Modern cybersecurity strategies frequently concentrate on the visible architectural pillars of an enterprise, yet a more insidious and equally critical vulnerability often resides within the ubiquitous, everyday applications that form the operational bedrock of any business. While network perimeters, server infrastructure, identity management systems, and cloud environments typically dominate discussions about an organization’s attack surface, the legion of third-party tools integral to daily work — from document readers to communication platforms — often receive insufficient scrutiny, creating a fertile ground for sophisticated cyber threats.
Beyond the Obvious Attack Surface
When security architects delineate an organization’s digital perimeter, the initial focus understandably gravitates towards high-profile assets. Enterprise servers, sophisticated identity management platforms, virtual private network (VPN) gateways, intricate cloud workloads, and even web browsers are frequently inventoried, diagrammed, and fortified. These components represent the structural backbone of an IT ecosystem, their presence evident and their security implications well-understood within established frameworks. However, this conventional lens often overlooks a vast, interwoven layer of software that, while less visible in strategic diagrams, is profoundly embedded in every operational workflow.
This overlooked stratum comprises the essential, often passively adopted, applications that empower employees to perform their core functions. Consider the pervasive nature of PDF readers, file compression utilities, remote access clients, word processing suites, spreadsheet applications, email clients, screen-sharing tools, and a myriad of background update managers. These are not merely supplementary programs; they are the silent engines powering contemporary business activities, facilitating communication, data processing, and collaboration across the digital landscape. Organizations rarely deliberate their deployment; instead, they are absorbed into the operational environment almost by default, a fundamental consequence of participating in a digitally driven economy where contracts arrive as PDFs, financial data is manipulated in spreadsheets, and global teams collaborate remotely. This inherent commonality, driven by practical necessity, paradoxically transforms these seemingly innocuous tools into prime targets for malicious actors.
The Inherent Value of Ubiquity
Modern enterprises, despite their varied network configurations, architectural nuances, and evolving security stacks, exhibit a striking commonality in their internal software landscapes. Specific classes of applications, and frequently the same leading software titles within those classes, reappear across countless installations. Operating effectively in the contemporary business world is virtually impossible without an email client, robust document processing software, a web browser, and utilities for file packaging, previewing, and sharing. This homogeneity is less a matter of organizational preference and more a direct consequence of the imperative for interoperability.
Business operations hinge on the seamless exchange of information in universally accessible formats. Absent these established standards, industries would revert to an era characterized by debilitating "file-format wars," where productivity is stifled by incompatible systems and valuable time is lost simply making data usable. The industry’s broad standardization around certain major software providers is a direct response to this need for frictionless collaboration. Threat actors are acutely aware of this standardization. Instead of expending resources on anticipating every bespoke application an organization might run, they strategically focus on this pervasive overlap. A vulnerability discovered in a widely deployed PDF rendering engine, a popular spreadsheet parser, a common email preview component, or a remote access utility carries a significantly higher probability of successful exploitation across a broad spectrum of targets. The exploit’s efficacy is thus rooted not in targeting unique architectures, but in leveraging universally familiar software. The majority of successful exploitations do not rely on arcane, exotic techniques; rather, they capitalize on ingrained user habits. Employees routinely open PDFs, Word documents, spreadsheets, and click on links countless times throughout their day. Attackers wager that these actions have become so routine that users will execute them without hesitation or critical assessment. This understanding of user behavior and software ubiquity profoundly influences how cyber campaigns are constructed and, consequently, how robust defense strategies must be conceived.
Probabilistic Attack Strategies
Historically, many cyber attacks bore the hallmarks of guesswork. An attacker might dispatch a meticulously crafted email designed to exploit a vulnerability in a specific email client, such as Outlook, operating on the hopeful assumption that the recipient indeed utilized that particular client. Similarly, weaponized spreadsheets were distributed with the hope that Microsoft Excel was present, or malicious PDFs sent in anticipation of a vulnerable reader. This approach inherently carried a degree of uncertainty. The exploit often launched before the attacker possessed definitive intelligence about the target’s precise software environment, elevating the risk of early detection and the wasteful expenditure of valuable, often single-use, exploit code that, once detected, could be profiled and subsequently neutralized.
The widespread prevalence of common utilities, however, fundamentally alters this probability curve. Email clients, web browsers, word processors, spreadsheet applications, PDF readers, and archive tools are not merely common; they are foundational components across nearly all business environments because the very nature of modern work mandates their use. An attacker, therefore, does not require perfect, granular information to confidently anticipate the presence of compatible software. Instead, exploitation becomes a calculated exercise in likelihood. Threat actors strategically allocate their resources where the overlap in software deployment is most extensive. The more universally adopted a tool, the more attractive it becomes as an initial point of entry. This dynamic explains why vulnerabilities discovered in these everyday utilities disseminate rapidly through global exploit ecosystems. Once a method proves effective within a widely adopted toolchain, its scalability is virtually assured. If a single user relies on a common suite of applications like Outlook, Word, and Adobe Acrobat, there is a high probability that their colleagues and external business partners utilize the same or functionally equivalent products for reasons of seamless interoperability.
