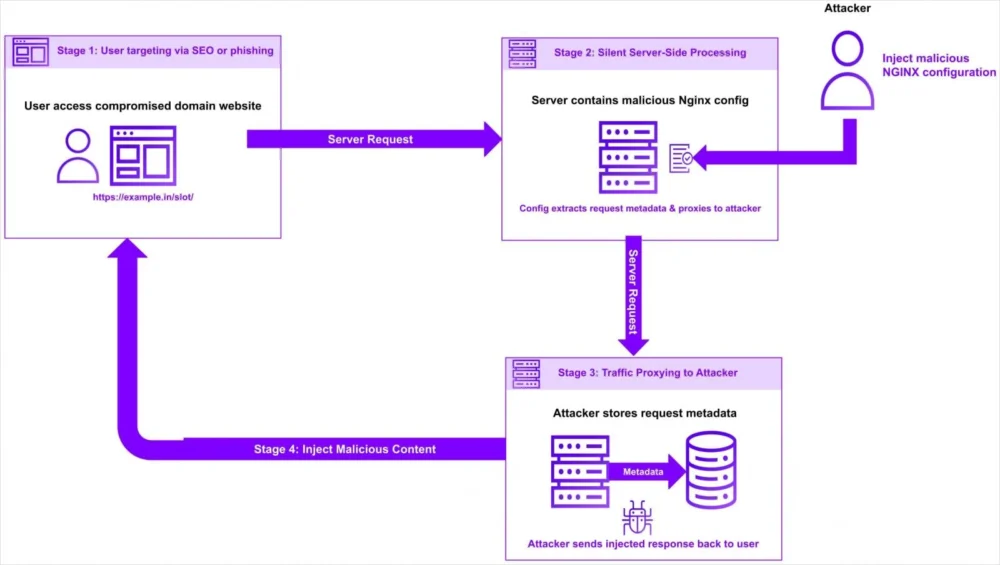
A sophisticated and stealthy campaign has emerged, exploiting NGINX web servers by surreptitiously modifying their configuration files to divert user traffic through attacker-controlled infrastructure. This illicit redirection poses significant risks, enabling potential data interception, content manipulation, and further malicious activities without immediately alerting either the user or the compromised organization.
NGINX, an indispensable piece of open-source software, serves as a cornerstone of modern web infrastructure. Its robust architecture and efficiency make it a preferred choice for managing web traffic, acting as a high-performance web server, a reverse proxy, a load balancer, and an HTTP cache. In its capacity as a reverse proxy, NGINX intermediates connections between client requests and backend servers, handling tasks such as SSL termination, request routing, and content compression. This critical intermediary role positions NGINX as a highly attractive target for malicious actors seeking to intercept or manipulate the flow of information on a large scale. By controlling the NGINX configuration, attackers can effectively commandeer the very pathways through which legitimate user interactions traverse, gaining an advantageous vantage point over data streams.
The current malicious operation, meticulously analyzed by cybersecurity researchers, specifically targets NGINX installations and, notably, Baota hosting management panels. Baota, a widely adopted server management panel, particularly prevalent in certain regions, provides a graphical interface for managing web servers, databases, and other services. Its compromise can grant attackers broad control over the underlying NGINX configurations and potentially other critical system components. Geographically, the campaign exhibits a discernible focus on sites associated with specific top-level domains (TLDs) such as .in (India), .id (Indonesia), .pe (Peru), .bd (Bangladesh), and .th (Thailand). Furthermore, a concerning aspect of this targeting is its extension to governmental (.gov) and educational (.edu) institutions, indicating a potential interest in sensitive data, intellectual property, or strategic disruption. The successful compromise of such entities could have far-reaching implications, from national security risks to the erosion of public trust in digital services.
The operational methodology of this campaign demonstrates a nuanced understanding of NGINX’s flexible configuration system. Attackers do not rely on exploiting a software vulnerability within NGINX itself, which would typically trigger immediate security alerts and patch cycles. Instead, they gain unauthorized access to the server environment and then proceed to inject malicious location blocks into existing NGINX configuration files. These location blocks are directives that specify how NGINX should handle requests for particular URL paths. By carefully crafting these blocks, the attackers instruct NGINX to capture incoming requests for specific paths that they have selected.

Upon capturing a request, the malicious configuration then rewrites the Uniform Resource Locator (URL) to include the full original URL, a critical step for maintaining the appearance of legitimacy. Following this, the proxy_pass directive is leveraged to forward the traffic to attacker-controlled domains. The proxy_pass directive is a standard and legitimate NGINX function primarily used for load balancing or directing traffic to different backend servers within a legitimate architecture. Its normal application involves distributing requests across multiple servers to enhance performance, reliability, and availability. The very legitimacy and common use of proxy_pass is precisely what makes its abuse so effective; its invocation does not inherently trigger typical security alerts, as it performs an expected NGINX operation.
To further ensure the covert nature of the traffic redirection, the attackers meticulously preserve essential HTTP request headers. Headers such as Host, X-Real-IP, User-Agent, and Referer are maintained in their original form. The Host header specifies the domain name of the server the client is trying to reach, while X-Real-IP often carries the original client IP address, especially when NGINX is acting as a proxy. User-Agent identifies the client’s browser and operating system, and Referer indicates the URL of the previous web page from which the current request was linked. By preserving these headers, the redirected traffic appears indistinguishable from legitimate requests to both the compromised server’s logs and potentially to any backend systems that might be inspecting traffic. This high degree of camouflage significantly complicates detection efforts, allowing the malicious activity to persist unnoticed for extended periods.
