
A recent analysis has unveiled a highly sophisticated cyber campaign, dubbed "Ruby Jumper," orchestrated by the North Korean state-sponsored group APT37, which leverages an innovative malware suite to bridge isolated network segments and facilitate surreptitious data exfiltration and surveillance. This operation signifies a critical evolution in the tactics of advanced persistent threats, specifically targeting environments traditionally considered impervious to remote intrusion. The discovery underscores a persistent and escalating challenge for cybersecurity professionals safeguarding sensitive and critical infrastructure globally.
The group identified as APT37, also known by aliases such as ScarCruft, Ricochet Chollima, and InkySquid, is a prolific state-sponsored entity with a documented history of espionage and intelligence-gathering operations primarily targeting South Korean entities, defectors, journalists, and government organizations. Their primary objective typically revolves around acquiring sensitive information to support North Korean strategic interests. Over the years, APT37 has demonstrated a consistent pattern of adapting its methodologies, incorporating zero-day exploits, sophisticated social engineering, and novel malware strains to bypass evolving security countermeasures. The emergence of the Ruby Jumper campaign further illustrates their commitment to enhancing their operational capabilities, particularly in overcoming formidable physical security barriers.

Air-gapped networks represent the pinnacle of network isolation, deliberately designed to prevent any direct electronic connection to external networks, including the public internet. This stringent isolation is typically achieved through a combination of physical and logical controls. Physically, air-gapped systems are disconnected from all network interfaces – Wi-Fi, Bluetooth, Ethernet, and even cellular modems – ensuring no electromagnetic pathways exist for data transfer. Logically, these systems often employ dedicated hardware, distinct operating systems, and rigorous access controls. Such environments are indispensable in sectors where data integrity and confidentiality are paramount, including critical national infrastructure (e.g., nuclear power plants, electrical grids), military command and control systems, classified research facilities, and high-security government networks. The fundamental premise of air-gapping is that without a direct network connection, data can only be moved in or out via physical media, primarily removable storage devices like USB drives. This method, while seemingly archaic, forms the Achilles’ heel that threat actors consistently attempt to exploit.
The "Ruby Jumper" campaign, meticulously dissected by cloud security researchers, reveals a meticulously crafted toolkit comprising five distinct malicious components: RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, and FOOTWINE. This arsenal is designed to systematically infiltrate, persist within, and exfiltrate data from air-gapped environments, transforming otherwise secure physical media into covert conduits for command and control (C2) and data egress.
The initial vector for this sophisticated intrusion typically involves social engineering, leading a victim to open a specially crafted Windows shortcut file (LNK). This seemingly innocuous action triggers a multi-stage infection process. The LNK file executes an embedded PowerShell script, which is responsible for extracting further payloads concealed within the LNK file itself. To maintain stealth and divert user attention, the script concurrently launches a decoy document. In a notable operational detail, researchers observed one such decoy document to be an Arabic translation of a North Korean newspaper article discussing the Palestine-Israel conflict, indicating a potential targeting interest in individuals or organizations engaged with Middle Eastern geopolitics or North Korean foreign policy narratives.

Following the initial compromise, the PowerShell script deploys RESTLEAF, the campaign’s first-stage implant. RESTLEAF establishes covert communication with APT37’s command-and-control infrastructure, ingeniously leveraging legitimate cloud services, specifically Zoho WorkDrive, to mask its malicious traffic. This tactic, known as "living off the land" or using legitimate services for malicious purposes, makes detection more challenging as network defenders often whitelist such services. RESTLEAF’s primary function is to retrieve encrypted shellcode from the C2 server, which subsequently downloads the next-stage payload.
