Unauthenticated Root Control: A Grave Exposure in Juniper PTX Routers Threatens Global Network Integrity
A severe security vulnerability has been identified within the Junos OS Evolved operating system, specifically impacting Juniper Networks’ PTX Series core and peering routers. This critical flaw could enable an…
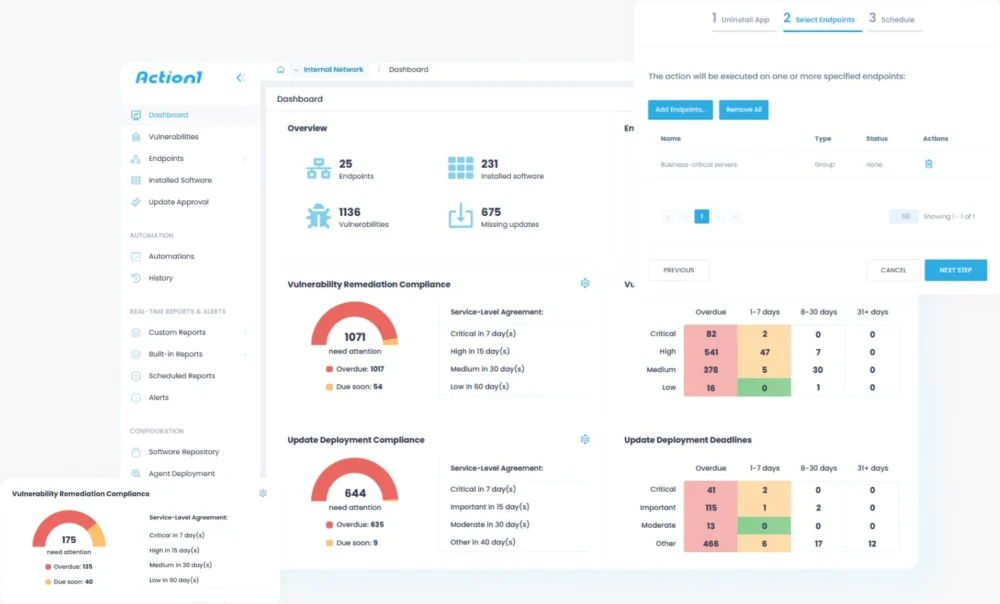
The Unseen Battleground: Securing the Pervasive Third-Party Software Footprint
Modern cybersecurity strategies frequently concentrate on the visible architectural pillars of an enterprise, yet a more insidious and equally critical vulnerability often resides within the ubiquitous, everyday applications that form…
High-Profile Security Breach: South Korean Tax Authority’s Operational Oversight Leads to $4.8 Million Cryptocurrency Heist
A significant operational security lapse by South Korea’s National Tax Service (NTS) has resulted in the theft of approximately $4.8 million in digital assets, following the inadvertent public exposure of…
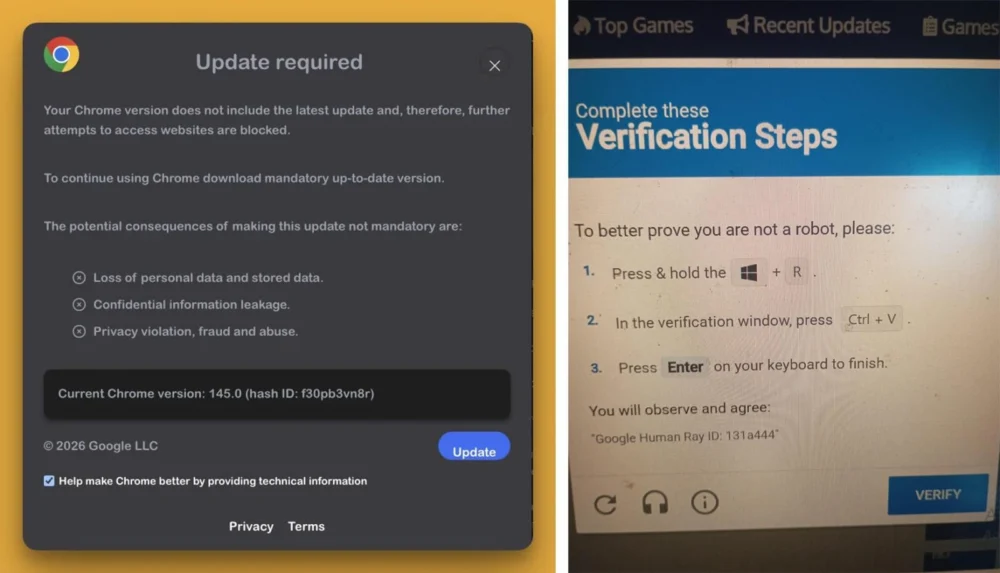
Stealthy Acquisition Transforms Popular Chrome Extension into Potent Cryptocurrency and Data Theft Platform
A widely adopted browser extension, "QuickLens – Search Screen with Google Lens," previously recognized for its utility and even featured by Google, has been irrevocably compromised, transitioning from a benign…
CISA Unveils Deeply Concealed RESURGE Threat Lurking on Ivanti Appliances, Posing Persistent Stealth Risk
The United States Cybersecurity and Infrastructure Security Agency (CISA) has issued a critical intelligence update detailing the advanced capabilities of RESURGE, a sophisticated malicious implant found compromising Ivanti Connect Secure…
Global Intelligence Agencies Uncover, Disrupt Transnational Cybercrime Syndicate Exploiting Youth and Corporate Infrastructure
A comprehensive, year-long international law enforcement initiative has delivered a substantial blow against a formidable digital criminal collective known as "The Community," or "The Com." This meticulously coordinated operation, spearheaded…
Advanced Persistent Threat 37 Deploys Novel Ruby-Based Toolkit to Circumvent Air-Gapped Network Defenses
A recent analysis has unveiled a highly sophisticated cyber campaign, dubbed "Ruby Jumper," orchestrated by the North Korean state-sponsored group APT37, which leverages an innovative malware suite to bridge isolated…
Microsoft Fortifies Windows 11 Batch Script Execution Against Runtime Tampering and Enhances Shared Audio Capabilities.
Recent Windows 11 Insider Preview builds from Microsoft introduce significant advancements designed to bolster the security and optimize the operational efficiency of batch file and Command Prompt script execution within…
International Cybercrime: AI-Powered Counterfeit Identity Operation Dismantled as Ukrainian Operator Enters Guilty Plea
A significant development in the realm of cybercrime has seen a Ukrainian national admit guilt in orchestrating a sophisticated online enterprise that leveraged artificial intelligence to fabricate and distribute more…
Digital Retailer ManoMano Faces Major Data Compromise, Exposing Information of 38 Million Customers Via Third-Party Breach
A significant cybersecurity incident has afflicted ManoMano, the prominent European online marketplace for home improvement and DIY products, leading to the unauthorized disclosure of personal data belonging to approximately 38…