Google Accelerates Visual AI Frontier with New High-Efficiency Image Generation Model
Google is poised to significantly advance the accessibility and speed of artificial intelligence in image generation with the impending release of its "Nano Banana 2 Flash" model. This new iteration,…
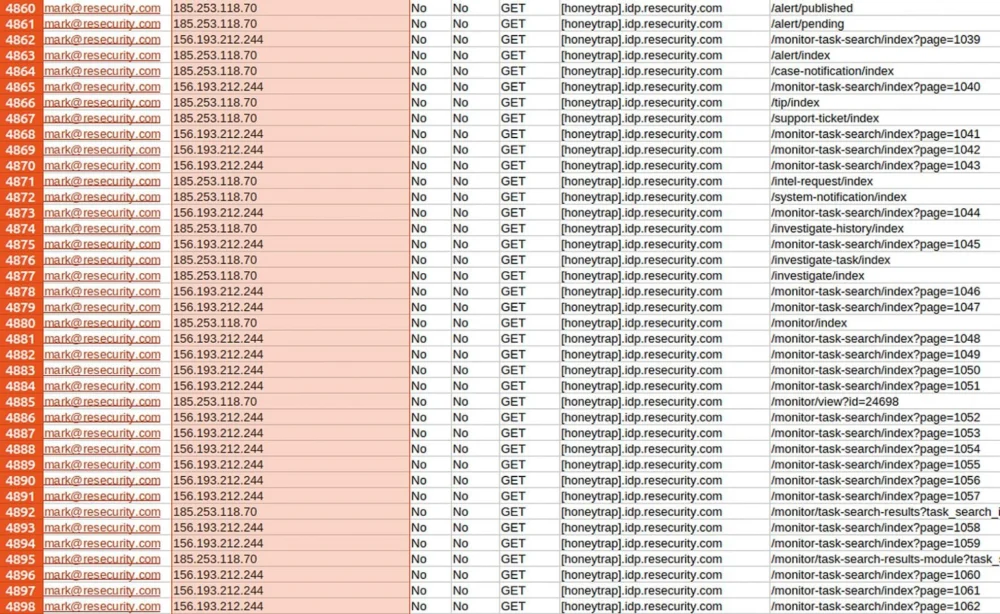
Cybersecurity Firm Resecurity Alleges Strategic Deception Amidst Hacker Breach Claims
A prominent collective of cyber threat actors, identifying themselves as "Scattered Lapsus$ Hunters," has publicly asserted a significant compromise of the cybersecurity entity Resecurity, purporting to have exfiltrated extensive internal…
Pervasive Threat: Over 10,000 Fortinet Firewalls Remain Susceptible to Long-Standing 2FA Bypass Vulnerability Amid Active Exploitation Campaigns
Thousands of network security appliances from Fortinet, specifically FortiGate firewalls, continue to operate with a critical, five-year-old two-factor authentication (2FA) bypass vulnerability, exposing organizations to persistent and actively observed exploitation…
Historic LastPass Breach Fuels Multi-Year Cryptocurrency Heist Campaign, Russian Laundering Network Implicated
A sophisticated, multi-year campaign of cryptocurrency thefts, cumulatively totaling over $35 million, has been definitively linked by blockchain forensics experts to the comprehensive data compromise suffered by the LastPass password…
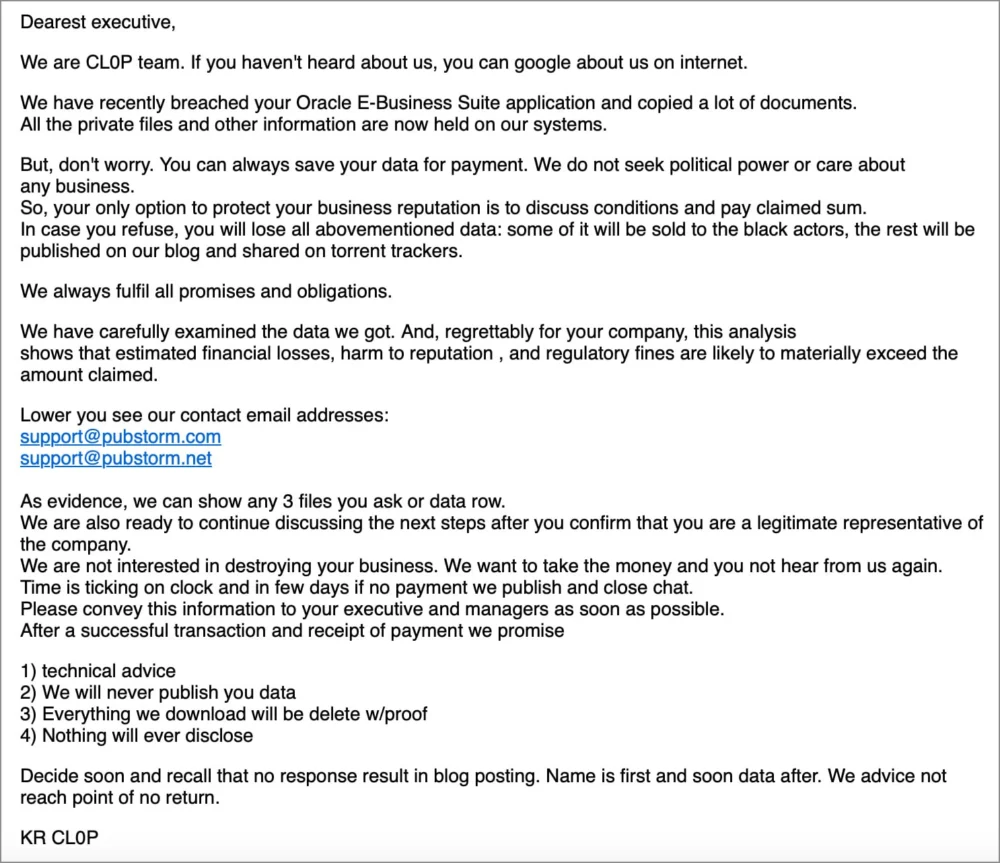
Massive Patient Data Exposure Unveiled: Covenant Health Breach Impact Far Exceeds Initial Estimates, Qilin Ransomware Implicated
A significant cybersecurity incident at Covenant Health has been revealed to have compromised the personal and medical information of nearly half a million patients, a dramatic upward revision from the…
