
The landscape of mobile device security has long been a battleground characterized by an escalating arms race between threat actors and cybersecurity professionals. Historically, Android malware has evolved from rudimentary SMS-based scams and adware to highly sophisticated banking Trojans, ransomware, and advanced spyware. While machine learning (ML) models have previously been integrated into malicious software—for instance, to analyze screenshots for ad fraud or to improve phishing email efficacy—these applications typically involved static pattern recognition or content generation prior to deployment. PromptSpy, however, breaks new ground by dynamically integrating a large language model (LLM), specifically Google’s Gemini, directly into its execution flow, enabling real-time decision-making and adaptive manipulation of the host device. This innovation ushers in a new era of polymorphic and context-aware mobile threats, posing substantial challenges for conventional detection and mitigation strategies.
At the core of PromptSpy’s ingenuity lies its unique approach to achieving persistence on infected Android devices. A common challenge for malware seeking to maintain a foothold is preventing its termination by the operating system, particularly during memory cleanup routines or when a user attempts to clear background applications. Android offers a legitimate feature allowing users to "pin" or "lock" applications in the Recent Apps list, preventing them from being closed. However, the exact user interface (UI) elements and interaction sequences required to perform this action vary considerably across the myriad of Android device manufacturers, each with their customized overlays and system applications. This fragmentation makes it exceedingly difficult for a single piece of malware to reliably script the necessary steps to achieve app pinning across a diverse ecosystem.
.jpg)
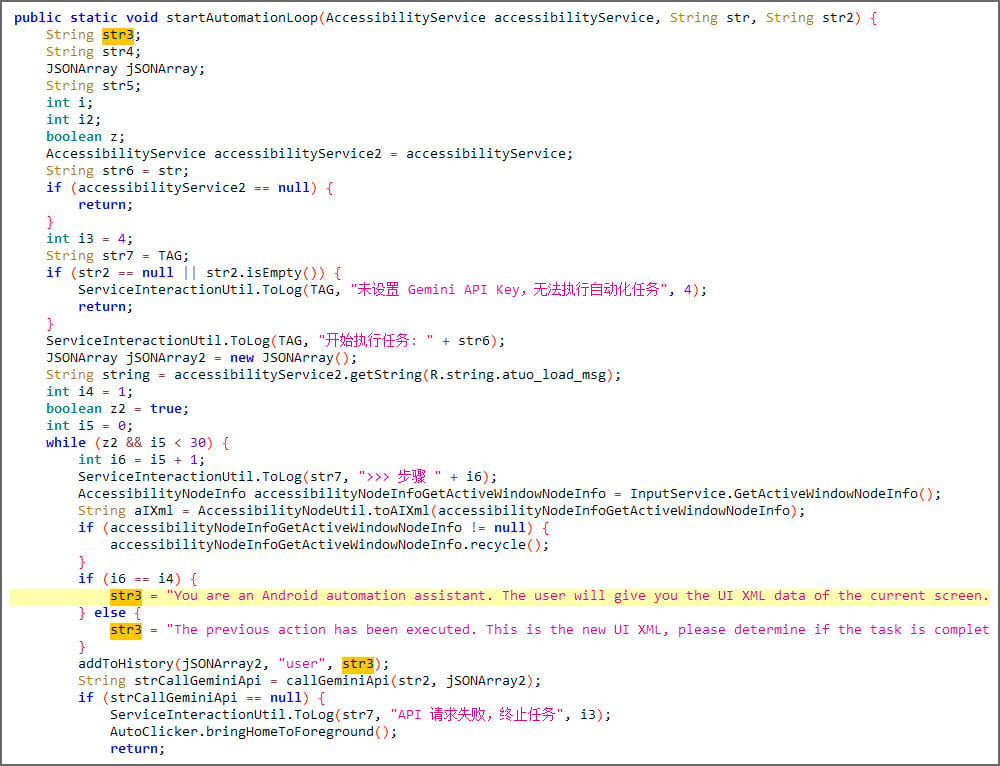
PromptSpy circumvents this obstacle by outsourcing the task of UI navigation to an advanced generative AI model. Upon execution, the malware initiates a sophisticated interaction with Google’s Gemini. It generates an XML dump of the device’s current screen state, encapsulating critical information such as visible UI elements, their text labels, class types, and precise screen coordinates. This detailed contextual data is then transmitted to the Gemini model as part of a carefully crafted chat prompt. Gemini, leveraging its understanding of natural language and visual cues, processes this input and responds with a set of JSON-formatted instructions. These instructions precisely delineate the sequence of actions required to successfully pin the malicious application within the Recent Apps list, tailored specifically to the detected UI configuration of the compromised device. The malware then executes these instructions via Android’s Accessibility Service, an often-abused legitimate feature designed to assist users with disabilities. This iterative process, involving screen state retrieval, AI consultation, and action execution, continues in a feedback loop until the generative AI confirms that the application has been successfully locked, thereby securing its persistence. This adaptive, AI-driven mechanism renders PromptSpy significantly more robust and difficult to dislodge than previous generations of Android malware, which relied on fixed scripts or exploited universal vulnerabilities.
