
A clandestine state-backed cyber apparatus has unleashed an expansive espionage campaign, codenamed ‘Shadow Campaigns,’ successfully compromising governmental and vital infrastructure networks in dozens of nations while conducting widespread reconnaissance across an astonishing 155 countries. This sophisticated operation, exhibiting high levels of operational security and advanced tooling, signals a profound and persistent threat to global stability and national sovereignty, forcing an urgent re-evaluation of cybersecurity defenses worldwide.
Over the span of just two months, between November and December of the preceding year, this highly organized threat group demonstrated an alarming capability to infiltrate sensitive targets. While actively engaging in reconnaissance activities against government entities spanning an unprecedented 155 nations, the actor simultaneously achieved confirmed compromises in at least 70 governmental and critical infrastructure organizations situated in 37 distinct countries. Forensic analysis by leading cybersecurity experts indicates that this formidable group has been operational since at least January 2024, with a strong assessment pointing to its origins within Asia. Until a definitive and public attribution can be made, the actor is provisionally identified by the tracking nomenclature TGR-STA-1030/UNC6619.
The strategic focus of the ‘Shadow Campaigns’ is demonstrably broad yet acutely targeted, concentrating primarily on institutions pivotal to national governance and economic stability. Victims include government ministries, law enforcement agencies, border control authorities, financial institutions, trade organizations, energy providers, mining operations, immigration services, and diplomatic missions. This diverse portfolio of targets underscores a comprehensive intelligence-gathering objective, seeking to acquire strategic, economic, and political insights across a vast geopolitical spectrum.
The sheer scale of the confirmed breaches is staggering, encompassing vital entities across multiple continents. In the Americas, organizations involved in trade policy, complex geopolitical issues, and electoral processes have been compromised. Across Europe, numerous ministries and parliamentary bodies have fallen victim. The Australian Treasury Department faced direct intrusion attempts, and critical government infrastructure in Taiwan experienced successful penetration. These specific instances highlight the actor’s calculated approach to target nations and institutions at the heart of international relations and economic power.

The operational timing of these cyber incursions appears to be meticulously synchronized with significant geopolitical events and national vulnerabilities. During the U.S. government shutdown in October 2025, for example, the threat actor significantly intensified its scanning activities against entities across North, Central, and South America. Countries such as Brazil, Canada, the Dominican Republic, Guatemala, Honduras, Jamaica, Mexico, Panama, and Trinidad and Tobago were subjected to heightened scrutiny. This opportunistic behavior suggests a strategic exploitation of perceived distractions or reduced vigilance during periods of internal governmental instability.
A particularly telling example of this geopolitical alignment was the extensive reconnaissance conducted against infrastructure associated with the Government of Honduras. More than 200 IP addresses were scanned just 30 days prior to a national election, an election in which both leading candidates had expressed an openness to re-establishing diplomatic ties with Taiwan. Such a targeted pre-election operation strongly implies an intelligence agenda focused on influencing or pre-empting shifts in international diplomacy and trade relations. Beyond successful compromises, the actor also made documented attempts to connect via SSH to critical infrastructure, including Australia’s Treasury Department, Afghanistan’s Ministry of Finance, and Nepal’s Office of the Prime Minister and Council of Ministers, demonstrating a persistent and varied approach to initial access.
Further evidence of the campaign’s ambitious scope includes extensive reconnaissance and breach attempts against European entities. Infrastructure connected to the Czech government, encompassing its Army, Police, Parliament, Ministries of Interior, Finance, Foreign Affairs, and even the president’s official website, was subjected to intense scanning. The group also directed its efforts towards the broader European Union infrastructure, targeting over 600 IP addresses hosting *.europa.eu domains. In July 2025, Germany became a primary focus, with the group initiating connections to more than 490 IP addresses associated with government systems, underscoring a continuous and dynamic adaptation of targets based on regional significance and unfolding events.
