Recent intelligence indicates a highly focused and automated cyber campaign, with a single threat actor executing the vast majority of attacks targeting critical vulnerabilities within Ivanti Endpoint Manager Mobile (EPMM). This sophisticated entity has demonstrated a wide-ranging operational scope, leveraging resilient infrastructure to exploit severe remote code execution flaws not only in Ivanti products but also across multiple other high-value enterprise applications, signaling a significant and coordinated threat to global digital infrastructure.
The cybersecurity community has been alerted to an alarming concentration of malicious activity surrounding two critical security flaws in Ivanti Endpoint Manager Mobile (EPMM), identified as CVE-2026-21962 and CVE-2026-24061. These vulnerabilities, both rated with critical severity, permit unauthenticated code injection, culminating in remote code execution (RCE) on susceptible systems. Such a capability grants attackers complete control over compromised devices, posing an existential threat to organizational data integrity, operational continuity, and overall security posture. The urgency of the situation was underscored by Ivanti’s prompt security advisories, which confirmed active exploitation as zero-day attacks and provided immediate hotfixes to mitigate the immediate risk.
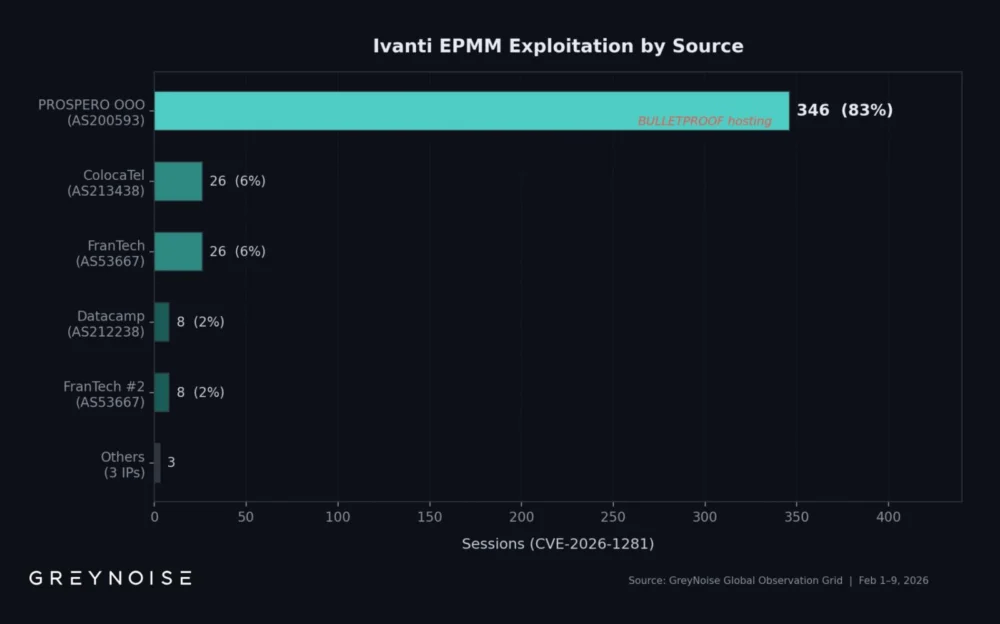
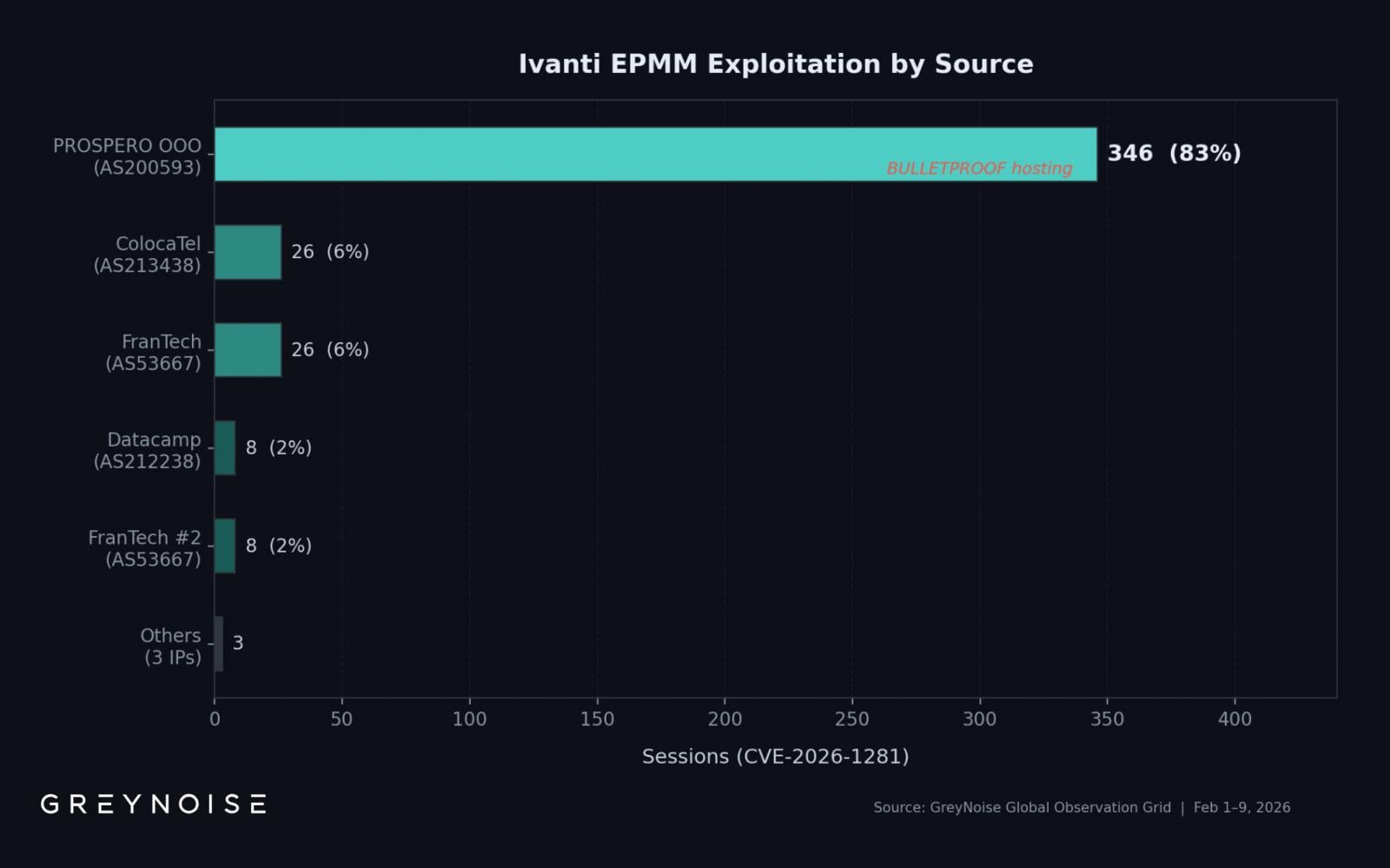
Analysis of threat intelligence observations reveals a striking pattern: a solitary threat actor is responsible for an overwhelming 83% of the observed exploitation attempts related to these two Ivanti EPMM vulnerabilities. This level of concentration is highly unusual in the