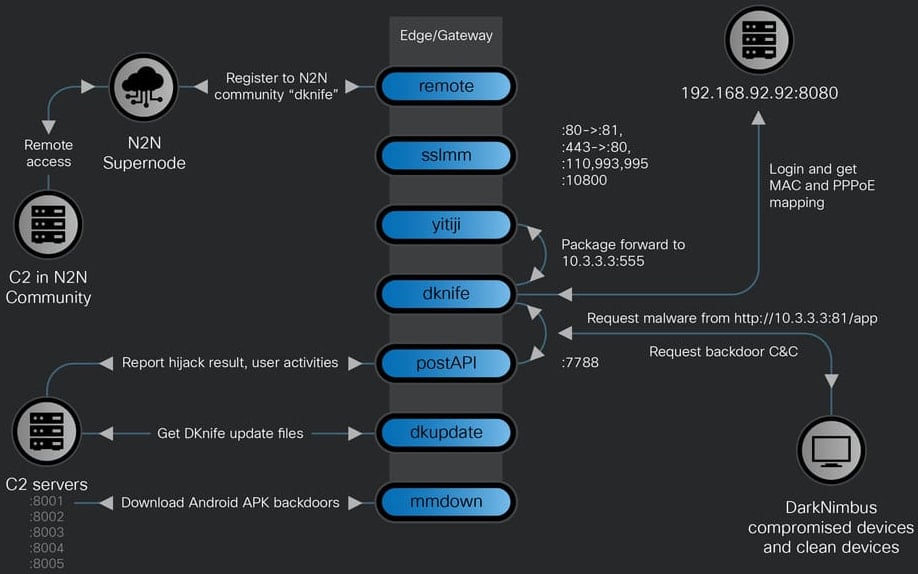
A sophisticated Linux-based framework, dubbed DKnife, has been actively employed since 2019 to clandestinely infiltrate and commandeer network edge devices, orchestrating comprehensive traffic manipulation for espionage and malware dissemination. This formidable toolkit functions as a post-compromise platform, enabling persistent traffic monitoring and advanced Adversary-in-the-Middle (AitM) operations, specifically engineered to intercept and re-route data flows intended for various endpoints within a compromised network. Its strategic placement at critical network junctions allows for unparalleled visibility and control over user communications, rendering it a potent instrument for targeted intelligence gathering and covert payload delivery.
The operational methodology of DKnife demonstrates a high degree of technical sophistication, leveraging an ELF (Executable and Linkable Format) framework composed of seven distinct Linux-based modules. These components are meticulously designed to execute a range of illicit activities, including deep packet inspection (DPI), granular traffic manipulation, harvesting of sensitive credentials, and the surreptitious deployment of malicious software. The toolkit’s pervasive capabilities are further underscored by linguistic artifacts found within its component names and code comments, which are predominantly in Simplified Chinese. This, coupled with its explicit targeting of various Chinese digital services—such as popular email providers, mobile applications, media domains, and the widely used WeChat platform—has led cybersecurity researchers to attribute DKnife’s development and deployment with high confidence to a China-nexus threat actor.
The selection of edge devices, such as routers and gateway appliances, as primary targets highlights a strategic shift in advanced persistent threat (APT) operations. These devices represent a critical choke point for all network traffic, making them ideal platforms for AitM attacks. By compromising these foundational elements, DKnife operators gain a panoramic view of network activity and the ability to modify data in transit without directly engaging with individual endpoints. This approach circumvents many traditional endpoint security measures, presenting a significant challenge for detection and remediation. While the precise initial access vector for DKnife remains unconfirmed by researchers, common methods for compromising network equipment often include the exploitation of known vulnerabilities in device firmware, leveraging default or weak administrative credentials, supply chain compromises, or sophisticated social engineering tactics targeting network administrators. The toolkit’s ability to establish a persistent presence on these devices ensures long-term access and control over the targeted network’s data flow.

At its core, DKnife facilitates an extensive range of malicious functionalities through its modular architecture. One of its pivotal components, identified as yitiji.bin, is responsible for creating a bridged TAP interface—a virtual network device—on the compromised router. This interface is typically configured with a private IP address, such as 10.3.3.3, which enables the threat actor to seamlessly intercept, analyze, and rewrite network packets as they traverse the device en route to their legitimate destinations. This fundamental capability underpins DKnife’s capacity for various AitM attacks, allowing it to inject malicious content, redirect traffic, or alter data payloads with precision and stealth. The implication of such an interface is profound: it allows the attackers to essentially become an invisible proxy for all network communications, exercising complete control over the information exchanged between internal users and external services.