This next-stage payload is SNAKEDROPPER, a Ruby-based loader. Its deployment signifies a notable departure from APT37’s historical reliance on more conventional programming languages for initial stages, suggesting a deliberate effort to diversify their toolkit and potentially evade signature-based detections. SNAKEDROPPER then proceeds to install a complete Ruby 3.3.0 runtime environment, including the interpreter, standard libraries, and the RubyGems infrastructure. This entire Ruby installation is meticulously disguised as a legitimate USB-related utility, typically named usbspeed.exe, further enhancing its camouflage. A critical step in SNAKEDROPPER’s execution involves modifying the RubyGems default file operating_system.rb with a malicious version. This modification ensures that the malicious code is automatically loaded every time the Ruby interpreter starts. Persistence is achieved through a scheduled task, rubyupdatecheck, configured to execute every five minutes, ensuring continuous operation of the threat.
The subsequent components downloaded are THUMBSBD and VIRUSTASK, both delivered as Ruby files (ascii.rb and bundler_index_client.rb, respectively). THUMBSBD functions as a robust backdoor with multiple capabilities. Its core functions include comprehensive system information collection, staging of command files received from the threat actor, and meticulous preparation of collected data for exfiltration. Crucially, THUMBSBD is designed to scan for connected USB drives, creating hidden directories on them and copying designated files into these covert locations. This sophisticated mechanism transforms removable storage devices into a bidirectional covert C2 relay, enabling APT37 to deliver commands to systems within air-gapped networks and, equally important, to extract sensitive data from them. This technique effectively bypasses the fundamental security premise of air-gapping by weaponizing the very method intended for secure data transfer.
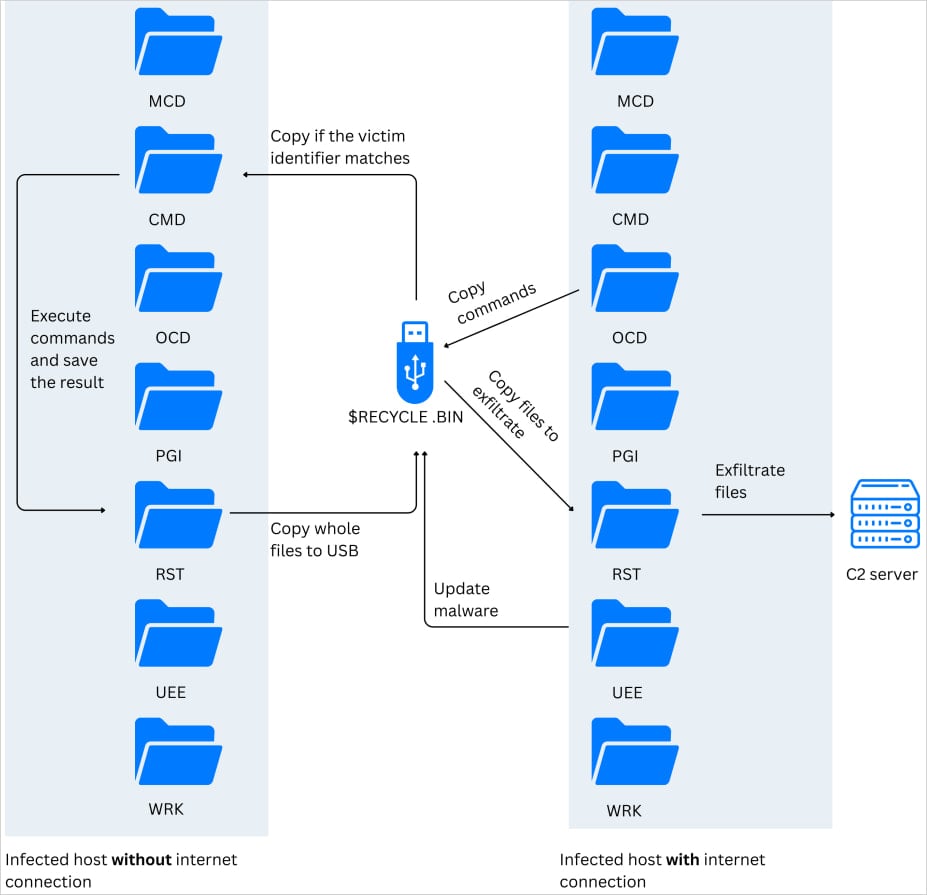
VIRUSTASK complements THUMBSBD by serving as the primary propagation mechanism for the Ruby Jumper campaign within air-gapped environments. Its role is to spread the infection to new, isolated machines. It achieves this by weaponizing removable drives: it hides legitimate files on the drive and replaces them with malicious shortcut files (LNKs). When a user opens one of these seemingly legitimate shortcuts, it surreptitiously executes the embedded Ruby interpreter, initiating the infection chain on the new machine. A subtle but effective control mechanism for VIRUSTASK is its conditional activation: the module will only trigger an infection process if the inserted removable media possesses at least 2GB of free space, likely to ensure adequate room for the embedded Ruby runtime and other payloads without immediately raising suspicion due to disk space issues.
