In a significant development for industrial cybersecurity, Dutch multinational paint and coatings behemoth AkzoNobel has officially acknowledged a digital security incident impacting one of its operational sites within the United States. This confirmation follows the emergence of leaked data attributed to the Anubis ransomware collective, highlighting the persistent and evolving threat landscape facing global enterprises. While company representatives assert that the breach has been contained and its overall impact remains circumscribed, the nature of the exfiltrated data raises substantial concerns regarding intellectual property, client confidentiality, and potential regulatory ramifications.
AkzoNobel, a titan in the paints and coatings industry, commands an impressive global presence, boasting approximately 35,000 employees and annual revenues surpassing $12 billion. Its expansive portfolio includes globally recognized brands such as Dulux, Sikkens, International, and Interpon, underscoring its critical role in various sectors from architectural finishes to protective industrial coatings. The company’s vast operational footprint across more than 150 countries renders it a prime target for sophisticated cyber adversaries seeking high-value data and potential disruption.
According to statements provided by AkzoNobel, the identified security incident was isolated to a specific U.S. facility, with swift action taken to mitigate further spread. A company spokesperson conveyed to relevant media outlets that "AkzoNobel has identified a security incident at one of our sites in the United States. The incident was limited to the respective site and was already contained." They further elaborated, "The impact is limited, and we are taking the appropriate steps to notify and support impacted parties, and will work closely with relevant authorities." This proactive communication, while asserting control, simultaneously initiates a complex process of victim notification and regulatory engagement.
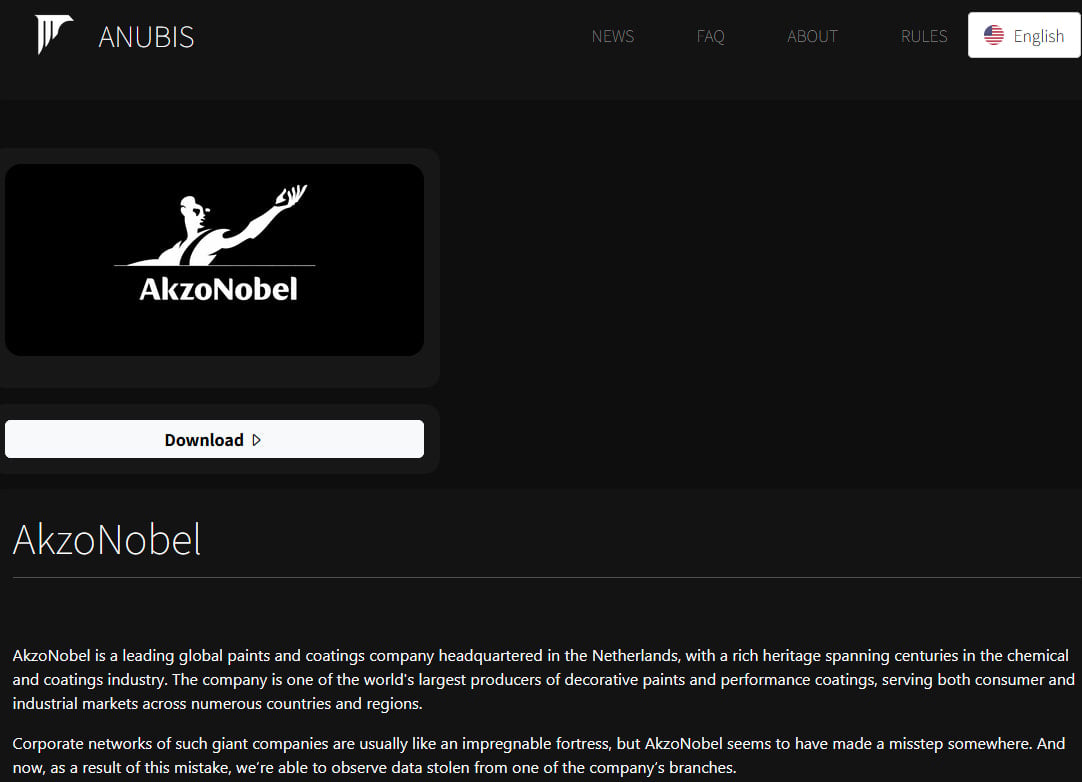
The disclosure by AkzoNobel comes in the wake of claims made by the Anubis ransomware gang, a relatively new but increasingly aggressive player in the cybercrime arena. Anubis publicly asserted responsibility for the attack, detailing on its dark web leak site the alleged exfiltration of a substantial volume of data: approximately 170 gigabytes comprising nearly 170,000 individual files. To substantiate their claims and exert pressure on the victim, the group published a selection of sample documents, including screenshots and an itemized list of the compromised files. These samples, featured prominently on the Anubis ransomware site, serve as a stark reminder of the tangible consequences of such intrusions.
