A former data analyst has been convicted in a high-stakes scheme involving the illicit exfiltration of sensitive corporate information and a subsequent attempt to extort a technology company for $2.5 million, underscoring the escalating risks posed by disgruntled employees and contractors within the digital enterprise landscape. The case, originating from North Carolina, centered on Cameron Curry, also known by the alias "Loot," who leveraged his privileged access to internal systems at Brightly Software, a prominent Software-as-a-Service (SaaS) provider, to pilfer critical data before initiating a sophisticated blackmail operation. This incident serves as a stark reminder of the persistent challenge of insider threats, where individuals with authorized access exploit their positions for malicious gain, often driven by perceived grievances or financial desperation.
The targeted entity, Brightly Software, holds significant standing in the technology sector, having operated for over two decades and servicing more than 12,000 clients globally with its intelligent asset management and maintenance solutions. Acquired by Siemens in August 2022, the company, previously known as SchoolDude, employs over 700 professionals across its operations, primarily in North America, the United Kingdom, and Australia. Curry, then a 27-year-old contractor, was engaged as a data analyst with extensive permissions to access the company’s payroll information and other proprietary corporate data. It was in this capacity that he meticulously gathered a trove of sensitive documents, including personally identifiable information (PII) of employees such as names, dates of birth, home addresses, and compensation details. His actions reportedly stemmed from learning that his six-month contract, set to conclude on December 10, would not be extended, a common trigger for insider malicious activity.
