Google has issued an emergency security bulletin, releasing critical updates for its Chrome web browser to remediate two high-severity vulnerabilities that have been actively exploited by malicious actors in the wild. This urgent patch underscores the persistent and evolving threat landscape facing web browsers, which serve as primary gateways to the internet for billions of users worldwide. The rapid deployment of these fixes highlights Google’s proactive stance in mitigating immediate dangers posed by sophisticated threat campaigns.
The two critical flaws, designated CVE-2026-3909 and CVE-2026-3910, were identified and addressed by Google within a remarkably short timeframe, signifying the severity and potential widespread impact of their exploitation. The company’s security advisory, published on Thursday, confirmed that "exploits for both CVE-2026-3909 & CVE-2026-3910 exist in the wild," a declaration that immediately elevates these vulnerabilities from theoretical risks to active threats demanding prompt user action. This "in the wild" status indicates that sophisticated attackers have already developed and deployed methods to leverage these weaknesses against unsuspecting users, potentially compromising their systems and data.
The first of these vulnerabilities, CVE-2026-3909, is rooted in an out-of-bounds write flaw within Skia, Google’s open-source 2D graphics library. Skia is a fundamental component of Chrome, responsible for the rendering of a vast array of web content and user interface elements, from text and images to complex animations. An "out-of-bounds write" error occurs when a program attempts to write data beyond the allocated memory buffer, potentially corrupting adjacent data or even executing arbitrary code. In the context of a web browser, successful exploitation of such a vulnerability could lead to a range of severe consequences. At a minimum, it could cause the browser to crash, disrupting user activity. More critically, an attacker could leverage this flaw to achieve arbitrary code execution within the browser’s sandbox, and potentially even escape the sandbox to gain control over the underlying operating system. The criticality of Skia to Chrome’s operations means that a vulnerability within it presents a significant attack surface, making it a prime target for adversaries.
The second vulnerability, CVE-2026-3910, is classified as an "inappropriate implementation" flaw residing within the V8 JavaScript and WebAssembly engine. V8 is the powerhouse behind Chrome’s ability to execute complex web applications, processing JavaScript and WebAssembly code at high speeds. An "inappropriate implementation" typically refers to a design or logical error in how security mechanisms are applied or how certain features interact, leading to unintended and exploitable behaviors. This type of vulnerability could allow attackers to bypass security checks, disclose sensitive information, or execute malicious code in contexts where it should be prevented. Given V8’s central role in dynamic web content processing, an exploitation here could grant attackers substantial control over the browser’s execution environment, potentially leading to data theft, malware injection, or further system compromise.
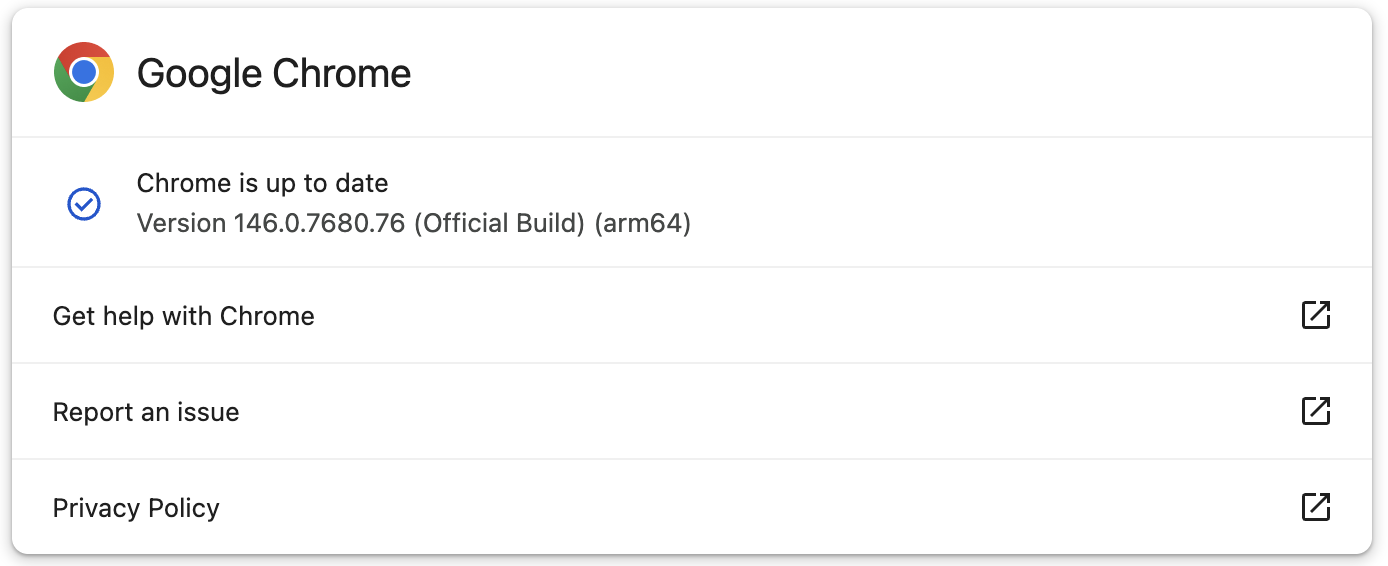
Both vulnerabilities were discovered internally by Google’s own security teams, underscoring the company’s continuous investment in proactive security research and threat intelligence. The rapid development and deployment of patches – within two days of discovery – for users across the Stable Desktop channel highlights the urgency Google places on containing active exploits. The updated Chrome versions now rolling out are 146.0.7680.75 for Windows and Linux systems, and 146.0.7680.76 for macOS. While Google has communicated that these out-of-band updates may take several days or even weeks to propagate across the entire user base, many users, including security researchers, have reported immediate availability upon checking for updates. This disparity emphasizes the importance of users proactively initiating manual updates rather than solely relying on the automatic update cycle, especially when critical zero-day exploits are known to be active.