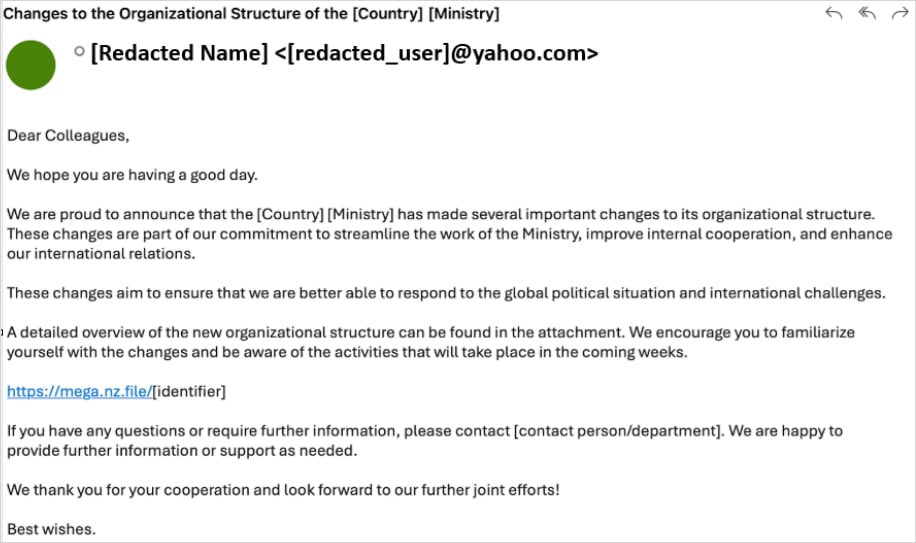
The ‘Shadow Campaigns’ employ a multi-faceted and highly sophisticated attack chain, beginning with initial access through both social engineering and vulnerability exploitation. Early operations relied heavily on meticulously crafted phishing emails, tailored with compelling lures such as references to internal ministry reorganization efforts. These emails contained embedded links directing targets to malicious archives, often hosted on legitimate cloud storage services like Mega.nz. The compressed files typically included a custom malware loader, dubbed Diaoyu, alongside an innocuous-looking, zero-byte PNG file named pic1.png.

The Diaoyu loader is a testament to the actor’s advanced evasion techniques. Upon execution, it performs a series of environmental checks designed to thwart analysis and detection. It specifically looks for a horizontal screen resolution greater than or equal to 1440 pixels, a hardware requirement that can often differ in virtualized analysis environments. Crucially, the presence of the pic1.png file in its execution directory serves as a file-based integrity check; without it, the malware terminates, preventing its full payload from being exposed to security researchers. Furthermore, Diaoyu actively scans for the presence of commonly used security products, including Kaspersky, Avira, Bitdefender, Sentinel One, and Norton (Symantec), terminating its execution if any are detected. Only after successfully bypassing these checks does the loader proceed to fetch and deploy advanced payloads such as Cobalt Strike, a popular post-exploitation framework, and the VShell framework for command-and-control (C2) communications, allowing the attackers to establish persistent access and control over compromised systems.
Beyond these sophisticated phishing tactics, TGR-STA-1030/UNC6619 also leverages known vulnerabilities to gain initial footholds. Investigations revealed the exploitation of at least 15 identified security flaws across various widely used platforms, including SAP Solution Manager, Microsoft Exchange Server, D-Link networking equipment, and Microsoft Windows. This dual approach—combining highly personalized social engineering with opportunistic exploitation of unpatched systems—demonstrates the actor’s versatility and resourcefulness in gaining access to a wide array of targets.
The toolkit deployed within the ‘Shadow Campaigns’ is extensive, comprising a mix of commercially available and custom-developed malicious software. Standard webshells like Behinder, Godzilla, and Neo-reGeorg are utilized for remote access and persistence, while network tunneling tools such as GO Simple Tunnel (GOST), Fast Reverse Proxy Server (FRPS), and IOX facilitate covert communication and lateral movement within compromised networks. However, the discovery of a bespoke Linux kernel eBPF rootkit, uniquely named ‘ShadowGuard,’ represents a significant leap in the actor’s capabilities and underscores their advanced development resources.
