The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a high-priority alert regarding a critical vulnerability within Ivanti’s Endpoint Manager (EPM) software, designated CVE-2026-1603, confirming its active exploitation in ongoing cyberattacks and subsequently mandating an expedited remediation timeline for all federal civilian executive branch agencies. This directive underscores the severe risk posed by the flaw, which could permit unauthenticated remote attackers to compromise systems and harvest sensitive credential data, necessitating immediate action across government networks and serving as a stark warning to private sector entities leveraging Ivanti’s solutions.
The Strategic Imperative of Endpoint Management Solutions
Ivanti’s EPM stands as a foundational enterprise tool, offering a comprehensive, centralized platform for managing a diverse ecosystem of client devices. Spanning operating systems such as Windows, macOS, Linux, Chrome OS, and various Internet of Things (IoT) platforms, EPM solutions are indispensable for maintaining configuration consistency, deploying software, enforcing security policies, and overseeing device health across vast organizational footprints. Their intrinsic role in governing the integrity and functionality of an organization’s endpoints, however, simultaneously positions them as immensely attractive targets for sophisticated threat actors. A compromise of such a pervasive management interface can grant adversaries unparalleled access and control over an entire network, transforming a single vulnerability into a potential gateway for widespread systemic infiltration.
Unpacking CVE-2026-1603: A High-Severity Threat
The vulnerability in question, CVE-2026-1603, is categorized as a high-severity security flaw due to its potential for profound impact and relative ease of exploitation. Technical analysis reveals this weakness enables remote attackers, operating without any prior authentication or elevated privileges, to execute sophisticated cross-site scripting (XSS) attacks. Crucially, these attacks require no user interaction, dramatically lowering the barrier for entry for malicious campaigns.
In practice, a successful exploitation of this XSS vulnerability can lead to an authentication bypass. This typically occurs when an attacker injects malicious scripts into a web application, which are then executed by a legitimate user’s browser. In the context of an EPM solution, this could involve session hijacking, where the attacker steals session cookies or authentication tokens, thereby gaining unauthorized access to the system as if they were the legitimate, authenticated user. The primary objective articulated for this flaw is the theft of credential data. This encompasses a range of sensitive information, from user login credentials to potentially API keys or other authentication artifacts, which can then be leveraged for deeper network penetration, lateral movement within the compromised environment, or even persistent access. The "low-complexity" nature of these XSS attacks further amplifies the risk, suggesting that even less sophisticated adversaries could successfully weaponize this vulnerability.
CISA’s Mandate and the Known Exploited Vulnerabilities Catalog
CISA’s decision to add CVE-2026-1603 to its authoritative Known Exploited Vulnerabilities (KEV) Catalog signifies a critical escalation in the threat assessment. The KEV Catalog serves as a definitive resource for identifying vulnerabilities that have been confirmed to be actively exploited in the wild, providing an unequivocal signal to federal agencies and, by extension, to the broader cybersecurity community, that these flaws demand immediate attention. CISA’s inclusion criteria for the KEV Catalog are stringent, requiring verifiable evidence of active exploitation, thus transforming theoretical risks into tangible, imminent threats.

This designation triggers a binding operational directive (BOD 22-01), issued in November 2021, which mandates that all Federal Civilian Executive Branch (FCEB) agencies prioritize and remediate vulnerabilities listed in the KEV Catalog within specific, aggressive timelines. For CVE-2026-1603, the deadline for federal agencies to apply the necessary patches is March 23, a mere three weeks from the date of the alert. This swift turnaround reflects the urgency CISA places on neutralizing threats that have demonstrated real-world exploitability, recognizing them as "frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise." The directive underscores a proactive strategy aimed at bolstering the cybersecurity posture of federal networks against the most pressing and proven threats.
Ivanti’s Response and Discrepancies in Reporting
Ivanti, the vendor, proactively addressed CVE-2026-1603 approximately one month prior to CISA’s public alert, releasing a patch as part of Ivanti EPM 2024 SU5. This update also remediated an SQL injection flaw, allowing authenticated remote attackers to read arbitrary database data. According to Ivanti’s original advisory, the company stated it was "not aware of any customers being exploited by these vulnerabilities prior to public disclosure" and that the vulnerabilities were disclosed through its responsible disclosure program. When initially contacted for confirmation regarding active exploitation, Ivanti reiterated that it had received no reports of such activity.
