
A recent sophisticated cyberattack campaign has been uncovered, meticulously targeting employees within financial and healthcare organizations through Microsoft Teams, ultimately leading to the deployment of a novel remote access trojan dubbed A0Backdoor. This intricate operation combines advanced social engineering tactics with highly evasive technical methodologies to establish persistent unauthorized access, underscoring a significant evolution in threat actor capabilities and a pressing challenge for enterprise cybersecurity defenses.
The initial breach vector for this campaign capitalizes on the ubiquitous nature of internal communication platforms. Threat actors initiate contact with targeted employees via Microsoft Teams, a channel typically associated with trusted internal communications. This choice of platform immediately lends an air of legitimacy to the interaction, a critical factor in successful social engineering. Before direct engagement on Teams, the attackers often precede their approach by flooding the target’s corporate inbox with a deluge of unsolicited spam emails. This pre-conditioning serves a dual purpose: it creates a perceived problem for the employee, making them more receptive to "help," and it provides a plausible pretext for the subsequent impersonation.

Following the spam barrage, the attackers pivot to Microsoft Teams, masquerading as internal IT support personnel. Their message is crafted to appear helpful and urgent, offering assistance to resolve the disruptive email situation. This impersonation leverages the inherent trust employees place in their IT departments, particularly when facing a technical nuisance. The psychological manipulation at play is profound; the attackers present themselves as solutions to a problem they themselves initiated or amplified, thereby cultivating a sense of relief and cooperation from the victim.
The pivotal step in gaining initial access to the target system involves the abuse of Quick Assist, a legitimate Microsoft Windows remote assistance utility. Employees, under the guidance of the impersonating "IT staff," are instructed to initiate a Quick Assist session. This tool, designed for legitimate remote troubleshooting, becomes a conduit for malicious activity. Once remote access is established, the threat actor swiftly deploys a bespoke malicious toolset. A notable characteristic of this deployment is the use of digitally signed MSI (Microsoft Installer) packages, which are hosted on personal Microsoft cloud storage accounts. The digital signatures lend an undeserved veneer of authenticity, making these files less likely to be flagged by basic security measures, while the use of personal cloud storage allows for agile and low-cost infrastructure setup, circumventing more scrutinized enterprise hosting solutions.
Cybersecurity researchers at BlueVoyant have meticulously analyzed these malicious MSI files, revealing their deceptive nature. They are crafted to impersonate legitimate Microsoft Teams components and the "CrossDeviceService," a genuine Windows utility integral to the Phone Link application. This mimicry is a deliberate tactic to blend malicious executables with legitimate system processes, further complicating detection by both automated security tools and human analysts. The filename and internal metadata are carefully chosen to mirror those of benign software, reducing suspicion during initial inspection.
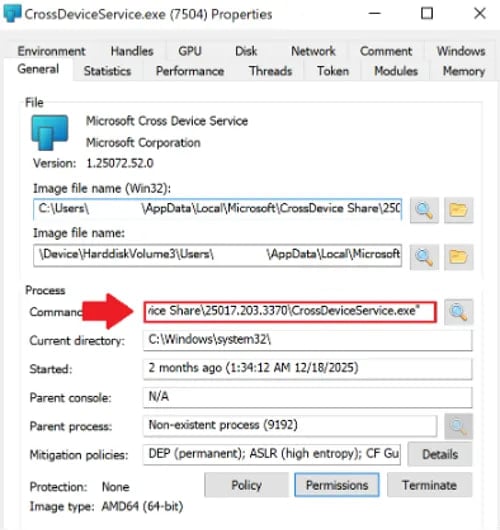
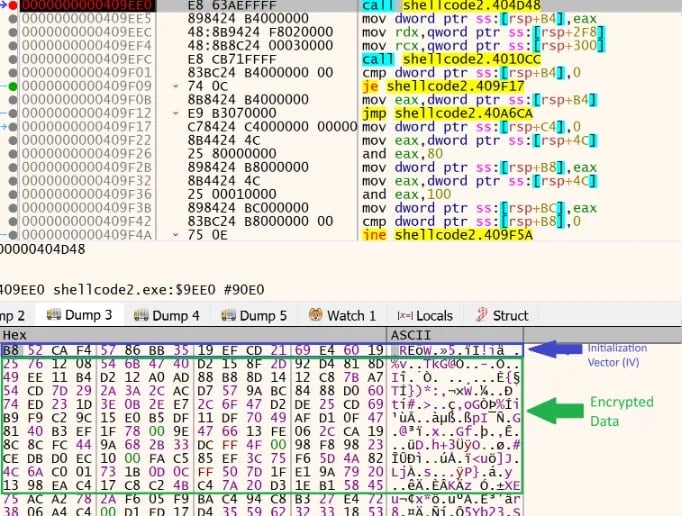
The technical sophistication extends to the method of malware execution, which employs a technique known as DLL sideloading. This method exploits the legitimate loading order of dynamic-link libraries (DLLs) by legitimate executables. The attackers introduce a malicious library, specifically hostfxr.dll, into a directory where a trusted application will attempt to load it before its legitimate counterpart. This malicious hostfxr.dll contains highly compressed or encrypted data. Upon being loaded into memory by a legitimate Microsoft binary, the library decrypts this obfuscated data into shellcode and then transfers execution control to it. This technique is particularly effective as it leverages trusted processes to execute malicious code, making it difficult for traditional endpoint protection solutions to differentiate between legitimate and malicious activity.
