
A significant cybersecurity incident has afflicted ManoMano, the prominent European online marketplace for home improvement and DIY products, leading to the unauthorized disclosure of personal data belonging to approximately 38 million customers, stemming from a security lapse within a contracted service provider. The incident, discovered in January 2026, underscores the escalating vulnerabilities introduced by extensive reliance on third-party vendors in the contemporary digital supply chain, prompting widespread concern across the e-commerce sector and among regulatory bodies.
ManoMano, a French-headquartered e-commerce powerhouse, has carved a substantial niche in the European market, specializing in a diverse array of DIY, home improvement, and gardening products. Operating across key European economies including France, Belgium, Spain, Italy, Germany, and the United Kingdom, the platform boasts an impressive reach, reportedly attracting 50 million unique visitors monthly. This extensive customer base and operational footprint amplify the scale and potential ramifications of any data security compromise. The company’s recent notification to its vast customer base confirms a breach that emanated not from its core infrastructure, but from a subcontractor responsible for customer service operations.
The company initiated an internal investigation immediately upon detection of the unauthorized access in January 2026. Preliminary findings concluded that the personal information of a staggering 38 million individuals had been illicitly accessed and extracted. While specific technical details remain under wraps due to the ongoing nature of the investigation, the company has confirmed that the breach originated with a third-party customer service provider, often referred to as a "subcontractor" in their communications. This distinction is critical, as it points to the increasingly complex attack surface presented by interconnected digital ecosystems.

Earlier this month, a threat actor operating under the alias "Indra" publicly claimed responsibility for the ManoMano attack on a prominent cybercrime forum. This individual alleged possession of data pertaining to 37.8 million user accounts, alongside thousands of customer support tickets and associated attachments. While the slight discrepancy in the number of affected individuals (37.8 million versus the company’s confirmed 38 million) is minor, the claim corroborates the severity and extent of the data exfiltration. Unconfirmed intelligence reports suggest that the compromised entity was a customer support service provider based in Tunis, and that the breach may have involved vulnerabilities within the Zendesk platform utilized by this subcontractor. Should these reports be substantiated, it would highlight a common vector for data breaches: the exploitation of widely used software-as-a-service (SaaS) solutions by third-party providers.
The types of customer data exposed vary depending on the nature and extent of an individual’s interactions with ManoMano and its customer service channels. The compromised data categories are extensive and include, but are not limited to: email addresses, full names, postal addresses, telephone numbers, details of past orders, and comprehensive logs of customer service interactions. This aggregation of personal and transactional data represents a significant trove for malicious actors. It is paramount to note that ManoMano has emphasized that no customer account passwords were compromised during the incident, nor were any modifications made to data residing on the company’s core systems. While this mitigates the immediate risk of direct account takeovers, the exposure of other sensitive data still poses substantial threats.
The implications of such a comprehensive data exposure are multifaceted and severe. For affected individuals, the primary concern revolves around the heightened risk of sophisticated phishing, vishing (voice phishing), and smishing (SMS phishing) attacks. Cybercriminals can leverage the exposed email addresses, full names, and order details to craft highly personalized and convincing fraudulent communications. These tactics aim to trick victims into divulging further sensitive information, such as financial credentials or login details, or to install malware. The inclusion of postal addresses and phone numbers further amplifies the risk of identity theft, enabling fraudsters to open fraudulent accounts, divert mail, or conduct social engineering attacks that exploit personal information to bypass security protocols. Even without direct access to passwords, this granular level of detail significantly lowers the barrier for subsequent attacks.
From a corporate standpoint, the breach carries substantial reputational and financial consequences for ManoMano. Restoring customer trust after such a large-scale incident is a formidable challenge, potentially leading to customer churn and a tarnished brand image. Financially, the company faces significant costs associated with the ongoing investigation, forensic analysis, legal expenditures, potential regulatory fines, and possibly compensation or credit monitoring services for affected customers.

