
A sophisticated and deeply entrenched Android malware, designated ‘Keenadu,’ has been meticulously uncovered, revealing its pervasive ability to compromise mobile devices through various vectors, including pre-installed firmware, system applications, and even seemingly legitimate offerings on Google Play. This multi-pronged attack vector grants the threat actors unparalleled control over infected devices, posing a significant risk to user data integrity and privacy across a global scale.
The discovery, detailed in a comprehensive report by cybersecurity researchers, illuminates Keenadu’s advanced capabilities, which position it as one of the more insidious mobile threats observed in recent years. Unlike typical malware that might reside in user-installed applications, Keenadu demonstrates a concerning capacity for deep system integration, particularly through its firmware-embedded variants. This deep integration is pivotal to its enduring persistence and its ability to circumvent standard security protocols designed to protect Android users. The malware essentially operates with elevated privileges, capable of compromising virtually every application on a device and executing arbitrary code, thus transforming a user’s smartphone or tablet into a fully controlled node within a malicious network.
Researchers have identified multiple distinct variants of Keenadu, each tailored with a specific set of functionalities and distribution methods. The most potent and alarming iteration is undoubtedly the one integrated directly into the device’s firmware. This pre-installation at the manufacturing or supply chain stage means that a device can be compromised before it even reaches the end-user, establishing a persistent foothold that is exceptionally difficult, if not impossible, to eradicate using conventional means. This method bypasses most user-level security measures and even factory resets, as the malicious code resides within the foundational software layer of the device itself.

Beyond firmware, Keenadu’s distribution mechanisms highlight a broad and adaptive strategy. It has been observed propagating through compromised Over-The-Air (OTA) updates, which are typically trusted channels for device maintenance and security patches. This tactic exploits the inherent trust users place in official software updates. Furthermore, the malware has been found embedded within critical system applications, granting it inherent elevated permissions from the outset. Modified applications downloaded from unofficial sources also serve as a vector, a common route for less sophisticated malware but one that Keenadu effectively leverages. Most concerningly, analysis confirmed the presence of Keenadu loaders within applications hosted on Google Play, the official Android app store, demonstrating the threat actors’ ability to bypass stringent security checks designed to protect millions of users.
As of early 2026, cybersecurity experts have confirmed over 13,000 devices globally have fallen victim to Keenadu. The geographic distribution of these infections is widespread, with significant concentrations observed in Russia, Japan, Germany, Brazil, and the Netherlands. This international footprint underscores the global reach and indiscriminate nature of the threat, indicating either a broad targeting strategy or opportunistic infections wherever the compromised devices or applications are distributed. The presence in diverse markets suggests a well-resourced operation capable of managing a geographically dispersed victim base.
The sophistication and modus operandi of Keenadu bear striking resemblances to previously identified firmware-level threats, notably the Triada malware family. Triada, which surfaced in counterfeit Android devices, primarily low-cost smartphones routed through less regulated supply chains, also demonstrated the ability to be pre-installed in device firmware. The comparison to Triada is crucial as it highlights a persistent and evolving challenge within the Android ecosystem: the vulnerability of the supply chain, particularly for devices from less reputable manufacturers or those sold through unofficial channels. This pattern suggests that threat actors are consistently targeting points of weakness early in the device lifecycle to establish deep, enduring infections.

Intriguing clues regarding Keenadu’s potential origin have emerged from its operational parameters. The firmware-integrated variant exhibits a peculiar behavior: it deactivates if the device’s language or timezone settings are associated with China. This geographic exclusion could serve as an evasion tactic to avoid detection within a specific region or might offer a subtle hint about the threat actor’s provenance, suggesting an origin outside of or a deliberate avoidance of Chinese territories for operational reasons. Additionally, the malware ceases operation if Google Play Store and Play Services are not detected on the device, indicating a dependency on the standard Android environment, likely for command and control communications or specific exploitation techniques reliant on Google’s mobile services framework.
While current observations indicate that Keenadu’s primary operational focus revolves around ad fraud, the true breadth of its capabilities extends far beyond this initial objective. Researchers unequivocally state that Keenadu functions as a fully operational backdoor, providing its operators with virtually unfettered control over a compromised device. This level of access translates into a profound risk for data theft and a wide array of malicious actions. The malware can inject itself into every installed application, enabling it to pilfer sensitive information such as media files, private messages, banking credentials, and precise location data. Disturbingly, it has also been observed monitoring search queries entered by users into the Chrome browser, even when operating in incognito mode, underscoring its capacity for deep surveillance and privacy violation. The ability to install any application from APK files and grant them arbitrary permissions further solidifies its status as a comprehensive control mechanism, transforming infected devices into tools for espionage, financial fraud, or broader cybercriminal enterprises.