landscape of widespread vulnerability exploitation, which often involves a more dispersed set of actors. The attacker’s operational base is traced to a specific IP address, 193[.]24[.]123[.]42, which is hosted within infrastructure notoriously characterized as "bulletproof." This designation signifies a service provider (PROSPERO OOO, operating under AS200593) known for its tolerance of illicit activities, offering resilience against takedowns and obscuring the true identity and location of its clients.

Between February 1st and February 9th, a comprehensive monitoring platform documented 417 distinct exploitation sessions originating from a limited pool of eight unique source IP addresses. The dominant IP, 193[.]24[.]123[.]42, accounted for the vast majority of this activity, specifically targeting CVE-2026-21962 and CVE-2026-24061. This singular focus from a hardened infrastructure provider points to a well-resourced and determined adversary, potentially operating with specific strategic objectives rather than engaging in opportunistic mass scanning.
The intensity of this campaign was not uniform but rather punctuated by a dramatic surge. On February 8th, the monitoring platform recorded an astonishing 269 exploitation sessions in a single day. This figure represents an almost thirteen-fold increase over the daily average of 22 sessions observed during the monitoring period, indicating a deliberate escalation of activity. Such a spike could signify a concerted effort to maximize compromises within a narrow window, perhaps in anticipation of increased defensive measures or patch deployments, or to capitalize on a specific time when target systems might be less actively monitored.