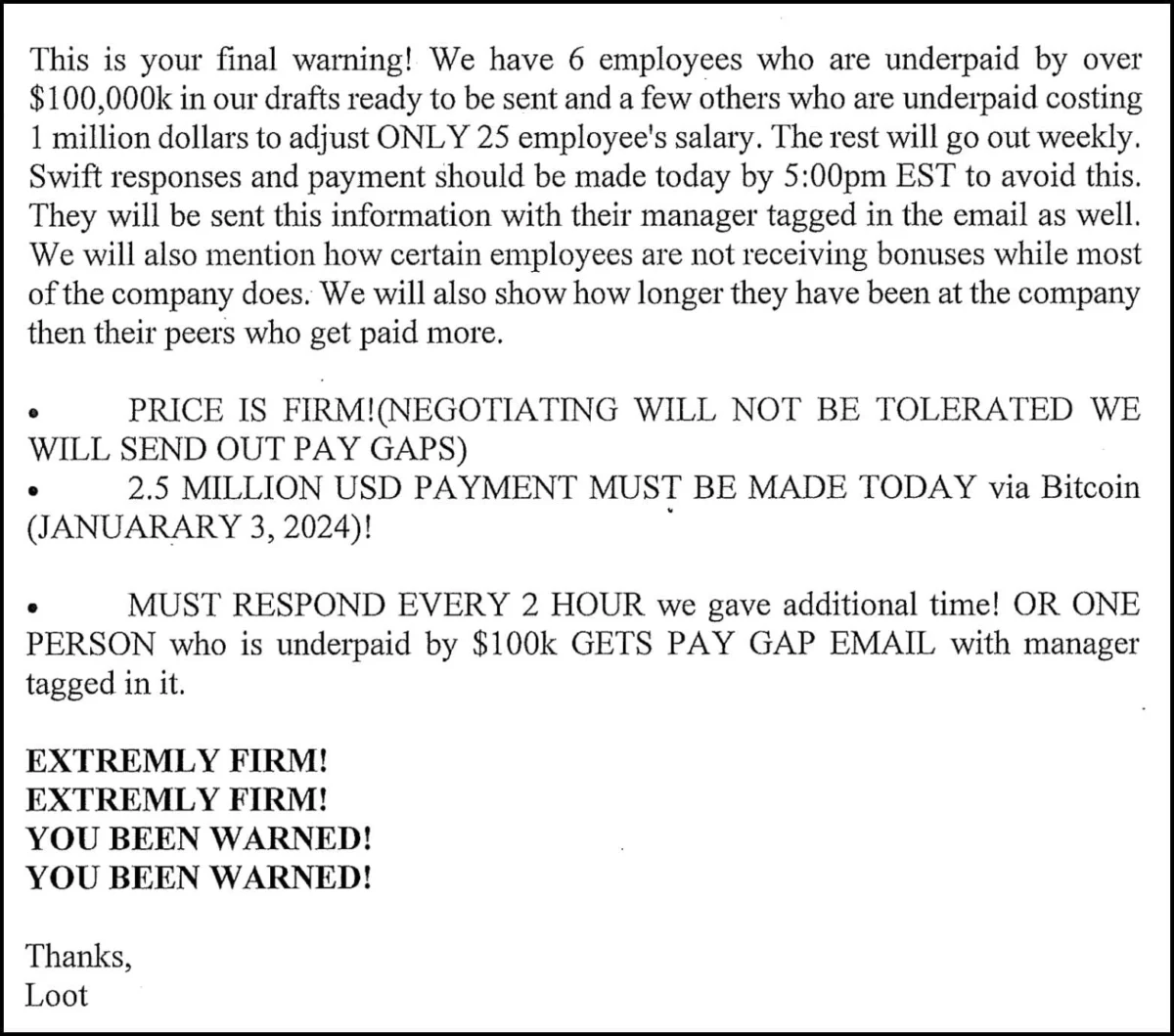
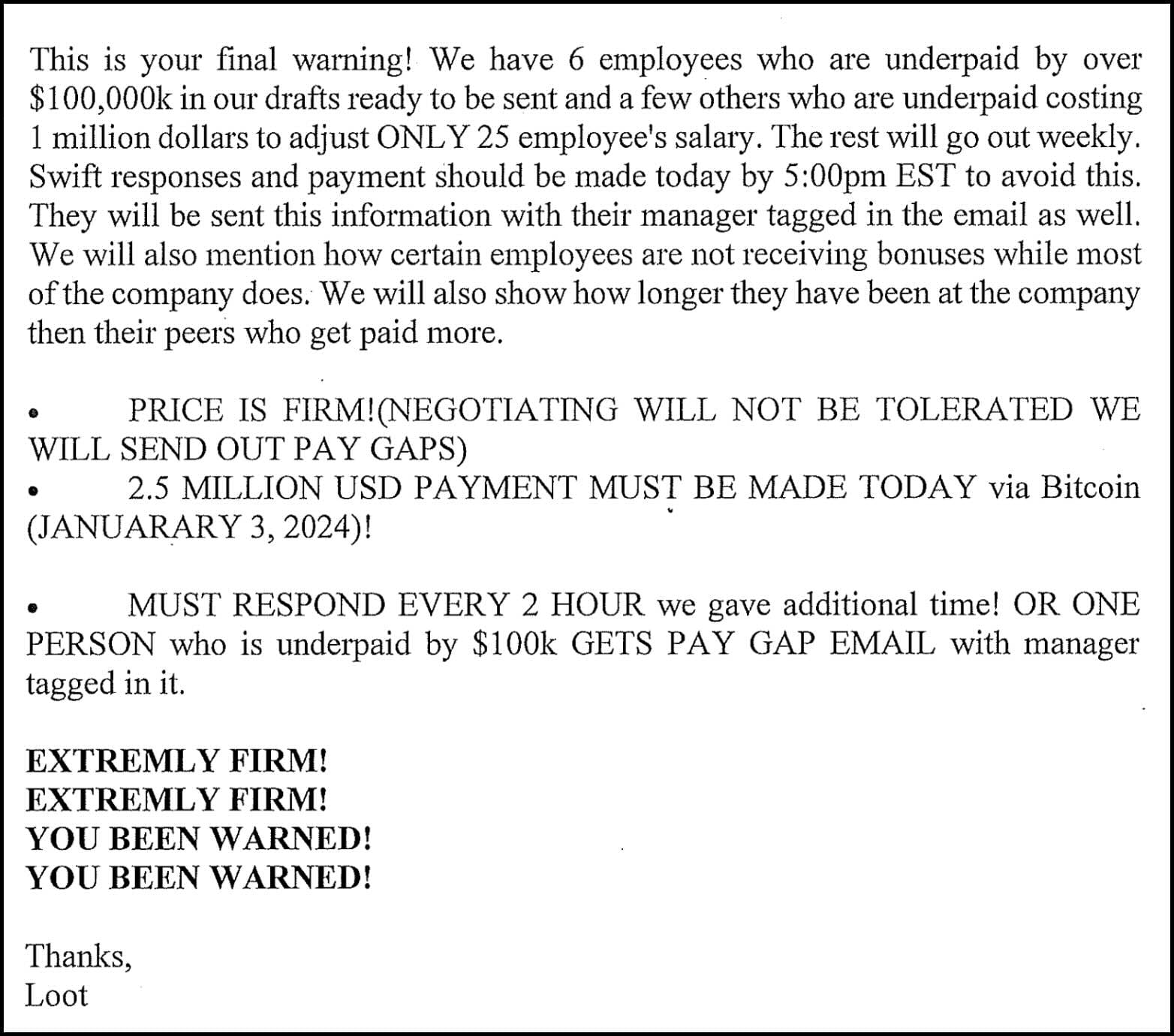
The transition from disgruntled contractor to active threat actor was swift and deliberate. Merely one day after his contract formally ended, Curry initiated a calculated extortion campaign. Utilizing a Microsoft email address, [email protected], and the "Loot" alias, he dispatched over 60 threatening emails to Brightly employees. These communications demanded a $2.5 million ransom, payable in cryptocurrency, to prevent the public dissemination of the sensitive information he had illegally acquired between August and December 2023. To substantiate his threats and demonstrate the veracity of his claims, Curry attached screenshots of spreadsheets containing the compromised PII of Brightly personnel, serving as undeniable proof of his illicit access and data exfiltration.

Beyond the immediate threat of data leakage, Curry’s extortion strategy incorporated a significant regulatory component. He explicitly threatened to report Brightly to the U.S. Securities and Exchange Commission (SEC) for failing to disclose the data breach, leveraging the company’s potential legal obligations and the reputational damage associated with non-compliance. One particularly revealing email stated, "We will commence the process of disseminating salary information starting January 1, 2024, in phases to all employees and will report you to the SEC after for not reporting the breach." He further intensified the pressure, asserting, "If you wish to reclaim your