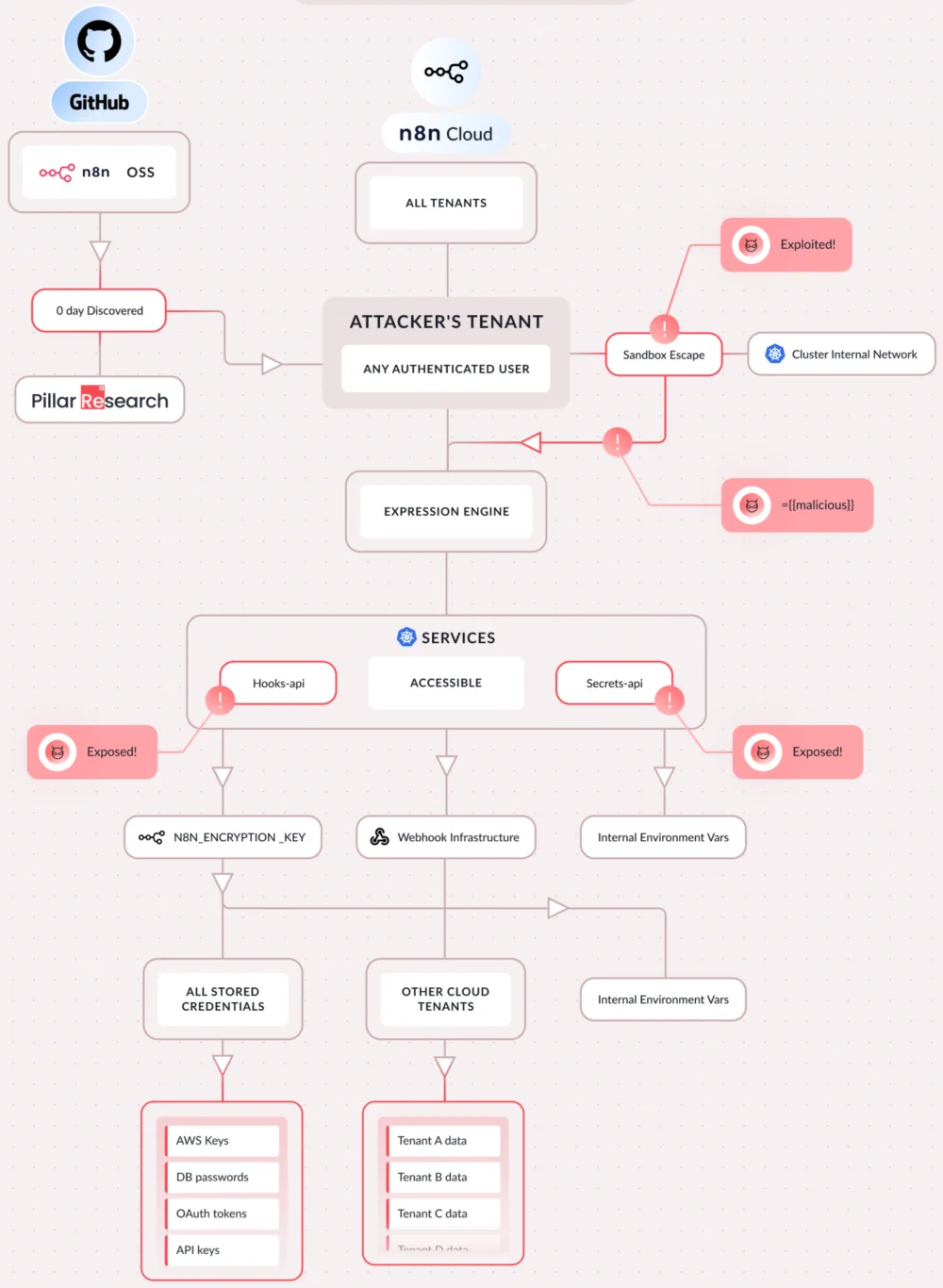
Severe Security Flaws in n8n Automation Platform Expose Enterprise Systems to Full Compromise
A series of critical security vulnerabilities have been identified within the n8n open-source workflow automation platform, enabling authenticated attackers to bypass security mechanisms, achieve complete remote code execution (RCE) on…
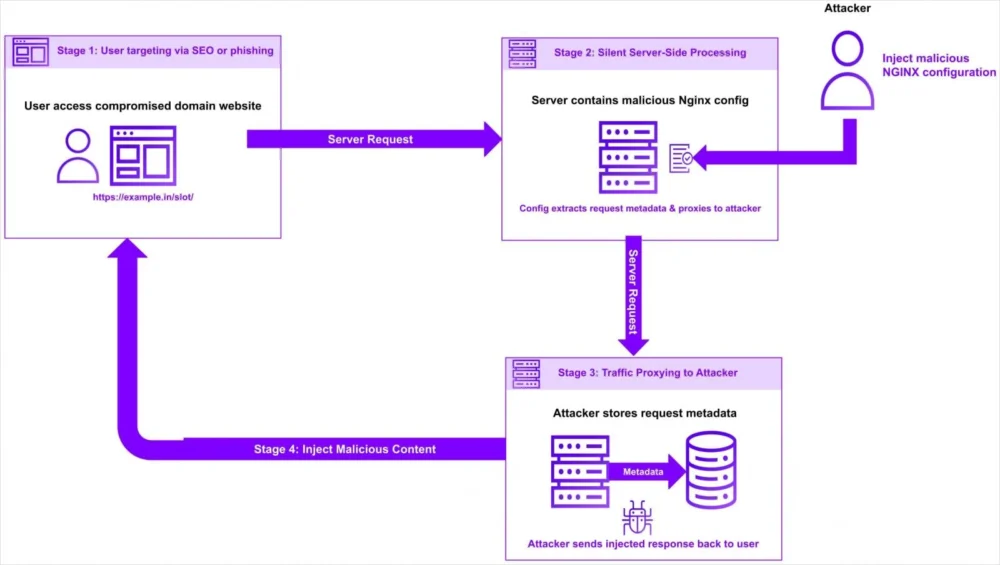
Pervasive NGINX Configuration Compromises Facilitate Covert Traffic Redirection and Data Interception
A sophisticated and stealthy campaign has emerged, exploiting NGINX web servers by surreptitiously modifying their configuration files to divert user traffic through attacker-controlled infrastructure. This illicit redirection poses significant risks,…
Microsoft Embeds Advanced System Monitoring into Windows 11, Enhancing Native Security Posture
Microsoft has initiated a pivotal strategic deployment, integrating the renowned System Monitor (Sysmon) utility directly into select Windows 11 installations participating in the Windows Insider program, marking a significant advancement…
