Washington Hotel Confronts Digital Extortion: Japanese Hospitality Sector Under Scrutiny Following Major Ransomware Attack
Fujita Kanko Inc.’s esteemed Washington Hotel chain, a pivotal entity within Japan’s business hospitality sector, has officially confirmed a significant ransomware infiltration that impacted its internal server infrastructure. This sophisticated…
Federal Agencies Face Urgent Mandate: CISA Directs Immediate Patching for Actively Exploited BeyondTrust Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an unequivocal directive to federal civilian executive branch (FCEB) agencies, compelling them to remediate an actively exploited remote code execution…
Sophisticated ClickFix Campaigns Leverage DNS Queries for Covert Payload Delivery and Advanced Evasion
Cyber adversaries are now deploying an innovative tactic within their "ClickFix" social engineering campaigns, exploiting Domain Name System (DNS) lookups to clandestinely retrieve and execute malicious PowerShell scripts, marking a…
Google Expedites Patch for First Critical Chrome Zero-Day of the Year Under Active Exploitation
The digital security landscape has once again highlighted the relentless cat-and-mouse game between developers and malicious actors, as Google moved swiftly to deploy urgent updates for its Chrome web browser.…
Luxury Retailer Canada Goose Grapples with Extensive Customer Data Exposure Amidst Hacker Claims of Third-Party Compromise
A significant cybersecurity incident has emerged, involving luxury outerwear brand Canada Goose, as a prominent data extortion collective, ShinyHunters, publicly asserts the acquisition and subsequent leak of over 600,000 customer…
Urgent Threat: Unauthenticated Remote Code Execution in BeyondTrust Platforms Actively Exploited Following Public PoC Release
A severe security vulnerability permitting unauthenticated remote code execution in BeyondTrust’s Remote Support and Privileged Remote Access solutions is now subject to active exploitation in the wild, mere days after…
Urgent Mandate Issued: CISA Elevates Microsoft SCCM Flaw to Critical Exploit Status, Demanding Immediate Federal Action
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent directive to federal agencies, compelling immediate mitigation against a critical vulnerability within Microsoft Configuration Manager (SCCM) that is…
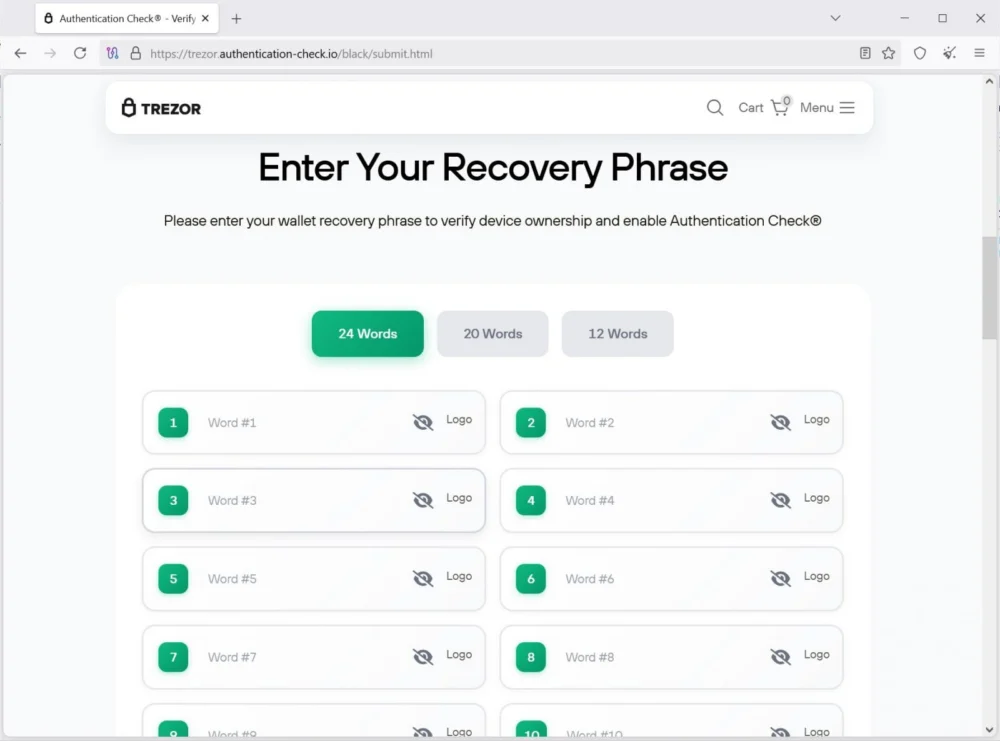
Sophisticated Physical Phishing Campaign Targets Hardware Wallet Users, Exposing Crypto Assets to Theft
A sophisticated and deeply concerning wave of physical phishing attacks has emerged, specifically designed to compromise the digital assets of cryptocurrency hardware wallet owners by impersonating leading manufacturers Trezor and…
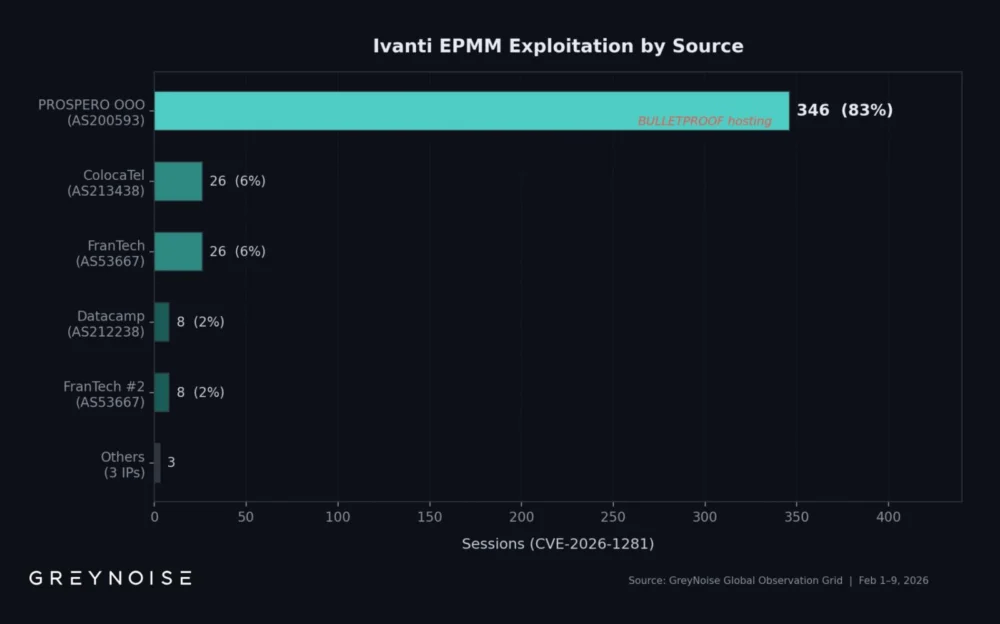
A Singular Adversary’s Broad Campaign: Dominating Ivanti EPMM Exploitation and Beyond
Recent intelligence indicates a highly focused and automated cyber campaign, with a single threat actor executing the vast majority of attacks targeting critical vulnerabilities within Ivanti Endpoint Manager Mobile (EPMM).…
Elevating Cyber Defenses: Integrating Advanced Threat Intelligence with IBM QRadar for Proactive Security Operations
The modern cybersecurity landscape demands increasingly sophisticated tools and integrated workflows to combat persistent and evolving threats. A significant advancement in this domain is the seamless integration of Criminal IP,…