
Taiwanese networking equipment manufacturer Zyxel has issued a critical security advisory, urging customers to promptly deploy firmware updates addressing a severe vulnerability that permits unauthenticated remote command execution on numerous router models and other network devices. This significant security flaw, tracked as CVE-2025-13942, represents a substantial risk, potentially allowing threat actors to gain complete control over affected devices without requiring any prior authentication. The widespread nature of Zyxel’s products, often deployed as default equipment by internet service providers globally, amplifies the potential impact of this discovery, necessitating immediate attention from users and network administrators.
The core of the vulnerability, identified as a command injection flaw, resides within the Universal Plug and Play (UPnP) function present in a diverse range of Zyxel products. This includes various Zyxel 4G LTE/5G NR Customer Premises Equipment (CPE), DSL/Ethernet CPE, Fiber Optical Network Terminals (ONTs), and wireless extenders. Attackers can exploit this weakness by crafting malicious UPnP Simple Object Access Protocol (SOAP) requests, which, when processed by a vulnerable device, compel it to execute arbitrary operating system commands. Such a capability grants an attacker extensive control, ranging from data exfiltration and device misconfiguration to the establishment of persistent backdoors or inclusion in botnets.
While the severity of remote command execution (RCE) vulnerabilities is inherently high, Zyxel’s advisory notes specific prerequisites for successful exploitation of CVE-2025-13942, which may somewhat limit its immediate broad impact. Crucially, for a remote attack to succeed, both the UPnP function and WAN (Wide Area Network) access to the device’s management interface must be enabled. Zyxel emphasizes that WAN access is typically disabled by default on these devices, thereby providing a layer of inherent protection for users who adhere to default configurations. However, any deviation from these defaults—whether due to user modification, ISP provisioning, or previous compromise—could expose devices to exploitation. Despite these mitigating factors, the potential for unauthenticated RCE underscores the imperative for all users to install the provided security patches without delay, ensuring their network infrastructure remains optimally protected against evolving threats.
In addition to the critical RCE flaw, Zyxel simultaneously released patches for two other high-severity vulnerabilities. These are post-authentication command injection flaws, designated CVE-2025-13943 and CVE-2026-1459. Unlike the unauthenticated RCE, these vulnerabilities require an attacker to first obtain valid credentials for the device. Once authenticated, threat actors could leverage these flaws to execute operating system commands, further compromising the device’s integrity and potentially gaining deeper access to the network. While requiring prior authentication, these vulnerabilities still pose a significant risk, particularly in scenarios where default or weak credentials are in use, or where credentials have been compromised through other means, such as phishing or brute-force attacks. The cumulative effect of these disclosures highlights a period of heightened security scrutiny for Zyxel’s product portfolio.

The widespread adoption of Zyxel devices across global networks significantly amplifies the implications of these vulnerabilities. Zyxel boasts a formidable presence, with over a million businesses and countless home users across 150 markets relying on its networking products. Many of these devices are deployed as standard equipment by internet service providers, making them ubiquitous in both residential and small-to-medium business environments. This broad footprint renders Zyxel devices attractive targets for cybercriminals seeking to establish large botnets, conduct reconnaissance, or launch further attacks against connected networks.
