A wide-ranging federal investigation has been launched by the Federal Bureau of Investigation (FBI) into a series of highly deceptive malware campaigns that have infiltrated the popular Steam gaming platform, targeting users with sophisticated information-stealing software embedded within seemingly legitimate video games. The agency is actively seeking individuals who may have been impacted by these malicious titles, which have been observed circulating on the platform over an extended period, leading to substantial financial losses and data compromise.
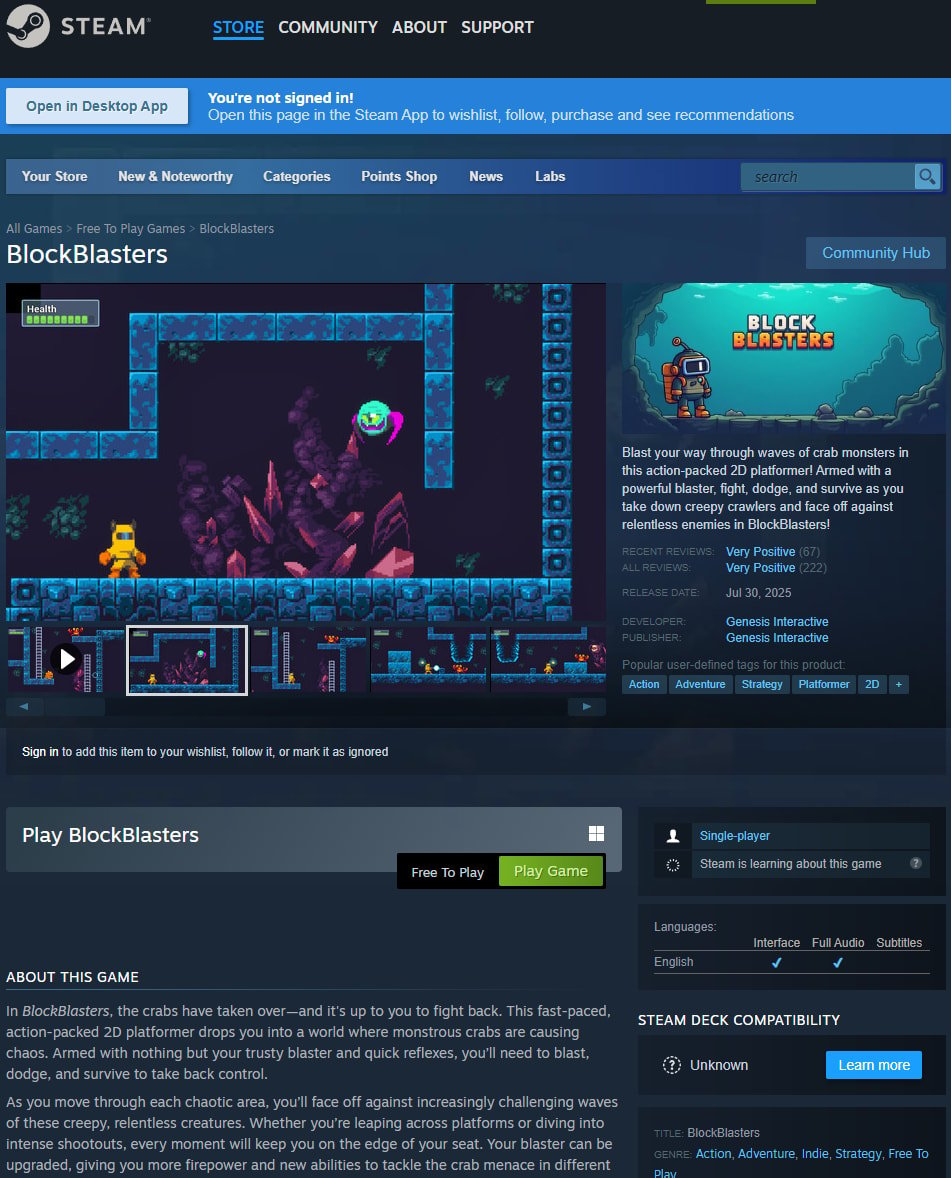
The FBI’s Seattle Division has issued a public appeal for information, aiming to meticulously identify and document victims who downloaded and installed specific malicious games available on Steam. This critical phase of the investigation focuses on incidents occurring between May 2024 and January 2026, a timeframe during which threat actors successfully deployed multiple compromised applications. The agency’s notice explicitly names several titles implicated in this illicit activity, including "BlockBlasters," "Chemia," "Dashverse/DashFPS," "Lampy," "Lunara," "PirateFi," and "Tokenova." This extensive list underscores the pervasive nature of the threat and the variety of genres exploited by cybercriminals.
The primary objective of this victim identification initiative is to gather comprehensive data regarding the impact of these malicious programs, particularly concerning the theft of cryptocurrency and the unauthorized takeover of user accounts. A specialized questionnaire deployed by the FBI delves into crucial details such as cryptocurrency transaction records, specifics of compromised accounts, and the precise amounts of funds misappropriated. Furthermore, investigators are requesting any communication screenshots with individuals who promoted these games, a strategic move designed to aid in the intricate process of tracing stolen digital assets and linking them back to the perpetrators responsible for distributing the malware.
The FBI’s involvement in this case highlights the significant federal implications of such cybercrimes, extending beyond individual financial loss to encompass organized criminal activity, interstate commerce violations, and potentially international dimensions. As mandated by law, the FBI is committed to identifying victims of federal crimes, ensuring they are afforded access to relevant services, restitution opportunities, and legal rights under both federal and state statutes. The agency has affirmed its commitment to maintaining the strict confidentiality of all victim identities, encouraging full cooperation without fear of exposure. While specific operational details of the ongoing investigation remain guarded, the FBI has confirmed the legitimacy of its outreach efforts, including official communications sent to potentially affected users and the designated email address, [email protected], for inquiries.