A detailed examination of the published data samples reveals a disturbing array of sensitive information. Among the exfiltrated documents are confidential agreements with high-profile clients, indicating potential contractual details and business strategies could be exposed. Furthermore, the cache reportedly contains a wealth of personally identifiable information (PII) such as email addresses, phone numbers, and even scanned copies of passports, posing significant risks of identity theft and phishing attacks for individuals. Internal communications, including private email correspondence, were also reportedly compromised. Beyond PII and client data, the breach appears to have impacted technical and proprietary information, including material testing documents and internal technical specification sheets. Such data could hold immense value for competitors or state-sponsored actors engaged in industrial espionage, potentially undermining AkzoNobel’s competitive edge and future innovation.
At the time of this reporting, the data release by Anubis is understood to be partial, suggesting the group may hold back a larger portion of the stolen information as leverage. AkzoNobel has maintained discretion regarding any potential engagement or negotiation with the threat actors, a common stance for organizations navigating ransomware incidents where public acknowledgment of payment can incentivize further attacks.
The Anubis ransomware operation emerged onto the cybercrime scene in December 2024, quickly establishing itself as a potent force. Operating under a ransomware-as-a-service (RaaS) model, Anubis offers its affiliates a substantial 80% share of any ransoms successfully extracted from victims. This high-payout incentive structure attracts a wide network of cybercriminals, enabling the group to scale its operations rapidly. The RaaS model lowers the technical barrier for entry into ransomware attacks, allowing less skilled individuals to execute sophisticated campaigns using tools and infrastructure provided by the core Anubis developers.
Further bolstering its capabilities and reach, Anubis launched an aggressive affiliate program on the prominent RAMP cybercrime forum in February 2025. This move significantly amplified its influence and activity within the illicit cyber landscape, providing a platform for recruitment and coordination among threat actors. The group’s evolution continued with a notable and particularly destructive addition to its arsenal in June of the same year: a data wiper module. This wiper is designed to permanently destroy victim files, rendering data recovery impossible, even if a ransom were paid. The deployment of such a destructive tool elevates the stakes for victims, transforming a data theft and encryption event into a potential irreversible data loss scenario, pushing organizations to prioritize prevention and robust backup strategies.
Broader Context and Expert Analysis of the Incident
The cyberattack on AkzoNobel is not an isolated event but rather indicative of a broader and increasingly aggressive trend in the global cybersecurity landscape. Large multinational corporations, particularly those in manufacturing, chemicals, and critical infrastructure sectors, have become prime targets for ransomware groups. These organizations often possess vast amounts of valuable intellectual property, sensitive client data, and interconnected operational technology (OT) systems, making them lucrative targets for financial extortion and industrial espionage.
The "limited impact" assessment by AkzoNobel, while reassuring in the immediate term, warrants deeper scrutiny from an analytical perspective. "Containment" typically refers to the successful isolation of affected systems to prevent further spread of the malicious activity. However, it does not erase the fact that data has been exfiltrated. The long-term implications of such a breach can extend far beyond initial operational disruptions. Reputational damage, loss of customer trust, and potential competitive disadvantages arising from the exposure of confidential client agreements and technical specifications can have enduring effects on market position and shareholder value.