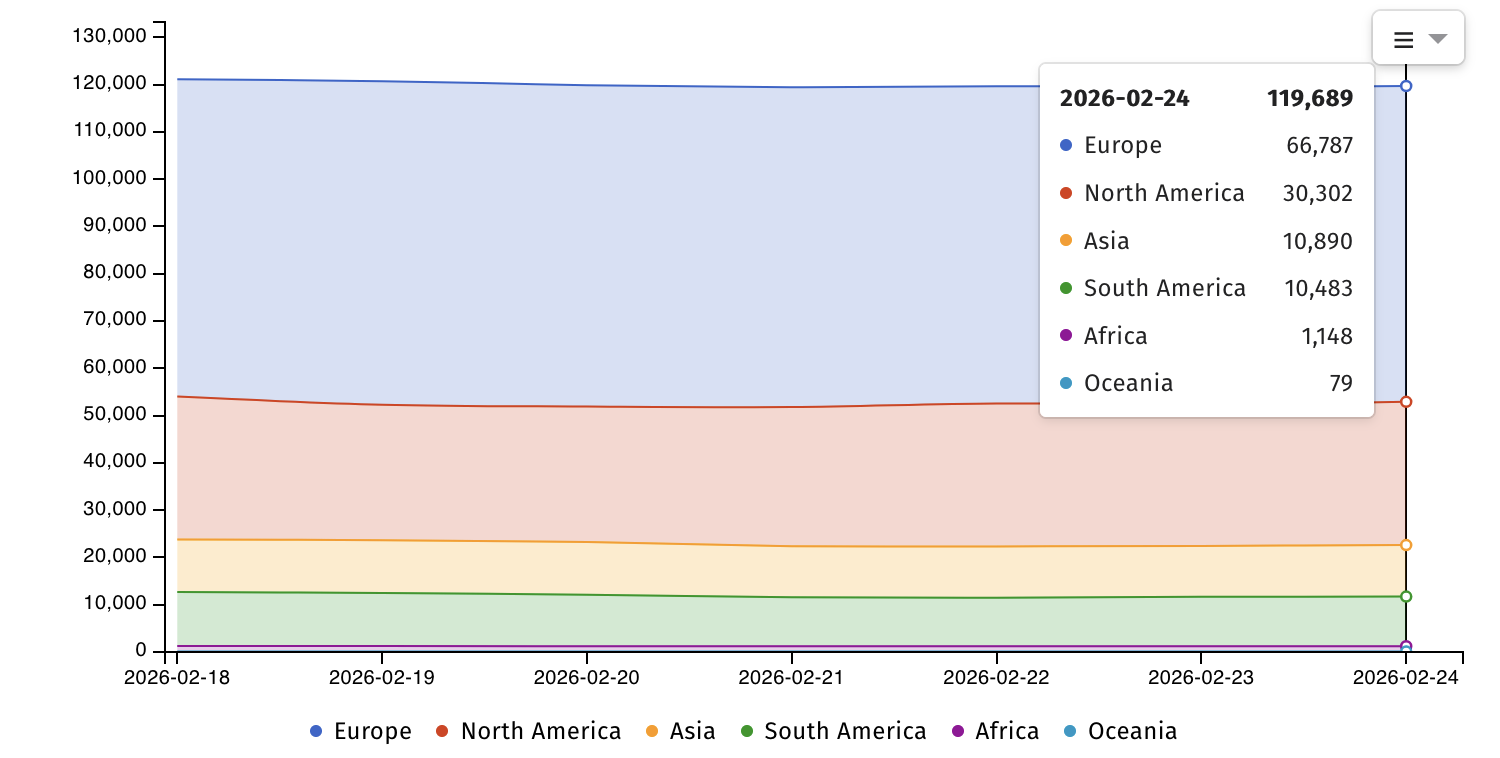
Data from internet security watchdog Shadowserver corroborates this extensive exposure, identifying nearly 120,000 internet-exposed Zyxel devices, with over 76,000 specifically categorized as routers. This considerable attack surface presents a persistent opportunity for malicious actors to scan for and exploit known vulnerabilities. The sheer volume of accessible devices underscores the urgency of Zyxel’s patching efforts and the critical need for users to implement these updates. Each unpatched device contributes to the global pool of vulnerable systems, increasing the overall risk landscape for critical infrastructure and individual users alike.
This latest series of advisories is not an isolated incident but rather fits into a broader pattern of security challenges faced by Zyxel and the networking equipment industry. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) currently tracks 12 Zyxel vulnerabilities that have been, or are still being, actively exploited in the wild, impacting routers, firewalls, and Network Attached Storage (NAS) devices. This history underscores the constant pressure on manufacturers to maintain robust security postures throughout the product lifecycle and the ongoing efforts by adversaries to identify and exploit weaknesses in widely deployed hardware.
Further complicating the security landscape, Zyxel recently issued a separate warning regarding a pair of zero-day vulnerabilities (CVE-2024-40891 and CVE-2024-40891, likely a typo for two distinct CVEs) actively exploited in attacks. These flaws affect several end-of-life (EOL) router models, for which the company explicitly stated it has no plans to release patches. The affected models include VMG1312-B10A, VMG1312-B10B, VMG1312-B10E, VMG3312-B10A, VMG3313-B10A, VMG3926-B10B, VMG4325-B10A, VMG4380-B10A, VMG8324-B10A, VMG8924-B10A, SBG3300, and SBG3500. Zyxel’s recommendation for users of these EOL devices is unequivocal: replace them with newer-generation products that receive ongoing security support. This stance, while understandable from a product lifecycle management perspective, presents a significant challenge for users who may be unaware their devices are EOL or lack the resources to immediately upgrade, leaving a segment of the user base perpetually exposed to known, unpatched threats.