Further demonstrating the attackers’ focus on evasion, the malicious library incorporates anti-analysis measures. Researchers note the use of the CreateThread function, specifically designed to spawn an excessive number of threads. While this activity has a negligible impact on the system’s performance under normal operation, it can severely disrupt or even crash debuggers and analysis tools attempting to inspect the malware’s execution flow. This deliberate sabotage of forensic tools highlights a sophisticated understanding of reverse engineering methodologies and a proactive effort to impede threat intelligence gathering.
Once executed, the shellcode proceeds with additional layers of evasion and preparation. It first performs sandbox detection, a common technique for malware to identify if it is running within a controlled analysis environment. If a sandbox is detected, the malware may alter its behavior, remain dormant, or self-terminate to avoid revealing its full capabilities. Following successful sandbox evasion, the shellcode generates a SHA-256-derived key. This key is then used to decrypt the primary payload, the A0Backdoor, which is robustly encrypted using the Advanced Encryption Standard (AES algorithm). The multi-stage decryption process, coupled with strong encryption, ensures that the backdoor’s core functionality remains concealed until deep within the execution chain, making static analysis extremely challenging.
Upon successful decryption and loading, the A0Backdoor initiates its core routines. It first relocates itself into a new memory region, further obscuring its presence and making it harder to track. It then decrypts its core functionalities and begins a reconnaissance phase. This involves making various Windows API calls, such as DeviceIoControl, GetUserNameExW, and GetComputerNameW, to systematically collect detailed information about the compromised host. This host fingerprinting data typically includes system configuration, installed software, network settings, user account details, and hardware identifiers. Such information is crucial for threat actors to understand their environment, tailor subsequent attacks, and establish persistent control.
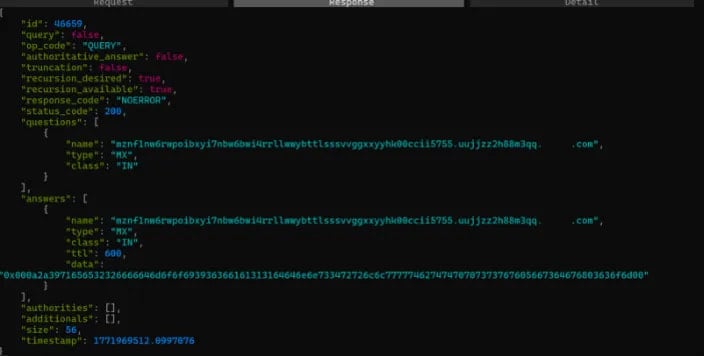
A particularly innovative aspect of the A0Backdoor is its command-and-control (C2) communication mechanism. Instead of relying on more commonly monitored HTTP/HTTPS or direct TCP connections, the malware cleverly hides its C2 traffic within standard DNS queries. Specifically, it sends DNS MX (Mail Exchanger) queries. The encoded metadata, containing instructions or exfiltrated data, is embedded within high-entropy subdomains of the requested domain names. These queries are directed to public recursive DNS resolvers, making the traffic appear as routine network activity. The C2 servers respond by providing MX records that contain encoded command data for the malware. This method of DNS tunneling, particularly using MX records, is highly effective at evading network security controls that are often tuned to detect TXT-based DNS tunneling, which is more commonly known and monitored. The ability of the traffic to blend seamlessly with legitimate DNS activity provides a stealthy and resilient communication channel for the attackers.
BlueVoyant’s analysis reveals that two prominent targets of this sophisticated campaign include a financial institution operating in Canada and a global healthcare organization. These sectors are consistently high-value targets for cybercriminals due to the sensitive nature of the data they handle—ranging from financial records and intellectual property to protected health information—and their critical role in national infrastructure. A successful breach in these sectors can lead to severe financial losses, reputational damage, regulatory penalties, and even disruption of essential services.
The researchers assess with moderate-to-high confidence that this campaign represents an evolution of the tactics, techniques, and procedures (TTPs) previously associated with the BlackBasta ransomware gang. BlackBasta, a notorious and prolific ransomware-as-a-service (RaaS) operation, gained significant infamy before its purported dissolution following the leak of its internal chat logs. While there are discernible overlaps with BlackBasta’s previous methodologies, this new campaign introduces several distinct elements. These include the use of digitally signed MSI files, the deployment of new malicious DLLs, the specific A0Backdoor payload itself, and the innovative DNS MX-based C2 communication. This evolution suggests that either remnants of the BlackBasta group have re-emerged with refined capabilities, or other sophisticated threat actors have adopted and enhanced some of their proven TTPs.
The emergence of campaigns like the one deploying A0Backdoor underscores a critical shift in the cyber threat landscape. Threat actors are increasingly combining highly effective social engineering with advanced technical evasion techniques. For organizations, this necessitates a multi-layered defense strategy that goes beyond traditional perimeter security. Enhanced security awareness training is paramount, focusing specifically on impersonation tactics over internal communication platforms like Microsoft Teams and the dangers of granting remote access. Technical controls must include robust endpoint detection and response (EDR) solutions capable of detecting sophisticated DLL sideloading and anti-analysis measures. Network monitoring capabilities need to be upgraded to identify anomalous DNS traffic, including high-entropy subdomains and MX-based tunneling. Furthermore, strict application whitelisting and granular control over legitimate remote assistance tools like Quick Assist are essential. Adopting a zero-trust security model, where every access request is verified regardless of its origin, becomes increasingly critical in mitigating such persistent and evasive threats. The continuous adaptation of threat actors demands a corresponding agility and sophistication in organizational cybersecurity defenses to protect vital assets and maintain operational integrity.






