Sophisticated Phishing Campaign Leverages Microsoft Teams and Quick Assist to Deploy Stealthy A0Backdoor Malware Against Critical Sectors
A recent sophisticated cyberattack campaign has been uncovered, meticulously targeting employees within financial and healthcare organizations through Microsoft Teams, ultimately leading to the deployment of a novel remote access trojan…
Artificial Intelligence Search Systems Exploited to Propagate Advanced Malware Through Fabricated Software Repositories
A recent cybersecurity incident has exposed a sophisticated campaign where threat actors exploited artificial intelligence-powered search functionalities, specifically within Microsoft Bing, to disseminate information-stealing and proxy malware through deceptive GitHub…
Cyber Adversaries Exploit Infrastructure-Specific .arpa Domains and IPv6 for Sophisticated Phishing Attacks
Malicious actors are increasingly leveraging specialized internet infrastructure, specifically the .arpa top-level domain (TLD) and IPv6 reverse DNS mechanisms, to orchestrate advanced phishing campaigns that effectively bypass conventional email security…
Landmark EU Legal Stance Poises Banks for Immediate Phishing Reimbursements
A significant legal opinion from the highest judicial advisory body in the European Union suggests a fundamental shift in the liability framework for unauthorized payment transactions. The Advocate General of…
Covert Chinese Cyber Espionage Unveils Sophisticated Multi-Platform Toolkit Against South American Telecommunication Infrastructure
A sophisticated and persistent cyber espionage campaign, meticulously linked to state-sponsored actors operating out of China, has been systematically compromising critical telecommunications service providers across South America since early 2024,…
Microsoft Fortifies Data Resilience with Granular File and Folder Recovery for Microsoft 365 Backup
Microsoft is poised to introduce a pivotal enhancement to its Microsoft 365 Backup service, enabling administrators to execute highly precise file and folder-level restorations. This strategic advancement signifies a profound…
Termite ransomware breaches linked to ClickFix CastleRAT attacks
A formidable cybercriminal organization, identified by intelligence agencies as Velvet Tempest and tracked by some as DEV-0504, has been observed deploying a complex array of initial access techniques and stealthy…
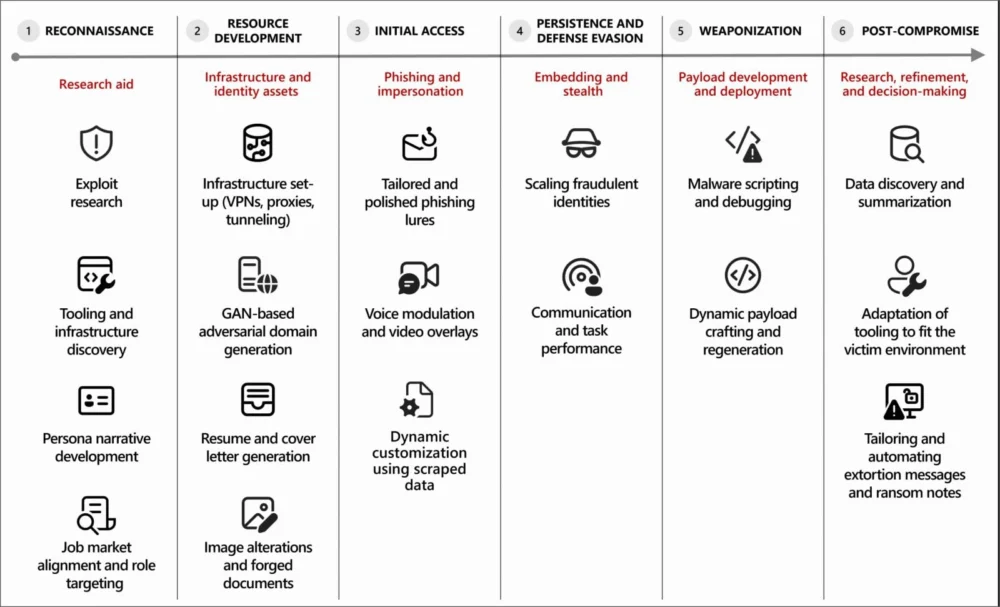
The Dawn of Algorithmic Malice: How Advanced AI is Empowering a New Generation of Cyber Adversaries
The global cybersecurity landscape is undergoing a profound transformation as malicious actors increasingly leverage sophisticated artificial intelligence capabilities across the full spectrum of their illicit digital operations. This strategic adoption…
Digital Scams Evolve: Malicious Install Guides Exploit AI Tool Demand to Deliver Info-Stealers
A sophisticated new cyberattack vector, dubbed "InstallFix," is actively leveraging deceptive installation guides for popular command-line interface (CLI) tools, including a fraudulent version of Anthropic’s Claude Code, to propagate advanced…
EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
A significant strategic initiative has been launched by EC-Council, a global leader in applied cybersecurity education, through the introduction of its Enterprise AI Credential Suite and a comprehensively updated Certified…