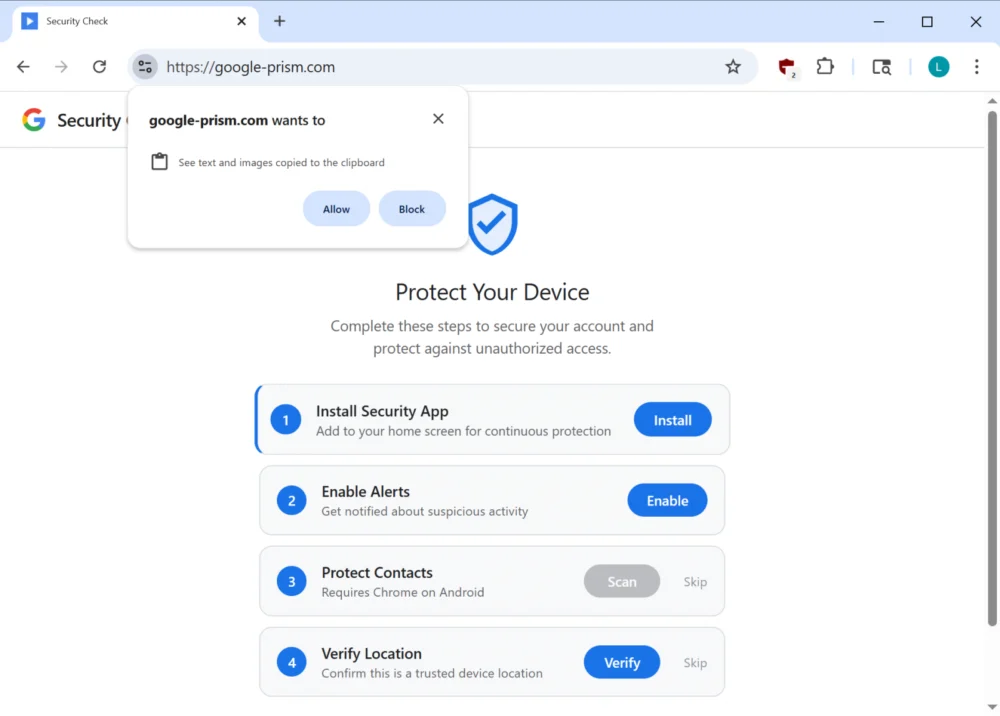
Sophisticated Phishing Campaign Leverages Progressive Web Apps and Android Malware for Multi-Vector Credential and Data Exfiltration
A highly deceptive cyber-attack is actively exploiting the capabilities of Progressive Web Applications (PWAs) alongside sophisticated social engineering tactics to compromise user accounts, bypass multi-factor authentication (MFA), and establish persistent…
The Dawn of Autonomous Cyber Warfare: CyberStrikeAI Unleashes a New Era of AI-Powered Attacks
A paradigm shift in cyber offensive capabilities is underway, marked by the emergence and operational deployment of CyberStrikeAI, an advanced open-source artificial intelligence-native security testing platform. This sophisticated tool has…
Global Service Interruption Strikes Anthropic’s Claude AI Platform
Anthropic, a prominent innovator in artificial intelligence, is currently grappling with a significant worldwide service outage impacting its flagship large language model, Claude. The widespread disruption, first officially acknowledged on…
Digital Frontline: Olympique Marseille Grapples with Sophisticated Cyber Intrusion Amidst Escalating Threats to Sports Sector
A prominent French football institution, Olympique de Marseille, has formally acknowledged a recent cyberattack attempt, an incident that surfaced following claims by a malicious actor regarding unauthorized access to the…
Navigating the Digital Divide: Samsung’s Agreement with Texas Redefines Smart TV Data Practices
A significant development in consumer data privacy has unfolded as Samsung, a global electronics giant, has finalized a comprehensive settlement with the State of Texas, addressing allegations of unauthorized collection…