The Interconnected Business Footprint
These ubiquitous tools rarely exist in isolation; they form an interconnected ecosystem. The very origination of an email, for instance, discernibly from a Microsoft Outlook client, provides a subtle but significant hint about the broader software environment. Email workflows are intrinsically linked to document workflows. The presence of Outlook frequently implies the proximate availability of Word and Excel. Each utility, therefore, tacitly reinforces the likely presence of others within the same operational context.

For malicious actors, this interconnectedness transforms isolated exploits into cohesive attack paths. A vulnerability within an email client can seamlessly connect to its attachment handling mechanisms, preview engines, document renderers, shared libraries, and the array of integrations that commonly coexist on a single system. Instead of merely targeting a singular application, the potential attack surface expands to encompass the entire operational "business footprint"—the integrated collection of tools that employees rely upon every day. When vulnerabilities emerge within this deeply embedded footprint, they garner heightened attention from attackers precisely because they align so naturally with established patterns of human work and digital interaction. This inherent synergy between commonly used tools creates a rich, interconnected environment that attackers can systematically probe and exploit.
Unintended Information Disclosure
Beyond overt vulnerabilities, another significant aspect of this pervasive software footprint is the quiet, often unconscious, leakage of information that users do not realize they are sharing. Digital documents, for example, frequently embed metadata: PDFs can reference the specific engine that generated them, spreadsheets might carry formatting behaviors indicative of particular software suites, and email headers often expose granular details about the client used for sending. Browser traffic routinely advertises user agents, and the very structure of digital files can reveal underlying habits and versioning.
Individually, these data points might appear innocuous, often remaining invisible to the casual observer. Yet, over time, the aggregation of these seemingly minor details constructs a comprehensive profile of an organization’s software stack. This composite picture reveals which tools are prevalent, what standards they adhere to, and how files are routinely processed. Crucially, it can expose outdated software details within current workflows, signaling that the processing software itself is likely antiquated. Old software often signifies years of accumulated, unpatched exploit potential, effectively bottled up within a single application package. This subtle, continuous stream of information transforms mere speculation into precise, targeted exploitation. These digital breadcrumbs empower attackers to craft payloads that are meticulously aligned with the specific software environment they anticipate on the target’s system, thereby significantly increasing the effectiveness of their attacks while simultaneously reducing the noisy, detectable experimentation phase.
The Dynamics of Software Drift and Neglect
Most enterprises dedicate considerable resources and systematic effort to operating system (OS) patching. Established update pipelines are well-understood, web browsers are typically configured for frequent automatic updates, and mobile devices often adhere to rigorous management policies. Systems are initiated with robust security baselines and are continuously monitored for deviations. However, third-party utilities frequently exist outside these tightly controlled regimes, exhibiting a distinct and problematic update lifecycle.
Vendors employ diverse installer methodologies, some applications feature built-in auto-update functions, others depend entirely on user-initiated updates, while some are deliberately frozen or disabled by enterprise packaging systems to maintain compatibility with critical workflows. Consequently, over extended periods, a fragmented landscape emerges where multiple builds of the same application proliferate across endpoints. Many of these versions become stale, languishing for years with known, exploitable vulnerabilities simply because they have fallen off the radar of active management. Analysis of enterprise environments consistently reveals the coexistence of various versions of the same third-party application, with some lagging years behind current security fixes. This pervasive fragmentation quietly accumulates substantial exploit potential without triggering overt security alerts. From a strategic security perspective, this "drift" is critically important because attackers do not necessarily require novel exploits. They merely benefit from any vulnerable version that still persists somewhere within the organizational footprint. A five-year-old PDF reader, for instance, silently carries five years’ worth of cumulative exploit potential. What might appear as minor technical debt or an operational oversight ultimately widens the opportunity window for significant and potentially catastrophic exploitation.
The Human Element of Trust
The role of human psychology is also paramount when considering these ubiquitous tools. Email clients, document editors, web browsers, and archive utilities are often perceived by users as fundamental infrastructure, akin to physical desks or keyboards. The act of opening a PDF file does not intuitively feel like executing code; previewing an email does not register as a program execution event; and extracting files from an archive feels like a routine, benign action. This deeply ingrained trust is a critical vulnerability.