A significant proportion of the exploitation attempts, specifically 354 out of the 417 recorded sessions (85%), employed Out-of-Band Application Security Testing (OAST)-style DNS callbacks. This sophisticated technique is a hallmark of initial access broker (IAB) activity. OAST callbacks allow an attacker to verify the successful execution of injected code without establishing a direct, persistent connection to the compromised system. Instead, the compromised system is instructed to perform a DNS lookup for a unique, attacker-controlled domain. The successful resolution of this lookup confirms to the attacker that their code has executed, providing a stealthy and efficient method for validating vulnerabilities and confirming initial access. This modus operandi strongly suggests that the primary objective of this actor may be to gain and then potentially sell access to compromised networks, rather than to immediately deploy further payloads such as ransomware.

A critical observation from the ongoing analysis is that the primary IP address associated with this dominant exploitation campaign is conspicuously absent from widely disseminated Indicators of Compromise (IoCs). This presents a significant challenge for defenders who rely predominantly on public threat intelligence feeds for blocking known malicious entities. Organizations whose defensive strategies are limited to filtering published IoCs are at a distinct disadvantage, likely overlooking the most active and potent source of these attacks. This highlights the imperative for organizations to adopt more proactive and behavior-based detection methodologies, moving beyond reactive signature matching to identify anomalous network traffic and system behaviors that might indicate compromise.
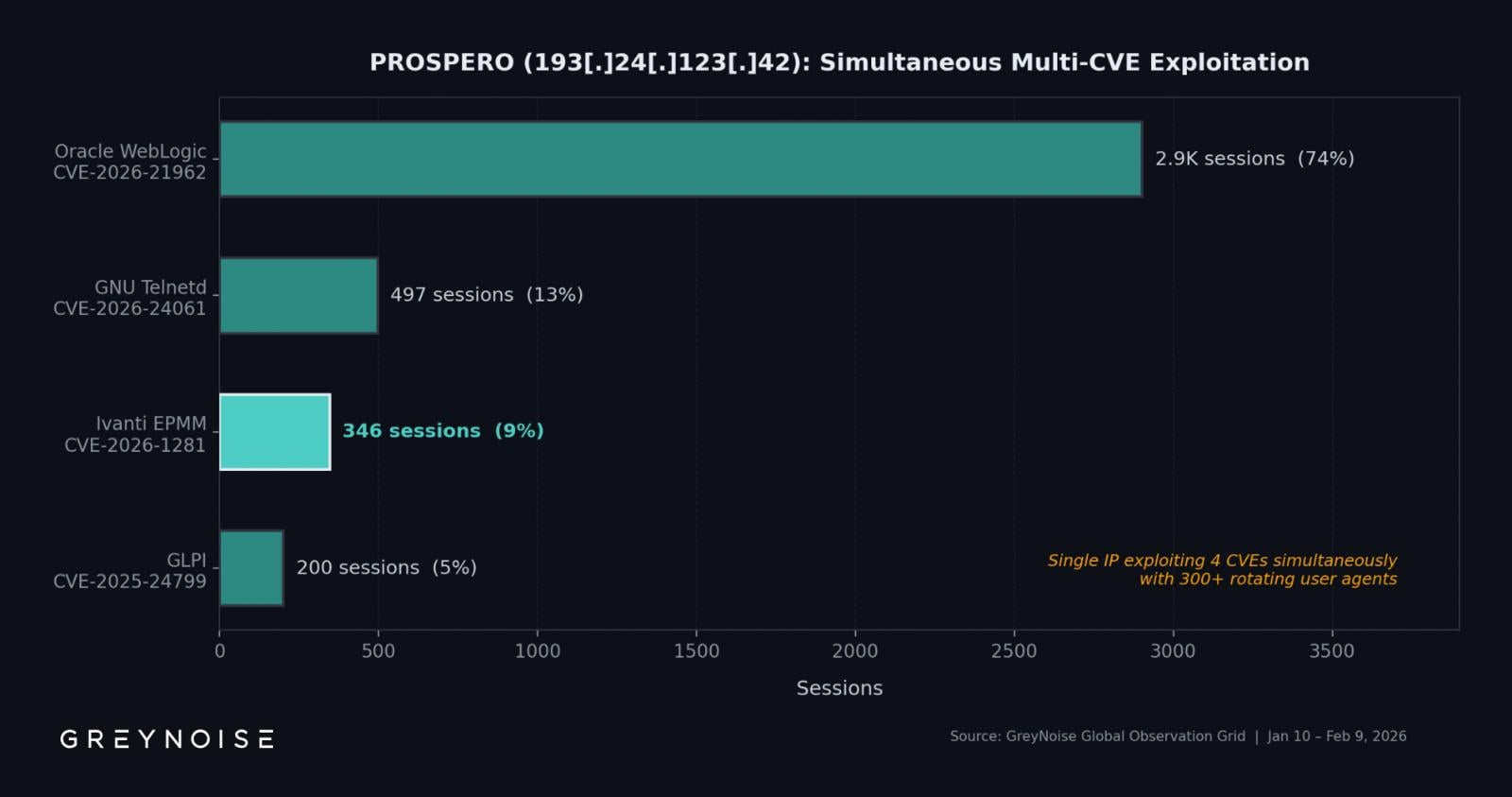
The operational scope of this threat actor extends far beyond just Ivanti systems. Intelligence indicates that the same PROSPERO OOO IP address is simultaneously engaged in the exploitation of three additional critical vulnerabilities across different enterprise software products. These include another instance of CVE-2026-21962 (this time targeting Oracle WebLogic), CVE-2026-24061 (exploiting GNU Inetutils Telnetd), and CVE-2025-24799 (impacting GLPI, an IT asset management software). This multi-faceted targeting strategy underscores the actor’s breadth of capabilities and ambition, suggesting a sophisticated entity with diverse objectives or an intent to maximize potential entry points into a wide array of enterprise environments.