The divergence between Ivanti’s stated awareness and CISA’s definitive flagging of active exploitation highlights a common challenge in the cybersecurity landscape: the lag and disparate sources of threat intelligence. CISA’s KEV Catalog often incorporates intelligence from a broad spectrum of sources, including government agencies, intelligence communities, and trusted security researchers, which may not always directly correlate with a vendor’s internal reporting mechanisms or what is publicly disclosed. This discrepancy does not necessarily imply a contradiction but rather illustrates the dynamic nature of threat intelligence gathering and the varying visibility into the global attack surface. For organizations, CISA’s KEV listing serves as the authoritative confirmation of active exploitation, irrespective of the vendor’s immediate awareness.
The Pervasive Threat to Ivanti EPM Deployments
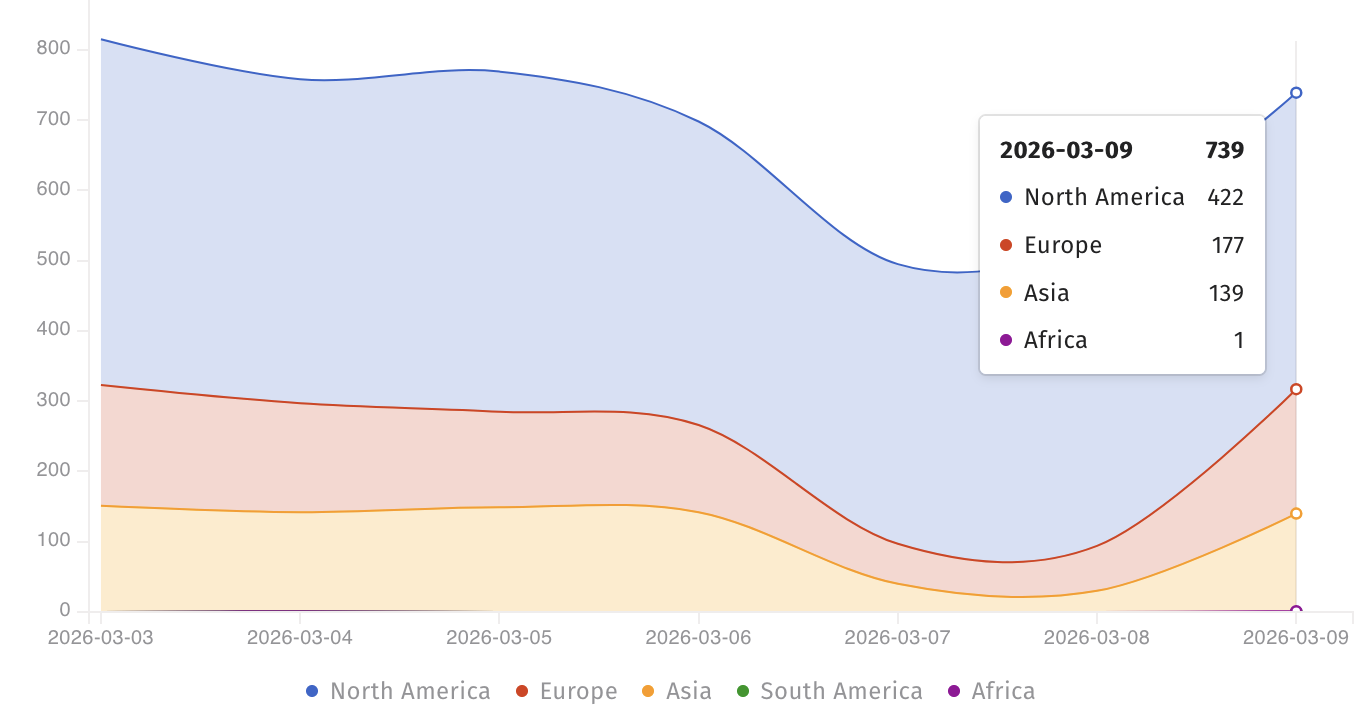
The global footprint of Ivanti EPM installations presents a substantial attack surface. Data from the Shadowserver threat monitoring platform reveals over 700 Internet-facing Ivanti EPM instances currently exposed, with a significant concentration in North America. While this figure provides an indication of visibility, it offers no precise insight into how many of these publicly accessible instances remain unpatched and therefore vulnerable to CVE-2026-1603. This lack of granular data suggests that the true extent of the exploitable population could be considerably higher, extending beyond directly exposed systems to those accessible through less obvious network pathways.