Expert Analysis and Implications

The critical RCE flaw in Zyxel devices highlights several recurring themes in cybersecurity, particularly concerning consumer and small business networking equipment. The reliance on UPnP, a protocol designed for ease of use rather than stringent security, often creates exploitable pathways. UPnP automatically configures network devices for applications like gaming or media streaming by opening ports and directing traffic, bypassing traditional firewall controls. While convenient, this automation can inadvertently expose internal services to the internet, creating a significant attack surface if not meticulously managed or if the underlying implementation is flawed, as is the case here. Security best practices typically recommend disabling UPnP unless absolutely necessary and, even then, exercising extreme caution.
Remote Command Execution is one of the most severe categories of vulnerabilities because it grants an attacker the ability to execute arbitrary code on the target system. For a networking device like a router, this means an attacker can:
- Establish Persistence: Install malware, rootkits, or backdoors that survive reboots.
- Network Pivoting: Use the compromised router as a beachhead to launch attacks against other devices on the internal network.
- Data Interception: Monitor or redirect network traffic, potentially capturing sensitive information.
- Service Disruption: Cause denial of service by reconfiguring or crashing the device.
- Botnet Recruitment: Enroll the device into a botnet for distributed denial-of-service (DDoS) attacks, spam campaigns, or cryptocurrency mining.
The combination of UPnP exposure and RCE capability creates an incredibly potent threat. Even with WAN access disabled by default, misconfigurations are common, and internal network compromises could still lead to exploitation. This situation underscores the broader challenges of securing the "edge" of the network, where many IoT and consumer-grade devices often lack the robust security features and consistent patching cycles of enterprise-grade equipment.
Mitigation and Recommendations
For users of affected Zyxel products, immediate action is paramount.
- Apply Firmware Updates: The most critical step is to install the latest security patches provided by Zyxel. Users should visit the official Zyxel support website for their specific model to download and apply the updates.
- Disable UPnP: If UPnP functionality is not strictly required for specific applications, it should be disabled in the device’s administrative settings. This removes a significant attack vector.
- Disable WAN Management Access: Ensure that administrative access to the router’s management interface from the Wide Area Network (internet) is disabled. This is typically the default setting but should be verified. Access should only be permitted from trusted devices within the local network.
- Strong, Unique Credentials: Use strong, unique passwords for all administrative accounts on Zyxel devices. Avoid default credentials and regularly change passwords.
- Network Segmentation: For businesses, consider segmenting networks to isolate critical systems. If a router is compromised, network segmentation can limit an attacker’s ability to move laterally across the network.
- Regular Monitoring: Implement network monitoring to detect unusual traffic patterns or unauthorized access attempts.
- Replace EOL Devices: For users still operating Zyxel’s end-of-life devices, the recommendation to upgrade to newer, supported products is critical. Continuing to use unpatched EOL hardware represents an unacceptable security risk.
Future Outlook
The continuous stream of vulnerabilities in networking hardware, particularly in devices widely distributed by ISPs, highlights an ongoing tension between convenience, cost-effectiveness, and security. As more devices become interconnected and the attack surface expands, the onus on manufacturers to implement security-by-design principles and provide long-term security support grows. Similarly, ISPs and end-users must become more proactive in device management, moving beyond a "set it and forget it" mentality.
The future of network security at the edge will likely involve:
- Enhanced Supply Chain Security: Greater scrutiny on the security of components and software libraries used in device firmware.
- Automated Updates: More seamless and automated firmware update mechanisms to ensure users receive patches promptly without manual intervention.
- Improved User Interfaces: Simpler, more intuitive security configurations that guide users toward secure practices.
- Increased User Awareness: Ongoing educational efforts to inform users about the risks associated with vulnerable devices and the importance of security hygiene.
Ultimately, securing the vast landscape of connected devices requires a collaborative effort from manufacturers, service providers, and end-users to mitigate the pervasive threat of remote exploitation and maintain a resilient digital infrastructure.