The nature of the stolen data—particularly passport scans, confidential agreements, and technical specifications—presents multi-faceted risks. Passport scans expose individuals to heightened risks of identity theft, fraud, and targeted social engineering attacks. Confidential client agreements, if exploited, could reveal pricing strategies, contractual terms, and business relationships, potentially allowing competitors to undercut AkzoNobel or for threat actors to engage in secondary extortion schemes against AkzoNobel’s partners. The theft of material testing documents and internal technical specification sheets represents a significant loss of intellectual property, which could be leveraged for industrial espionage, counterfeiting, or reverse engineering by rival entities or hostile nation-states.
From a regulatory standpoint, the incident triggers various compliance obligations. Depending on the residency of the affected individuals and clients, AkzoNobel may fall under the purview of regulations such as the General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA) in the United States, and other industry-specific data protection laws. These regulations mandate strict breach notification protocols, potentially imposing significant fines for non-compliance or inadequate data protection measures. The process of identifying and notifying all impacted parties, as stated by AkzoNobel, is a complex and resource-intensive undertaking, further adding to the cost and complexity of the incident response.
The use of a data wiper by Anubis, though not explicitly confirmed to have been deployed in this specific attack, underscores the escalating destructive potential of modern ransomware. The psychological impact of facing not just data encryption but the complete obliteration of critical files can be immense, pushing organizations to consider all available options, including difficult decisions regarding ransom payments, to avoid catastrophic operational paralysis. This tactic shifts the ransomware paradigm from merely holding data hostage to threatening its permanent destruction, making robust data backup and recovery strategies more critical than ever.
Implications and Future Outlook for Corporate Cybersecurity
The AkzoNobel incident serves as a critical case study for global enterprises in assessing their cyber resilience. It highlights several key areas that demand immediate and continuous attention:
- Robust Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) Systems: The ability to rapidly detect, contain, and eradicate threats like Anubis is paramount. This requires sophisticated monitoring tools that can identify anomalous behavior and prevent lateral movement within a network.
- Zero-Trust Architecture: Assuming no user or device can be implicitly trusted, regardless of their location, is a fundamental shift that can limit the blast radius of a successful breach. Granular access controls and continuous verification are essential.
- Comprehensive Data Classification and Protection: Organizations must meticulously classify their data based on sensitivity and apply appropriate protection mechanisms. This includes encryption at rest and in transit, as well as strict access controls to prevent unauthorized exfiltration of critical assets like intellectual property and PII.
- Supply Chain Cybersecurity: As evidenced by the leakage of client agreements, an organization’s cybersecurity posture affects its entire ecosystem. Robust vendor risk management and supply chain security protocols are no longer optional.
- Employee Training and Awareness: While sophisticated attacks often bypass technical controls, human error remains a significant vulnerability. Continuous training on phishing, social engineering, and secure data handling practices is vital.
- Incident Response Planning and Testing: AkzoNobel’s ability to "contain" the incident points to an existing incident response capability. However, regular testing and refinement of these plans, including simulated data exfiltration scenarios, are crucial to ensure their effectiveness under pressure.
- Investment in Threat Intelligence: Staying abreast of emerging threats, attacker tactics, techniques, and procedures (TTPs) like those employed by Anubis, including their RaaS model and data wiper capabilities, is essential for proactive defense.
The long-term outlook for corporate cybersecurity suggests a continuous arms race between defenders and attackers. Ransomware groups like Anubis will continue to innovate, refining their methods for initial access, lateral movement, data exfiltration, and extortion. The move towards more destructive tactics, such as data wipers, indicates a willingness to inflict maximum damage, increasing the pressure on victims. For companies like AkzoNobel, the incident is not merely a single event but the initiation of an ongoing process of investigation, remediation, and reinforcement of their digital defenses. The true measure of its impact will unfold in the coming months as the full scope of data exposure is determined and the company navigates the complex landscape of regulatory compliance, potential legal challenges, and the imperative to restore full confidence among its stakeholders and customers.