By the time any behavior within these applications appears unusual or suspicious, the initial, compromising interaction has often already transpired in an environment that users rarely question. These routine actions occur thousands of times daily across an organization, making the arduous task of tracing a compromise back to a specific document, email, or user interaction exceptionally difficult. This inherent human trust, coupled with the sheer volume of daily interactions, provides a broad and easily exploitable avenue for attackers who understand how to leverage these routine activities for malicious ends.
Strategic Imperatives: Beyond the Platform
For organizational leadership, this analysis offers a crucial shift in perspective, moving beyond mere apprehension to informed strategic planning. While security strategies correctly prioritize the platform layer—operating systems, network infrastructure, identity management, and cloud environments—these components alone do not fully encapsulate the intricate reality of how work is actually performed.
Work fundamentally occurs within email clients, spreadsheet applications, PDF viewers, web browsers, archive tools, and remote access sessions. This is precisely where files are opened, previews are rendered, links are clicked, and sensitive data traverses between individuals and systems. This very predictability makes these applications attractive targets. Consequently, the strategic weight of third-party patching often exceeds conventional expectations. Even if the underlying operating system is meticulously managed and updated, the myriad of applications layered upon it can quietly define the true extent of an organization’s exposure. Adopting a holistic view of the entire business footprint is not about assuming inherent weakness, but rather about gaining a profound understanding of where everyday operational activities intersect with critical security vulnerabilities.
The Strategic Significance of Routine Patching
Third-party patching is frequently relegated to an operational task rather than a strategic imperative. Yet, these utilities sit at the critical intersection of human interaction, data processing, and code execution. Their ordinariness is precisely what imbues them with such significant strategic importance. This is not because every organization is identical, but because they are sufficiently similar that sophisticated attackers design their campaigns to capitalize on these shared characteristics.
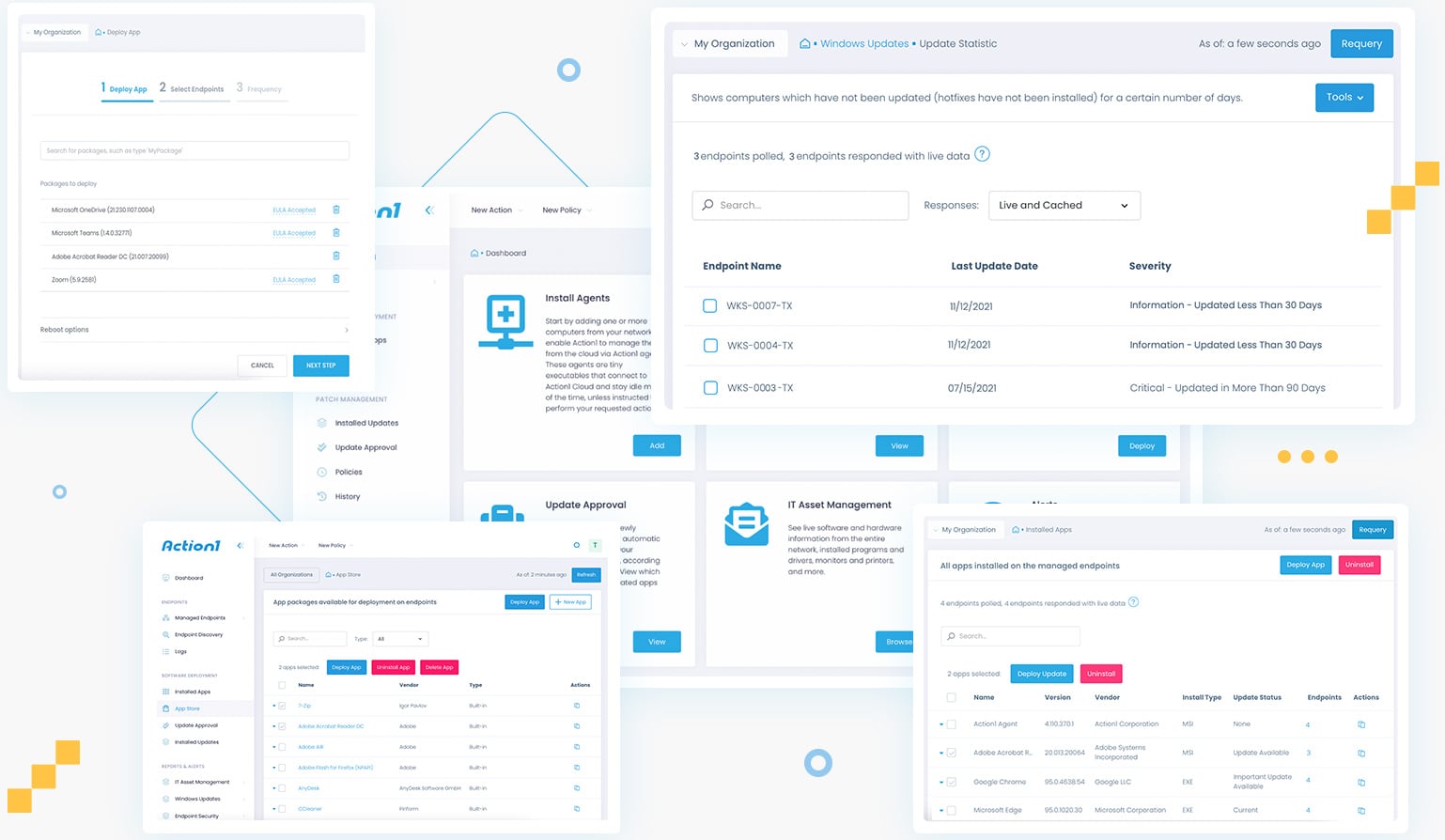
When security teams audit their environments, the focus typically remains on core infrastructure. However, there is immense strategic value in systematically assessing the standard business application suite across all endpoints: how it evolves, and the consistency with which it is kept current. Critical questions must be asked: Which tools are genuinely indispensable? Which were deployed merely as part of a default installation? Which remain installed but unused, presenting latent risk? And crucially, which have ceased receiving updates because their presence went unnoticed?