The Keenadu variant embedded within system applications, while somewhat more limited in its deepest functionalities compared to the firmware version, still maintains significant privileges. Its integration into essential system components, such as a facial recognition application commonly used for device unlocking and authentication, allows it to operate with elevated system-level permissions. This enables the silent installation of additional applications without user consent or notification, effectively establishing a covert channel for further compromise or the deployment of secondary payloads. The exploitation of fundamental system processes highlights a sophisticated understanding of the Android operating system’s architecture.
.png)
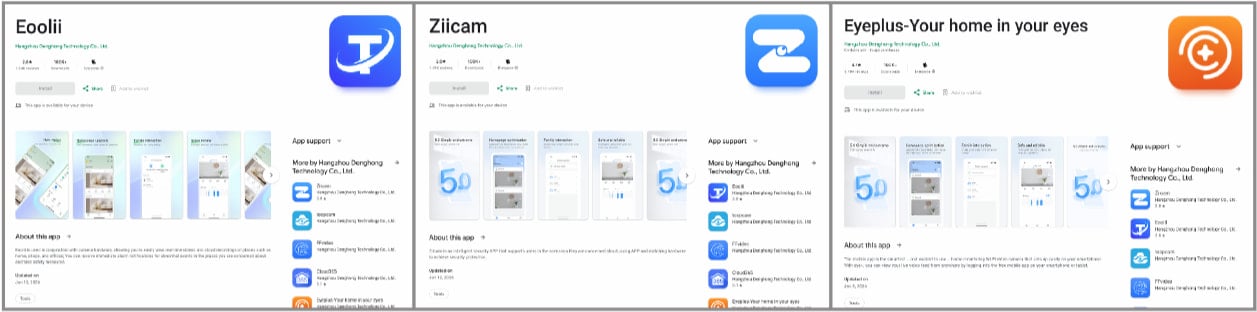
The most public-facing distribution vector, and arguably one of the most concerning, involved applications found on Google Play. Researchers identified malicious "smart home camera apps" that contained Keenadu loaders, collectively accumulating over 300,000 downloads before being removed from the official Android store. These applications, upon execution, launched invisible web browser tabs in the background, navigating to predetermined websites without the user’s knowledge. This stealthy activity mirrors techniques previously documented in other Android malware families, indicating a shared understanding of evasion tactics or potentially a common toolkit among various threat groups. The successful infiltration of Google Play, despite Google’s continuous efforts to enhance its security scanning and app vetting processes, underscores the persistent cat-and-mouse game between malicious actors and platform defenders.
Concrete evidence of firmware compromise was further substantiated by findings on specific hardware. Keenadu was detected in the firmware of Android tablets from multiple manufacturers, including the Alldocube iPlay 50 mini Pro (T811M) tablet, where the malicious firmware image was dated August 18, 2023. This timeline is critical, aligning with a public acknowledgement from Alldocube in March 2024 regarding a "virus attack through OTA software" that led to malware insertion into their firmware. While the company did not specify the exact nature of the threat at the time, this incident strongly corroborates the researchers’ findings and highlights a direct compromise within the supply chain or OTA update infrastructure of a device manufacturer.
A detailed technical analysis of the Keenadu backdoor reveals its method of achieving deep system compromise: it specifically targets and modifies the libandroid_runtime.so component. This library is a core, fundamental element of the Android operating system, responsible for bridging the Android application framework with the underlying native runtime. By compromising libandroid_runtime.so, Keenadu gains the ability to operate "within the context of every app on the device." This unparalleled access means the malware can intercept, modify, or inject code into any application, effectively making it omnipresent and granting it control over all user activities and data. This level of deep system manipulation is indicative of highly advanced malware engineering.
The implications of Keenadu’s firmware-embedded nature are profound, particularly concerning remediation. Due to its deep integration into the foundational software of the device, the malware is impossible to remove using standard Android OS tools or even factory resets. These conventional methods only affect the user-accessible partitions, leaving the malicious firmware intact. For affected users, the recommended course of action is extremely challenging: sourcing and installing a clean, verified firmware version for their specific device model. This process is inherently risky, requiring technical expertise and potentially leading to the "bricking" of the device if an incompatible or corrupted firmware is flashed.
Given the complexities and risks associated with self-remediation, one of the safest, albeit most drastic, recommendations is to cease using the compromised device entirely and replace it with a new product acquired from trusted vendors and authorized distributors. This emphasizes the critical importance of secure supply chains and purchasing decisions in mitigating sophisticated, pre-installed threats.
The emergence of Keenadu serves as a stark reminder of the evolving threat landscape in mobile security. It highlights the increasing sophistication of malicious actors who are now targeting deeper layers of the operating system and exploiting vulnerabilities in the hardware supply chain. For consumers, this necessitates increased vigilance regarding device provenance and software sources. For manufacturers, it underscores the imperative for robust security protocols throughout the entire product lifecycle, from initial design and component sourcing to manufacturing, software development, and OTA update delivery. The battle against threats like Keenadu demands a multi-faceted approach involving enhanced industry collaboration, rigorous security audits, and continuous innovation in threat detection and prevention across the entire mobile ecosystem.