To ensure the highest level of protection, users are strongly advised to update their Chrome browsers without delay. The update process is straightforward: users can navigate to the "Help" menu, select "About Google Chrome," and the browser will automatically check for and initiate the installation of any pending updates. A browser restart is typically required to finalize the installation and apply the security fixes. For enterprise environments, centralized patch management solutions should be leveraged to ensure timely deployment across all organizational endpoints, minimizing the attack surface.
In line with its standard security protocols, Google has refrained from releasing extensive technical details regarding the specific nature of these exploits or the attack campaigns currently leveraging them. This deliberate policy aims to prevent reverse engineering of the patches by other malicious actors, which could then be used to develop new exploits targeting unpatched systems. Google stated, "Access to bug details and links may be kept restricted until a majority of users are updated with a fix. We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed." This approach prioritizes user safety by creating a window of opportunity for widespread patching before detailed attack vectors become public knowledge.
These two newly patched vulnerabilities represent the second and third actively exploited Chrome zero-days addressed by Google since the beginning of 2026, signaling a concerning trend in the current year. The first, identified as CVE-2026-2441, was a critical "iterator invalidation" bug found in CSSFontFeatureValuesMap, a component of Chrome’s implementation of CSS font feature values. This flaw was patched in mid-February, indicating a consistent stream of sophisticated attacks targeting Chrome’s core functionalities. The pattern of multiple zero-day exploits within a short period underscores the relentless efforts of advanced persistent threat (APT) groups and other cybercriminals to find and exploit weaknesses in widely used software.
The historical context further emphasizes the gravity of the situation. In the preceding year, 2025, Google fixed a total of eight zero-days that were actively exploited in the wild. A significant portion of these high-stakes vulnerabilities were reported by Google’s renowned Threat Analysis Group (TAG). TAG is a dedicated team of security researchers specializing in tracking and identifying zero-days, particularly those associated with state-sponsored espionage and commercial spyware operations. Their consistent detection of such threats highlights the global proliferation of sophisticated digital weaponry and the critical role browsers play as targets in these campaigns. The exploitation of browser zero-days often serves as an initial access vector for more extensive attacks, including the deployment of surveillance tools or ransomware.
The continuous battle against these sophisticated threats is a testament to the ongoing cat-and-mouse game between software developers and malicious actors. While Google invests heavily in securing its products, the sheer complexity of modern web browsers and the innovative tactics of adversaries mean that vulnerabilities will inevitably emerge. The prompt identification and patching of these flaws, particularly those actively exploited, are paramount to maintaining the integrity and security of the digital ecosystem.
Beyond the immediate crisis management of zero-days, Google also champions proactive security measures through its Vulnerability Reward Program (VRP). On the same day these emergency patches were announced, Google revealed a significant investment in this program, having paid out over $17 million to 747 independent security researchers in 2025 for reporting security flaws. This substantial financial incentive encourages ethical hackers and security experts worldwide to responsibly disclose vulnerabilities, allowing Google to fix them before they can be discovered and exploited by malicious entities. The VRP is a critical component of Google’s holistic security strategy, leveraging the collective intelligence of the global security community to enhance product safety.
In conclusion, the patching of two new Chrome zero-days exploited in active attacks serves as a stark reminder of the ever-present dangers in the digital realm. It underscores the critical importance of maintaining up-to-date software, particularly web browsers, which are often the first line of defense against cyber threats. For both individual users and large organizations, prioritizing these security updates is not merely a recommendation but an essential practice for safeguarding sensitive information and preventing system compromise in an increasingly hostile online environment. The ongoing vigilance of Google’s security teams, coupled with the valuable contributions of external researchers, remains crucial in this continuous effort to secure the internet for all users.