ShadowGuard is a particularly insidious piece of malware, operating within the highly privileged kernel space of Linux systems using the Extended Berkeley Packet Filter (eBPF) framework. eBPF is a powerful, legitimate Linux technology that allows programs to run in the kernel without modifying kernel source code, enabling high-performance networking and tracing. However, in the hands of malicious actors, eBPF can be weaponized to create extremely stealthy backdoors that are notoriously difficult to detect. By operating at this fundamental level, ShadowGuard can manipulate core system functions and audit logs before security tools or system monitoring applications can perceive the true state of the system. This allows the rootkit to effectively blind security mechanisms to its presence and activities.

Specifically, ShadowGuard conceals malicious process information at the kernel level, capable of hiding up to 32 Process IDs (PIDs) from standard Linux monitoring tools through syscall interception. It also boasts the ability to cloak files and directories named swsecret from manual inspection, further hindering forensic analysis. Adding another layer of sophistication, the malware incorporates a mechanism that allows its operators to define specific processes that should remain visible, potentially to create a façade of normal activity or to monitor specific legitimate processes without being detected. The development and deployment of such a unique and sophisticated kernel-level rootkit signify a profound commitment to long-term, high-stealth espionage operations against critical Linux-based infrastructure.
The command and control infrastructure supporting ‘Shadow Campaigns’ is designed for resilience and obfuscation. It relies on a distributed network of victim-facing servers hosted by legitimate Virtual Private Server (VPS) providers in strategic locations such as the U.S., Singapore, and the UK. These are complemented by relay servers used for traffic obfuscation and further anonymized through the use of residential proxies or the Tor network. This multi-layered approach makes it exceedingly difficult to trace the ultimate origin of the attacks and disrupt the C2 channels.
Intriguingly, the actor demonstrates an understanding of cultural and linguistic nuances in their C2 domain selection. Examples include the use of the .gouv top-level extension for French-speaking target countries, designed to mimic legitimate government domains. Another notable example is the dog3rj[.]tech domain observed in attacks within the European space. Researchers speculate this domain could be a reference to ‘DOGE Jr,’ which carries multiple meanings in a Western context, potentially alluding to the U.S. Department of Government Efficiency, or even the popular cryptocurrency ‘Dogecoin Jr.’ Such subtle choices indicate a meticulous effort to blend in and reduce suspicion among targeted populations.
The cumulative evidence paints a clear picture of TGR-STA-1030/UNC6619 as an operationally mature and exceptionally well-resourced state-sponsored espionage actor. Their capacity to conduct global-scale reconnaissance, execute precision compromises against high-value targets, and develop custom, cutting-edge malware like ShadowGuard, places them among the most formidable threats in the contemporary cyber landscape. The prioritization of strategic, economic, and political intelligence aligns with the objectives typically associated with nation-state actors seeking to gain a competitive advantage on the international stage.
The implications of the ‘Shadow Campaigns’ are profound. This widespread and persistent cyber espionage underscores the ongoing global struggle for strategic advantage in the digital realm. Governments and critical infrastructure providers worldwide face an existential challenge in defending against such advanced threats. The blend of sophisticated social engineering, rapid exploitation of known vulnerabilities, and innovative custom malware like eBPF rootkits demands an evolution in defensive strategies. Defenders must move beyond signature-based detection, implement robust patching regimes, invest in advanced threat intelligence, and develop capabilities for deep kernel-level monitoring, particularly for Linux environments. The pervasive nature of these operations also highlights the urgent need for enhanced international cooperation and intelligence sharing to collectively counter these state-sponsored threats that transcend national borders. The ‘Shadow Campaigns’ serve as a stark reminder that the battle for digital sovereignty is continuous, complex, and ever-escalating.