The strategic importance of EPM solutions, combined with their extensive deployment across more than 40,000 companies globally, positions them as high-value targets for a wide array of threat actors, from state-sponsored groups engaged in espionage to financially motivated ransomware syndicates. A successful compromise of an EPM system can serve as a critical pivot point, enabling initial access, privilege escalation, lateral movement across an enterprise network, and ultimately, data exfiltration or the deployment of destructive payloads.
A Pattern of Exploitation: Historical Context
The current alert concerning CVE-2026-1603 is not an isolated incident but rather fits into a recurring pattern of Ivanti EPM vulnerabilities being actively targeted by malicious actors. In the past, CISA has repeatedly issued warnings and mandates regarding other EPM flaws that have fallen under active exploitation. For instance, approximately one year prior, CISA cautioned federal agencies to secure their networks against three distinct EPM vulnerabilities—CVE-2024-13159, CVE-2024-13160, and CVE-2024-13161—all of which were confirmed to be exploited in the wild. Furthermore, in October 2024, CISA mandated patching for another actively exploited EPM vulnerability, CVE-2024-29824, which allowed for remote code execution.
This historical context underscores the persistent attractiveness of Ivanti EPM products as targets. The consistent exploitation of these management tools by adversaries reflects their understanding of the critical role EPM plays in an organization’s IT infrastructure and the significant leverage a compromise can provide. This pattern necessitates that organizations view these alerts not as isolated events, but as symptomatic of an ongoing, strategic targeting of essential enterprise management software.
Comprehensive Remediation and Proactive Defense
Addressing CVE-2026-1603, and indeed any critical EPM vulnerability, demands a comprehensive and multi-layered approach beyond simply applying the patch. Organizations must first identify all instances of Ivanti EPM within their environment, including those that might not be directly Internet-facing but could still be vulnerable from internal network segments. The application of the Ivanti EPM 2024 SU5 update is paramount. However, the process of patching such a central management system can be complex, often requiring careful planning to minimize disruption to critical business operations.
Beyond patching, rigorous verification is essential to confirm that the update has been successfully applied across all relevant systems and that the vulnerability is no longer exploitable. This should be coupled with a thorough forensic investigation to ascertain if any systems were compromised prior to the patch application. Indicators of compromise (IoCs) related to XSS attacks or credential theft should be actively sought within system logs, network traffic, and endpoint detection and response (EDR) telemetry.
Proactive defensive measures are equally vital. These include robust network segmentation to limit the blast radius of any potential compromise, stringent access controls and the implementation of multi-factor authentication (MFA) for all EPM administrators, and continuous monitoring for anomalous activity around EPM systems. Regular security audits, penetration testing, and vulnerability management programs should specifically target critical infrastructure components like EPM to identify and mitigate risks before they can be exploited.
Implications for the Broader Cybersecurity Landscape
The CISA alert regarding CVE-2026-1603 serves as a potent reminder for all organizations, irrespective of their federal affiliation, to maintain vigilance and prioritize the patching of known exploited vulnerabilities. The cascading effects of a compromise to a widely deployed management solution like Ivanti EPM can extend far beyond the initially targeted entity, impacting supply chains and interconnected ecosystems. As threat actors continue to evolve their tactics, the focus on exploiting weaknesses in foundational enterprise software will undoubtedly persist. Organizations must therefore embed a culture of continuous security, proactive threat intelligence consumption, and swift incident response to effectively navigate the complex and ever-changing cyber threat landscape. The imperative is clear: secure these critical management platforms, or risk becoming another statistic in the growing roster of cyberattack victims.