
A significant operational security lapse by South Korea’s National Tax Service (NTS) has resulted in the theft of approximately $4.8 million in digital assets, following the inadvertent public exposure of a seized cryptocurrency wallet’s mnemonic recovery phrase. This incident underscores critical vulnerabilities in the handling of digital evidence by governmental bodies and highlights the profound importance of fundamental cybersecurity protocols within the nascent field of virtual asset management. The compromise occurred after the NTS released images containing the unredacted "seed phrase" of a hardware wallet, which was part of a larger confiscation effort targeting high-value tax evaders.
The Context of Confiscation: Targeting Digital Wealth
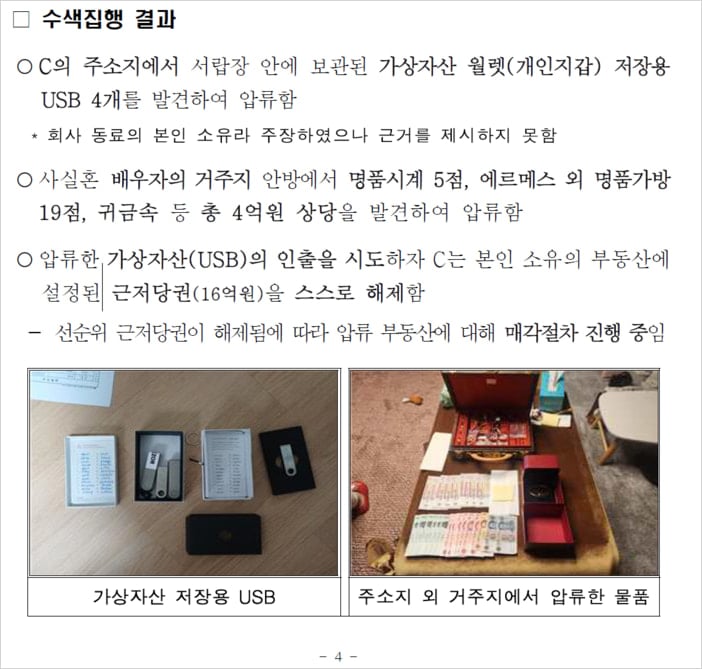
In recent years, as the cryptocurrency market has matured and gained mainstream adoption, national tax agencies worldwide have intensified their efforts to track and seize digital assets from individuals attempting to evade taxation. South Korea, a global leader in cryptocurrency adoption and innovation, has been at the forefront of these initiatives. The NTS has proactively developed strategies to identify and confiscate digital holdings, recognizing that virtual currencies can serve as a potent tool for illicit financial activities and tax avoidance. The agency had previously announced a successful operation involving raids on 124 high-value tax evaders, resulting in the confiscation of digital assets valued at approximately 8.1 billion Korean Won (approximately $5.6 million USD at the time of the original announcement). This operation was lauded as a significant victory in the ongoing battle against sophisticated financial crime, demonstrating the NTS’s increasing capability to penetrate the complex world of blockchain transactions.
Among the seized assets was a Ledger cold wallet, a popular brand of hardware wallet renowned for its robust security features, designed to store private keys offline and provide a secure environment for cryptocurrency transactions. The appeal of such devices lies in their resistance to online hacking attempts, making them a preferred choice for storing substantial digital wealth. However, the inherent security of a hardware wallet is entirely contingent upon the absolute secrecy of its associated mnemonic recovery phrase, often referred to as a "seed phrase." This sequence of 12 or 24 words acts as the master key to the entire wallet, allowing its contents to be restored on any compatible device, regardless of physical possession or any other security measures like PINs or biometric authentication.
The Catastrophic Disclosure: A Fundamental Security Failure
The critical error occurred when the NTS, in its enthusiasm to publicize the success of its anti-tax evasion campaign, disseminated press materials that included photographs of the seized Ledger device. Crucially, these images also prominently featured a handwritten note containing the complete 24-word recovery phrase for the confiscated wallet. This oversight represented a profound breach of fundamental cryptographic security principles. By publishing the seed phrase, the NTS effectively broadcast the master key to a wallet containing millions of dollars in digital assets to the entire internet, inviting any technically savvy individual to claim the funds. The public disclosure of a seed phrase is akin to publishing the full credentials to a bank vault, including the combination, key, and location, for anyone to exploit.

The Swift and Calculated Heist
The repercussions of this egregious error were immediate and financially devastating. Within a short period following the press release’s publication, on-chain analytics confirmed that 4 million Pre-Retogeum (PRTG) tokens, valued at approximately $4.8 million at the time, were systematically drained from the compromised NTS wallet. Blockchain data, specifically from explorers like Etherscan, provided a transparent chronicle of the theft. The perpetrator demonstrated a clear understanding of blockchain mechanics:
- Gas Fee Injection: The attacker first transferred a small amount of Ethereum (ETH) into the compromised wallet. This seemingly innocuous transaction served a critical purpose: to provide the necessary "gas fees" required to execute subsequent transfers of the PRTG tokens on the Ethereum blockchain. Without sufficient ETH for gas, the PRTG tokens would have remained inaccessible, highlighting the attacker’s methodical approach.
- Staged Asset Transfer: Following the gas fee injection, the 4 million PRTG tokens were not moved in a single, large transaction. Instead, the attacker meticulously transferred the funds in three separate transactions to a new, unidentified wallet address. This multi-stage transfer could have been an attempt to evade detection, manage transaction sizes, or simply reflect a cautious approach to moving a significant sum of digital assets.