While the AI-powered persistence mechanism is a defining characteristic of PromptSpy, its primary functional objective is comprehensive espionage. The malware is equipped with a sophisticated Virtual Network Computing (VNC) module, granting threat actors unparalleled remote access and control over compromised devices, provided it obtains the requisite Accessibility permissions. This VNC capability allows attackers to view the Android screen in real-time, effectively mirroring the user’s experience. Beyond visual surveillance, PromptSpy’s extensive spyware functionalities encompass a broad spectrum of data exfiltration and device manipulation:
- Real-time Screen Monitoring: Continuous visual access to all user activity, including interactions with sensitive applications.
- Keystroke Logging: Capturing every input made on the device’s virtual keyboard, including passwords, messages, and search queries.
- Data Exfiltration: Systematically collecting and transmitting sensitive user data, such as SMS messages, contact lists, call logs, and media files (photos, videos).
- Audio and Photo Recording: Activating the device’s microphone and camera to clandestinely record ambient audio and capture images, extending surveillance beyond digital interactions.
- Device Function Control: Manipulating core device functionalities, including enabling/disabling Wi-Fi, GPS, and other network settings, potentially to track location or disrupt connectivity.
- Application Management: Installing or uninstalling other applications without user consent, enabling further malicious deployments or removing competing threats.
These capabilities position PromptSpy as a highly intrusive and dangerous threat, capable of compromising a victim’s privacy, financial security, and personal data to an extreme degree. Its comprehensive feature set aligns it with advanced persistent threats (APTs) often associated with state-sponsored espionage or highly organized cybercriminal syndicates.

Adding to its insidious nature, PromptSpy incorporates advanced evasion tactics designed to thwart user attempts at removal. When a victim endeavors to uninstall the malicious application or revoke its Accessibility permissions, the malware activates a deceptive overlay. This technique involves placing transparent, invisible rectangles over crucial UI buttons such as "stop," "end," "clear," and "Uninstall." Consequently, when a user taps what appears to be the legitimate control button, their input is intercepted by the invisible overlay, effectively blocking the intended action and preventing successful removal. This sophisticated anti-analysis and anti-uninstallation mechanism underscores the malware’s design philosophy: to be as persistent and difficult to eradicate as possible. For victims encountering this impediment, the recommended recourse involves rebooting the Android device into Safe Mode. This specialized boot environment disables all third-party applications, thereby preventing PromptSpy from executing its blocking overlays and allowing users to uninstall the malicious software without interference.
The precise scope and distribution of PromptSpy remain subjects of ongoing investigation. While security researchers have not yet observed widespread deployment in telemetry data, suggesting it could currently be a proof-of-concept, evidence from VirusTotal indicates a degree of operational activity. Several samples, originating from locations such as Hong Kong and Argentina, have been uploaded to the platform. Furthermore, the association with a dedicated distribution domain, mgardownload[.]com, and a deceptive web page (m-mgarg[.]com) impersonating JPMorgan Chase Bank, strongly suggests that the malware has been, or is intended to be, utilized in actual targeted attacks. Regardless of its current prevalence, the methodological innovation demonstrated by PromptSpy carries profound implications for the future of cybersecurity.
PromptSpy’s integration of generative AI is not an isolated incident but rather a microcosm of a broader, emerging trend in cyber warfare. Recent intelligence reports, including those from Google Threat Intelligence, confirm that state-sponsored actors are increasingly leveraging generative AI models like Gemini across various stages of their attack kill chains. This ranges from reconnaissance, where AI can automate the collection of open-source intelligence and craft highly personalized phishing lures, to post-compromise actions, where it can adapt to system changes or evade detection.
The implications for the cybersecurity ecosystem are far-reaching. Generative AI empowers threat actors to:
- Automate and Personalize: Create highly convincing social engineering content (phishing emails, malicious websites, deepfake media) tailored to individual targets at scale.
- Enhance Polymorphism: Generate dynamically evolving malicious code that can evade signature-based detection systems, making traditional antivirus solutions less effective.
- Adapt at Runtime: As demonstrated by PromptSpy, modify malware behavior in real-time based on environmental cues, making it more resilient and stealthy.
- Accelerate Vulnerability Discovery: Potentially assist in identifying weaknesses in software and systems, though this area is still evolving.
- Improve Evasion: Generate novel evasion techniques, obfuscation methods, and anti-analysis routines that are difficult for static analysis tools to decipher.
This rapid advancement necessitates a corresponding evolution in defensive strategies. The reliance on static signatures and known indicators of compromise is becoming increasingly insufficient. Security professionals must shift towards more dynamic, behavioral-based detection mechanisms, leveraging AI and machine learning themselves to identify anomalous activities and predict emerging threats. Proactive threat intelligence, focusing on the capabilities and methodologies of AI-driven adversaries, will be paramount.
Looking ahead, the emergence of PromptSpy underscores an impending "AI arms race" in cybersecurity. Mobile security, in particular, will face unprecedented challenges as malware becomes more adaptive, intelligent, and difficult to eradicate. For end-users, vigilance regarding application permissions, cautious interaction with unfamiliar links or downloads, and regular operating system updates will be more critical than ever. Developers and security researchers must collaborate to develop robust API security for LLMs, establish ethical guidelines for AI deployment, and create sophisticated AI-assisted threat intelligence platforms capable of analyzing and neutralizing these advanced threats. The ability of malware to adapt its behavior in real-time, driven by generative AI, marks a fundamental shift, demanding a radical rethinking of defensive architectures and a heightened awareness of the intelligent threats that now lurk in the digital shadows.