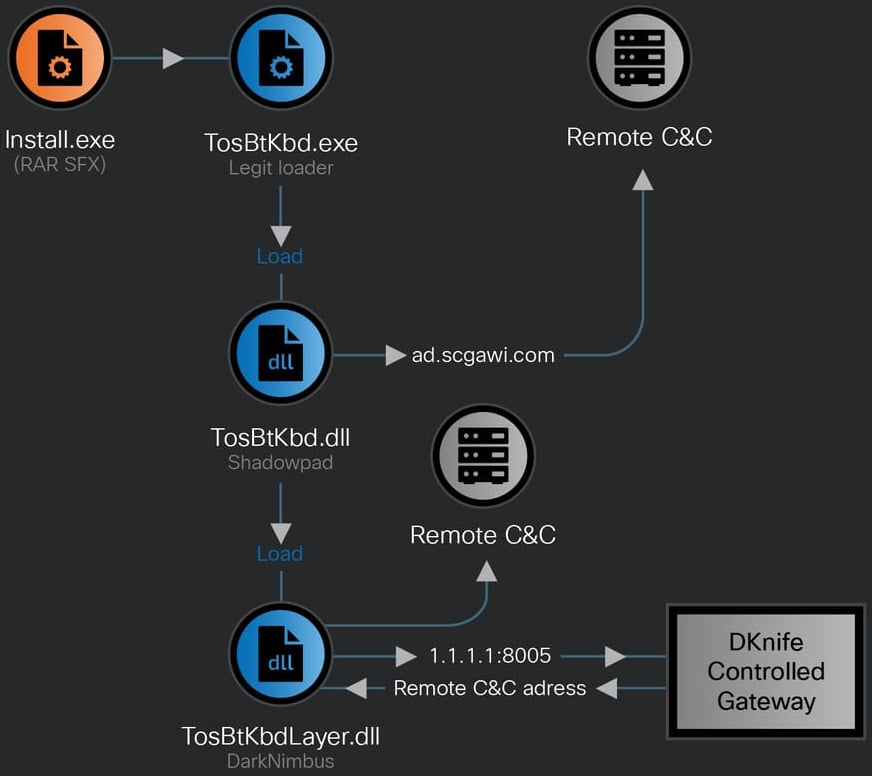
The primary objective of DKnife extends beyond mere traffic observation; it serves as a robust delivery mechanism for other sophisticated malware. Investigations into DKnife’s operational infrastructure have revealed its intimate connection with the deployment of several notorious backdoors, including ShadowPad and DarkNimbus. ShadowPad, a highly modular backdoor, has a well-documented history of use by various state-sponsored Chinese APT groups, often employed for espionage and intellectual property theft. DKnife has been observed delivering ShadowPad to Windows systems, with the malicious payload sometimes signed with a certificate associated with a Chinese firm, adding another layer of operational sophistication and potential obfuscation. Following the deployment of ShadowPad, the DarkNimbus backdoor is often subsequently deployed, indicating a multi-stage infection process designed for layered persistence and capability. For Android mobile devices within the compromised network, DKnife directly delivers its designated backdoor, often in the form of malicious Android Package (APK) files, exploiting the device’s connection to the compromised router. Furthermore, the same infrastructure utilized by DKnife has also been found hosting the WizardNet backdoor, which has previously been associated with the Spellbinder AitM framework, reinforcing the pattern of advanced network-level interception tools linked to specific threat actors.
DKnife’s comprehensive capabilities are tailored for deep reconnaissance and active manipulation. These include:
- Traffic Interception and Rewriting: The foundational ability to capture and alter data packets in real-time, forming the basis of all AitM operations.
- Malware Delivery: The targeted distribution of specific backdoors like ShadowPad, DarkNimbus, and malicious APKs to Windows and Android devices respectively.
- DNS Hijacking: The manipulation of DNS queries to redirect users to attacker-controlled servers or malicious websites, facilitating phishing, credential harvesting, or further malware delivery.