data, we recommend doing so promptly at 2.5 million USD in order to save your company and stocks, as each subsequent month will incur a $100,000 USD increase. Discrepancies in your books are currently over 16 million USD, posing a potential risk for retention issues, a hostile work environment, resentment, and more." This multi-pronged approach, combining data exposure threats with regulatory reporting implications, highlights a sophisticated understanding of corporate vulnerabilities and potential legal repercussions.
The company, facing an immediate and credible threat, engaged with the extortionist, ultimately transferring $7,540 in Bitcoin to a cryptocurrency wallet under Curry’s control. While this amount was significantly less than the initial $2.5 million demand, it signifies a direct response to the threat and likely represented an attempt to buy time, assess the situation, or mitigate immediate harm. The involvement of cryptocurrency in the transaction underscores a growing trend in cybercrime, as digital currencies offer a degree of anonymity that criminals often exploit, though law enforcement agencies have made significant strides in tracing such transactions. Following Brightly’s report to federal authorities, the Federal Bureau of Investigation (FBI) launched an intensive investigation. On January 24, law enforcement executed a search warrant at Curry’s residence, seizing various electronic devices that contained conclusive evidence of his elaborate extortion scheme. Curry was subsequently released on bond and now faces a maximum of 12 years in federal prison for six counts of transmitting or willfully causing interstate communications with the intent to extort a victim company.