This sequence of events underscores the rapid exploitation potential inherent in public blockchain environments, where transactions are immutable and often irreversible once confirmed. The speed with which the funds were moved after the seed phrase exposure illustrates the constant vigilance required in the digital asset space and the immediate consequences of security vulnerabilities.
Expert Condemnation and Systemic Deficiencies
The incident drew sharp criticism from experts in the field of blockchain and digital asset security. Professor Cho Jae-woo of Hansung University in Seoul, a renowned blockchain data analysis expert, likened the NTS’s blunder to "leaving a wallet open and advertising it to the entire nation for people to take the money." His pointed commentary highlighted a perceived "lack of basic understanding of virtual assets" within the tax authorities. This assessment goes beyond a simple mistake, suggesting a systemic deficiency in training, protocol, and awareness regarding the unique operational security requirements of digital assets.
Professor Cho’s critique resonates with a broader concern within the cybersecurity community: as governments and traditional institutions increasingly engage with advanced technologies like blockchain, there is an urgent need for specialized expertise and rigorous training. The principles governing the security of physical documents or traditional financial accounts do not directly translate to the digital asset realm, where a single string of words can hold the key to millions. The NTS’s oversight effectively nullified the painstaking efforts of their investigative teams, costing the national treasury tens of billions of won that had been successfully confiscated from tax evaders.
Implications and Broader Lessons
This high-profile theft carries profound implications for government agencies, institutional asset managers, and individual cryptocurrency holders globally:
- Governmental Competency in Digital Assets: The incident serves as a stark reminder that as digital assets become integral to the global economy, governmental bodies must cultivate deep expertise in their handling. This includes not only understanding the legal and financial aspects but also the fundamental technical and security protocols. Without this foundational knowledge, agencies risk undermining their own enforcement efforts and eroding public trust.
- Operational Security Protocols: The NTS’s failure underscores the critical need for robust operational security protocols specifically tailored for digital assets. These protocols must include stringent review processes for all public-facing materials, especially those containing sensitive information. Redaction should be a multi-layered, mandatory step, overseen by personnel specifically trained in digital asset security.
- Irreversibility of Blockchain Transactions: The immutable nature of blockchain transactions means that once funds are transferred from a compromised wallet, recovery is exceptionally difficult, often requiring the cooperation of the attacker or a centralized exchange. This highlights the "self-custody, self-responsibility" ethos of cryptocurrency and the unforgiving nature of security breaches in this domain.
- Reputational Damage and Public Trust: Beyond the immediate financial loss, the NTS’s blunder likely incurred significant reputational damage. Such incidents can diminish public confidence in governmental agencies’ ability to manage complex digital challenges and protect confiscated assets, potentially impacting future compliance efforts.
- A Clarion Call for All Wallet Owners: For individuals, the case reinforces the paramount importance of safeguarding seed phrases. Hardware wallets provide robust security, but this security is entirely negated if the seed phrase is exposed. Best practices include:
- Offline Storage: Never digitize a seed phrase (e.g., in photos, emails, cloud storage, or messaging apps). It should be physically written down.
- Secure Physical Location: Store the physical copy in a secure, fireproof, and waterproof location, such as a safe deposit box or a home safe.
- Multiple Backups (Securely): Consider creating multiple physical backups and storing them in geographically dispersed, secure locations, but always ensure each copy is protected against unauthorized access.
- Never Share: The seed phrase should never be shared with anyone, under any circumstances.
- Immediate Action Post-Exposure: If a seed phrase is ever suspected of being compromised, all associated funds must be immediately moved to a new, secure wallet with a newly generated seed phrase.
The Path Forward: Enhanced Training and Robust Frameworks
The NTS has reportedly removed the problematic press release from its website, but it remains unclear whether a formal investigation into the theft has been initiated to trace the stolen funds. Given the nature of blockchain, tracing the funds might be possible, but recovery is another matter entirely.
Moving forward, this incident necessitates a comprehensive re-evaluation of how governmental bodies approach digital asset management. This should include:
- Specialized Training Programs: Mandatory, in-depth training for all personnel involved in the seizure, custody, and management of virtual assets, focusing on cryptographic security fundamentals.
- Dedicated Digital Asset Units: Establishing specialized units with expertise in blockchain forensics, digital asset security, and secure custody solutions.
- Multi-Signature Wallets and Institutional Solutions: Exploring the use of multi-signature (multi-sig) wallets for seized assets, which require multiple private keys to authorize a transaction, thus eliminating single points of failure. Institutional-grade custody solutions could also be considered.
- Standardized Operating Procedures: Developing and strictly adhering to standardized operating procedures (SOPs) for the documentation, storage, and public communication related to seized digital assets, with an emphasis on rigorous security reviews.
- Collaboration with Industry Experts: Fostering partnerships with blockchain security firms and experts to leverage their knowledge and tools.
The South Korean NTS incident serves as a powerful, albeit costly, lesson. As the digital economy continues to evolve, the security of virtual assets will remain a paramount concern for both individuals and institutions. The imperative for governments to adapt, learn, and implement advanced security protocols is no longer merely a best practice but a critical necessity to prevent similar and potentially even larger financial catastrophes. The consequences of underestimating the unique security challenges of the blockchain world are clear: significant financial loss, erosion of public trust, and a stark reminder that in the realm of digital assets, operational oversight can translate directly into millions lost.