Sophisticated Evolution: GlassWorm Malware Intensifies macOS Assault with Trojanized Crypto Wallets
A formidable and continuously evolving cyber threat, dubbed "GlassWorm," has initiated its fourth documented campaign, now specifically targeting the macOS developer community with highly insidious tactics involving trojanized cryptocurrency wallet…
The Cybersecurity Crucible of 2025: A Retrospective on Major Threats and Transformative Trends
The year 2025 marked an inflection point in the digital threat landscape, characterized by an unprecedented surge in sophisticated cyberattacks, expansive data compromises, and the alarming ascendance of new threat…
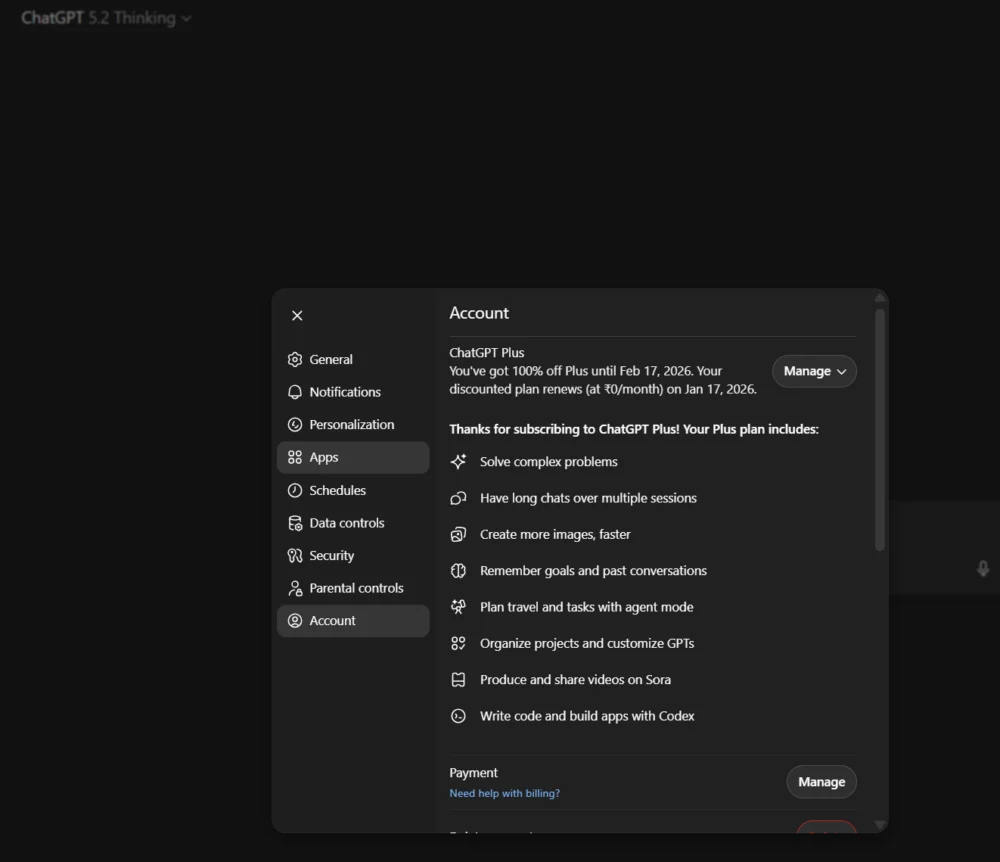
OpenAI Implements Strategic User Retention Program, Offering Complimentary Premium Access to Select Churn-Risk Subscribers
The landscape of artificial intelligence services is witnessing a heightened focus on subscriber retention, with leading provider OpenAI reportedly deploying a sophisticated strategy to mitigate customer churn. This initiative involves…
Sophisticated Botnet Unleashes Coordinated Assault on Next.js Ecosystem Through React2Shell Vulnerability
A highly adaptive and persistent botnet, identified as RondoDox, has been observed systematically exploiting the critical React2Shell flaw, designated CVE-2025-55182, to compromise a vast array of Next.js servers, subsequently deploying…
Decentralized IP Platform Unleash Protocol Suffers $3.9 Million Exploit Following Critical Multisignature Governance Breach
A sophisticated security breach has crippled Unleash Protocol, a pioneering decentralized intellectual property platform, resulting in the illicit exfiltration of approximately $3.9 million in various digital assets. The incident, which…