This incident casts a critical spotlight on the broader issue of insider threats, which remain among the most challenging cybersecurity risks for organizations. Unlike external attacks, insider threats originate from individuals who possess legitimate access to an organization’s systems and data, making detection and prevention particularly complex. The motivations behind such threats are diverse, ranging from financial gain, as seen in Curry’s case, to personal grievances, espionage, or even negligence. A key factor enabling such breaches is often inadequate access control mechanisms and insufficient monitoring of privileged user activity. Data analysts, by the nature of their roles, often require broad access to sensitive datasets, creating a critical attack surface if not properly managed and audited. Organizations must implement robust data loss prevention (DLP) strategies, user behavior analytics (UBA), and stringent access management protocols based on the principle of least privilege, ensuring that individuals only have access to the data absolutely necessary for their job functions.
The regulatory implications of such data breaches are also substantial. Curry’s threat to report Brightly to the SEC for non-disclosure points to the increasing accountability placed on companies regarding cybersecurity incidents. Publicly traded companies, or those like Brightly that have been acquired by public entities such as Siemens, are subject to stringent disclosure requirements, particularly concerning material cybersecurity incidents that could impact investors. Failure to report a breach in a timely and transparent manner can lead to severe penalties, including fines, legal action, and significant reputational damage. Beyond SEC regulations, various data privacy laws, such as the General Data Protection Regulation (GDPR) in Europe and state-level laws like the California Consumer Privacy Act (CCPA) in the United States, mandate strict breach notification protocols when PII is compromised. These regulations underscore the necessity for organizations to have comprehensive incident response plans that include legal and public relations strategies, in addition to technical remediation.
The financial and reputational ramifications for Brightly Software extend beyond the immediate extortion attempt. While the company stated its full cooperation with the FBI and Department of Justice (DOJ), the very fact of an insider breach can erode trust among clients, partners, and employees. The cost of such incidents encompasses not only the direct financial losses from the extortion payment and investigative expenses but also potential legal fees, regulatory fines, and the long-term impact on brand image. Moreover, employee morale can be significantly affected when their personal data is compromised by a colleague, leading to heightened anxiety and a potential decrease in productivity. This incident also raises questions about the vetting processes for contractors and the offboarding procedures in place. Effective offboarding protocols should include immediate revocation of all system access, data retrieval, and forensic analysis of user activity during the final period of employment to detect any suspicious data exfiltration attempts.
It is noteworthy that this insider threat incident occurred against the backdrop of another, unrelated data breach experienced by Brightly in May 2023. In that instance, attackers gained unauthorized access to the database of its SchoolDude online platform, compromising credentials and personal data, including names, email addresses, account passwords, and phone numbers, affecting nearly 3 million customers. While distinct from Curry’s extortion scheme, the proximity of these events highlights the multifaceted cybersecurity challenges faced by large technology companies. It underscores the critical importance of a holistic security posture that addresses both external threats and internal vulnerabilities. A robust security framework must encompass continuous monitoring, advanced threat detection, comprehensive employee training on cybersecurity best practices, and a culture of security awareness that permeates all levels of the organization, including contractors.
Looking ahead, the landscape of insider threats is expected to evolve, particularly with the proliferation of remote work models and the increasing reliance on contractors and third-party vendors. Organizations must adapt their security strategies to account for a more distributed workforce and the inherent complexities of managing access and monitoring activity across diverse environments. This includes investing in sophisticated security technologies that can detect anomalous behavior, implementing stronger identity and access management (IAM) solutions, and fostering an environment where employees feel empowered to report suspicious activities without fear of reprisal. Furthermore, the legal and regulatory frameworks governing data protection and breach disclosure will continue to mature, placing greater onus on companies to safeguard sensitive information. The successful prosecution of individuals like Cameron Curry serves as a deterrent but also emphasizes the ongoing imperative for organizations to fortify their defenses against the persistent and insidious risk of insider threats. The Brightly Software case is a critical reminder that while external adversaries command significant attention, the threats lurking within an organization’s own ranks demand equally rigorous attention and proactive mitigation strategies.






