
The United States Cybersecurity and Infrastructure Security Agency (CISA) has issued a critical directive, compelling federal entities to promptly address severe security vulnerabilities within Apple’s iOS ecosystem, which have been actively exploited by a formidable exploit kit known as Coruna in campaigns ranging from state-sponsored espionage to sophisticated cryptocurrency theft. This mandate underscores the escalating threat landscape where advanced cyber capabilities, once the exclusive domain of state actors, are increasingly being leveraged for illicit financial gain, posing a significant risk to organizational integrity and national security.
The Coruna exploit kit represents a paradigm shift in the sophistication of mobile device attacks. As detailed by researchers from Google’s Threat Intelligence Group (GTIG), this toolkit harnesses an extensive arsenal of approximately 23 distinct iOS vulnerabilities, many of which have been deployed as zero-day exploits—meaning they were leveraged by malicious actors before vendors had knowledge of them or released patches. The broad scope of targeted flaws highlights a concerted effort by the kit’s developers to ensure a wide attack surface and persistent compromise capabilities across various iOS versions. The comprehensive nature of Coruna’s attack chains signifies a high level of expertise and resource allocation, characteristic of advanced persistent threat (APT) groups or well-funded commercial surveillance enterprises.
Understanding the technical prowess of the Coruna exploit kit necessitates a deeper dive into its core capabilities. At its heart, Coruna is designed to achieve deep system compromise, enabling attackers to bypass critical security mechanisms engineered into the iOS architecture. These include:

- Pointer Authentication Code (PAC) Bypass: PAC is a security feature introduced by Apple to protect against certain types of memory corruption attacks, specifically those involving arbitrary code execution through pointer manipulation. It works by signing pointers with cryptographic hashes, ensuring their integrity before use. A PAC bypass allows attackers to circumvent this critical defense, making it significantly easier to inject and execute malicious code.
- Sandbox Escape: iOS employs a robust sandboxing mechanism, which isolates applications from the core operating system and from each other. This prevents a compromised application from accessing sensitive system resources or data belonging to other apps. A sandbox escape allows the exploit kit to break free from these confines, gaining broader access to the device and its stored information.
- Page Protection Layer (PPL) Bypass: PPL is another fundamental security layer within the iOS kernel, designed to prevent unauthorized modification of critical kernel memory regions. Bypassing PPL provides attackers with the ability to alter kernel structures, granting them deep control over the device and facilitating the persistence of their malicious payloads.
- WebKit Remote Code Execution (RCE): WebKit is the rendering engine used by Safari and other browsers on iOS. RCE in WebKit is often the initial vector for these attacks, allowing attackers to execute arbitrary code on a vulnerable device simply by tricking a user into visiting a malicious website. This is a common entry point for highly sophisticated mobile exploits.
- Kernel Privilege Escalation: The ultimate goal of many sophisticated exploits is to achieve kernel-level privileges. The kernel is the core of the operating system, and gaining control over it grants an attacker complete authority over the device, allowing them to install rootkits, steal any data, and maintain persistent access despite reboots or system updates.
The sequential chaining of these exploits demonstrates a highly sophisticated attack methodology. An attacker would typically initiate with a WebKit RCE to gain initial access within the browser’s sandbox. Subsequently, they would leverage a sandbox escape to break out of the browser’s restricted environment. Following this, PAC and PPL bypasses would be employed to elevate privileges to the kernel level, effectively granting the threat actor full control over the compromised device. This multi-stage approach is indicative of advanced adversary capabilities and significant investment in exploit development.
Critically, timely software updates and robust security configurations prove effective against Coruna. GTIG’s analysis confirms that these exploits are rendered ineffective on modern versions of iOS. Furthermore, activating Apple’s Lockdown Mode, an enhanced security feature designed for individuals at high risk of targeted cyberattacks, provides substantial protection against such spyware-grade threats. Even simply utilizing private browsing modes can offer a degree of mitigation by preventing the persistence of certain exploit components. This underscores the paramount importance of maintaining up-to-date operating systems and adopting enhanced security postures when dealing with sensitive information or facing elevated threat profiles.
The proliferation of the Coruna exploit kit across diverse threat actor groups highlights a troubling trend in the cyber landscape. GTIG’s observations reveal its deployment by:
- Commercial Surveillance Vendors: These entities develop and sell sophisticated cyber weaponry to governments and intelligence agencies globally. The presence of Coruna in their arsenal signifies its advanced capabilities and the commercialization of highly potent offensive tools.
- Suspected Russian State-Backed Hacking Group (UNC6353): The involvement of state-sponsored actors underscores the geopolitical motivations behind such attacks, typically focused on intelligence gathering, espionage, or strategic disruption. Groups like UNC6353 possess significant resources and operate with national objectives.
- Financially Motivated Chinese Threat Actor (UNC6691): This group has leveraged Coruna for direct financial gain, deploying it through deceptive gambling and cryptocurrency-themed websites. Victims lured to these sites would have their devices compromised, leading to the theft of their cryptocurrency wallets. This illustrates the convergence of advanced exploit capabilities with traditional cybercrime, elevating the risk profile for individuals and organizations involved in digital assets.