Critical "ClawJacked" Flaw Exposes OpenClaw AI Agents to Remote Takeover and Data Exfiltration
A recently unearthed, high-severity vulnerability, designated "ClawJacked," allowed malevolent websites to surreptitiously gain unauthorized access and control over locally deployed instances of the widely adopted OpenClaw AI agent platform, facilitating…
Unauthenticated Root Control: A Grave Exposure in Juniper PTX Routers Threatens Global Network Integrity
A severe security vulnerability has been identified within the Junos OS Evolved operating system, specifically impacting Juniper Networks’ PTX Series core and peering routers. This critical flaw could enable an…
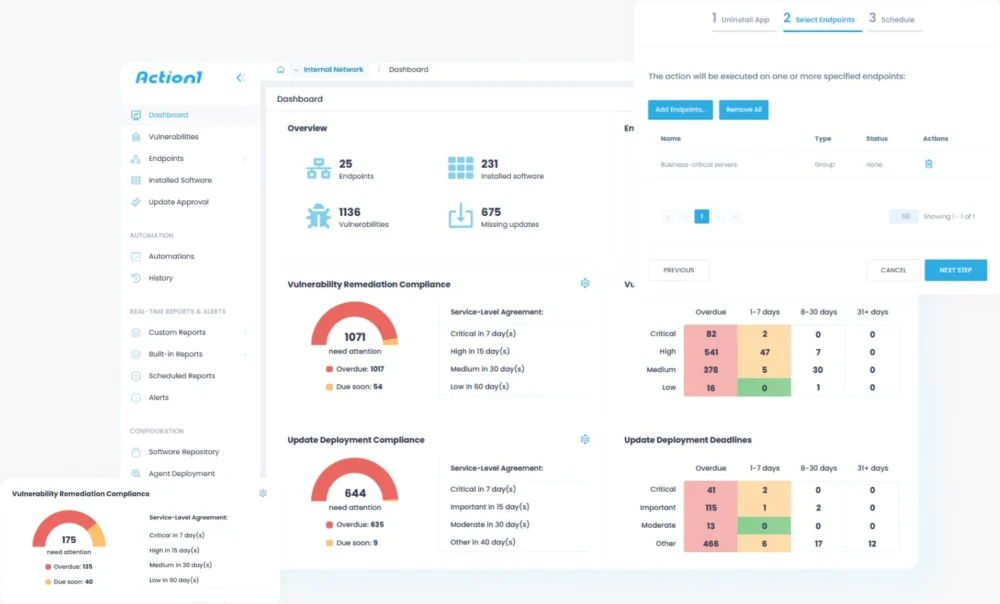
The Unseen Battleground: Securing the Pervasive Third-Party Software Footprint
Modern cybersecurity strategies frequently concentrate on the visible architectural pillars of an enterprise, yet a more insidious and equally critical vulnerability often resides within the ubiquitous, everyday applications that form…
High-Profile Security Breach: South Korean Tax Authority’s Operational Oversight Leads to $4.8 Million Cryptocurrency Heist
A significant operational security lapse by South Korea’s National Tax Service (NTS) has resulted in the theft of approximately $4.8 million in digital assets, following the inadvertent public exposure of…
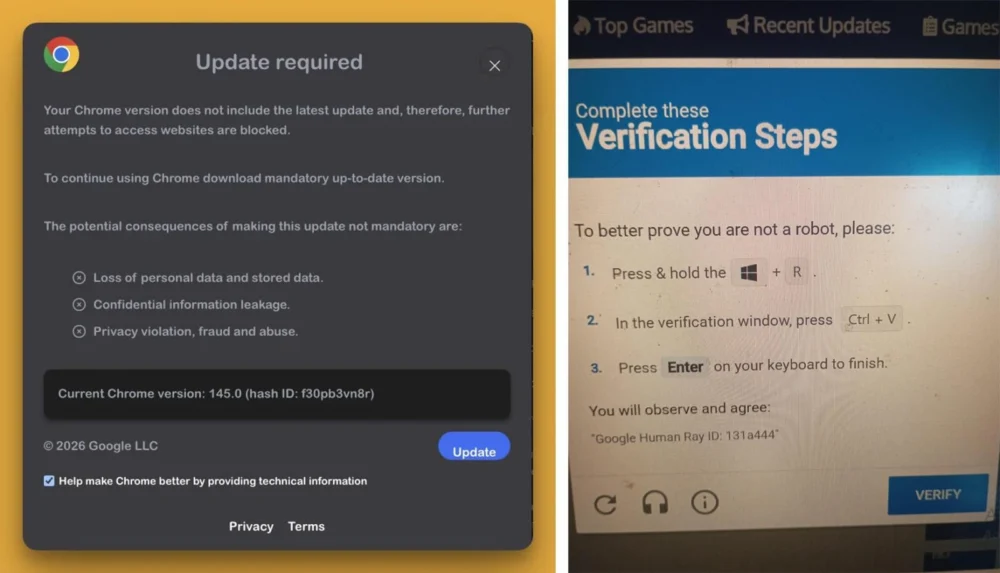
Stealthy Acquisition Transforms Popular Chrome Extension into Potent Cryptocurrency and Data Theft Platform
A widely adopted browser extension, "QuickLens – Search Screen with Google Lens," previously recognized for its utility and even featured by Google, has been irrevocably compromised, transitioning from a benign…