This concerted effort by federal law enforcement underscores a growing concern within the cybersecurity landscape: the weaponization of trusted digital platforms, such as online gaming storefronts, to disseminate sophisticated malware. The inherent trust users place in verified platforms, combined with the often-casual approach to software downloads within the gaming community, creates an opportune environment for cybercriminals to execute their schemes. The incident highlights a critical vulnerability in the digital supply chain, where malicious code can be injected into what appears to be legitimate software, circumventing standard security protocols and user vigilance.
The modus operandi of these attacks typically involves the deployment of information-stealing malware, commonly referred to as "infostealers" or "cryptodrainers." These sophisticated programs are designed to clandestinely extract a wide array of sensitive data from infected devices. Upon successful execution, they can harvest user credentials for various online services, access and exfiltrate cryptocurrency wallet keys, siphon browser data including cookies and saved passwords, and even collect system information. The extracted data is then transmitted to command-and-control servers operated by the threat actors, who subsequently leverage it for financial gain, identity theft, or further malicious activities.
A particularly egregious example cited in the investigation involves "BlockBlasters," a 2D platformer initially launched as a benign application. Subsequent updates, however, surreptitiously introduced cryptodrainer malware, transforming a seemingly innocuous game into a potent tool for illicit cryptocurrency theft. The devastating impact of this particular variant was dramatically brought to light when a video game streamer, engaged in a charity fundraiser for cancer treatment, reportedly lost over $32,000 from his cryptocurrency wallet after installing the compromised game. Subsequent blockchain analysis estimated the total theft from "BlockBlasters" to be approximately $150,000 across 261 Steam accounts, with some researchers indicating an even higher victim count. This incident vividly illustrates the dual threat of financial exploitation and the erosion of trust in digital communities built around altruistic endeavors.
Another case involved the survival crafting game "Chemia," where a known threat actor, identified as EncryptHub, integrated the HijackLoader malware, which in turn facilitated the download of the Vidar information stealer. Further analysis revealed that "Chemia" also installed EncryptHub’s proprietary "Fickle Stealer" malware, designed to pilfer credentials, browser data, cookies, and cryptocurrency wallet information. Similarly, "PirateFi" distributed the Vidar infostealer, remaining on the Steam platform for approximately one week and potentially affecting up to 1,500 users before its removal. The rapid deployment and subsequent removal of such titles underscore the agility of these threat actors and the reactive nature of platform security measures. Following the "PirateFi" incident, Steam issued a public warning to players, advising them to conduct comprehensive antivirus scans, review installed software, and consider a complete operating system reinstallation – a drastic measure indicative of the potential depth of system compromise.
The proliferation of malware within gaming platforms is not an isolated phenomenon but rather a growing trend in the broader cybersecurity landscape. Cybercriminals are increasingly diversifying their attack vectors, moving beyond traditional phishing campaigns and exploit kits to leverage seemingly legitimate channels. Gaming platforms, with their vast user bases, frequent software updates, and often less stringent security consciousness among users, present an attractive target. The financial allure is particularly strong given the rising popularity and value of cryptocurrencies, which offer a relatively untraceable means of illicit financial gain. The nature of these attacks often blurs the lines between individual targeting and organized cybercrime, making federal intervention crucial for comprehensive investigation and mitigation.
The challenges faced by platforms like Valve, the operator of Steam, in policing millions of user-generated and third-party applications are immense. The sheer volume of content necessitates a balance between fostering an open development environment and implementing robust security vetting. While automated scanning tools and user reporting mechanisms are in place, sophisticated malware can often evade initial detection, especially when payloads are introduced through delayed updates or obfuscated code. This incident prompts critical questions about the efficacy of current content moderation policies, the speed of threat detection, and the responsibility of platform providers in safeguarding their users from evolving cyber threats. The silence from Valve regarding the FBI’s investigation, while potentially strategic, underscores the complexity and sensitivity of such high-profile security breaches.
From a user perspective, the implications extend beyond immediate financial loss. Compromised credentials can lead to identity theft, unauthorized access to other online accounts, and severe privacy breaches. The psychological impact on victims, particularly those who lose significant funds or have their personal data exposed, can be substantial. Therefore, proactive user education and enhanced security practices are paramount. Gamers are advised to exercise extreme caution when downloading new titles, particularly those from unknown developers or offered for free. Implementing multi-factor authentication (MFA) on all gaming and financial accounts, utilizing robust antivirus and anti-malware solutions, regularly backing up critical data, and scrutinizing game reviews for any red flags are essential preventative measures. Furthermore, running games in a sandboxed environment or on a dedicated gaming machine, separate from sensitive financial or personal data, can provide an additional layer of defense against potential compromise.
Looking ahead, this investigation is likely to have significant ramifications for both the cybersecurity industry and the digital entertainment sector. It will undoubtedly prompt stricter vetting processes for games submitted to major platforms, potentially leading to a more rigorous "know your developer" standard. Law enforcement agencies will continue to refine their strategies for tracking cryptocurrency flows and dismantling international cybercriminal networks that exploit digital platforms. The incident serves as a stark reminder that the boundaries between virtual entertainment and real-world financial risk are increasingly blurred, demanding a more integrated and sophisticated approach to security from all stakeholders – platform providers, developers, and users alike. The ongoing efforts by the FBI underscore a clear message: the digital realm is not immune to law, and those who exploit its vulnerabilities will face federal scrutiny and prosecution.