The trajectory of Coruna, as noted by mobile security firm iVerify, exemplifies a concerning pattern: the migration of "sophisticated spyware-grade capabilities" from highly specialized commercial surveillance vendors to nation-state actors, and ultimately, into the hands of mass-scale criminal operations. This democratisation of advanced cyber tools significantly lowers the barrier to entry for malicious activities, empowering a broader range of actors to execute highly effective and damaging attacks. The implications are profound, suggesting that tools once reserved for high-value targets are now being repurposed for broader campaigns, increasing the overall risk to the general public and private sector alike.
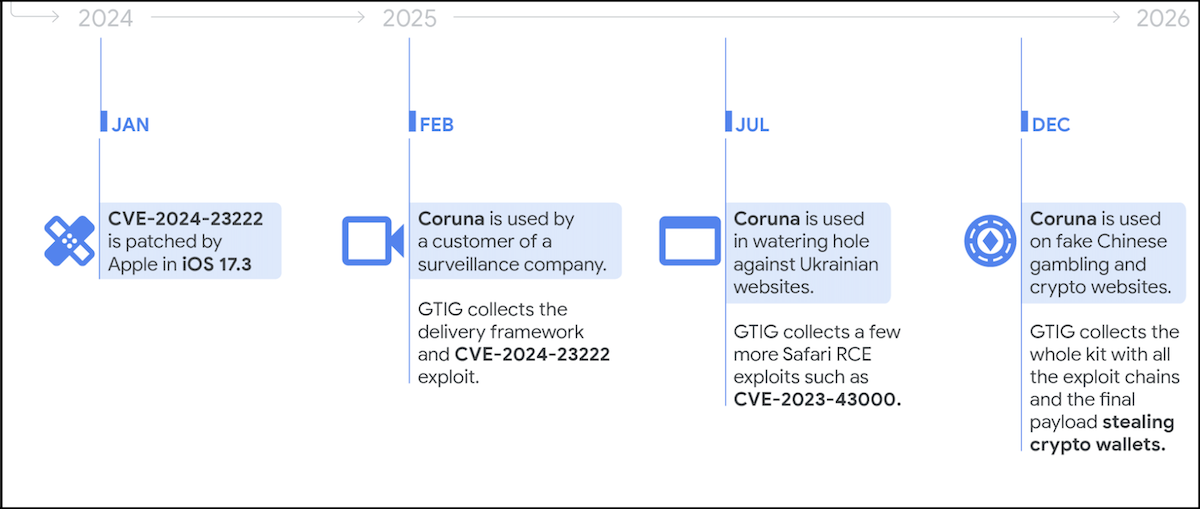
In response to this evolving threat, CISA has taken decisive action, integrating three of the 23 Coruna-related vulnerabilities (specifically CVE-2023-41974, CVE-2021-30952, and CVE-2023-43000) into its authoritative Catalog of Known Exploited Vulnerabilities (KEV). This action immediately triggers a compliance requirement for all Federal Civilian Executive Branch (FCEB) agencies under the stipulations of Binding Operational Directive (BOD) 22-01. This directive mandates that FCEB agencies apply vendor-provided mitigations, follow specific guidance for cloud services, or, if mitigations are unavailable, discontinue the use of affected products. The deadline for these critical security updates is March 26, emphasizing the urgent nature of the identified threat and CISA’s commitment to fortifying federal cyber defenses.
CISA’s warning extends beyond the federal sphere, serving as a critical alert for all organizations, including those in the private sector. The agency explicitly urged all entities to prioritize the patching of these vulnerabilities without delay. This recommendation stems from the understanding that vulnerabilities exploited by state-sponsored actors and sophisticated criminal groups pose "significant risks to the federal enterprise" and, by extension, to critical infrastructure, supply chains, and the broader economy. The interconnectedness of digital ecosystems means that a compromise in one sector can rapidly cascade, affecting others. Therefore, a collective, proactive approach to patching and security hygiene is indispensable.
The increasing focus on mobile device security, particularly for iOS, reflects the reality that smartphones have become central repositories for sensitive personal, professional, and financial data. Their pervasive use makes them highly attractive targets for a diverse array of threat actors. The sophisticated nature of the Coruna exploit kit underscores the continuous cat-and-mouse game between attackers developing novel ways to bypass security features and defenders implementing enhanced protections. The battle against such advanced threats requires not only prompt patching but also a multi-layered defense strategy that includes robust endpoint detection and response (EDR) solutions, comprehensive employee security training, and stringent mobile device management (MDM) policies within enterprises.
Looking ahead, the landscape of mobile cybersecurity is likely to become even more challenging. As operating systems and hardware integrate more advanced security features like PAC and PPL, attackers will continue to innovate, seeking new bypasses and zero-day vulnerabilities. The convergence of commercial spyware, nation-state capabilities, and financially motivated cybercrime suggests that sophisticated tools will remain accessible to a broader range of malicious actors. Organizations and individuals must cultivate a culture of continuous vigilance, embracing regular software updates, understanding the risks associated with unverified sources, and leveraging available security enhancements like Apple’s Lockdown Mode. The imperative to protect digital assets and sensitive information against evolving and increasingly sophisticated mobile threats remains a paramount concern for all stakeholders in the digital age.