The entire compromise and configuration injection process is facilitated by a sophisticated, scripted multi-stage toolkit. While the exact stages were not fully detailed, such toolkits typically involve several key phases: initial reconnaissance to identify vulnerable targets and potential entry points; gaining initial access, often through compromised credentials, exploitation of vulnerabilities in management panels like Baota, or other server-side weaknesses; privilege escalation to obtain the necessary permissions to modify critical system files; payload delivery and execution, which in this case involves injecting the malicious NGINX configuration; establishing persistence to ensure continued access even after reboots or security remediations; and finally, the traffic redirection itself, coupled with potential data exfiltration or further malicious actions. The automation inherent in a multi-stage toolkit enables the threat actor to scale their operations and efficiently target a broader range of victims.
One of the primary reasons these attacks are exceedingly difficult to detect lies in their fundamental nature. They do not exploit a vulnerability within the NGINX software itself, which would typically be flagged by vulnerability scanners or intrusion detection systems looking for known exploits. Instead, the malicious instructions are cleverly embedded within NGINX’s legitimate configuration files. These configuration files, while critical, are rarely subjected to the same level of rigorous, continuous scrutiny as executable code or network traffic by automated security tools. Furthermore, a crucial element contributing to their stealth is that user traffic, even after being routed through the attacker’s infrastructure, ultimately reaches its intended destination. This "pass-through" mechanism means that users experience no service interruption, making them unlikely to notice any anomaly. The absence of error messages, timeouts, or unexpected content renders the attack largely transparent from an end-user perspective, further diminishing the chances of detection unless specific, advanced monitoring techniques are actively deployed.

The significance of compromising NGINX servers cannot be overstated. As a central gateway for web traffic, NGINX acts as a critical choke point. Its compromise allows attackers to perform various malicious actions, including but not limited to: intercepting sensitive data such as login credentials, personal identifiable information (PII), and financial details; injecting malicious code or advertisements into legitimate web pages; redirecting users to phishing sites or malware download pages; and potentially leveraging the compromised server as a pivot point for further attacks deeper into an organization’s network. The ability to manipulate traffic at such a fundamental level provides attackers with immense power over the integrity and confidentiality of online communications.
This campaign highlights a broader trend in the cybersecurity landscape: a shift from solely exploiting application vulnerabilities to targeting misconfigurations, weak access controls, and the underlying infrastructure management. Initial access to the target servers or Baota panels could stem from various vectors, including brute-force attacks against weak administrator credentials, exploitation of known vulnerabilities in the Baota panel or the operating system, phishing campaigns leading to credential theft, or even supply chain compromises involving legitimate software components. The sophistication lies not in a zero-day exploit, but in the operational security and stealth required to maintain persistence and execute the redirection without raising alarms.
The implications for organizations relying on NGINX are profound. A compromise can lead to severe data breaches, significant reputational damage, financial losses due and regulatory fines, and a potential loss of trust from users and partners. For users, the risk includes identity theft, financial fraud, and malware infections. The targeting of government and educational institutions further amplifies the potential impact, raising concerns about espionage, intellectual property theft, and critical infrastructure disruption.
Defending against such insidious attacks requires a multi-layered and proactive security strategy. Organizations must prioritize robust configuration management, implementing strict version control for NGINX configuration files and regularly auditing them for unauthorized changes. Automated configuration integrity checks, perhaps using tools that compare current configurations against known good baselines, are essential. Strong access controls are paramount: restricting administrative access to NGINX servers and Baota panels to only authorized personnel, enforcing multi-factor authentication (MFA), and regularly rotating credentials.
.jpg)
Enhanced monitoring and logging are critical for early detection. This includes comprehensive logging of NGINX access and error logs, as well as system-level logs for any unusual process activity or file modifications. Anomaly detection systems, capable of identifying deviations in traffic patterns, unusual proxy_pass directives, or unexpected outbound connections from NGINX servers, can be invaluable. Endpoint Detection and Response (EDR) solutions on the servers hosting NGINX can help detect initial compromise attempts and subsequent malicious activity. Furthermore, network segmentation can limit the blast radius of a successful compromise, preventing attackers from easily moving laterally within the network. Regular security awareness training for staff, particularly those with administrative privileges, can mitigate risks associated with phishing and social engineering.
Looking ahead, the evolution of such attacks will likely see increased automation and diversification of targeting. As security defenses mature, attackers will continue to seek out the weakest links, which often reside in the operational configurations and human elements rather than just code vulnerabilities. The industry must respond by developing more sophisticated tools for configuration security posture management (CSPM) that specifically monitor and protect critical infrastructure configurations. Open-source software like NGINX, while offering immense benefits, also presents a broad attack surface due to its widespread adoption. This necessitates a collective effort from the security community, developers, and users to foster a culture of proactive security, continuous vigilance, and rapid incident response to safeguard the digital ecosystem. The ability to covertly redirect traffic at the NGINX layer underscores the ongoing arms race between defenders and attackers, demanding perpetual innovation in security strategies.