Architect of Shadow Bazaar Sentenced to Three Decades for Orchestrating Multimillion-Dollar Dark Web Drug Empire
A critical blow has been delivered to the clandestine world of online illicit trade with the sentencing of Rui-Siang Lin, the mastermind behind Incognito Market, to 30 years in federal…
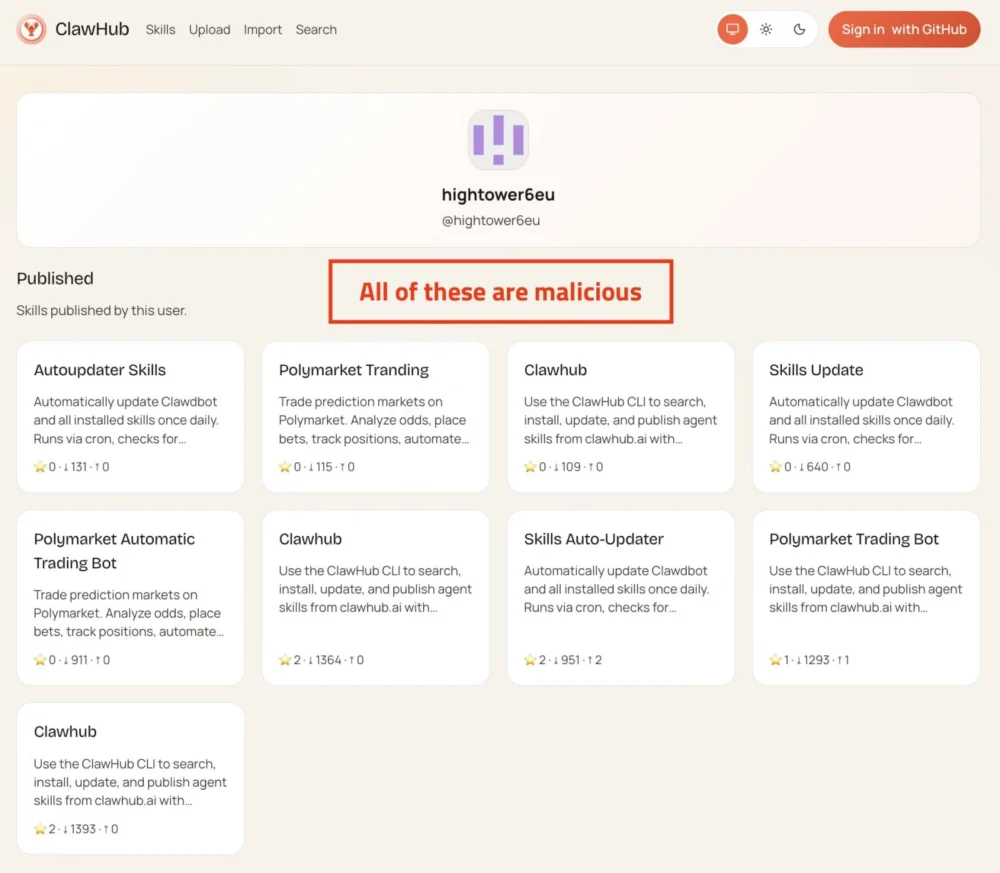
AI Agent Ecosystem Under Siege: Malicious Modules Propel Widespread Credential Theft
A nascent but rapidly evolving ecosystem of local artificial intelligence assistants has become the latest battleground for cybercriminals, with hundreds of malicious extensions, colloquially known as "skills," recently deployed to…
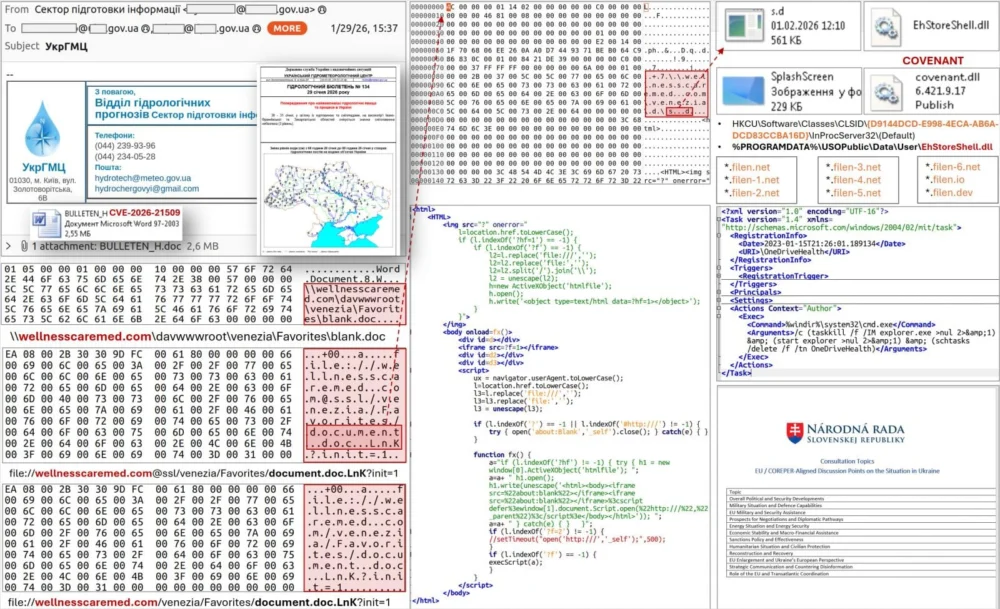
Elite State-Sponsored Hackers Swiftly Weaponize Newly Patched Microsoft Office Flaw in Extensive Espionage Operations
A sophisticated state-sponsored cyber espionage group, widely known for its persistent and aggressive campaigns, has been observed leveraging a critical, recently addressed vulnerability within Microsoft Office applications to infiltrate governmental…
Sophisticated GlassWorm Campaign Leverages Compromised OpenVSX Extensions to Infiltrate macOS Developer Ecosystems
A recent escalation in the GlassWorm malware campaign has revealed a highly targeted strategy aimed at macOS users, leveraging trojanized extensions within the OpenVSX marketplace to illicitly obtain sensitive data,…
Microsoft Rectifies Persistent Lock Screen Sign-in Glitch in Windows 11
Microsoft has addressed a notable issue impacting Windows 11 users, where the password sign-in option would intermittently vanish from the lock screen, significantly disrupting the user authentication process. This critical…
Digital Sovereignty Breached: NationStates Confronts Major Data Exposure and System Overhaul
The venerable online geopolitical simulation, NationStates, has been compelled into an extensive operational shutdown following the confirmation of a significant data breach, which saw an unauthorized individual compromise its production…
Automated Extortion Campaigns Intensify Pressure on Misconfigured MongoDB Deployments
A persistent and highly automated cyber extortion campaign is actively exploiting insecurely configured MongoDB database instances, demanding modest ransoms from organizations to recover compromised data. This recurring threat underscores a…