Among the various targets, the Oracle WebLogic flaw garnered the highest volume of exploitation sessions, dwarfing the activity directed at other vulnerabilities with an astounding 2,902 recorded sessions. The GNU Inetutils Telnetd issue followed with 497 sessions. The disproportionate focus on Oracle WebLogic, a widely deployed enterprise application server, suggests that this actor may be prioritizing access to high-value targets often residing deeper within corporate networks, which could yield greater strategic advantage or financial gain if sold to other cybercriminal groups. This diversified attack vector indicates a strategic approach to maximize the attack surface and potential for compromise across different software stacks.
The exploitation activity itself appears to be fully automated, a characteristic that enables the actor to conduct high-volume, wide-area scanning and attack operations efficiently. Further supporting this automation is the observation that the actor rotates through approximately three hundred different user agents. This tactic is often employed to evade detection by security systems that might flag repetitive requests from a single user agent, mimicking legitimate user behavior and distributing the attack footprint to avoid triggering rate-limiting or behavioral anomaly alerts.
Regarding Ivanti’s response, it is important to note that the initial fixes provided for two related Ivanti vulnerabilities, CVE-2026-1281 and CVE-2026-1340, were described as interim measures. Ivanti has publicly committed to releasing comprehensive, permanent patches with the upcoming launch of EPMM version 12.8.0.0, anticipated within the first quarter of the current year. Until these complete patches become available, organizations are strongly advised to implement the recommended RPM packages: specifically, 12.x.0.x for EPMM versions 12.5.0.x, 12.6.0.x, and 12.7.0.x, and RPM 12.x.1.x for EPMM versions 12.5.1.0 and 12.6.1.0.
For organizations facing significant concerns or grappling with complex environments, the most conservative and secure approach recommended by the vendor is to construct an entirely new EPMM instance and migrate all existing data to this fresh installation. This recommendation underscores the potential severity and persistent risk associated with the current vulnerabilities, suggesting that a clean slate may be the most reliable path to ensuring long-term security. Detailed instructions for executing such a rebuild and migration are readily available through Ivanti’s support channels.
The concentrated nature of this exploitation campaign by a single, highly capable threat actor operating from "bulletproof" infrastructure presents significant implications for enterprise cybersecurity. The use of IAB tactics, coupled with a multi-platform targeting strategy, suggests a sophisticated and potentially state-sponsored or well-organized criminal entity aiming to establish a broad base of compromised systems for future monetization or strategic objectives. The ability of this actor to operate largely undetected by widely published IoCs necessitates a fundamental shift in defensive strategies, moving towards more advanced threat intelligence integration, behavioral analytics, and a proactive posture.
Organizations must prioritize robust vulnerability management programs, ensuring the rapid deployment of patches and hotfixes. Beyond technical controls, a comprehensive understanding of the threat landscape, including the capabilities and methodologies of prevalent threat actors, is paramount. Network segmentation, robust monitoring solutions like Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR), and the implementation of Zero Trust architectures are no longer aspirational but essential components of a resilient defense strategy. The ongoing cat-and-mouse game between attackers and defenders continues to evolve, with the current Ivanti situation serving as a stark reminder of the persistent and adaptive nature of cyber threats. Proactive measures, combined with deep intelligence analysis, will be key to safeguarding critical digital assets against such pervasive and focused campaigns.