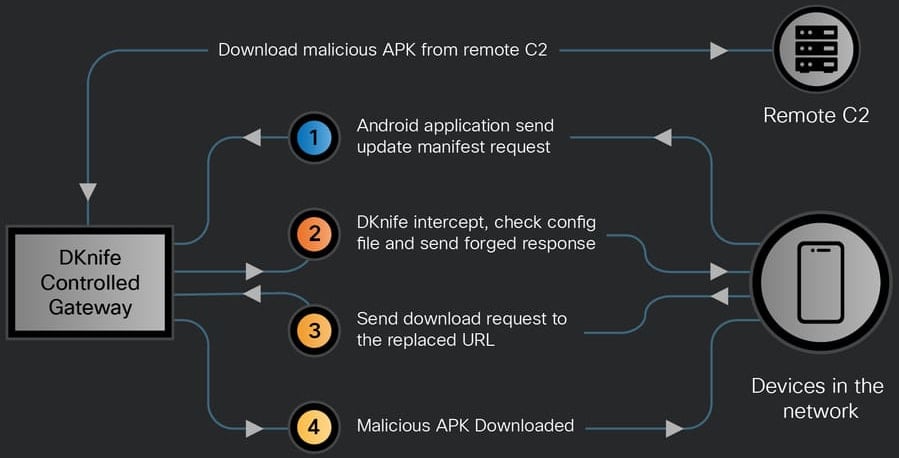
- Hijacking Android Application Updates and Binary Downloads: A particularly insidious capability that allows DKnife to intercept legitimate requests for software updates or binary files and substitute them with malicious versions, ensuring a wide distribution vector for malware.
- Exfiltration of User Activity Data: The systematic collection and transmission of sensitive user data, browsing habits, and communication metadata to remote command-and-control (C2) servers.
- Targeting of Specific Chinese Services: A deliberate focus on platforms like WeChat, indicating an interest in specific demographics or intelligence targets.
- Disruption of Security Product Traffic: A sophisticated evasion technique where DKnife selectively interferes with traffic related to security products, potentially preventing updates, disabling telemetry, or hindering detection mechanisms.
The toolkit’s granular monitoring extends to highly personal communication platforms. Cisco Talos researchers have detailed DKnife’s analytical tracking of WeChat activities, observing and collecting data on voice and video calls, text messages, images sent and received, and even articles read within the application. This level of surveillance underscores the espionage-oriented nature of DKnife, aiming to gather comprehensive intelligence on targeted individuals or groups. All observed user activity events are first routed internally between DKnife’s various components for processing and then systematically exfiltrated via HTTP POST requests to pre-configured command-and-control (C2) API endpoints. This real-time reporting mechanism, facilitated by DKnife’s strategic placement on gateway devices, ensures that operators receive immediate updates on user behavior and collected data.
The attribution of DKnife to a China-nexus threat actor carries significant implications for geopolitical cybersecurity. Such actors are typically associated with state-sponsored entities or groups aligned with national interests, often engaging in intelligence gathering, economic espionage, or cyber warfare activities. The sophistication, persistence, and specific targeting observed with DKnife align with the characteristics commonly associated with these types of advanced persistent threats. The toolkit’s ability to operate undetected for an extended period since 2019, coupled with its active C2 servers as of early 2026, signals a long-term, well-resourced campaign. The strategic value of compromising edge devices for these actors lies in their ability to act as silent, pervasive eavesdroppers and manipulators, affecting a broad spectrum of users and systems simultaneously without requiring individual endpoint compromises. This approach presents a formidable challenge to conventional cybersecurity defenses, which often focus on endpoint protection.
The emergence and sustained operation of toolkits like DKnife highlight an evolving landscape in cyber threats, where attackers are increasingly focusing on the foundational network infrastructure rather than solely on end-user devices. This shift necessitates a corresponding evolution in defensive strategies. Organizations and individuals must prioritize robust security measures for all network equipment, including routers, firewalls, and other gateway devices. This includes ensuring that firmware is regularly updated, default credentials are changed to strong, unique passwords, and unnecessary services are disabled. Network segmentation can limit the lateral movement of threats even if an edge device is compromised. Furthermore, vigilant monitoring of outbound network traffic for anomalous patterns, such as unexpected connections to unknown IP addresses or unusual data exfiltration volumes, becomes critical. The adoption of advanced threat intelligence platforms and network-level detection systems capable of identifying deep packet inspection and AitM indicators is paramount. For individuals, using Virtual Private Networks (VPNs) can encrypt traffic from the endpoint to a trusted server, potentially mitigating some forms of AitM attacks orchestrated by a compromised local router.
The DKnife toolkit represents a sophisticated and persistent threat, demonstrating the capabilities of state-sponsored or highly organized cyber actors to conduct extensive espionage and deliver malware through the manipulation of critical network infrastructure. Its continued activity underscores the ongoing need for enhanced vigilance, proactive security measures, and a comprehensive understanding of the evolving attack surface. As cyber adversaries continue to innovate, the focus on securing the "edge" of the network will only intensify, demanding greater investment in network security architecture, threat intelligence, and incident response capabilities to counteract these advanced and insidious threats.






