently exfiltrating data from S3 storage and proceeding to wipe critical data from both production and cloud environments. The "s1ngularity" attack itself exposed sensitive information, including GitHub tokens, SSH keys, configuration files, and npm tokens, from thousands of accounts and repositories, highlighting the cascading impact of supply chain compromises. Such incidents underscore the critical need for organizations to secure their development pipelines, scrutinize third-party dependencies, and meticulously manage identity federation across cloud services.
The Evolving Landscape of Insider Threats
While external threats often dominate security discussions, the danger posed by malicious insiders remains a significant concern. The analysis of over a thousand insider data theft incidents revealed a growing trend: insiders are increasingly leveraging legitimate cloud services for data exfiltration, moving beyond traditional methods like email and portable storage devices. Services such as Amazon Web Services (AWS), Google Cloud, Microsoft Azure, Google Drive, Apple iCloud, Dropbox, and Microsoft OneDrive are becoming preferred conduits for illicit data transfer.
The data indicates that a substantial majority of these incidents occurred while the insider was still employed, with a smaller but still significant number happening post-termination. This shift underscores the need for robust data loss prevention (DLP) mechanisms that monitor and control data movement within and outside an organization’s cloud perimeter. Companies must implement comprehensive data protection strategies that account for both external threats and the potential for employees, contractors, or consultants to violate trust and steal corporate data. This trend suggests that cloud services are rapidly replacing email as the primary method for information exfiltration, necessitating a proactive and adaptive approach to internal threat detection.
The Urgency of Automated Response and Future Projections
The accelerating pace of cloud attacks presents a critical challenge for traditional, manual incident response schemes. The speed at which threat actors operate, sometimes deploying payloads within an hour of a new instance’s creation, renders manual intervention largely ineffective. Attackers are also increasingly deleting backups, removing log files, and wiping forensic artifacts to impede recovery efforts and obscure their tracks. This necessitates the urgent implementation of automated incident response systems capable of detecting, containing, and remediating threats at machine speed.
Looking ahead, the outlook for cloud security suggests a continued escalation in threat activity. Geopolitical conflicts are expected to fuel state-sponsored cyber operations, as nations leverage digital means to gain strategic advantages and conduct espionage. Major global events, such as the FIFA World Cup and significant national elections, will inevitably serve as magnets for malicious operations, attracting both financially motivated groups and state actors seeking to disrupt, influence, or profit. Organizations must anticipate these heightened threat levels and fortify their defenses accordingly, embracing advanced security technologies, adopting zero-trust architectures, and fostering a culture of continuous security vigilance to navigate the increasingly complex and volatile cloud threat landscape. The future of cloud security hinges on proactive, intelligent, and automated defenses capable of keeping pace with an ever-evolving adversary.