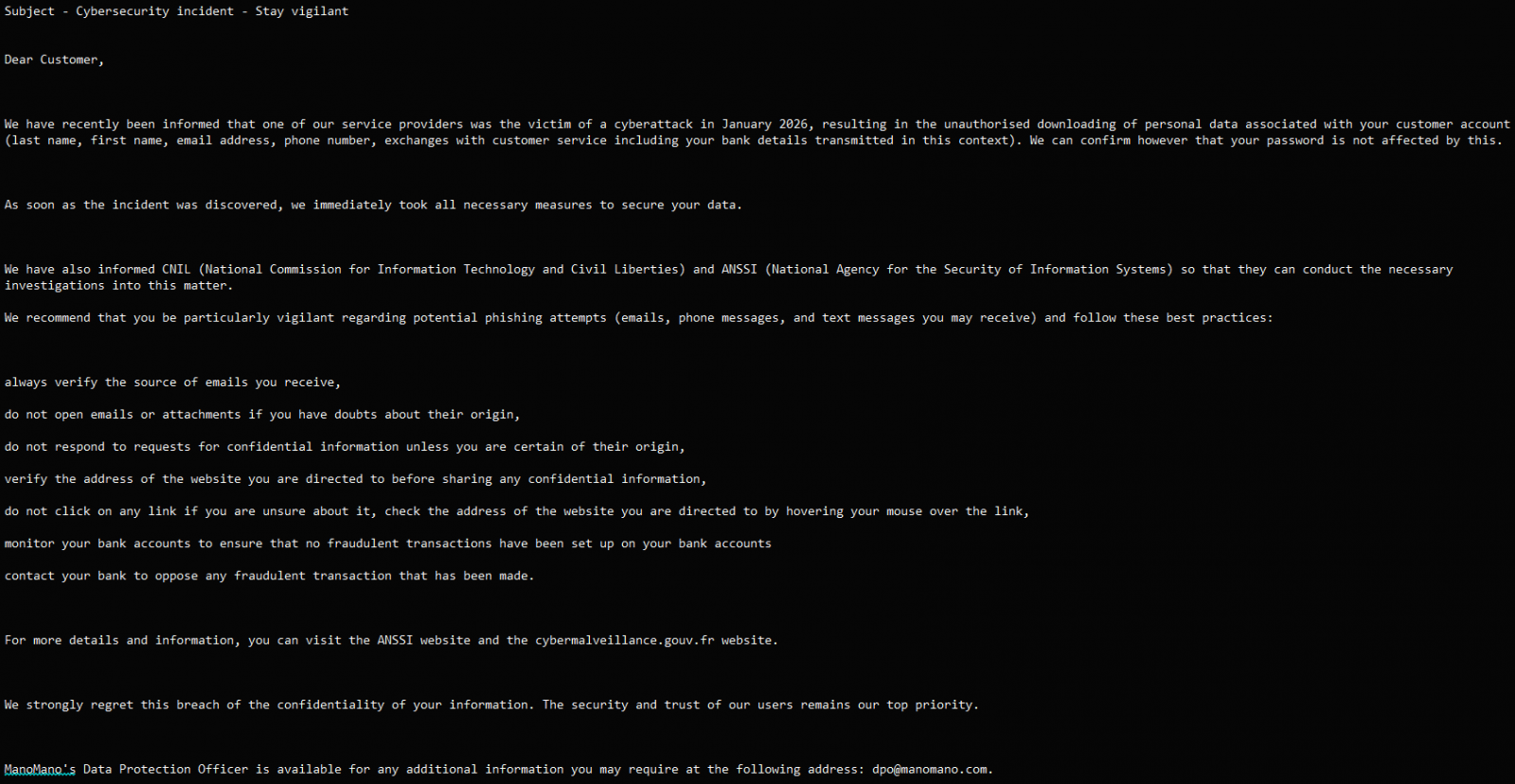
Upon discovering the unauthorized access, ManoMano asserts that it took immediate and decisive action to contain the breach. These measures included disabling the compromised access points, revoking the subcontractor’s access permissions to customer data, and implementing strengthened access controls and monitoring protocols across its systems. Furthermore, in compliance with European data protection regulations, ManoMano promptly notified relevant supervisory authorities, specifically mentioning France’s National Commission for Data Protection and Liberties (CNIL) and the National Agency for the Security of Information Systems (ANSSI). The company also initiated the process of informing all impacted customers, providing guidance to enhance their vigilance against potential follow-up attacks.
The customer notification shared by ManoMano includes crucial recommendations designed to help individuals mitigate their risk. These advisories typically counsel customers to scrutinize all incoming communications for authenticity, carefully verify sender identities, meticulously monitor their bank accounts and credit card statements for any suspicious or fraudulent transactions, and exercise extreme caution when encountering suspicious links or downloading attachments from unsolicited emails. While these are standard best practices, the sheer volume of exposed data necessitates a sustained period of heightened vigilance from affected individuals.
This incident serves as a potent reminder of the pervasive and growing threat of supply chain attacks. In today’s interconnected digital economy, organizations increasingly outsource various functions, from cloud hosting to customer support, to third-party vendors. While this strategy offers efficiency and specialized expertise, each vendor integration expands an organization’s attack surface. A vulnerability or security lapse within a single, seemingly peripheral subcontractor can have catastrophic ripple effects, compromising the data of the primary organization’s entire customer base.
To counter this escalating threat, robust third-party risk management (TPRM) programs are no longer merely advisable but are an absolute necessity. Such programs involve rigorous due diligence during vendor selection, including comprehensive security assessments and audits. Furthermore, strong contractual agreements must stipulate clear data security obligations, incident response protocols, and accountability frameworks. Continuous monitoring of third-party security postures, stringent access controls based on the principle of least privilege, and regular penetration testing of vendor systems are critical components. Organizations must also ensure that their incident response plans are holistic, encompassing scenarios where third-party systems are the initial point of compromise. The ManoMano breach highlights that even when core systems are secure, the weakest link in the extended digital supply chain can be exploited.
Looking ahead, the fallout from this breach will likely lead to increased scrutiny from regulators across Europe. Under the General Data Protection Regulation (GDPR), companies are held accountable for the data they control, regardless of where that data is processed. This includes data managed by third-party processors. Significant fines, potentially reaching up to 4% of a company’s annual global turnover, can be levied for non-compliance or inadequate security measures that lead to a breach. The ongoing investigation by ManoMano, in collaboration with authorities, will aim to uncover the full extent of the compromise, the precise vulnerabilities exploited, and any systemic weaknesses in the company’s or its subcontractor’s security architecture. Transparency throughout this process will be crucial for ManoMano to rebuild trust with its extensive customer base.
In conclusion, the ManoMano data breach represents a substantial cybersecurity event, impacting millions of European consumers and underscoring the critical importance of comprehensive supply chain security. As digital commerce continues its rapid expansion, the reliance on interconnected services will only grow. This incident serves as a stark illustration that an organization’s security posture is only as strong as its weakest link, emphasizing the imperative for businesses to extend their cybersecurity vigilance far beyond their immediate operational perimeters to encompass every entity within their digital ecosystem. The long-term implications for ManoMano and the broader e-commerce landscape will depend significantly on the efficacy of their response, their commitment to enhanced security protocols, and the evolving regulatory landscape concerning third-party data stewardship.