The Ruby Jumper campaign also incorporates FOOTWINE, a powerful Windows spyware backdoor, cleverly disguised as an Android package file (APK). This component significantly enhances APT37’s surveillance capabilities, offering functionalities such as keylogging, screenshot capture, audio and video recording, comprehensive file manipulation, registry access, and the ability to execute remote shell commands. The inclusion of FOOTWINE underscores the campaign’s objective beyond mere data exfiltration, extending to deep, continuous monitoring of compromised systems. Furthermore, researchers observed the deployment of BLUELIGHT, a full-fledged backdoor previously attributed to APT37, confirming the group’s established presence and leveraging of their known arsenal within this new campaign.
Attribution of the Ruby Jumper campaign to APT37 is supported by a confluence of strong indicators. These include the consistent use of the BLUELIGHT malware, the characteristic reliance on LNK files for initial compromise, the two-stage shellcode delivery technique, and the specific C2 infrastructure patterns that align with APT37’s historical operational footprint. The nature of the decoy document, specifically its focus on North Korean media narratives, further strengthens the attribution by aligning with the known victim profiles and intelligence interests of this state-sponsored threat actor.
.jpg)
The implications of the Ruby Jumper campaign are profound for national security, critical infrastructure protection, and enterprise cybersecurity. For organizations operating air-gapped networks, this campaign serves as a stark reminder that physical isolation, while a robust defense, is not an impenetrable shield. The human element, coupled with the necessity of data transfer via removable media, remains a critical vulnerability. Organizations in defense, intelligence, energy, and advanced manufacturing sectors must reassess their removable media policies, implement stringent scanning protocols, and consider behavioral analytics even on isolated systems.
From a cybersecurity defense perspective, the use of Ruby-based malware poses detection challenges. Many traditional security solutions are heavily geared towards common scripting languages like PowerShell or compiled executables. The novelty of a full Ruby runtime environment, along with its legitimate-looking usbspeed.exe disguise, can enable it to fly under the radar of less sophisticated detection mechanisms. This necessitates a shift towards advanced endpoint detection and response (EDR) solutions that focus on behavioral anomalies, process injection, and unusual file system modifications, rather than solely relying on signature-based detection. The covert C2 relay via USB drives also emphasizes the need for robust network segmentation, even within air-gapped environments, and meticulous auditing of all data transfers across isolation boundaries.
Looking ahead, the Ruby Jumper campaign signals an escalating arms race in cyber warfare, particularly concerning critical infrastructure. State-sponsored actors will undoubtedly continue to innovate methods to breach the most secure environments. We can anticipate other sophisticated groups adopting similar techniques, leveraging obscure programming languages, legitimate cloud services, and weaponized removable media to achieve their objectives. Mitigating such advanced threats requires a multi-layered approach: strengthening physical security, implementing comprehensive insider threat programs, enforcing rigorous data handling protocols for removable media, investing in advanced threat intelligence sharing, and fostering a culture of cybersecurity awareness among all personnel, especially those interacting with air-gapped systems. The continuous adaptation of defensive strategies, mirroring the agility of threat actors like APT37, is paramount to safeguarding sensitive information and critical national assets in an increasingly complex cyber landscape.