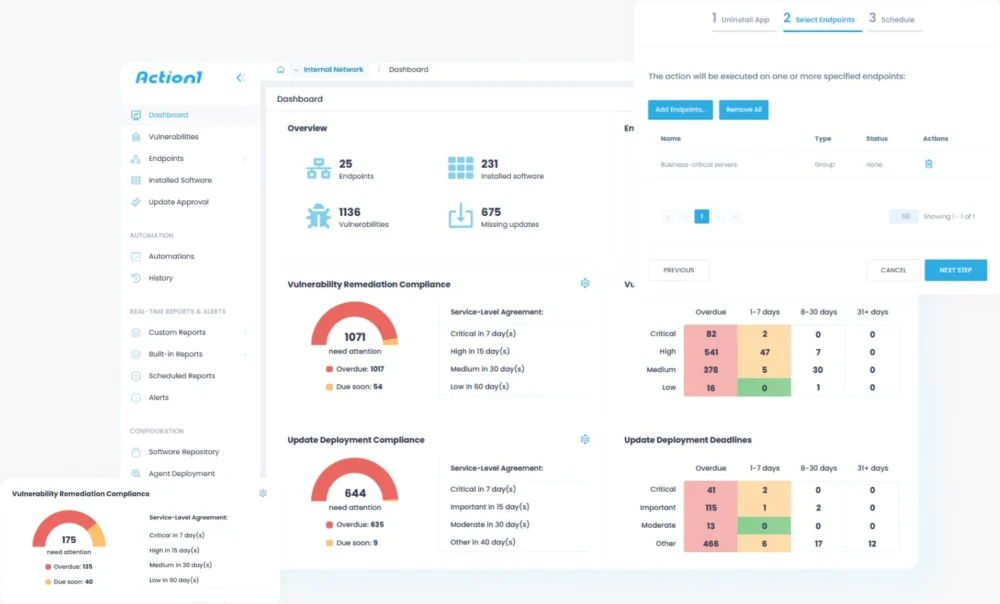
This granular understanding explains why platforms designed for comprehensive endpoint management consistently demonstrate that rigorous third-party patching delivers a greater reduction in real-world risk than many more visible and ostensibly sophisticated security controls. Exploitation rarely hinges on a single, newly discovered vulnerability; it is more frequently enabled by years of accumulated software drift across third-party applications that quietly fall out of date while remaining deeply embedded in daily workflows. These conditions—the prevalence of unpatched, everyday software—exist long before any exploit is conceived or deployed. They fundamentally shape the practical attack surface by dictating which software executes, which files are opened, and which user actions are routine enough to evade scrutiny. Third-party software is not merely adjacent to the core platform; it is an intrinsic part of how the platform operates, and it is frequently the point where significant exposure concentrates, even when every other aspect of the environment appears meticulously managed.
Organizations are increasingly recognizing that patching operating systems alone, while crucial, is insufficient, and that comprehensive third-party application patching can no longer be treated as a secondary, low-priority task. Addressing the complexities of modern cyber risk necessitates continuous visibility into the third-party software landscape and the agile capability to remediate vulnerable applications across all endpoints with speed and consistency. When evaluating contemporary patch management solutions, the most effective options are those explicitly designed around this critical reality.
By activating a robust patch management strategy, organizations can proactively identify and mitigate the silent, pervasive risks posed by the often-overlooked software that underpins their daily operations, thereby transforming their overall security posture.